Trojan.gen.npe.2 (Simple Removal Guide) - Free Instructions
Trojan.gen.npe.2 Removal Guide
What is Trojan.gen.npe.2?
Trojan.gen.npe.2 – a computer threat that should not be ignored
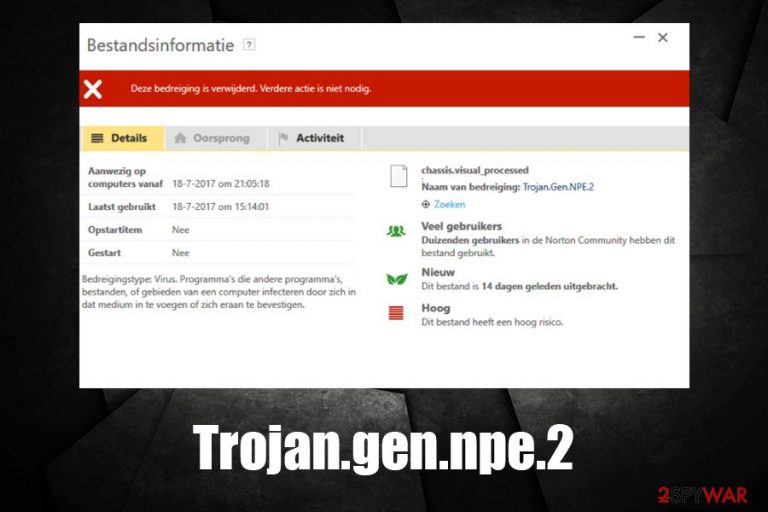
Trojan.gen.npe.2 is a heuristic detection name that can be used by security software providers, especially Symantec.[1] Because the infection name is generic, there might be a variety of different malware that is hiding behind it, including Trojans, info-stealers, or cryptominers. Due to this, the symptoms of the infection may vary greatly, although most of the malware behind Trojan.gen.npe.2 is created to operate silently in the background.
Besides its malicious properties, Trojan.gen.npe.2 virus is also known to be a false-positive, and there were instances where legitimate tools like WordPress or Windows files were flagged. This happens when a non-malicious file performs Windows system changes in order to operate and resembles malware. In case your security software flagged the infection, you should never ignore it and investigate first.
| Name | Trojan.gen.npe.2 |
| Type | Malware, false-positive |
| Infiltration | The infection might occur in various ways, as Trojans are malicious apps that pretend to be legitimate executables. These can be downloaded after being tricked by a scam, fake update, or other phishing techniques. Besides, malicious spam email attachments are also often used to proliferate Trojans |
| System impact | Malware can weaken the defenses of the Windows operating system and even corrupt some files. To recover from this, the affected users can employ FortectIntego after the virus is eliminated |
| Symptoms | Symptoms can greatly vary, as Trojans are programmed to perform different actions on the infected system. In most cases, stealthy malware will display no symptoms, although users can notice suspicious files running in the background, application crashes, mouse movements, etc. |
| Risks | Installation of other malware, sensitive data disclosure to cybercriminals, financial loss, identity theft, etc. |
| Termination | Run a full system scan with anti-malware software; if a detection is a false-positive, add it to exception list |
If Trojan.gen.npe.2 is genuine malware, it is usually a Trojan – a type of malicious software designed to perform a different variety of functions on the infected systems. These threats are spread with the help of deception – users typically believe that they are launching a legitimate file on their system (such as pirated program installer). In some cases, Trojan.gen.npe.2 Trojan might also deliver the application, but also run malicious activities in the background.
However, the presence of Trojan.gen.npe.2 malware might not be so evident, especially if no security software is used. Nevertheless, users might encounter the following symptoms:
- Software crashes
- System reboots
- Errors and BSODs[2]
- Unsolicited mouse movements
- High CPU usage
- Unknown files running in the background, etc.
Since Trojan.gen.npe.2 can represent a variety of different threats, the goal of the infection might also vary. For example, malware like AZORult is developed to steal sensitive data in the background, with the help of a variety of functions, including keylogging, screenshot taking, etc. Unfortunately, such a virus usually operates silently, complicating Trojan.gen.npe.2 removal if no security software is used.
Personal information is among the most desired attributes in the cybercriminal world – the data can be sold on the dark web for profit or leveraged to steal money from bank accounts and similar. Without a doubt, such activity can harm the infected users greatly, resulting in vast financial losses, as well as identity theft.
Nevertheless, Trojan.gen.npe.2 might have other goals, including cryptomining.[3] This process helps cybercriminals to acquire digital currency, such as Bitcoin or Monero, by using a botnet of infected computers. In such a case, the infected users could experience lag, software crashes, OS reboots, high usage of hardware (fan in particular), and high CPU/GPU usage.
Additionally, victims might also expect large electricity bills due to excessive usage of computing power. It is important to note that Trojan.gen.npe.2 malware may damage Windows system files as well – you can repair this with the help of tools like FortectIntego later, however.
