Trojan.Multi.Brosubsc.gen (Tutorial) - Virus Removal Guide
Trojan.Multi.Brosubsc.gen Removal Guide
What is Trojan.Multi.Brosubsc.gen?
Trojan.Multi.Brosubsc.gen – a Trojan virus that is mostly active in Russia and drops advertising content even when the infected web browser is disabled
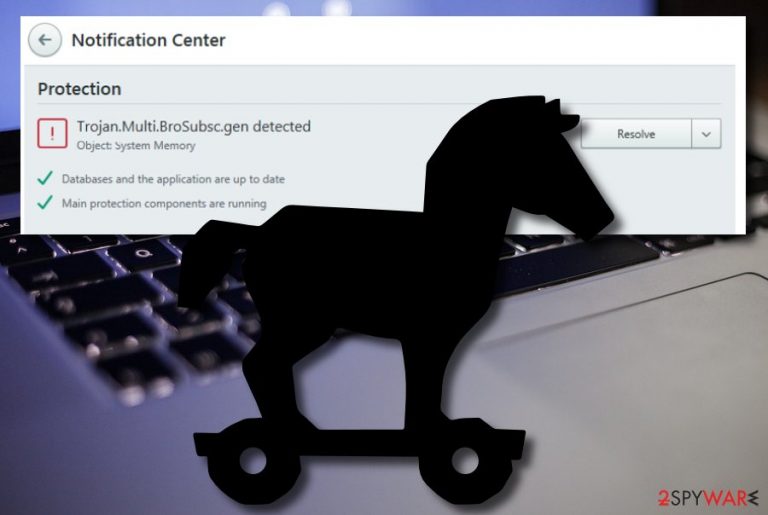
Trojan.Multi.Brosubsc.gen is malware that has a complex functionality, including web browser attack. The Trojan horse[1] can invade any type of web browser such as Chrome, Firefox, Explorer, or Safari and start displaying intrusive pop-up notifications, according to Kaspersky researchers.[2] The biggest number of victims has been spotted in Russia while Trojan.Multi.Brosubsc.gen virus also was found attacking users from Brazil, India, Kazakhstan, Ukraine, Mexico, Algeria, Saudi Arabia, France, and Vietnam.
Trojan.Multi.Brosubsc.gen is capable of deactivating the Windows Task Manager, so when you are infected with this particular parasite, you will receive the nvapi.dll error message while trying to open the Task Manager service. Furthermore, the malware can disguise as legitimate processes and run malicious tasks in the computer’s background. This makes it unnoticeable for a longer period of time and more persistent. Trojan.Multi.Brosubsc.gen can initiate any types of activities such as the installation of other malware, recording personal information and technical details that are stored on the infected device, stealing passwords, swindling money from users’ bank accounts, and so on.
| Name | Trojan.Multi.Brosubsc.gen |
|---|---|
| Type | Trojan virus/malware |
| Victims | According to Kaspersky researchers, the biggest number of victims was discovered in Russia. Other affected countries include Brazil, India, Kazakhstan, Ukraine, Mexico, Algeria, Saudi Arabia, France, and Vietnam |
| Activities | Once the malware gets installed on the computer system, it can initiate any types of activities such as the installation of other malware, gathering private data about the users, stealing passwords, swindling money, etc. |
| Features | The Trojan horse shows very little symptoms when it infects the targeted computer system. However, some users can spot the increase of the CPU power level, suspicious entries injected in the Windows Registry, slow computer work, windows struggling to maximize and minimize, etc. |
| Distribution | Parasites such as trojans are often distributed through email spam messages and the malicious attachments that get clipped to these emails. Furthermore, you can receive malware on your computer system if you have downloaded a fake update, installed cracked software, or clicked on a malicious advertisement |
| Elimination | You can remove the malware from your Windows computer with reliable antimalware software. If you are having some trouble with this process, you should try disabling malicious tasks and activities with the help of Safe Mode with Networking or System Restore |
| Fix software | If you have discovered any compromised areas on your device, you should try fixing them with reliable repair software such as FortectIntego or any other similar tool |
Users have been complaining that Trojan.Multi.Brosubsc.gen is a hard form of malware to remove.[3] Nevertheless, the Trojan virus can end up disabling your antivirus security tool and it might not be able to discover the parasite. This way the threat enhances its persistence and makes sure that the user has a hard time to eliminate it.
Furthermore, Trojan.Multi.Brosubsc.gen can run as a legitimate-looking process in the Windows Task Manager, e.g. web browser, popular software or service, etc. However, this malware version disables the Task Manager section and you will not be able to open it and discover all of the questionable executables that were added.
To continue, Trojan.Multi.Brosubsc.gen can insert rogue and malicious entries into the Windows Registry that might cause severe damage to the Windows computer system. However, if you do not enter this section and recognize the questionable registry keys, you might not be able to notice the Trojan horse for a long period of time.
