Torrent virus (Virus Removal Guide) - Tutorial
Torrent virus Removal Guide
What is Torrent virus?
Torrent virus is a term that describes a variety of malware that users inject via the peer-to-peer service
Torrent virus is a set of malicious applications that come from well-known BitTorrent sites or clients. Torrent files are used by several clients, such as uTorrent, BitComet, BitLord, Vuze, and many others. The peer-to-peer network is what allows users to download and upload all sorts of files between the machines. However, the servers are known to be connected to piracy, and many security experts consider sites that host torrent links particularly unsafe due to poor regulation and excessive redirecting. Additionally, the .torrent files themselves might be disguised and, for that reason, infected with malware. Finally, users can download malicious payload directly to their computers via the client. Several different virus types can be associated with Torrent virus, so we will be looking at them in this article.
| Name | Torrent virus |
| Type | Malware |
| Infiltration | Via the torrent client, malicious websites, malvertisements |
| Clients | uTorrent, BitComet, qBittorrent, BitLord, Vuze, Deluge, etc. |
| Risks | Infection of potent malware like ransomware, torjans, keyloggers, crypto-malware, etc. |
| Symptoms | Varies, depending of malware installed |
| Elimination | Use reputable anti-malware software |
| Optimization | Use FortectIntego to repair your computer after virus infection |
Many users have questioned whether or not torrents are legal. The answer is yes and no. The torrent client connects users into a large network that helps each other with file sharing and is malware-free and safe to use. However, as already mentioned, the use of this platform is often associated with pirated software, videos, music, and other content that is otherwise not free. Therefore, the use of Torrent client is legal as long as it is used to download files that are already paid for, or free.
Generally, a large portion of people uses torrents, whether it is for legal purposes or not. Nevertheless, the infections this service can bring can be extremely dangerous. There are several ways how to avoid malware while using the client, although Torrent virus removal should be the top priority if infected.
In infections that are connected with file-sharing sites may vary considerably: from potentially unwanted programs like system optimizers, driver updaters, adware programs to much more severe malware like data-stealers, banking trojans, crypto-miners, and even ransomware. Without a doubt, the instructions on how to remove Torrent virus vary depending on the infection acquired, but the uniform solution would be using anti-malware software like FortectIntego, SpyHunter 5Combo Cleaner, Malwarebytes, or other reputable AV engines.

Torrent clients often bundle software and are flagged as unsafe by some AV vendors
As mentioned above, there are multiple torrent clients available, and they can all be downloaded on official websites. One notice here: there are hundreds of fake links on the web that offer the download, but would actually result in Torrent virus infection, just as it happened with Russian BitTorrent client MediaGet.[1] Therefore, if you want to download the client safely, head to the official website.
Generally, an app like uTorrent, which is the most popular BitTorrent application in the world, is considered to be a potentially unwanted program and adware. When downloading the official client, users might often notice several optional apps offered together with the main install, and several tricks might be used to deceive users to install these additional programs.
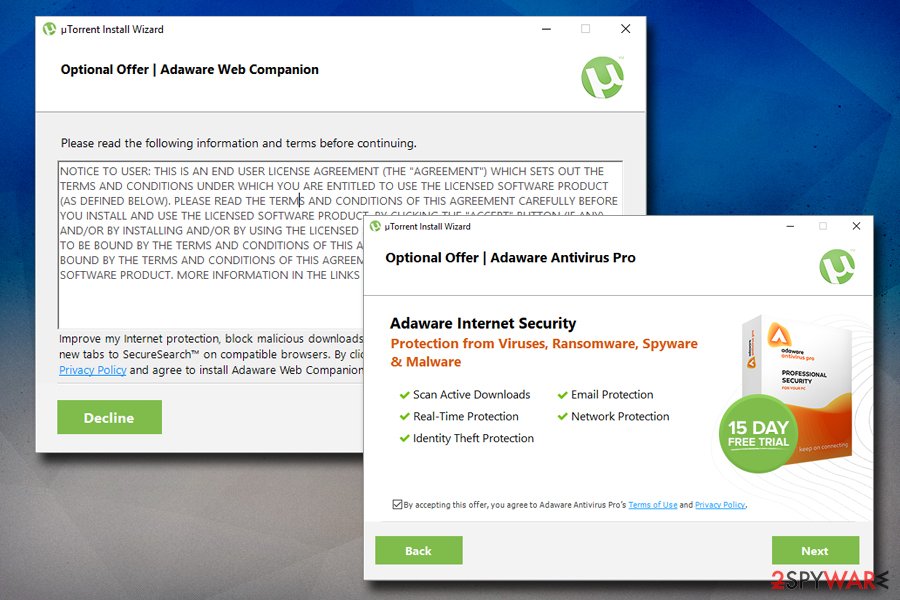
While most of the bundled software is relatively safe (for example, uTorrent often suggests installing Ad-Aware antivirus software), some apps are considered as bloatware that is entirely unnecessary for PC users (we are talking about such apps like Wajam or Value Apps). Additionally, in 2015, security experts noticed the client deceptively installing Epic Scale crypto mining software[2] that could abuse victims computer resources to mine Bitcoin, Litecoin, or another crypto.
