Scarry ransomware (Virus Removal Guide) - Decryption Methods Included
Scarry virus Removal Guide
What is Scarry ransomware?
Scarry ransomware – a new virus that cybercriminals use for money extortion
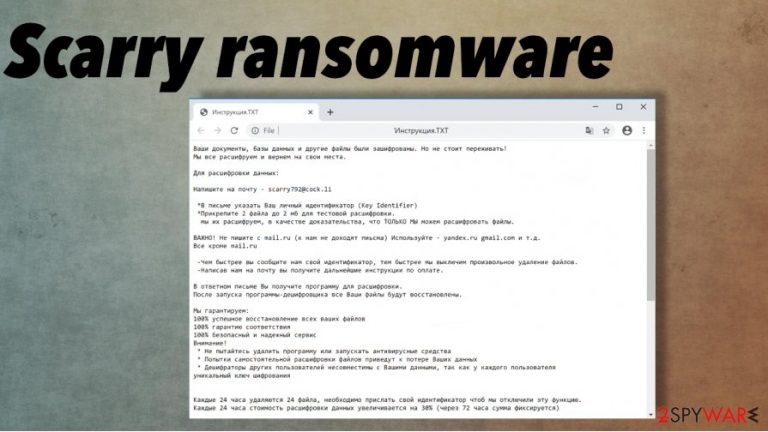
After the file locking process is completed, a ransom note “Инструкция.TXT” appears in all affected folders. The whole message is written in the Russian language. Developers of Scarry virus are urging the victims to contact them via email – scarry792@cock.li. A unique ID is prescribed to all victims. As a gesture of goodwill, the cybercriminals are offering to forward them two files for free decoding, thus showing that the decryption tool exists.
It is highly recommended not to agree with any demands of the criminals, sd the promised decoding tool/key might never get delivered. Perpetrators also advise not to use using any antivirus software or third-party decryption tools as it may lead to permanent data loss. A new feature that is introduced with this Scarry ransomware is that it deletes 24 files in 24 hours until the ransom is paid.
| NAME | Scarry file virus |
| TYPE | Ransomware |
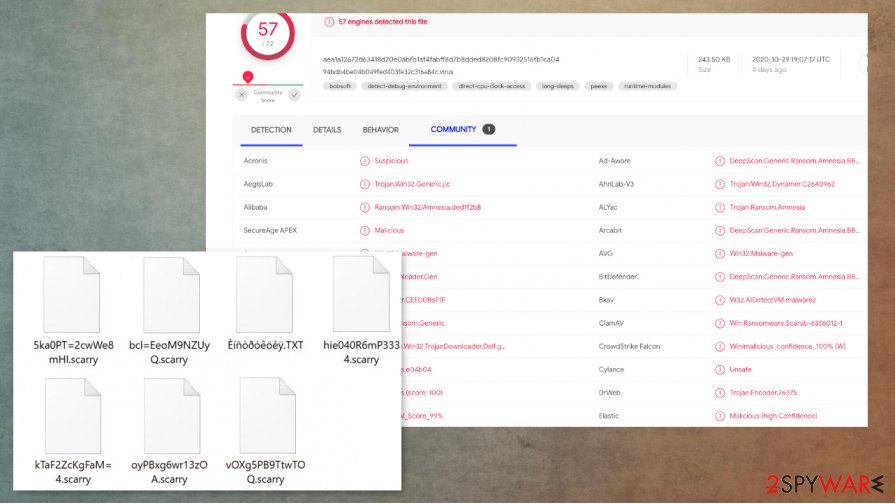
| FAMILY | Scarab Family |
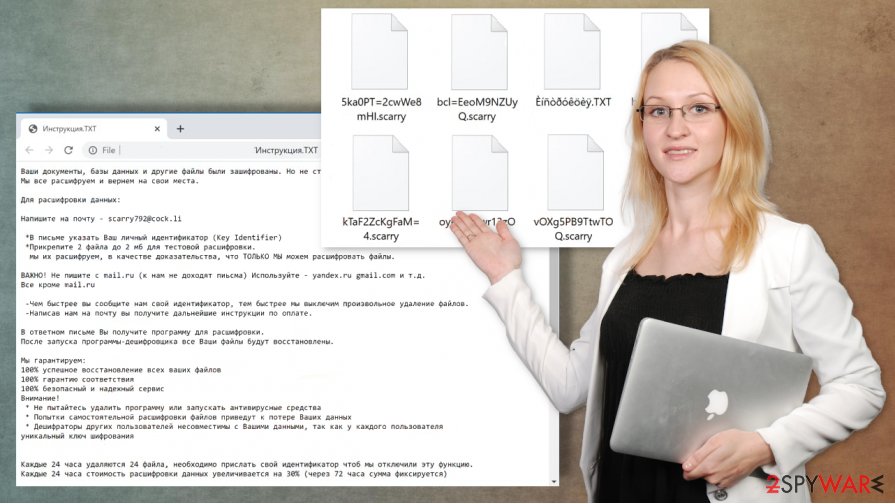
| EXTENSION | All non-system files are appended with two consecutive extensions: random character sequence and .scarry, e.g., a.pdf.001-30DE=I.scarry |
| RANSOM NOTE | A file “Инструкция.TXT” appears in contaminated folders. Written in Russian, urges the victims to contact the cybercriminals ASAP via email |
| CONTACT EMAIL | scarry792@cock.li |
| DISTRIBUTION | Spam emails, file-sharing platforms, malicious sites, other threats |
| ISSUES | All victim's personal data is encoded with a military-grade algorithms, thus making the data inaccessible. Every 24 hours victims lose 24 files. |
| REMOVAL | To remove Scarry virus use dependable software like SpyHunter 5Combo Cleaner or Malwarebytes. It will automatically remove the virus and all its allocated files. |