Often, trojans are such types of cyber threats that show very little signs of infection, so they can hide in the computer system for days, weeks, and even more. However, if you are an accurate user, you might spot some small changes on your PC that were initiated by Trojan.Multi.Brosubsc.gen:
- Your computer is operating slower than before.
- Programs became sluggish while launching and running.
- Windows are minimizing and maximizing slower than ever.
- You have encountered an increased energy level of your CPU power.

Trojan.Multi.Brosubsc.gen can aim to perform a big variety of malicious and dangerous activities on your Windows computer. It is known that the malware attacks web browsers and uses them for pushing advertisements on the device screen. Nevertheless, the advertising activity can still persist even when the browser is not in use.
Furthermore, Trojan.Multi.Brosubsc.gen can aim to steal passwords that are stored in your web browsers and computer system. Afterward, the virus can use them to connect to your banking accounts and swindle money or get into your social media accounts and send malicious messages to your entire friends list.
However, this is still not all that might come after the appearance of Trojan.Multi.Brosubsc.gen. This parasite can record all of the sensitive information that is saved on the attacked computer and use it for illegitimate purposes such as identity theft or putting up the details for sale on some dark web markets where they become accessible to various crooks.
Also, Trojan.Multi.Brosubsc.gen can install other malicious products to the computer system. In most cases, trojans are known to pass others of its kind with a specific capability, for example, cryptocurrency mining or file-encrypting cyber threats (ransomware) that aim to lock up all the data on the infected PC and demand a ransom for its release.
If you have discovered the trojan on your machine and do not know how to get rid of it, we are here to help. Trojan.Multi.Brosubsc.gen removal might be a complex process to complete and you are likely to need to boot your computer in Safe Mode with Networking or access System Restore first.
Afterward, you should download and install a reliable antivirus tool that will help you to remove Trojan.Multi.Brosubsc.gen via automatic technique. You should not try to eliminate the malware on your own as you might make some mistakes and the dangerous parasite would be likely to appear via the next computer boot-up process.
Virus installation happens when security measures are not followed
According to cybersecurity specialists from Virusai.lt,[4] malware installation occurs when users do not follow all of the recommended security measures and fail to protect their computer systems properly. One of the most popular virus distribution sources is known to be email spam that travels together with clipped attachments or inserted hyperlinks that execute the malicious payload once enabled.
You should beware of unrecognizable messages that reach your inbox or spam section. Always investigate the sender, check the content for grammar mistakes, and never open a clipped attachment without performing a malware scan first.
Furthermore, malware such as trojans can get downloaded from software cracks that come from pirating networks such as The Pirate Bay, eMule, BitTorrent, and others. Avoid using these sources for getting your wanted products and better visit websites that you can trust and are run by well-known developers.
Additionally, you can receive a malicious download if you carelessly click on a fake software update, advertisement or hyperlink that appears along your way. A tip for avoiding malware would be to run trustworthy antivirus software that will alert when there is a deceptive website ahead of you and this way you can immediately stop proceeding to it.
Go for Trojan.Multi.Brosubsc.gen removal ASAP
Trojans are not those types of infections that you can mess with. As soon as you spot this cyberthreat, you should speed up the Trojan.Multi.Brosubsc.gen removal process. If the malware has been blocking your antimalware tools and it is hard for you to do something, you should reboot your Windows computer in Safe Mode with Networking or activate the System Restore feature and then try to terminate the cyber threat again.
You should remove Trojan.Multi.Brosubsc.gen only by employing reliable and expert-tested antivirus products, otherwise, you might not manage to succeed. Completing the elimination on your own might result in system damage or missing some crucial components and the Trojan virus can start running again the next time you boot your computer.
When you uninstall Trojan.Multi.Brosubsc.gen properly and get rid of all of the malicious components that were brought by the malware to your computer, you should start searching for possible device damage with software such as SpyHunter 5Combo Cleaner and Malwarebytes. If these products reveal any corrupted areas, you can try repairing those affected locations with FortectIntego.
Getting rid of Trojan.Multi.Brosubsc.gen. Follow these steps
Manual removal using Safe Mode
To deactivate malicious processes that are operating on your Windows computer due to the Trojan virus attack, you should boot your device in the Safe Mode with Networking regime.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Trojan.Multi.Brosubsc.gen using System Restore
To disable the malware and diminish all the questionable activities that it has been running lately, you can use the below-provided instructions for enabling System Restore.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Trojan.Multi.Brosubsc.gen. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Trojan.Multi.Brosubsc.gen and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ What is a Trojan? Is it a virus or is it malware?. Norton. Internet Security.
- ^ TROJAN.MULTI.BROSUBSC. Kaspersky. Threat information.
- ^ Andrew Korobowicz. trojan.multi.brosubsc.gen. Microsoft Answers. Forums.
- ^ SAUGUMO IR VIRUSŲ NAUJIENOS. Virusai. Security and spyware news.







