Text Info adware (virus) - Free Instructions
Text Info adware Removal Guide
What is Text Info adware?
Text Info is an adware-type application that inserts advertisements to the pages you browse

Text Info is yet another browser extension you may come across accidentally. Its main purpose is to ensure that the affected users are exposed to all types of advertisements, including pop-ups, banners, coupons, deals, offers, etc. This is one of the main reasons the app is considered adware.
The description of Text Info adware claims that it “provides selected text info of the web page,” thus some users may install it intentionally, believing that it might be useful. However, this function is a mere disguise, and the main goal of the app developers is to earn revenue via the pay-per-click[1] advertising scheme.
Besides intrusive ads, the adware may also collect various user data, which may pose a direct risk to user privacy. We always recommend removing all potentially unwanted programs from the system as soon as they are detected. Below we provide a comprehensive guide on how to do that.
| Name | Text Info |
| Type | Adware, potentially unwanted application |
| Distribution | Software bundling, third-party websites, misleading ads |
| Symptoms | Increased likelihood of encountering pop-ups, banners, in-text links, and other ads while browsing the web; exposure to phishing material |
| Risks | Installation of potentially unwanted software; redirects can also lead to other malicious websites, resulting in financial losses or personal data disclosure to potentially malicious parties |
| Removal | You can uninstall adware from your device manually by following the instructions below. For a quicker solution, employ SpyHunter 5Combo Cleaner anti-malware |
| Other tips | After PUP elimination, make sure you clean your browsers to prevent data tracking. FortectIntego can significantly quicken this process |
Distribution and tips for avoidance
Adware is a type of potentially unwanted or even dangerous software that spreads in deceptive ways. This is why so many users might find the Text Info app installed without their permission, and the discovery would be rather a surprise. Below you will find two main ways how adware is spread and how to avoid it.
- Software bundling is one of the most prominent techniques used by PUP distributors to spread them. Third-party sources that host shareware/freeware are well-known for practicing bundling, so much so that you should expect almost any installer to include optional apps.
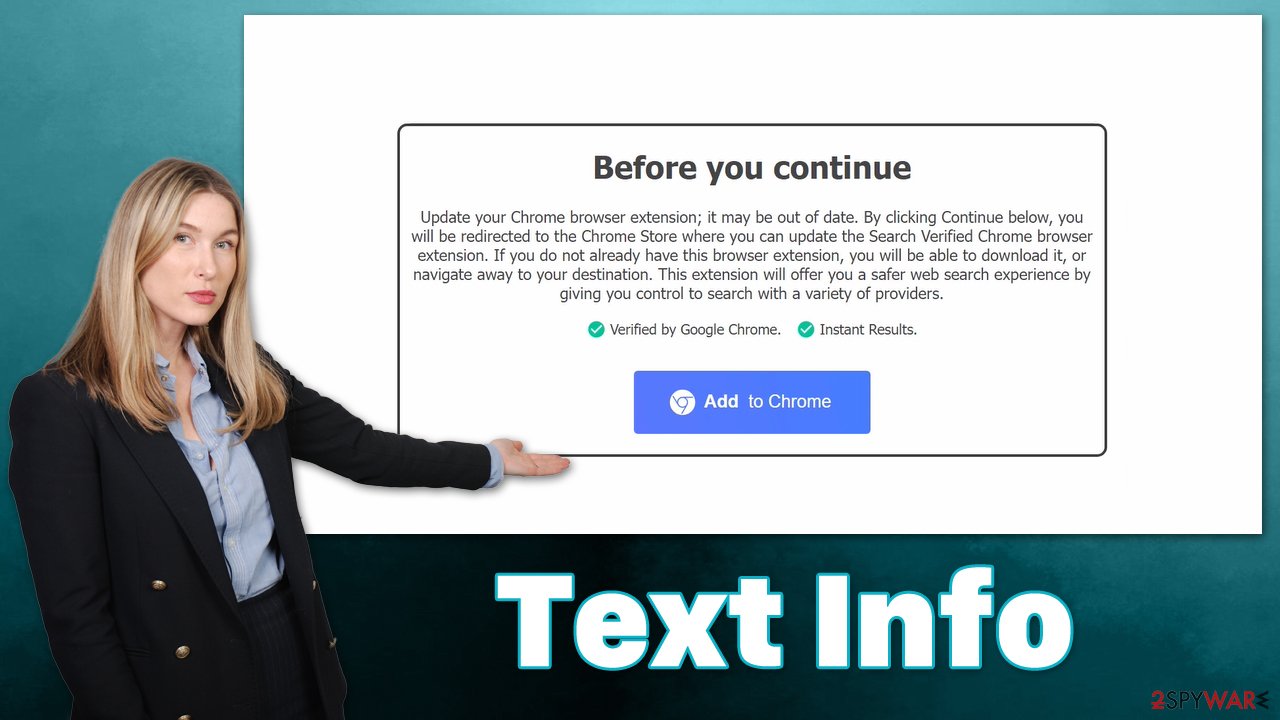
To avoid being affected by this, we recommend you always pay close attention to the installation process of new apps, especially if they are downloaded from unofficial websites. Always choose Advanced or Custom settings instead of Recommended/Quick ones, remove the ticks from the pre-ticked checkboxes, read the fine print, and never rush through the installation steps. - Deceptive ads is another popular method of adware distribution. In particular, fake software updates or misleading claims about something missing from the system are especially effective. For example, a fake Flash Player update can often ask users to install PUPs or even malware.
