Topeditsolutions.com ads (scam) - Free Instructions
Topeditsolutions.com ads Removal Guide
What is Topeditsolutions.com ads?
Topeditsolutions.com is a scam website that attempts to trick every visitor in malicious ways
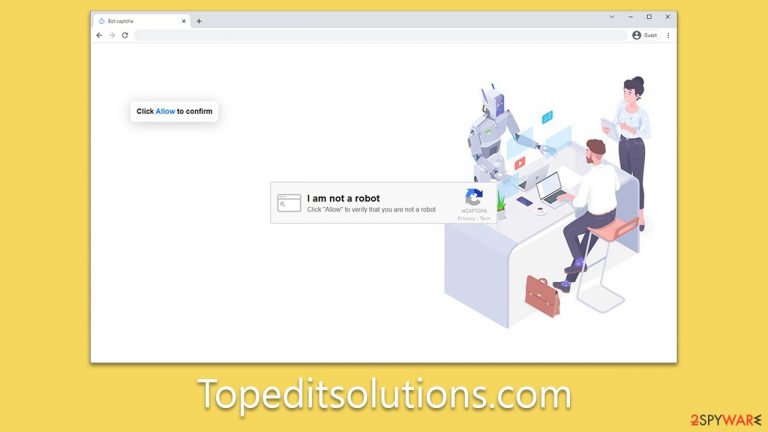
Topeditsolutions.com is a website made and operated by online scammers. Their main scheme is tricking individuals into subscribing to their push notifications. Once subscribed, the scammers use these notifications as a channel to disperse numerous malicious advertisements straight to users' screens. Often, users might not even recall the site's name until they are bombarded with intrusive pop-ups, overshadowing all other application windows on their screen. Typically, these notifications surface on either the top-right or bottom-right corner of the display, depending on the system used.
Even if a browser isn't actively in use, as long as it's running, Topeditsolutions.com's push notifications can function. Users might be engrossed in unrelated websites or multimedia while having the browser active in the background and still be subjected to these ads. Alarmingly, these ads can carry potentially harmful content, serving users with deceitful virus warnings, dubious get-rich-quick schemes, and a range of phishing content.
We urge utmost caution to avoid engaging with any links within these push notifications. Interacting with them could lead to unwarranted installation of malicious software on your device, compromising sensitive data to cybercriminals, or falling victim to various scams. If you find it challenging to eliminate these intrusive pop-ups, please refer to the information below – we provide guidance on managing push notifications and ensuring your system's security against potential threats.
| Name | Topeditsolutions.com |
| Type | Push notifications, pop-ups, ads, scam |
| Distribution | After users click the “Allow” button within the prompt upon site entry |
| Symptoms | Push notifications show on the desktop at random time intervals. They show fraudulent content and links to potentially dangerous websites |
| Risks | Links from the site might cause you to go to harmful websites, which may result in malware infections, financial losses, or personal data exposure. |
| Removal | To prevent the site from displaying notifications to you, access the site permission section via your web browser settings – you can find more details below. We also recommend checking the system for adware with SpyHunter 5Combo Cleaner security software |
| Other tips | FortectIntego can help you when dealing with leftover adware files, for example, you can get rid of various browser trackers and fix system damage automatically |
Scamming techniques used
Push notifications provide an avenue for website authors to transmit various data to users' desktops via the browser's API, granted the users' browsers are operational, irrespective of whether they're actively in use.
While this feature serves a beneficial role for websites to market their content and for users to promptly receive the latest site updates, it's often misused for monetizing ads. Topeditsolutions.com epitomizes a site exploiting this feature, tricking users into enabling push notifications through misleading messages.
Cyber fraud is rampant, with some forms proving more harmful than others. Websites impersonating legitimate ones pose a severe threat as they cunningly con individuals into revealing login details without arousing suspicion.
Push notification scams, while not as severe, should not be overlooked. Typically, these scams stem from insecure ad networks, potentially exposing users to subsequent phishing attacks. It's imperative for everyone to stay alert to such threats and safeguard personal data from malicious actors.
Fraudsters aim to profit from ad exposure, with user clicks being their primary target. Unfortunately, the unfamiliarity of many users with push notifications, coupled with their inability to remove them, makes this a lucrative scheme for scammers. They devise elaborate, false justifications to attract more users, such as:
- Click Allow to start downloading
- Click Allow to confirm that you are not a robot
- If you are 18+, click Allow
- Click “Allow” to win the prize and get it in our shop!
- Press “Allow” to watch the video, etc.

It's evident why some users might be deceived into clicking the “Allow” button within a notification prompt. However, even if you've allowed notifications from a dubious site like Topeditsolutions.com, there's no need for panic as long as you refrain from engaging with its promoted content – these notifications can be readily deactivated.
Adware or other infections could cause redirects to Topeditsolutions.com and similar sites
While inadvertent visits to Topeditsolutions.com and similar malicious websites often result from unintentional link clicks elsewhere, adware could also serve as a catalyst for such redirects. Adware is a form of malicious software designed to deliver unwanted advertisements, usually in the form of pop-ups, to a user's system. In addition to being disruptive and annoying, adware often tracks users' online behavior to tailor the advertising content, which can be a significant breach of privacy.
Once adware infiltrates your system, it can be challenging to eliminate. Often, it burrows deeply within the system, making manual removal almost impossible. Such a presence in the system could lead to continuous redirection to questionable websites like Topeditsolutions.com, exposing users to further threats and scams.
Moreover, the persistent presence of adware and frequent redirects can lead to system degradation, causing potential system errors, crashes, and other performance issues. These problems can be persistent and interfere with regular system operation, making it even more vital to remove any adware and clean up the system as soon as possible.
To remove the adware from your system, the use of reliable security software such as SpyHunter 5Combo Cleaner or Malwarebytes is recommended. These programs can scan your device for any malicious content and eliminate it effectively. These antivirus solutions have a robust detection system that can identify hidden threats, ensuring a thorough cleansing of your device.
However, the removal of adware is only the first step in the recovery process. Once the adware has been purged, it's recommended to use a system repair tool like FortectIntego to clean your browser caches and repair potential system damage. This comprehensive cleanup can help to resolve system errors and prevent crashes, ensuring your system returns to optimal performance. Always remember regular system checks and the use of reliable security tools can significantly mitigate the risks associated with malicious software.
Removal of Topeditsolutions.com ads
Disabling unwanted push notifications is not an overly complex task, although some individuals may lack familiarity with the process to identify and deactivate them. Given that most users do not engage with these features, despite their long-term availability, they may not have previously encountered the necessity to disable them. However, following the simple steps outlined below can help in mitigating the influx of undesired ads on your screen.
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.

- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
