ScreenSaver.app (Virus Removal Instructions) - Free Guide
ScreenSaver.app Removal Guide
What is ScreenSaver.app?
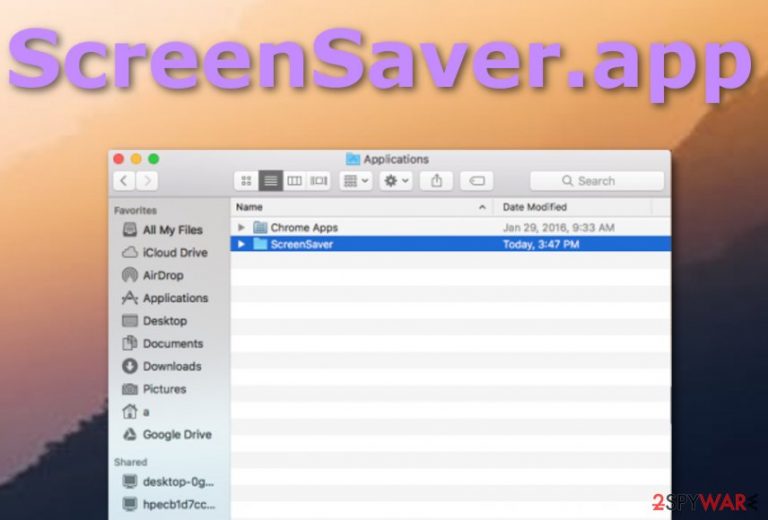
ScreenSaver.app – macOS-based adware that is programmed to promote a fake search provider searchbaron.com
ScreenSaver.app is categorized as adware[1] that targets macOS computer systems and promotes searchbaron.com. This fake search engine is known to provide search results from another legitimate provider – Bing by employing Amazon AWS Service. Furthermore, this is just a small part that ScreenSaver.app might be capable of. Adware programs are known for their advanced advertising skills that force various pop-up notifications straight on the user's computer screen and cause redirects during browsing sessions when web browsers such as Chrome, Firefox, and Safari get infected.
| Name | ScreenSaver.app |
|---|---|
| Type | Potentially unwanted program |
| Sub-type | Adware application |
| Mission | To promote other potentially unwanted applications such as searchbaron.com via Amazon AWS Service |
| OS-based | This suspicious application targets macOS computer systems and appears in the Applications folder |
| Web browsers | You might find browser helper objects in browser apps such as Chrome, Firefox, and Safari |
| Deletion | Use anti-malware software or make use of manual removal guide below |
| Optimization | To recover from PUP infection and ensure your Mac is running smoothly, use FortectIntego |
ScreenSaver.app virus can appear in the Applications folder of a Mac machine and even create its own folder named “ScreenSaver”. Afterward, the adware hijacks browsers and installs major changes in the homepage and new tab search sections. Also, the program might add suspicious extensions, add-ons, and tracking objects.
Collecting non-personal information is another activity highly promoted by ScreenSaver.app and similar adware. The developers use browser cookies to track information related to users' online sessions and habits. The adware might be able to record data such as the IP number, saved bookmarks, websites entered, links/ads clicked, etc.
Afterward, ScreenSaver.app might use the information for delivering targeted advertisements. Do not be surprised is you get loaded with various offers to purchase rogue security software, just decline all of them. Besides, be careful not to get lured in various technical support scams or surveys/questionnaires.
Some parties provide surveys that require entering personally-identifiable information. We recommend avoiding any type of content that comes from ScreenSaver.app as there is no chance that it would be reliable. Besides, do not provide sensitive data to bogus sources as you might experience identity theft in the upcoming future.
ScreenSaver.app removal is the best option here to prevent unwanted activities from continuing. Removing the PUP might be an easier task if you scan the entire system in search of suspicious content first. After that, we recommend you employ FortectIntego to ensure best results after the infection.
Continuously, you can successfully remove ScreenSaver.app from your macOS and web browsers by carrying out the process in manual technique. Scroll down to the end of the article and there you will find manual guiding steps that should help you to get rid of the ad-supported application by yourself.
Avoiding adware is necessary if wanting to ensure full system stability
Injection of PUPs might decrease your computer's safety level as together with an adware program alongside comes the risk of highly-developed infections such as trojan or ransomware-related ones. However, in order to avoid third-party apps, you need to gain knowledge on how do they reach the targeted computer system. According to research, there might be several ways for a PUP to land on a machine/device:
- Software bundling. A lot of third-party developers employ this deceptive technique so that it could work for their own needs. Bundled freeware comes together with the adware and sneaks into the computer system when the user opts for the Basic/Recommended installation option. To secure your downloads, change the configuration to Custom/Advanced.
- Third-party ads/links. There are many unsecured sources all over the Internet that might promote suspicious applications by attractively advertising them. Avoid clicking on questionable content that is provided to you on the web.
- Fake updates. If you are a frequent visitor of third-party networks, you might be provided with fake adobe flash player upgrades. Do not get tricked by such content and if you ever get concerned about some type of software update, you can check it online.
- Software cracks.[2] If you like downloading products and services from p2p networks and various torrenting websites, you are very likely to end with an additional PUP. Skip these types of pages and get your software only from reliable sources and trustworthy developers.
Additionally, you should employ an AV tool for ultimate system protection. Choose reliable software to secure your computing and browsing work automatically. Antimalware products are able to block access to malicious websites, alert when something bad is happening, and prevent suspicious threats from reaching your machine.
The removal process of ScreenSaver.app from macOS
You can remove ScreenSaver.app from your macOS machine with the help of antimalware products or by using step-by-step guidelines that have been added to the end of this article. Keep in mind that the adware might fill your browsers with unexpected material that also needs to be eliminated in order to get rid of the cyber threat properly.
ScreenSaver.app removal requires full attention of the user and at least a little bit of experience in the cybersecurity sphere. According to experts from LosVirus.es,[3] it is necessary to clean every part of your machine and browser, otherwise, the ad-supported application might renew itself within the next start process.
If you think that you would not be able to uninstall ScreenSaver.app virus from your computer on your own, you should employ antivirus software and let the tool to complete the task for you. The result would be much more effective.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of ScreenSaver.app. Follow these steps
Delete from macOS
To clean your macOS computer from suspicious programs, perform the following tasks
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Mozilla Firefox (FF)
To erase unwanted content from Mozilla Firefox, carry out these steps
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
To free Google Chrome from questionable components, try out the following
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
To delete questionable products from Safari, complete these guidelines
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of ScreenSaver.app registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ What is Adware?. Kaspersky Lab. Resource center.
- ^ Crack. Techopedia. Tech terms and definitions.
- ^ LosVirus.es. LosVirus. Security and spyware news.
