Seto ransomware (Removal Guide) - Sep 2019 update
Seto virus Removal Guide
What is Seto ransomware?
Seto – a malicious ransomware strain that ends up on Windows systems through hacked RDPs

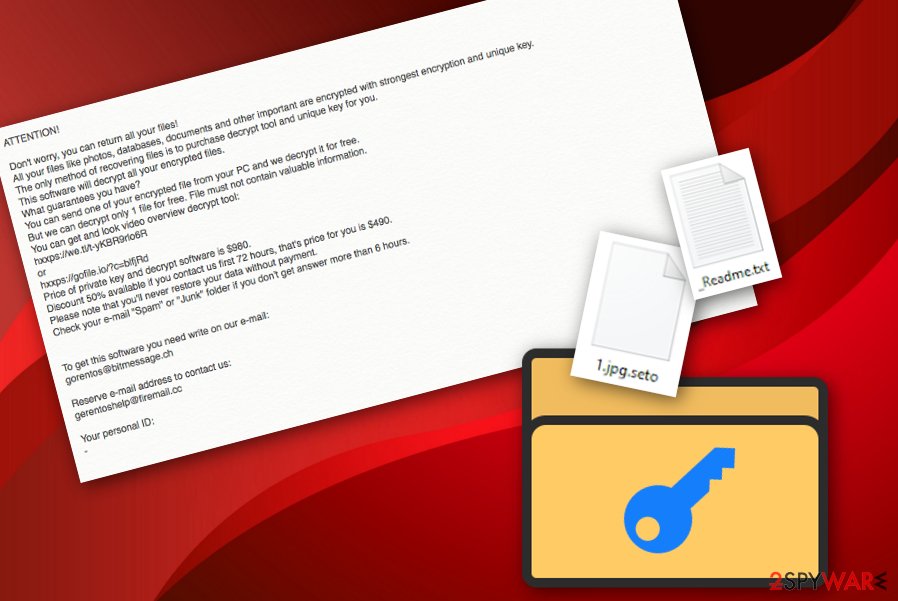
Seto ransomware, first discovered by a computer security researcher named GrujaRS, is a malicious version of the Djvu ransomware family that includes multiple operating features. If you are a frequent technology news follower, you should have already noticed that the Djvu and STOP ransomware families have been updated to prevent security researchers from helping people restore their files for free. Seto is one of the first viruses that is using advanced asymmetric encryption[1] to lock files such as pptx, docx, doc, jpg, png, zip, xlsx, xls, etc., and leaves data unavailable for usage. Additionally, it appends the .seto file extension and _readme.txt ransom message that informs users about the successful encryption process.[2] Finally, the victim is encouraged to pay $490 for the decryption tool as a 50% discount from the starter price – $980.
Seto also has interesting distribution tactics. According to experts' reports, this malware is capable of placing itself on the targeted system through a hacked RDP, known as TCP port 3389. In addition, the virus might reside on the machine after downloading some bogus security products such as IOBIT Driver Booster PRO installers, misuse some system or software flaws to end up on the machine or travel through misleading email texts that falsely claim to be from reputable shipping organizations (e.g. FedEx), banking companies, and other firms.
| Name | Seto |
|---|---|
| Type | Ransomware virus |
| Family | Djvu ransomware and STOP ransomware are two families to which Seto malware also belongs |
| Appendix | The notorious malware strain appends the .seto appendix to all locked files and documents that are found on the infected machine |
| Note | _readme.txt is the ransom-urging message where cybercriminals explain all purposes in order to receive the decryption software |
| Price | $490 for the start and doubled if no communication is made between a three day time period |
| Features | Locking files that are found on the infected machine, injecting other malware strains such as the AZORult trojan, deleting Shadow Volume copies, etc. |
| Spreading | RDPs, especially the TCP port 3389, fake email messages from reputable shipping companies, banking organizations, and similar |
| Detection | Try using a program such as FortectIntego for spotting all malicious components that have been placed by Seto virus on your computer system |
| File recovery | Unfortunately, STOPDecrypter does not work with this version. Follow Seto recovery steps from here. |
Seto ransomware is a tricky one also. It gives only three days to transfer the $490 ransom price, or, according to the claims, the price will be doubled and the victims will have to spend almost $1000 to receive the decryption software. However, paying neither price is recommendable as you might find yourself scammed at the very end.
