Telegram virus (Removal Guide) - 2021 update
Telegram virus Removal Guide
What is Telegram virus?
Telegram virus – is the malware spreading and affecting particular social media platform
Telegram virus is a possible threat that can be found spreading via messaging applications or even pose as the program itself. This term is used to describe a new cyber threat that is created for multiple purposes. Hackers distribute the malware via entirely legitimate cloud-based messaging software. The purpose of this infection is to either drop a cryptocurrency miner or infiltrate the system with spyware and other potentially unwanted programs (PUPs) and gain remote control of the device. Unfortunately, it is tough to identify the virus as it hides its presence in the system.
The term itself might also be used by users that describe issues with other programs or affiliates with the messaging app. In general, this program is more trustworthy than other ones, especially taken recent reports into consideration.[1] However, the Telegram virus can be associated with various intruders using the popularity of this service. Hackers often make clones of applications and promote them online, so gullible people fall into the campaign and download the fake version without thinking twice.
| Name | Telegram virus |
|---|---|
| Type | Malware |
| Danger level | Medium because various threats can be distributed using the name of a legitimate application |
| Distribution | Attackers send threats via the Telegram program as a deceptive .png image file or can distribute a malicious version of the app itself |
| Symptoms | Might start exploiting CPU power, cause system freezes, and collect sensitive data. Trojans can be distributed via the hacked or cloned application |
| Removal | Due to the complexity of the malware, we recommend using anti-malware tools to remove infection safely |
| Repair | Since various files might end up on the machine and programs can trigger processes behind your back, run a tool like FortectIntego that can repair some of the damage |
Once Telegram malware enters the system, it settles inside the deepest locations on the computer and starts operating in the background. Its primary purpose is to use excessive amounts of CPU power to mine digital currency, such as Monero, ZCash, Fantomcoin, and generate profit for its developers.
Unfortunately, high CPU power usage might result in significant deterioration of the PC's performance or even permanent damage. If you fail to get rid of the the virus and leave it for long periods of time on your system, there might be the following consequences:
- Increased latency[2];
- programs start to crash;
- continuous computer freezes.
According to the experts, the particular Telegram miner might have additional features to the primary one, including opening backdoors to infiltrate the system with other potentially unwanted programs (PUPs) or using the remote control to install malware directly. Thus, if your computer is infected, you risk your private data, credentials, and essential information.
After installation, it started to operate in a silent mode, which allowed the threat actor to remain unnoticed in the network and execute different commands including the further installation of spyware tools <…>

Therefore, the best decision would be to immediately scan your computer with a professional antivirus if you have any concerns about its security. We recommend using SpyHunter 5Combo Cleaner or Malwarebytes as such tools would remove Telegram virus easily as soon as it is detected.
Note that the security software has a malware database that is continuously updated to ensure that other cyber threats would be eliminated as well. But legitimate Telegram application is not going to appear as an infection. You will see those intruders that specifically trigger damage to your machine. Also, you can run FortectIntego for the issues with corrupted or altered system parts.
If you can't start the proper virus removal, there is a substantial risk that a more severe infection has hit your system and blocked the installation of the antivirus. In this case, check the guidelines appended at the end of this article and learn how to deactivate the malware before elimination.
Various popular applications have vulnerabilities or even security issues
Recently, some features of the legitimate app were mentioned as posing risks. Users can choose to share their location with friends to find who is nearby. However, such details can be used by malicious actors who might want to find where you are exactly or even scam your group of friends.
Other software with similar purposes might be used to perform additional campaigns and even attract unwanted attention from real-life stalkers. It is an issue, but many messaging and social media applications have such features linked with location sharing. This is not a Telegram virus, but some people might use the term when describing the program due to these media reports.
Most users don't understand they are sharing their location, and perhaps their home address. If a female used that feature to chat with a local group, she can be stalked by unwanted users.