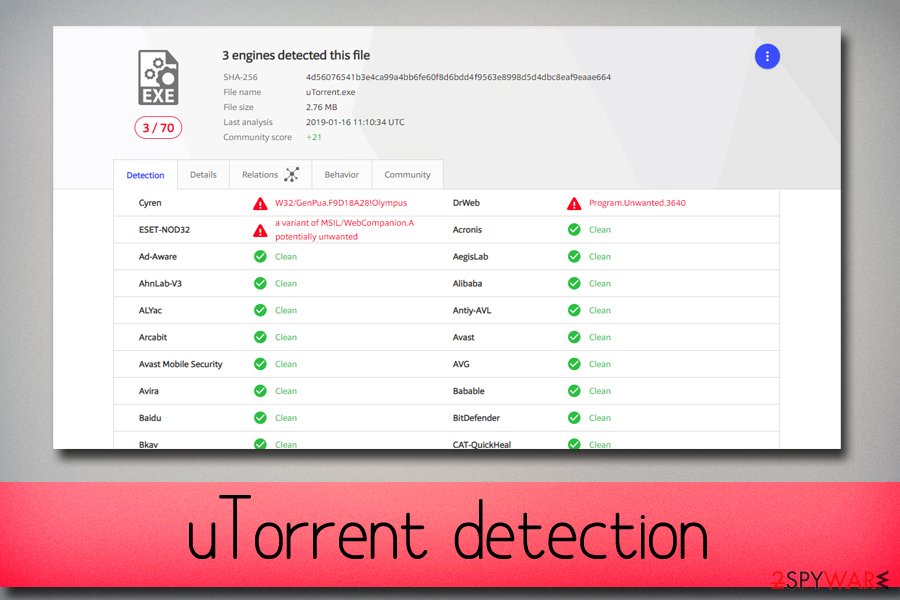
Furthermore, Torrent virus is also associated with the fact that some AV engines are recognizing the client as unsafe, and even block the official website entirely. This functionality is debated to this day, but according to VirusTotal, the uTorrent client is still detected by three anti-virus vendors.[3]
Websites that host torrent files can inject Torrent virus automatically
There are hundreds if not thousands of websites that offer .torrent file downloading service. Such sites as the Pirate Bay, Megatorrent, KickAss Torrents, and many others are well known even to those who never use the torrenting service due to scandals that these sites were involved in. However, another story of somebody going to jail is not the only reason why these sites are popular – many people use them.
As usual, hackers are prone to abuse services that are used widely, and torrent sites are known to be one of the most dangerous sites that are infested with various malware. According to research, one in three torrent sites host browser malware that exposes as many as 12 million users to various Torrent viruses.[4]
One of the most prominent ways to infect users with Torrent virus is by malvertising on the site, as these ads are very poorly regulated and the hosts remain anonymous. Symantec security researchers explain the process as follows:[5]
The infection cycle starts with the attackers creating malicious ads and injecting obfuscated JavaScript. These ads are then hosted on advertising networks across different clean domains which, in turn, compromises the users visiting those domains.
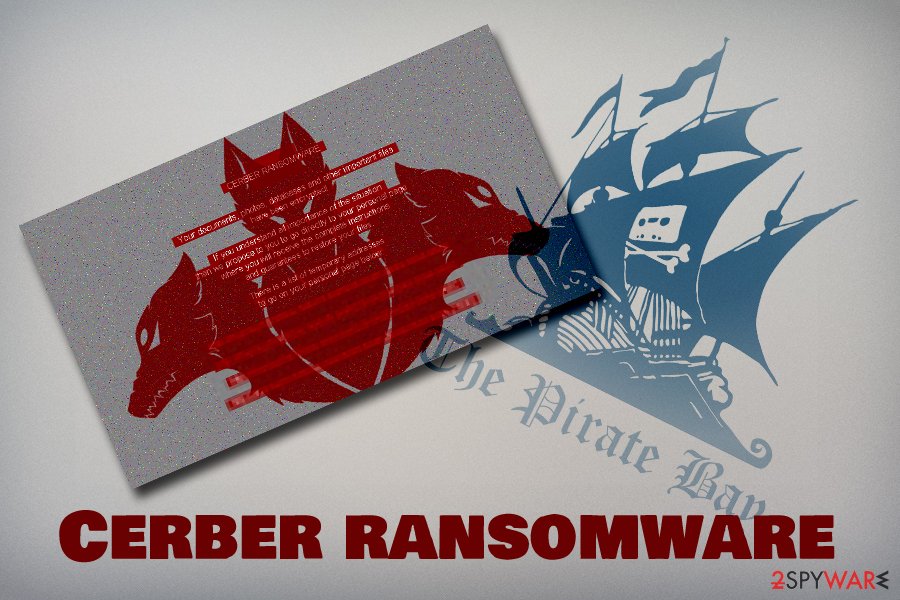
In 2016, Malwarebytes Labs found[6] that The Pirate Bay was hosting a pop-under was able to infect users with Cerber ransomware. According to research, hackers were using Magnitude exploit kit to infect machines that are vulnerable automatically. Ransomware is one of the most devastating types of computer infections as it may result in permanent data loss that is located on the device.