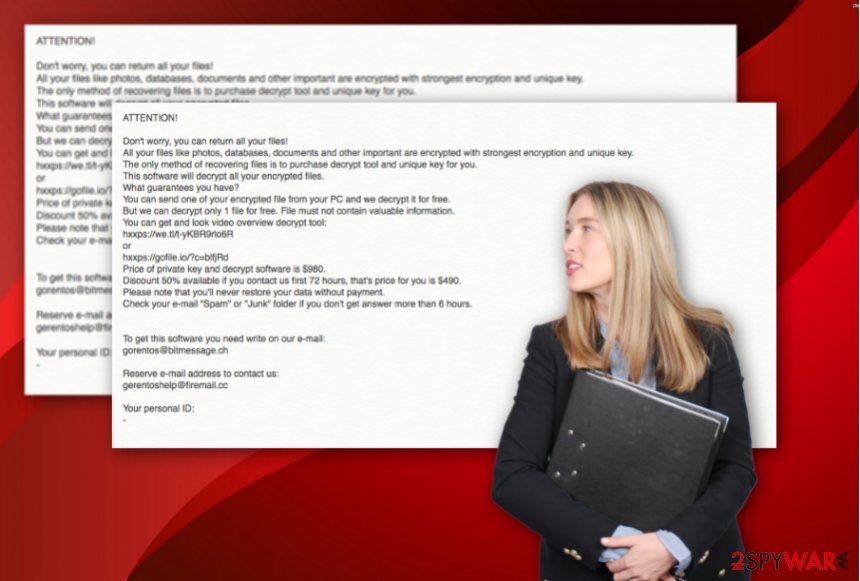
Criminals who use Seto and similar malware for gaining income do not think about the good for other people as if they would have thought about others, none of this attacking activity would have ever started at the first place. Besides, we recommend going to the bottom of the page and viewing possible decryption solutions there. If you ever deal with this malware, note that it will urge for money via this type of text message:
ATTENTION!
Don't worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-yKBR9rlo6R
or
hxxps://gofile.io/?c=blfjRd
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
gorentos@bitmessage.chReserve e-mail address to contact us:
gerentoshelp@firemail.ccYour personal ID:
–
Seto uses unique keys to lock up all targeted files and leaves them inaccessible for the purpose of receiving ransom payments. According to the criminals, they can be reached in three ways. You can write these people via gorentos@bitmessage.ch, gerentoshelp@firemail.ccc email addresses or via @datarestore Telegram name.
Note that you will supposedly overcome the _readme.txt ransom message planted not only on your desktop but in all other folders that have files with the .seto appendix also. As you can see, Seto ransomware definitely wants to make himself frequently spotted from every direction possible.
We DO NOT recommend agreeing to pay any type of ransom demand as it is a huge number and you face a big risk of being scammed. Even though files that have been encrypted by Seto ransomware are not decryptable yet, you can still try restoring some of the data back to their primary states by following guidelines at the end of this web article.
Continuously, we have searched the web and found out that DrWeb might be capable of decrypting some Djvu ransomware-related files that cannot be reversed by the STOP decryptor. In addition, DrWeb specialists offer a Rescue Pack if the free encryption appeared successful.[3] This package includes a personal decryption tool and 2 years of DrWeb Security Space protection for the price of $150.
However, before you start searching for data restoring possibilities, you need to put the Seto ransomware removal process as your top priority as if you do not get rid of the cyber threat first, file recovery will be useless and your data will remain locked as the malicious code will still be placed on your system and running active.
Seto ransomware is a threat that does not reside just in one place. Usually, malware skaters all around the targeted computer system and leaves bogus products in directories such as the Windows Registry, Task Manager, etc. Such keys and files allow the ransomware virus to execute and run its malicious code.
Keep in mind that you should no try to remove Seto ransomware without any help of automatical software. At least use a tool such as FortectIntego or SpyHunter 5Combo Cleaner for investigating the entire computer system. Locating malware strains on your computer will allow you to get a better view on which directories need to be fully cleaned.
Be aware that the detection name of Seto ransomware might differ depending on the type of antimalware program that you are using. Here are the detection names provided by some popular antivirus products:[4]
- Trojan.MalPack.GS (Malwarebytes).
- Trojan.GenericKD.41690750 (B) (Emsisoft).
- Trojan.GenericKD.41690750 (Bitdefender).
- Win32:DropperX-gen [Drp] (AVG and Avast).
- Trojan.Encoder.26996 (DrWeb).
Additional harmful features that might be included in the operating module of Seto ransomware
Ransomware infections themselves have a dangerous nature regarding the ability to lock all files found. However, some malware developers find even more ways to use the ransomware for benefiting their own needs. Sometimes, viruses such as Seto ransomware might be two (or more) different malware strains in one package.
For example, it is known that all STOP ransomware variants might distribute the AZORult Trojan horse. Trojan viruses[5] might be used for cryptocurrency mining, data stealing, and money swindling purposes. Also, if infected with this malware, you might face machine damage. So, Seto ransomware might also be one of the distributors of this malicious payload.
