Roll Safe ransomware (Simple Removal Guide) - Free Instructions
Roll Safe virus Removal Guide
What is Roll Safe ransomware?
Roll Safe ransomware is dangerous cryptomalware that threatens to delete all your files in 24 hours post-infection
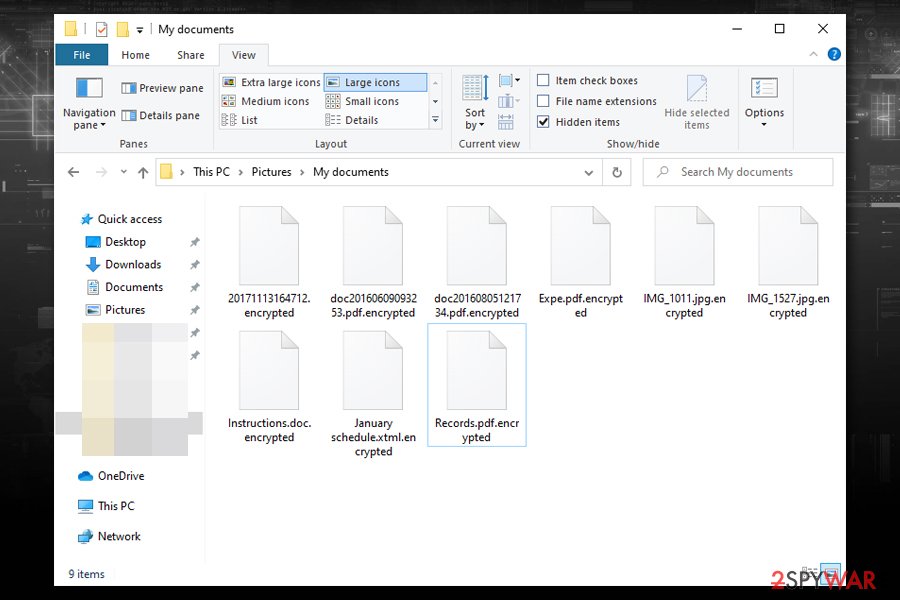
Roll Safe ransomware is malware that focuses on money extortion by encrypting all documents, pictures, videos, music, databases, and other files located on the computer. For this, malicious actors behind it use a sophisticated encryption algorithm, which also appends an .encrypted marker to each of the modified files. While the data is not corrupted, it requires a unique key that is only accessible to the attackers. However, because Roll Safe virus is a new ransomware, it is yet unknown whether threat actors actually have access to decryption software in the first place.
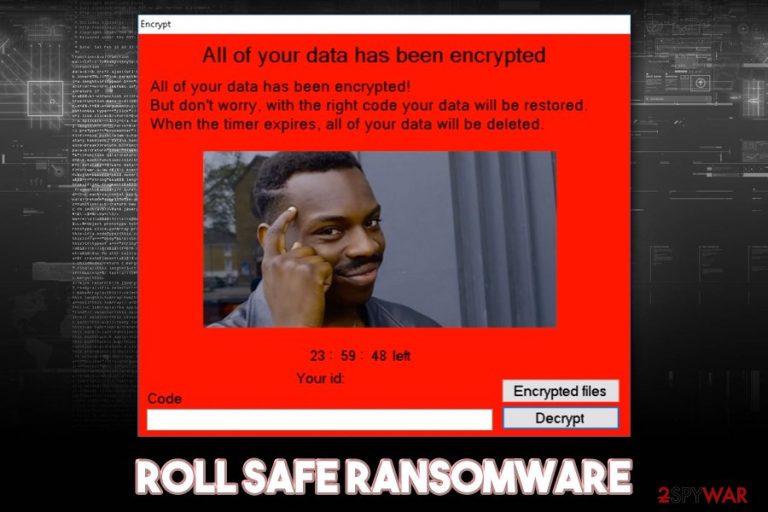
As soon as Roll Safe ransomware infects the host and encrypts files, it also drops a ransom note – a pop-up window titled “Encrypt.” While in most ransomware infection cases, this note serves as mean to contact cybercriminals (typically an email address is provided), there is no information about ways of reaching malicious actors. Nevertheless, crooks state that all the files will be deleted after 24 hours – an automatic timer starts running. Because Roll Safe ransomware does not provide any contact info and also fail to deliver user ID, it is highly likely that it is still in a development stage.
| Name | Roll Safe ransomware |
| Type | Cryptomalware, file locking virus |
| Infection means | Spam email attachments and hyperlinks, software cracks, fake updates, exploits, etc. |
| File extension | The virus appends all personal files with .encrypted extension, skipping system and executable files |
| Ransom note | After file encryption process, a pop-up message, titled “Encrypt,” shows up |
| Contact | Malicious actors do not provide contact details inside the ransom note |
| Detection |
Multitude of anti-virus engines detect malware sample as follows:
|
| File decryption | The only secure method to recover encrypted data is by copying it from backups. If not backups are available, you can try using third-party recovery software as per instructions provided in our recovery section |
| Malware removal | Terminate malicious software files with the help of powerful anti-malware software, such as SpyHunter 5Combo Cleaner or Malwarebytes |
| System fix | To remediate Windows and fix virus damage, scan your computer with FortectIntego |
Not much is known about Roll Safe ransomware yet, as not many victims have been infected so far. Nevertheless, when talking about malware propagation methods, it is highly likely that threat actors use one or several of the following tactics:
- Attachments and hyperlinks embedded inside a spam email;
- Software cracks placed on insecure sites;
- Pirated software installers from torrent and warez sites;
- Exploits[1] that initiate automatic infection sequence as soon as a malicious website is reached;
- Repacked installers on hacked or spoofed sites;
- Unprotected Remote Desktop connections;
- Trojans that serve as a backdoor[2] to deliver other malware.