Viruses can be hidden in various ransom messages with attachments or links
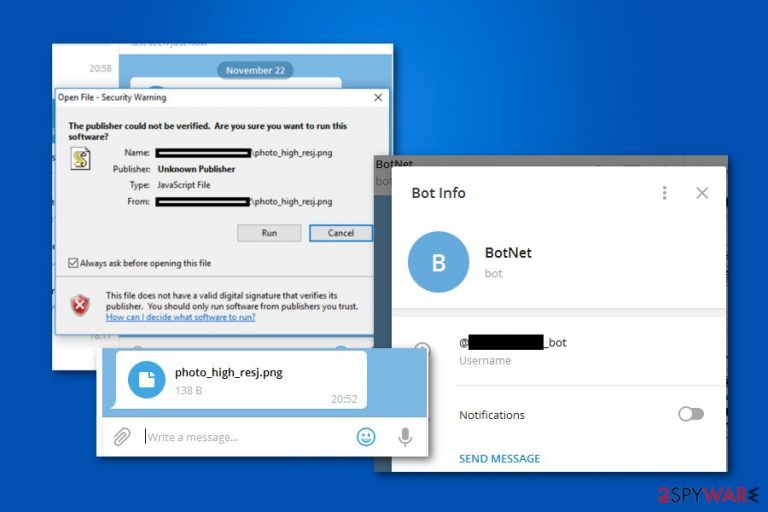
Experts have detected that the Telegram virus spreads as a JavaScript file which disguises as a PNG image during the download and installation. Distributing malware on social media platforms is not a new tactic. Yet, the attackers have slightly improved this method to make the infections more successful.
According to malware researchers, cybercriminals employed Right-to-Left Override (RLO)[3] character to force Telegram to display the counterfeit string of the file. For example, evil.js is displayed as photo_high_resj.png on the instant messaging platform.
Keep in mind that the file itself remains JavaScript and does not change to an actual PNG image. Although, criminals embed *U+202E* RLO characters to trick people into believing that the file is not malicious or potentially dangerous. Likewise, people who click on it immediately infiltrate their systems with malware.
Get rid of the virus ASAP to protect your privacy and information
NoVirus.uk[4] experts advise the users who have received a similar message or use Telegram to get help from a professional right now. It is because the researchers can't identify which products might be affected by this cyber threat.
We don’t have exact information about how long and which versions of the Telegram products were affected by the vulnerability.
As it was mentioned before, you can scan your computer files with a robust antivirus. Our top choices would be Malwarebytes, SpyHunter 5Combo Cleaner as they are designed to remove the virus and similar malicious programs within several minutes.
If you can't start Telegram virus removal because the malware is preventing you from installing the antivirus, you can follow a simple guide below. Although, please, be careful as these infections are highly sophisticated and might trick you into causing more damage to your PC. Do not alter system settings yourself, go for FortectIntego or a similar optimizer that helps with file damage.
Getting rid of Telegram virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Telegram using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Telegram. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Uninstall from Android
Uninstall unwanted programs from Android device:
- Go to Settings -> Apps/Applications.
- Expand the full list of the installed apps.
- Scroll through the list and tap on a suspicious application once.
- Tap on it and select Uninstall.
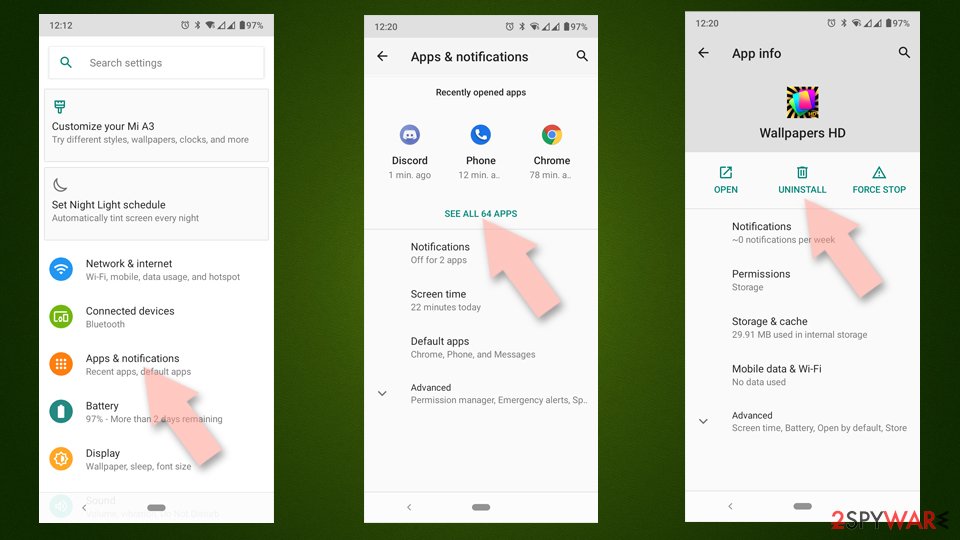
- Reboot the device.
