ShurL0ckr ransomware (Removal Guide) - Feb 2018 update
ShurL0ckr virus Removal Guide
What is ShurL0ckr ransomware?
ShurL0ckr – a ransomware virus that avoids detection by most of AV engines
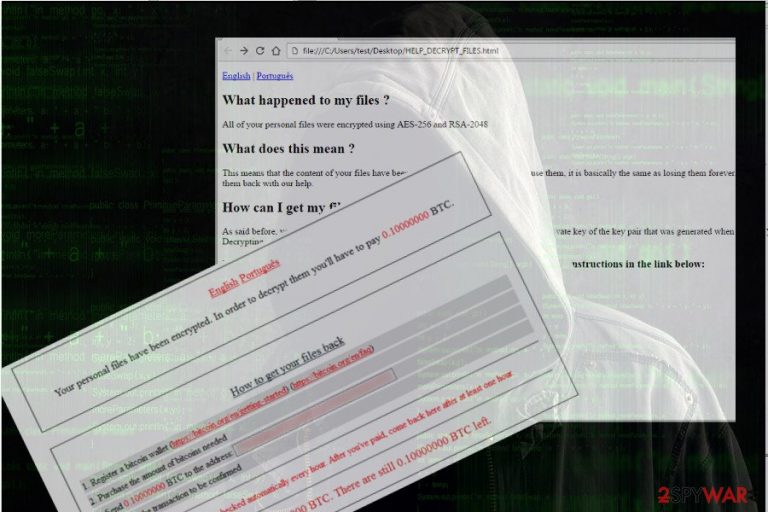
ShurL0ckr is zero-day ransomware[1] which has been detected by security broker Bitglass and Cylance at the beginning of February 2018. It was confirmed to be a new version of Gojdue ransomware and a Ransomware-as-a-Service[2] type virus. In other words, all people who want to earn money illegally by locking people's data and then demanding a ransom, can participate in the distribution of the ShurL0ckr virus.
Currently, ShurL0ckr is capable of bypassing the most of the anti-virus engines and evading well-known cloud applications, including Google Drive and Microsoft Office 365. Several tests of Bitglass on VirusTotal have revealed that only 7% of 67 tested AV engines are able to detect and remove ShurL0ckr.
As we have already mentioned, this ransomware has already been dubbed as a new version of Gojdue, though its performance coincides with Satan ransomware. However, no matter how surprising its ability to infect cloud services seems, it uses traditional distribution techniques. Mostly, it spreads around via spam when Word attachments are filled with the malicious Macros code.
ShurL0ckr virus is hazardous regarding capabilities to lock data in the cloud. The Bitglass Threat Research Team has already provided shocking test results[3] that claim that 44% of organizations have already been infected and at least one of their clouds has been locked by this ransomware. OneDrive, Google Drive, Dropbox and other cloud services with the built-in malware protection have already been found to be vulnerable to ShurL0ckr ransomware attack.
Because of the ability to evade detection by apps and services with the in-built malware protection, ShurL0ckr virus is expected to continue spreading worldwide. The amount of the ransom demanded is not clear. It might be that hackers customize the ransom fee according to the number of files encrypted or the amount of organization.
If you fall victim to this ransomware, you should remove ShurL0ckr virus from the system at first. At the moment, there are no official decrypters for this ransomware virus. Therefore, security experts do not recommend paying the ransom. Each ransom motivates hackers for further crimes, but there's no guarantee that the victim will receive a working decryptor after the transfer.
To decrypt files encrypted by the ShurL0ckr virus, you should either use backups or employ professional data recovery tools. You can find more information on data recovery methods at the end of the post. However, make sure you perform ShurL0ckr removal first. For that, use FortectIntego, SpyHunter 5Combo Cleaner, Malwarebytes or other professional anti-malware.
There's no hundred percent protection from ransomware attack
The ransomware we are talking about in this post is disseminated using the same methods as Satan ransomware. The author of the virus distributes spam email messages with a Word file attached. Such emails are sent to diverse email clients that are chosen randomly, so no one is immune from the reception of the spam. If the potential victim tries to open the file, he or she is asked to enable Macros. If the user allows for it, the ransomware executable, which is usually named as setup.exe, is launched and the virus settled down.
Also, hackers can also distribute it via phishing or a drive-by download. Once the virus is executed, it starts encrypting files and then creates a .txt file on the desktop, which is dubbed as ransom note by the security community. It explains the background of the virus and instructs the victim to pay the ransom (usually in Bitcoins via Tor browser).
Unfortunately, the golden rule that would help people to stay protected from ransomware doesn't exist. However, we suggest people not to open suspicious email messages, do not click on fishy lookings ads while browsing or downloading unknown software. You should be careful with stand-alone .exe installers.
Remove ShurL0ckr before recovering data
The Shurl0ckr virus is currently under investigation. Up until now, ransomware hunters informed people about the risk of this new zero-day ransomware attack and warned that it's capable of evading the detection by the majority of AV engines and cloud apps,[4] including those managed by Microsoft and Google.
If you are a victim of this virus, we would not recommend paying the ransomware. Since it's a newcomer to the market, it may have many flaws that can be discovered by cybersecurity experts in the nearest future.
Before that happens, we would suggest you remove Shurl0ckr ransomware from the system. Yes, all encrypted data will be wiped out with Shurl0ckr removal, but there's a chance to retrieve personal information from backups, Volume Shadow Copies or previous Windows Versions.
Getting rid of ShurL0ckr virus. Follow these steps
Manual removal using Safe Mode
Often ransomware blocks anti-virus programs. Therefore, to remove To remove Shurl0ckrreboot, you may need to reboot the system into Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove ShurL0ckr using System Restore
If the previous method did not work, try the following steps:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of ShurL0ckr. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove ShurL0ckr from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.The only way to recover the encrypted data is to use backups. If, however, you don't have them, there's a couple of methods that may help you retrieve at least the most important ones.
If your files are encrypted by ShurL0ckr, you can use several methods to restore them:
Try Data Recovery Pro
Data Recovery Pro has been developed by PC specialists to help people retrieve files lost after PC's crash or accidental deletion. Nevertheless, many people reported that it managed to unlock most of the files encrypted by ransomware, so it's worth a try.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by ShurL0ckr ransomware;
- Restore them.
Decrypt files with Windows Previous Versions feature
Windows Previous Version feature can help you to recover individual files. However, that's possible only if you have a System Restore function enabled on the system.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Recover encrypted files after Shurl0ckr ransomware arttack using ShadowExplorer
If you are dealing with a ransomware that does not remove Shadow Volume Copies, this method may work:
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Shurl0ckr decryptor is not yet available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from ShurL0ckr and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ What is ransomware and how can you prevent an attack?. Our IT department. GDPR service provider.
- ^ Sentinel One. Ransomware as a Service: Hacking Made Easy. CSO. Enterprise security decision-makers.
- ^ Bitglass Report: Microsoft SharePoint, Google Drive, and Majority of AV Engines Fail to Detect New Ransomware Variant. Bitglass. Cloud Access Security Broker.
- ^ Gavin Phillips . SECURITY Yes, Ransomware Can Encrypt Your Cloud Storage. MakeUseOf. Technology website.







