SATANA ransomware / virus (Jun 2016 update) - Easy Removal Guide
SATANA virus Removal Guide
What is SATANA ransomware virus?
Analysis of SATANA virus
If you happen to follow the recent IT news, you might encounter SATANA virus. It is one of the many malicious ransomware which is capable of encrypting personal information. Generally speaking, ransomware threats are highly profitable and relatively easy to develop. Regarding the current trends of rapidly emerging viruses of this kind, it seems that every person, who has at least obscure understanding about programming, can come up with a file-encrypting threat. Usually, hackers use other ransomware as a framework for the new releases. SATANA, for instance, is based on Petya and Mischa ransomware viruses and just like these malicious programs are designed to sneak into the computer and encrypt data. Of course, the virus victims have a choice. They can pay the ransomware creators around 0.5 BitCoin and receive the decryption key. Unfortunately, successful data recovery is a rare occurrence when dealing with such malicious programs. At the moment, SATANA removal is probably the best option you can go for. Choose FortectIntego or other reputable antivirus utility to remove this virus from the infected device.
In comparison with its “siblings” – Petya and Mischa – SATANA malware operates in two distinctive modes. In the former case, it leaves a file with a small kernel which acts as a bootloader. Speaking of the second mode, it behaves as ordinary ransomware. This double-track way of operating enables the virus to strike a powerful blow to the operating system. Thus, getting rid of SATANA becomes a tricky task. After the virus gets into the system and activates itself, it leaves its file in %TEMP% folder. Later on, a window emerges asking the victim to let ynuthwo.exe be installed. The problem is that the message cannot be canceled unless he or she clicks “Yes.” The latter option enables the virus to write the malignant file at the beginning of the disk. Following this, the malware starts its misdeed by encrypting personal files.
In the meantime, the virus places the file with the contact information of SATANA ransomware in the registry of the operating system. Another peculiarity of this threat functions silently without triggering any windows errors, such as BSOD (“blue screen of death”). In fact, it waits for the system reboot. Once SATANA virus enters your computer, the names of the infected files are then changed to Gricakova@techemail.com_[original file name] and from this point on become inaccessible. !satana!.txt file containing file recovery instructions is also added to the infected folders.
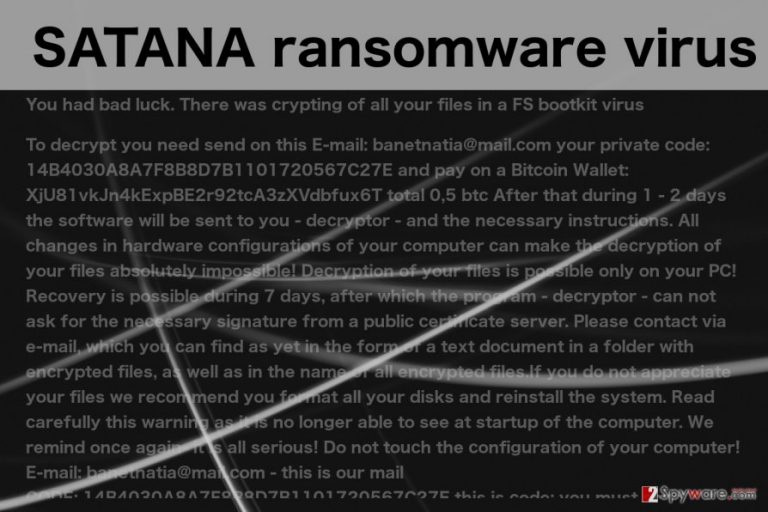
In this ransom note, the victim is given a seven-day deadline to pay for the data. Every infected computer is given an individual ID and should send it to the indicated email (banetnatia(@)mail.com) to receive the decryption key. After the specified time runs out, the criminals threaten to delete the decryption key which means that the encrypted files will be lost forever. What is also typical to this particular ransomware is that it alters the system’s settings as well. It changes the Master Boot Record settings and modifies them to load the ransomware at the system’s startup. This means that if you create some new files on your hard drive, they will most likely be encrypted the next time you reboot your computer.
After analysing the obtained samples, IT specialists suspect that the malware is still at the early stage of development. Since the dropper is enwrapped in FUD/crypter, IT experts were able to take a better look at the executable and the code strings. It enabled them to identify hackers’ goals. The obtained samples of the ransomware may help the experts come up with the decryption tool, until then, you should not let your guard down. Improve your security by installing the anti-spyware program. Undoubtedly, you must remove SATANA from your computer if you want to ensure the safety of your future data.
How can the virus invade my computer?
The cyber security experts warn that SATANA can infect your computer practically anywhere on the web. You can unknowingly install it on your device through fake software updates, download them on P2P networks or simply receive them in your email. The latter is the most common ransomware distribution technique. Your email provider filters malicious emails and places in the Spam folder. So, it is natural, that this catalog should be dealt with very carefully. Do not open emails if you do not recognize the sender. More importantly, refrain from downloading attachments added to such emails. The criminals will try to trick you by sending you supposed invoice information, online purchase receipt, speeding ticket, etc. So, remember to check the legitimacy of such emails before opening them.
Remove SATANA from the PC
If your computer has been infected with SATANA virus, you should not hesitate and remove it from your device immediately, because keeping it installed is a risk for your future files and your computer’s health. Use only the reputable antivirus utilities for that. We should remind you, though, that SATANA removal will not decrypt your data. You may need to use other data recovery software for this purpose. We recommend PhotoRec, R-Studio or Kaspersky virus-fighting utilities. Of course, a more guaranteed file recovery can be achieved by restoring data from backups. But if you do not have them, try the utilities above. If you are having trouble removing SATANA from your device, you can try decontaminating the virus using the instructions provided below this article.
Getting rid of SATANA virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove SATANA using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of SATANA. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from SATANA and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.