Quite often, users might be redirected to suspicious websites just by clicking anywhere on the torrent site, landing users on phishing, bogus software, tech support scam and similar websites, which consequently can lead to money loss or/and personal data exposure to malicious actors.
Torrent virus can be downloaded directly via the client
Another way to infect the computer with Torrent virus is by downloading malicious files directly via the client. Some of the sites that host torrent files might be even created by hackers in order to make users download Torrent virus. However, such sites are usually discarded by users quickly, and those who torrent often know which sites are safer.
Most popular torrent websites do offer some protection by marking files with “trusted upload” or similar, which means that the download is secure. Nevertheless, most users do not base their downloads on which files are considered safe but rather on what they want to download at the present time.
Therefore, if not paying close attention, users might click on something like GOTS4E2.torrent.zip which immediately indicates that the file is compressed and should not be trusted.
Some cybercriminals use other tricks to make unsuspecting users to infect their PC with Torrent virus – they add a video file that cannot be opened unless the alleged codec is installed, which is included in the download folder. The file is usually named something like codec xp-win7.exe[7] and, once clicked, executes the malicious payload.
Ways to avoid Torrent virus while using torrent networks and sites
While in some cases Torrent virus infection might not be the end of the world type of situation, some malware might be devastating. Illegal information harvesting, cryptocurrency mining or ransom demands can put most of the people in a terrible spot and result in personal file loss, money loss, or even identity theft. Not to mention, malware infections and data breaches cost millions in damages when it comes to businesses and organizations.
Generally, we advise avoiding torrent clients and websites that host the files. Nevertheless, if you are ready to put yourself through a risk based on the many examinations and statistics based on security research, you should take the following points into account:
- Install reputable anti-virus software and use Firewall;
- Use a VPN;
- Make sure your software and the operating system are running the latest versions;
- Disable Adobe Flash, Java and Microsoft Silverlight plugins. Set these to click-to-run;
- Never download or extract “cracks,” “keygens” and similar tools. Most anti-malware programs will recognize these files as malicious, and even if the file is safe, there is no way of checking it;
- Movies, music, and similar files should never be “zip” or “exe,” so never click on such files;
- Beware of “codecs” that are offered to download to open the desired file. It is most likely malware, as all modern media players can play any file – codecs are integrated;
- Run anti-virus scan or use services like Virus Total to make sure the downloaded item is not malicious;
- Before downloading torrent files, check the comments made by users – they often flag malware;
- Be aware that there are many copycat websites that try to mimic well-known sites. Check the URL to make sure you are on the correct website.
Remove Torrent virus with the help of anti-virus software
While Torrent virus removal can be performed manually, it is not recommended. Some severe infections can be impossible to eliminate unless professional software is used. Therefore, you can run such software like FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes, although there are many other programs available on the market.
Viruses are constantly evolving, and security experts are always working on solutions by adding new features to the malware removal software. Nevertheless, some viruses might not be detected by all AV engines, as they use separate databases for malware detection.
Therefore, in some cases, you will have to scan your PC with several tools in order to identify and remove Torrent virus. The safest way to do so is by entering Safe Mode with Networking as explained below. Once in the secure environment, you can run system scan safely and get rid of malicious software relatively easily.
Getting rid of Torrent virus. Follow these steps
Manual removal using Safe Mode
To remove Torrent virus successfully, we recommend entering Safe Mode with Networking – it is an environment that is ideal when it comes to dealing with malicious software:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Torrent using System Restore
System Restore can also be used to shut down the virus:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Torrent. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Torrent and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Alice Woods. Hacked BitTorrent client MediaGet infected 400k PCs with crypto-mining malware. 2-spyware. Cybersecurity news and articles.
- ^ Neil Sardesai. uTorrent Bundles Bloatware on an “Epic Scale”. Hacked. Analysis of Bitcoin, Ethereum, ICOs and Cryptocurrencies.
- ^ 4d56076541b3e4ca99a4bb6fe60f8d6bdd4f9563e8998d5d4dbc8eaf9eaae664. Virus Total. File and URL examiner.
- ^ Marshall Honorof. Torrent Sites May Expose Millions to Malware. Tom's Guide. Unbiased reviews, buyer s guides, tutorials and free software and app downloads.
- ^ Abhinav Singh. Malvertising and Dynamic DNS: A Never Ending Story. Symantec. Official Blog.
- ^ Jérôme Segura . Malvertising on The Pirate Bay drops ransomware. Malwarebytes Labs. Security blog.
- ^ Virus with torrent file, please help. Malwarebytes. Official forums.