In reality, Flash was already discontinued by its developer Adobe a few years ago, and all requests to install or update it are fake. Likewise, other popular app names, such as Google Chrome, are also commonly used in scam schemes like these.
Why you shouldn't trust adware apps
There are millions of apps available to download, especially when it comes to multiple platforms. It is often difficult to say which applications are useful and trustworthy, especially if they aren't downloaded from official sources or are less known in general. This is why many users install potentially unwanted programs without knowing about the negative impact it can have on one's browsing quality and even computer security.
Fake features
Adware and browser hijackers are often advertised as useful apps which can be beneficial due to some type of feature. For example, apps like “BlockAll – block ads” might seem like a good addition to the browser, as its title implies it can block ads effectively. What people don't know is that the app spreads via fake updates and inserts its own advertisements everywhere.
Thus, adware is often deceptive when it comes to disclosing the full extent of what it can and can't do. In some cases, potentially unwanted apps completely fail to fulfill their promises, as we have seen with Fast PDF Reader, YouPDFSearch, BestMapSearch, and many others.
Potentially dangerous ads
Adware operates in a deceptive manner because its developers only care about ad revenue. Unfortunately, using insecure advertising networks is always something that adware was known for, which results in users being exposed to phishing messages, scam websites, or prompts to download other PUPs/malware.
Data gathering
Adware also almost always gathers information about users who have it installed on their systems. Data collection is particularly important because it allows advertisers to benefit from targeted advertising,[2] increasing the likelihood of users purchasing items or subscribing to services more relevant to them. Unfortunately, this increases the risk of data disclosure to unknown parties, as no means of data protection can be failproof.
Text Info adware removal
There are plenty of reasons to remove potentially unwanted software from your device – it can increase your privacy and increase the quality of browsing without having to deal with intrusive and potentially dangerous ads. In order to get rid of the Text Info virus, you have to access browser settings and delete the relevant extension:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
To ensure that your system is not infected with other potentially unwanted programs or malware, we recommend you perform a full system scan with SpyHunter 5Combo Cleaner, Malwarebytes, or another powerful anti-malware. Likewise, removing cookies[3] and other web data from the browser is highly recommended, as it can prevent further data tracking by third parties. You can either use FortectIntego to quickly do this or proceed with the manual steps below.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Pay-per-click. Wikipedia. The free encyclopedia.
- ^ Yossi Spiegel. Commercial software, adware, and consumer privacy. TAU. International Journal of Industrial Organization.
- ^ What are Cookies?. Kaspersky. Security research blog.