Typically, a malicious executable that starts the infection is named as something that would not arouse suspicions from users, such as “Update.exe,” “Adobe Photoshop CC 2019 x64.exe,” “Hack PUBG Mobile PC.exe,” etc. Once launched, the executable creates a folder inside %AppData% directory and begins the infection routine. For example, Roll Safe ransomware deletes Shadow Volume Copies to prevent data recovery and changes the Windows registry. As a result, malware can run uninterrupted with each system launch.
After all the preparations are complete, Roll Safe ransomware runs a file encryption process, which usually takes merely a few seconds, although it can last up to few minutes depending on system configuration, amount of data to be encrypted, as well as the encryption algorithm used and its key size. As a result, all personal files located on the system are marked with .encrypted file extension, and can no longer be accessed by users. If you have no backups available, you should create a copy of locked data before performing Roll Safe ransomware removal.
The following information is shown to the Roll Safe virus-infected users in the pop-up message titled “Encrypt:”
All of your data has been encrypted
All of your data has been encrypted!
But don't worry, with the right code your data will be restored.
When the timer expires, all of your data will be deleted.23:59:59 left
Your id:
Note: to set the timer to “12:59:46 left,” simply enter the word “right” and press “Decrypt” – you can postpone the timer indefinitely.
As stated before, Roll Safe ransomware fails to display the ID correctly, and also does not provide contact information, making data recovery by retrieving the decryptor from criminals an impossible task. Nevertheless, even if such information was provided, security experts[3] advise against paying the ransom, as malicious actors may never provide the required key. The fact that this malware is in a development state, it makes it also unclear whether Roll Safe ransomware developers themselves can recover the required key.
Thus, while chances retrieving your files without backups is relatively small, you should copy the locked files and then remove Roll Safe ransomware from your computer using reputable anti-malware software after accessing Safe Mode with networking. After termination, we strongly advise you using FortectIntego to repair the Windows registry and other system files that might have been damaged by malware.
Ransomware authors can employ various methods for distribution
Spam email campaigns proved to be one of the most successful malware distribution tactics over the years, and many cybercriminals are still utilizing it. Nevertheless, because users are constantly reminded of not opening attachments inside email spam, the method became quite a bit less effective, as more users tend to delete unsolicited emails without even opening them. Nevertheless, some campaigns can employ advanced social engineering as well as technical advancements (such as email spoofing)[4] in order to make the email so much more believable. Therefore, always be on guard when dealing with new emails coming into your inbox, as some malicious ones might not be delivered into the Junk folder.
Other basic malware protection methods include:
- Install next-gen anti-malware software that can stop the infection from being triggered;
- Make sure your Windows OS and all the installed programs are up to date;
- Employ additional security precautions by enabling Firewall and installing ad-block;
- Use strong passwords (alphanumeric characters) for all your accounts – never reuse them (alternatively, make use of password manager software);
- Never use a default RDP port 3389;
- Backup all your personal files on backup systems like OneDrive, Google Drive, iCloud, etc. (you can also use physical drives like DVDs, USB sticks, external HDDs)
- Never download software cracks or pirated software installers.
Make sure you remove all the Roll Safe ransomware components
Those infected with malware, such as Roll Safe virus, should be aware that malware is often distributed along one another. Therefore, there is a chance that ransomware is not the only malicious software present on your machine. Additionally, it is also known that some crypto-malware import modules that are capable of stealing personal information – the best examples of such cases are variants of Djvu ransomware. Thus, you need to ensure that you perform Roll Safe ransomware removal properly.
For that, you should access Safe Mode with Networking (you can print out the instructions we provide below or use an alternative device to view them) and perform a full system scan with anti-malware software. Note that, because this malware is relatively unknown, it might take a few different scanners in order to detect and terminate it. Once done, you can then attempt to recover your data with third-party tools or use backups.
Note: you should backup the encrypted files before you get rid of Roll Safe ransomware, as data might become permanently corrupted otherwise.
Getting rid of Roll Safe virus. Follow these steps
Manual removal using Safe Mode
Access Safe Mode with networking if Roll Safe file virus prevents you from using an anti-malware program:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Roll Safe using System Restore
System Restore can also serve as a useful tool to remove malicious software:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Roll Safe. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Roll Safe from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Roll Safe, you can use several methods to restore them:
Data Recovery Pro might be successful in some data restoration
The less you use your computer after the infection, the higher chances are you can retrieve at least some portion of the locked data with tools like Data Recovery Pro:
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Roll Safe ransomware;
- Restore them.
Try using Windows Previous Versions feature to recover your files one-by-one
It might be possible to recover individual files with Windows Previous Versions feature. Follow these steps:
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Download ShadowExplorer software
This method might sometimes result in full data recovery – as long as Roll Safe ransomware failed to delete Shadow Volume Copies.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryption tool is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Roll Safe and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Exploit (computer security). Wikipedia. The Free Encyclopedia.
- ^ Kim Zetter. Hacker Lexicon: What Is a Backdoor?. Wired. American magazine that focuses on technology.
- ^ Dieviren. Dieviren. Security news and malware analysis.
- ^ Margaret Rouse. Email spoofing. SearchSecurity. Information Security information, news and tips.