| SYSTEM FIX | Malware harms system files, to prolong and enforce their wrongdoing. After Scarry ransomware removal use a powerful FortectIntego tool to restore the functions of your device to normal. |
Since Scarry ransomware belongs to the Scarab ransomware family, it employs a military-grade AES-256 and RSA-2048 algorithms to lock users' files. There is no possibility to unlock the files with any third-party software. But there's always hope that someday it will come out. Export infected files to empty, offline storage and keep your fingers crossed.
Whole text presented in the ransom note named “Инструкция.TXT”, written in Russian:
Ваши документы, базы данных и другие файлы были зашифрованы. Но не стоит переживать!
Мы все расшифруем и вернем на свои места.Для расшифровки данных:
Напишите на почту – scarry792@cock.li
*В письме указать Ваш личный идентификатор (Key Identifier)
*Прикрепите 2 файла до 2 мб для тестовой расшифровки.
мы их расшифруем, в качестве доказательства, что ТОЛЬКО МЫ можем расшифровать файлы.ВАЖНО! Не пишите с mail.ru (к нам не доходят пиьсма) Используйте – yandex.ru gmail.com и т.д.
Все кроме mail.ru-Чем быстрее вы сообщите нам свой идентификатор, тем быстрее мы выключим произвольное удаление файлов.
-Написав нам на почту вы получите дальнейшие инструкции по оплате.В ответном письме Вы получите программу для расшифровки.
После запуска программы-дешифровщика все Ваши файлы будут восстановлены.Мы гарантируем:
100% успешное восстановление всех ваших файлов
100% гарантию соответствия
100% безопасный и надежный сервис
Внимание!
* Не пытайтесь удалить программу или запускать антивирусные средства
* Попытки самостоятельной расшифровки файлов приведут к потере Ваших данных
* Дешифраторы других пользователей несовместимы с Вашими данными, так как у каждого пользователя
уникальный ключ шифрованияКаждые 24 часа удаляются 24 файла, необходимо прислать свой идентификатор чтоб мы отключили эту функцию.
