Thepharmadds.com ads (fake) - Free Instructions
Thepharmadds.com ads Removal Guide
What is Thepharmadds.com ads?
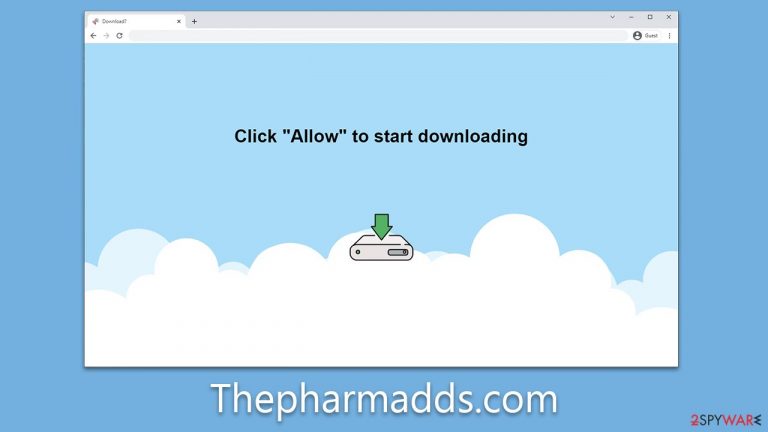
Thepharmadds.com ads show up due to unintentionally enabled push notifications
Thepharmadds.com is a notorious push notification scam site that deftly tricks internet users into subscribing to its services. Unwittingly, individuals may stumble upon this site and find themselves in a web of intrusive advertisements and deceptive content.
Once subscribed, users are bombarded with persistent and unwelcome pop-up notifications. These notifications infiltrate their browsing experience, surfacing irrespective of their current online activities. Alarmingly, these pop-ups contain misleading messages that can be severely detrimental. These range from faux virus infection alerts designed to incite panic to deceptive claims of lottery winnings aiming to lure in the susceptible.
Beyond just an annoyance, Thepharmadds.com employs a classic phishing tactic to exploit its victims. It presents fabricated security threats and offers false solutions, creating a plausible scenario for users to unwittingly divulge sensitive information. Understanding the modus operandi of such scam sites is vital for safeguarding our digital lives. In this article, we delve deeper into the dangerous realm of Thepharmadds.com, shedding light on its tactics and offering guidance on how to stay protected.
| Name | Thepharmadds.com |
| Type | Push notifications, ads, pop-ups, scam |
| Distribution | Intrusive pop-ups can start showing up at some point after the “Allow” button is pressed within the notification prompt |
| Symptoms | Pop-up notifications are shown on a desktop at random times |
| Risks | The advertisements displayed in push notifications could potentially contain deceptive content and direct you to harmful websites. Should you click on these, you run the risk of exposing your system to malware, revealing your personal details, or even losing funds |
| Removal | Navigate to your browser's settings to halt unwanted push notifications. Subsequently, ensure your system hasn't been compromised by adware or malware by running a scan with SpyHunter 5Combo Cleaner |
| Repair & tips | You should check your system with FortectIntego to fix virus damage and remove various trackers from your browsers |
Accidental access might contribute to the scam's success
While the internet has revolutionized how we interact and access information, it also has a dark side, marked by cyber fraud. Due to its vast and dynamic nature, the internet hosts an unpredictable landscape where scam websites like Thepharmadds.com can spring up and wreak havoc, victimizing numerous individuals in a startlingly short span.
This menace is often abetted by rogue advertising networks and under-regulated websites that distribute or host hazardous content. This could include malicious ads, infected files, or deceptive 'Download' links, amplifying the reach of scammers.
Particularly perilous are websites offering illicit content such as pirated software or torrent cracks. Not only can these sites redirect you to phishing pages, but they can also act as conduits for malware infection, making interaction with them fraught with risk.
Moreover, adware, a potentially harmful software type, often exacerbates this issue. Operating in the background, the adware can interfere with your browsing experience by overlaying ads on other content or embedding links in text messages. This makes users more susceptible to landing on dubious sites while the threat persists. Being cautious when navigating these sites is paramount to maintaining a safe browsing experience.
How scammers succeed
In the labyrinthine world of cyber threats, phishing and social engineering represent two of the most pervasive tactics employed by cybercriminals. Phishing involves tricking users into divulging sensitive information, often through deceptive emails or websites masquerading as trustworthy entities.
Meanwhile, social engineering involves manipulating individuals into carrying out specific actions or divulging confidential data. Together, these two methods create a dangerous nexus that leverages psychological manipulation to exploit digital vulnerabilities, setting the stage for the devious machinations of scam sites like Thepharmadds.com.
Visitors to Thepharmadds.com are frequently caught off guard by an unexpected request for age confirmation or robotic check – a seemingly innocent query that's common on the internet today. However, this seemingly benign request masks a sinister ploy aimed at tricking unsuspecting users, with its sudden appearance often causing individuals to fall into the trap.
Scammers exploit a lack of context to mislead users into expecting an event – such as the playback of a video or a prize-winning opportunity. Here are some examples to illustrate this manipulation tactic:
- Click Allow to watch the video
- Browser verification in progress – click the button “Allow” to access
- Press “Allow” bot verify, that you are not robot
- If you are 18+, click Allow
- Click “Allow” to win a prize and get it in our shop!

In essence, scammers hijack the notification prompt, capitalizing on user familiarity with age verification through captchas and sowing confusion. They lure victims with hollow promises of video content or unobtainable rewards, manipulating their desire for instant gratification.
It's important to reiterate that these sites offer no value, and their messages should be disregarded. If you've inadvertently enabled push notifications from the site, there's little reason to panic. As long as you refrain from clicking on any pop-ups, your safety should be ensured.
Thepharmadds.com ads removal
In order to eradicate the intrusive pop-up ads, it's imperative to navigate to the settings area of your web browser. Though push notifications themselves don't pose a direct threat, the links embedded within can carry malicious intent depending on their origin. This subtlety often renders them undetectable to anti-malware software, making manual intervention indispensable for their removal.
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.

- Locate the web address in question under Allowed sites and pick Remove.
Check the system for adware or other malware
When encountering sites like Thepharmadds.com, users risk exposure to adware or other malicious infections. To counteract this threat, performing a comprehensive system scan with potent anti-malware programs such as SpyHunter 5Combo Cleaner or Malwarebytes is recommended. These security tools are adept at detecting and purging all threats efficiently. However, it's crucial to ensure your security database is current before initiating the scan.
Subsequent to the malware removal, it's advisable to cleanse your web browsers and delete any remaining files that might facilitate advertising resurgence or data tracking by external entities. A PC repair tool like FortectIntego can be instrumental in this process. This tool not only helps expunge malware-induced damage but also mitigates system issues. As a result, it prevents problems like the dreaded Blue Screen of Death crashes and registry errors, promoting smoother and safer computer operations.
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