In addition, Seto ransomware might be capable of deleting Shadow Volume Copies of encrypted files in order to harden the data recovery process and encourage users to purchase the decryption tool from the criminals. However, do not be frightened as there are other ways how to restore data files without using Shadow Copies.
However, Seto virus, like all other Djvu variants is able to modify Windows hosts file. This is done to ensure that browser apps will not launch any websites or forums that are antivirus-related and the users will not be able to get any help. So, while performing the malware elimination, ensure that the damaged hosts component is also successfully removed.[6]
RDPs, email spam, software/system flaws – the most popular ransomware distribution places
Developers who promote ransomware infections discover various ways to inject malicious payload into the system. In some cases, crooks misuse Remote Desktop Protocol[7], for example, the popular TCP port 3389 by hacking it and forcibly entering the password in order to connect to the hacked machine.
Email spam campaigns are also one of the easiest and commonly used ways to distribute malware and this includes ransomware viruses also. Crooks drop malicious payload to random users inboxes or spam sections and leave a questionable executable, JavaScript, PDF, or Word file attached to the message.
According to LesVirus.fr experts,[8] this is the place where the virus is located. If the user tends to open or download the file, he/she launches the malicious payload straight onto the system. Bad actors pretend to be from reputable banking companies, shipping firms, and similar organizations.
Try not to get tricked by reputable-looking messages and always verify your expectations of receiving particular emails. Last but not least, the malicious payload can be carried straight to the system through software or computer flaws that allow hackers to enter the machine without big effort. Also, reports claim that crooks manage to inject the malware by using IOBIT Driver Booster PRO installers and similar bogus products.
Our point would be to always be careful while completing computing or browsing actions as danger might be hiding anywhere. However, you should not go without help from reputable antimalware software. Choose a trustworthy antivirus tool that will protect your system and its components daily.
Seto ransomware removal steps for every user
The best way to remove Seto ransomware is by employing specific security tools. Do not try to get rid of the cyber threat by your own as you might end up with only more damage or just not be able to eliminate the virus entirely. Antimalware software that is chosen properly will ensure that the entire process is completed with the best care and that all malicious strains vanish at once.
After the Seto ransomware removal process is finished, you can continue with the data recovery steps that we have provided below. In addition, we want to inform all users that DrWeb might have a chance of decrypting some files, so you can try using their services also. For example, the company offers to purchase their Rescue Pack which includes a personal decryptor and two-year computer protection for $150.
Additionally, you need to make sure that such encryption does not repeatedly happen in the future. For this purpose, ensure that you store copies of important documents on a remote server such as iCloud[9] or Dropbox. Also, you can keep your files safely on a USB device and prevent Seto ransomware and similar malware attacks.
Visual guidelines to help you get rid of Seto faster
We also have created a video-based removal process for Seto ransomware that should help users who like to watch things being done step by step. 2-spyware computer specialists have made the visual material look as simple as possible and help to guide you through the entire task. Down below you will find the video clip:
Getting rid of Seto virus. Follow these steps
Manual removal using Safe Mode
Activate Safe Mode with Networking to disable malicious processes that are ongoing on your computer system:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Seto using System Restore
Launch System Restore to bring your computer back to its previous state. Follow these steps:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Seto. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Seto from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Seto, you can use several methods to restore them:
Data Recovery Pro is a tool for data restoring:
Use this software for bringing your files and data back to their previous positions. Follow every step exactly as required in order to succeed.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Seto ransomware;
- Restore them.
Use Windows Previous Versions feature for data restoring activities:
If you have rebooted your computer system to System Restore in the past, you should give this method a try as you have a chance of experiencing great success.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Employ Shadow Explorer for file recovery tasks:
If Seto ransomware virus did not get in time to eliminate Shadow Volume Copies of your encrypted documents, you can give this piece of software a try.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No official decryptor has yet been released for Seto malware. We are looking forward to receiving updates on the decryption software one day.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Seto and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Josh Lake. What is AES encryption and how does it work?. Comparitech. Blog information.
- ^ Encryption. WIkipedia. The free encyclopedia.
- ^ Submit a request. DrWeb Support. Tech info.
- ^ 53 engines detected this file. Virus total. File information.
- ^ What is a Trojan Virus?. Kaspersky. Resource center.
- ^ Seto Virus Ransomware. Emsisoft Support. Topics.
- ^ Margaret Rouse. Remote desktop protocol (RDP). Search Enterprise Desktop. Tech Target.
- ^ LesVirus.fr. LesVirus. Security news.
- ^ Daniel Nations. What Is iCloud? How Do I Use It?. Lifewire.com. An independent news source.





