Каждые 24 часа стоимость расшифровки данных увеличивается на 30% (через 72 часа сумма фиксируется)P.S
Если Вам не ответили в течении 48 часов. Вам нужно будет связаться с нами по дополнительным контактам.Скачайте и установите Tor Browser – hxxps://www.torproject.org/ru/download/
Откройте через Tor Browser сайт – hxxp://sonarmsniko2lvfu.onion (сайт не будет работать через обычный браузер, только через ТОР)
Зарегистрируйтесь и напишите нам.*Наш ник в Sonar'e – savefile365
====================
Ваш идентификатор (ID)
–
If you had backups, use SpyHunter 5Combo Cleaner or Malwarebytes to automatically remove Scarry ransomware from your device and restore your data from backups. To strengthen their malicious impact on the system, ransomware usually modifies system files to block antivirus and similar software from working correctly.
After successful Scarry ransomware removal, use FortectIntego tool to automatically revert such changes and restore system functionality. This threat can trigger various changes and alterations in system folders, files, to even functions.
Popular methods hackers use to infect computers
Cybercriminals employ many diverse ways to spread their created malware. Most commonly, ransomware is distributed via file-sharing platforms, such as The Pirate Bay, BitTorrent, and email spam attachments. Viruses can be camouflaged as .jped, .pdf, .exe, .txt, and other file types. Upon getting entry into a computer system, ransomware starts the encryption process immediately.
Torrent sites are a very common method to spread infections, as users from all over the world can upload anything into them. Unaware people might think that they're downloading a new movie, game cheat codes, or some illegal software activation kit (aka “crack”), but in reality, they're getting themself in a lot of trouble.
Spam emails are another beloved way of the cyberthieves to administer their creations.[2] Uninformed users get their computer systems contaminated when opening mischievous hyperlinks and malicious email attachments. Always keep in mind that offenders are trying to trick users by sending them officially looking emails. Never download a file without scanning it first.
Scarry file virus removal requires AV detection engines
Ransomware removal should be trusted to professionals because trying to delete it manually could cause more harm. To remove Scarry ransomware, use apps like SpyHunter 5Combo Cleaner and Malwarebytes; this software will automatically remove the malicious content from infected devices.
However, this process won't decrypt files. You need tools that can detect[3] Scarry ransomware virus and get rid of it properly. Users should always keep backups in several different locations in case of emergencies like this. Use the aforementioned trustworthy anti-malware software to keep you safe while browsing.
The family that the virus belongs to is known to modify system files to run uninterrupted on the infected devices. After Scarry ransomware removal we recommend using FortectIntego to perform a powerful system scan and automatically restore any damage the virus has done to the device.
Getting rid of Scarry virus. Follow these steps
Manual removal using Safe Mode
Scarry ransomware can be removed when you rely on Safe Mode with Networking reboot
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Scarry using System Restore
You should try the System Restore feature as an alternate method for virus removal
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Scarry. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Scarry from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Scarry, you can use several methods to restore them:
Data Recovery Pro can help with affected files
When you accidentally delete files yourself or when data gets affected by Scarry ransomware, you can use Data Recovery Pro for the restoring
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Scarry ransomware;
- Restore them.
Windows Previous Versions feature can help with encoded files
If you used System Restore as the method for virus elimination, you can trust Windows Previous Versions and recover individual data yourself
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer – a method for encoded file recovery
You should be sure that Scarry ransomware is not affecting Shadow Volume Copies before you can use the feature for file recovery
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Decryption tool for Scarry ransomware is not released yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Scarry and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Detection rate. VirusTotal. Online malware scanner.
- ^ Encryption. Wikipedia. The free encyclopedia.
- ^ Danny Palmer. Ransomware: Attacks that start with phishing emails are suddenly back in fashion again. ZDNet. Technology and security news.







