Reyptson ransomware / virus (Free Instructions) - Tutorial
Reyptson virus Removal Guide
What is Reyptson ransomware virus?
Reyptson malware launches its own spam campaign
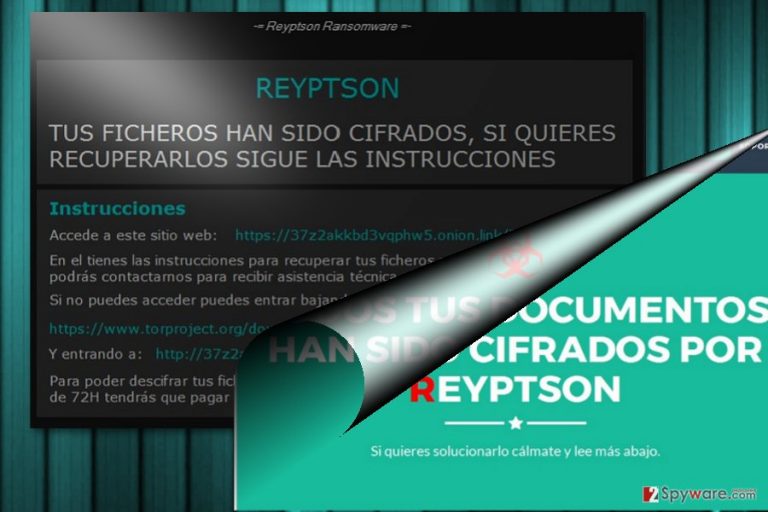
Reyptson virus operates as crypto-threat capable of encrypting netizens' data with the AES cipher. After the process, the malware appends .REYPTSON file extension to the data. Since the virus is written in the Spanish users, the malware targets users of this country.
Furthermore, recent analysis has revealed the threat's tendency to hack victims' Thunderbird contact list and plague its contacts with fraudulent invoices messages. Now it clearly prefers Spanish netizen. They are expected to receive the biggest share of such emails. At the moment one of the counterfeited senders is Folcan S.L. Facturación.
Here is a short extract of the fake email[1]:
Si tras leer la información de facturación ha localizado algún error no dude en respondernos a este mismo correo con el numero de factura y el numero de pedido.
Información de la compra
Fecha de compra 17 July 2017
Número de factura 1248325580
Objeto(s) Paquete con múltiples objetos. (Leer factura)
Método de pago PayPal
Pago a realizar desde [contact] (Estado: Aun sin pagar.)
Total 1220,30 EUR
Impuestos aplicables incluidos.
The developers have devised the GUI which leads users to the following pages of the file recovery. In the Como_Recuperar_Tus_Ficheros.txt file, the perpetrators instruct victims to pay 200€ within 72 hours. If a victim fails to do that within the specified amount of time, the sum of the ransom increases up to 500 euros. Its origin is still not fully investigated, but its trojan, Trojan.Zusy.D3C2E4 or Ransom.FileCryptor, suggests that it is related to some previous crypto-malware, for instance, FileIce ransomware which occupied the system via the similar trojan.
The malware exploits several methods of distribution: RDP, trojans, and spam emails. What is more, the malware also targets a wide choice of file formats. Regarding never-seen before features, this threat surely seems to be the result of professional cyber criminals. Luckily, multiple security tools are able to detect the infection so that you can remove Reyptson. For instance, FortectIntego or Malwarebytes might be of assistance when eliminating the malware.
Europe is getting targeted more
While the US happens to be the country which is the most frequent source and destination of crypto-malware, more international threats are spicing things up in the market. Speaking of international threats, Spanish-oriented[2] threats are becoming a norm.
Previously, we have seen the romantic version of CryptoLocker – Il tuo computer e stato infettato da Cryptolocker!, Reetner ransomware, etc.
In comparison with the recently emerged threats, Reyptson malware happens to be quite a complex threat. In the ransom message, the malware indicates the .onion website address: http://37z2akkbd3vqphw5.omon/7usuario…., though it connects to multiple websites.
The malware roots in the system quite much. It disperses its file in several Appdata locations. Reyptson threat also leaves its entry among the registry files, launches multiple processes. Thus, during the infection, you may spot that the computer starts underperforming[3]. Another significant feature is its distribution.
Ways to spread the infections and prevention tips
It is a common tendency among the hackers to disguise the files under the names of the application.
%APPDATA%\Spotify\SpotifyWebHelper\SpotifyWebHelper.pdf, HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run /v, Spotify Web Helper v1.0[4], SpotifyWebHelper.exe, SpotifyWebHelper.pdf, Spotify.vbs suggest that the infection mainly spreads via the corrupted version of Spotify. Netizens should beware of factura.pdf.exe as well.
It will be appended to the fake invoice. Once a victim opens the file, the malware connects to Command and Control server. It will then retrieve a unique ID specific to the victims' device. Additionally, the malware will also send the request for UJBTFity cookie, though its purpose remains unclear for now.
It is known that the malware also targets users via Remote Desktop Protocols. In that case, it is crucial to change the passwords and enforce the protection, but also fortify the overall security of the system. In order to do that, the anti-virus and anti-malware security applications are necessary. Now let us proceed to Reyptson removal options. 
Eliminate Reyptson virus
Though the malware entangles the system and leaves its multiple files on the system, there is still a way to get rid of the infection. Run a cyber security tool. If you cannot launch to remove Reyptson virus, then reboot the device in the Safe Mode and repeat the action. Below instructions explain the action in more detail.
Only after Reyptson removal, you may proceed to data recovery. Take a look at some of our recommended options. The automatic method will be handier as it will delete of related corrupted elements as well.
Getting rid of Reyptson virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Reyptson using System Restore
System Restore helps you revert the system to the last automatically saved restore point. It is an alternative solution to regain partial access to the system and eliminate the ransomware.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Reyptson. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Reyptson from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Reyptson, you can use several methods to restore them:
Data Recovery Pro option
It is promoted as the tool which is capable of to restore damaged and lost files. It is said to recover deleted emails as well.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Reyptson ransomware;
- Restore them.
The benefits of ShadowExplorer
This tool restores the files on the basis of shadow volume copies. Though the threat should not be underestimated, there is no information whether it eliminates the copies beforehand.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Reyptson Decrypter
At the moment, there is no official decryption tool released yet.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Reyptson and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Lawrence Abrams. Reyptson Ransomware Spams Your Friends by Stealing Thunderbird Contacts. BleepingComputer. News, Reviews and Tech support.
- ^ How to remove virtual threats. IT News, Reviews, and Malware Elimination Guides.
- ^ Incident Response. PayloadSecurity. Free Automated Malware Analysis Service.
- ^ Andrej Ivanov. Reyptson Ransomware. ID Ransomware Blog.