If that did not convince you to remove Trojan.gen.npe.2, you should also be aware that the threat can proliferate other malware, such as ransomware. This devastating computer infection renders all local and networked files useless and then asks for a ransom payment for a decryption tool. In this case, users may lose their data permanently, along with the money, as cybercriminals not always keep their promises and deliver the required decryptor.
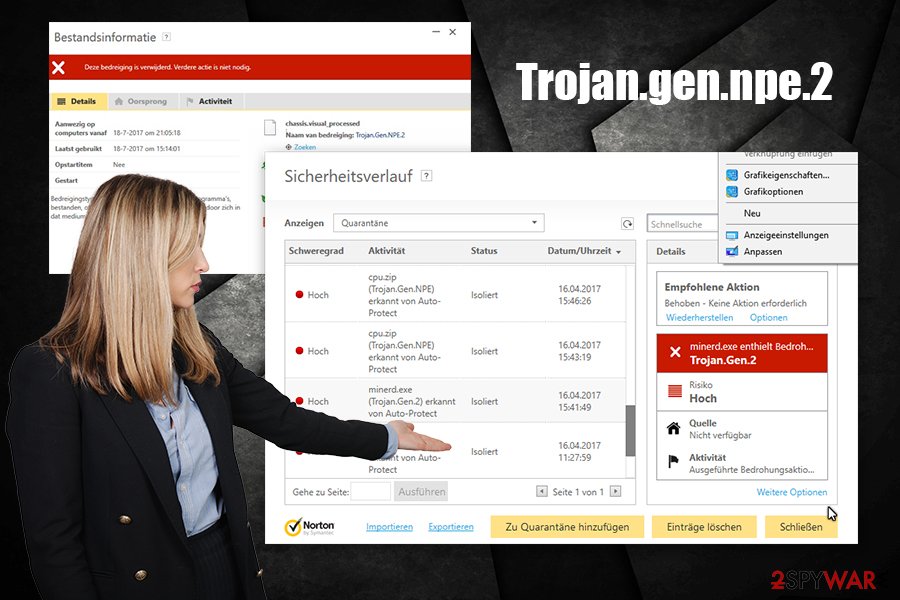
Keep in mind that Trojan.gen.npe.2 removal might compromise a useful file or a program, so you should be aware that the detection can also mean a false positive. If you are completely sure that the detection is an FP, you should add an exclusion on the security tool. The best way to determine whether Trojan.gen.npe.2 detection is actually correct is by scanning the file in question with another security tool.
Avoid Trojan and other malware by being careful online
Unfortunately, most users do not take cybersecurity seriously, and act careless when using their computers. For example, downloading software cracks or pirated software installers is one of the leading causes for malware infections, including Djvu ransomware, which infects hundreds of users each day. Nevertheless, many still risk their online security and computer safety despite knowing about the risks.
Unfortunately, employing anti-malware software is not enough to protect you from all harm online. Cybercriminals are sophisticated individuals and they are always looking for ways how to bypass the implemented security measures and prevent anti-malware tools from detecting viruses. Therefore, there are several other things you should keep in mind, including:
- Update your operating system and installed programs on a regular basis (as soon as patches are released);
- Protect all your accounts with strong passwords and use two-factor authentication where possible;
- When using Remote Desktop, employ a VPN and never use a default TCP/UDP port;
- Never allow spam email attachments to run macro function (“Allow Content”) and do not click on suspicious links inside;
- Backup your files regularly;
- Do not download software cracks, loaders, keygens, and other suspicious tools.
Trojan.gen.npe.2 removal instructions
You should not remove Trojan.gen.npe.2 if the detection is a false positive, as it may stop a legitimate application to stop working. If you are not sure whether the file is actually malicious, you should upload it to services like Virus Total for analysis, or scan with another anti-malware tool. Once you are sure that the detection is not a false-positive, you can hurry up with Trojan.gen.npe.2 removal. In some cases, this process might be hindered by malware's functionality – you can bypass that by accessing Safe Mode with Networking.
However, everything becomes a bit more complicated for those that do not use anti-virus software and are not aware of Trojan.gen.npe.2 virus' presence. Unfortunately, as mentioned above, Trojans rarely show any symptoms, so detecting the infecting is hardly possible without security software. Thus, ensure you are running anti-malware software at all times and perform regular scans.
Getting rid of Trojan.gen.npe.2. Follow these steps
Manual removal using Safe Mode
In case Trojan.gen.npe.2 is tampering with your security software, access Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Trojan.gen.npe.2 and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Large numbers of random false positives (Trojan.Gen.NPE.2). Norton. Community forums.
- ^ Chris Hoffman. Everything You Need To Know About the Blue Screen of Death. How-To Geek. Site that explains technology.
- ^ Forrest Stroud. Cryptomining malware. Webopedia. Online Tech Dictionary for Students, Educators and IT Professionals.