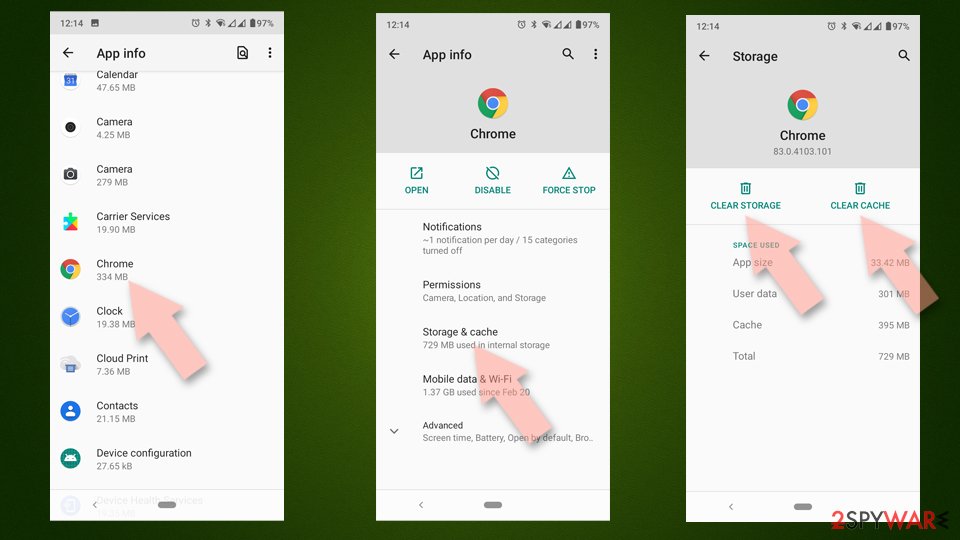
Clear Storage and data files on Android from Google Chrome or other apps:
- Go to Settings > Apps/Applications.
- Expand the full list of the installed apps.
- Tap on Chrome and select Storage & cache.
- Clear storage and clear cache of the app.
If you are seeing ads on top of other apps but are not sure what is causing it, perform the following steps:
- Go to Apps/Applications.
- Tap Advanced.
- Select Special App access.
- Tap on Display over other apps.
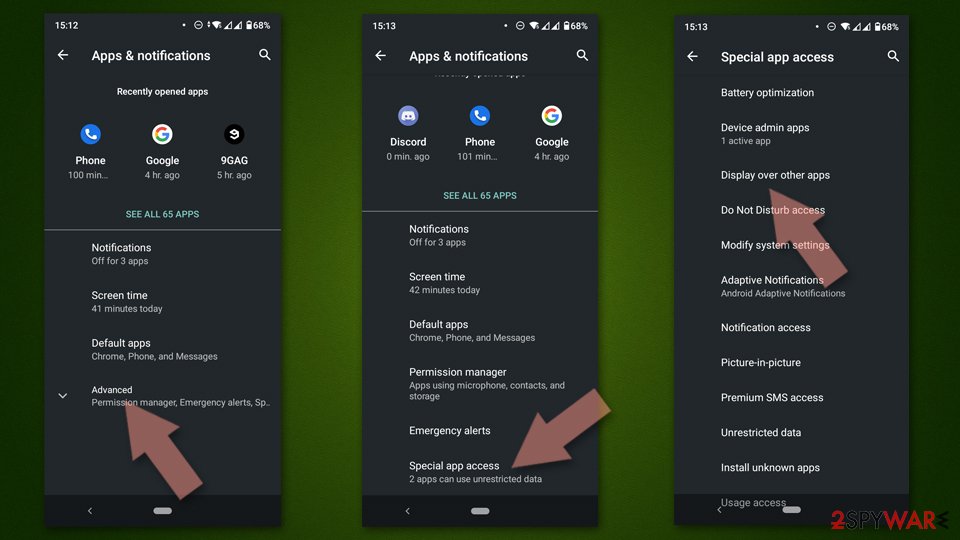
- Eliminate apps with these access rights enabled.
How to prevent from getting malware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Abeerah Hashim. WhatsApp vs Telegram vs Signal – Which One Is More Secure?. Latesthackingnews. IT and security reports.
- ^ Margaret Rouse. Latency. TechTarget. Computer Glossary, Computer Terms.
- ^ Spoof Using Right to Left Override (RTLO) Technique. InfoSec Institute. IT resources.
- ^ NoVirus. NoVirus. Security and Spyware News.







