Trojan.Win32.SEPEH.gen (Virus Removal Guide) - Free Instructions
Trojan.Win32.SEPEH.gen Removal Guide
What is Trojan.Win32.SEPEH.gen?
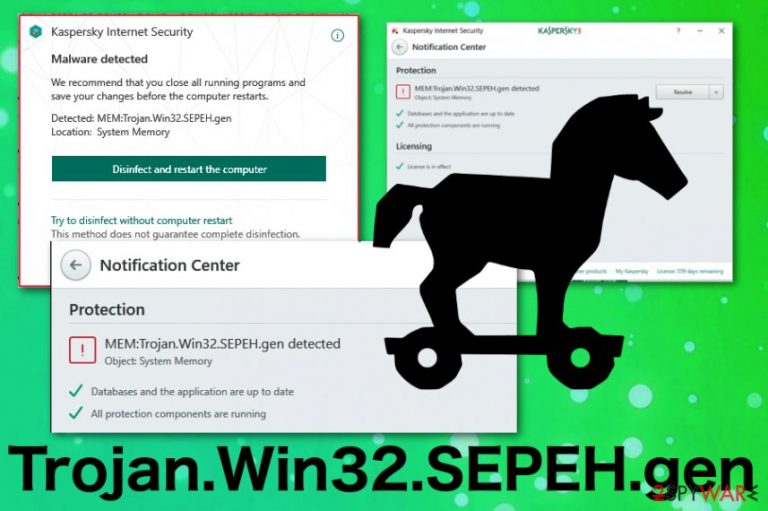
Trojan.Win32.SEPEH.gen is the detection name that indicates a generic trojan horse due to typical malware activity
Trojan.Win32.SEPEH.gen is the name of a trojan horse that runs on the machine and causes unwanted or even unnoticeable changes. This malware is created to attack devices with Windows operating systems and cause frustration by running questionable processes on the computer. The user can not notice the initial infiltration because this threat enters the system silently using shady techniques like spam email campaigns and phishing attacks.[1]
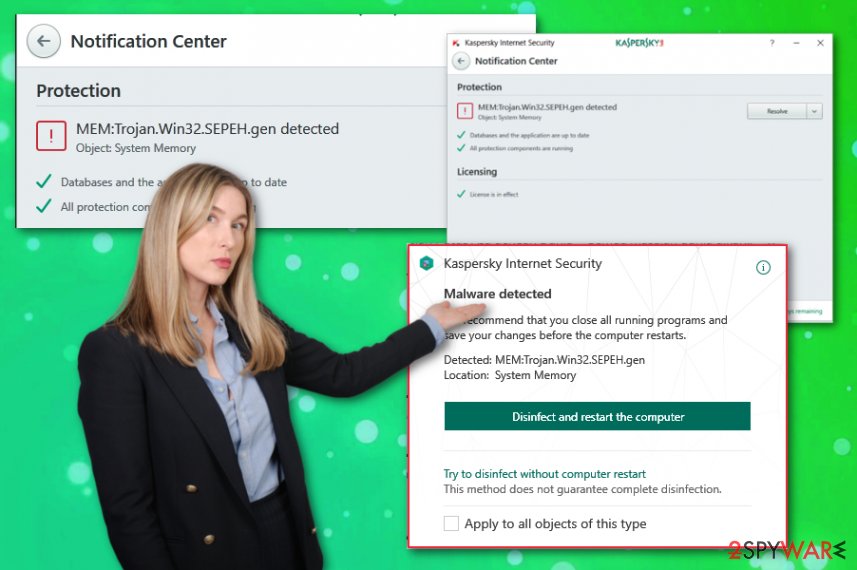
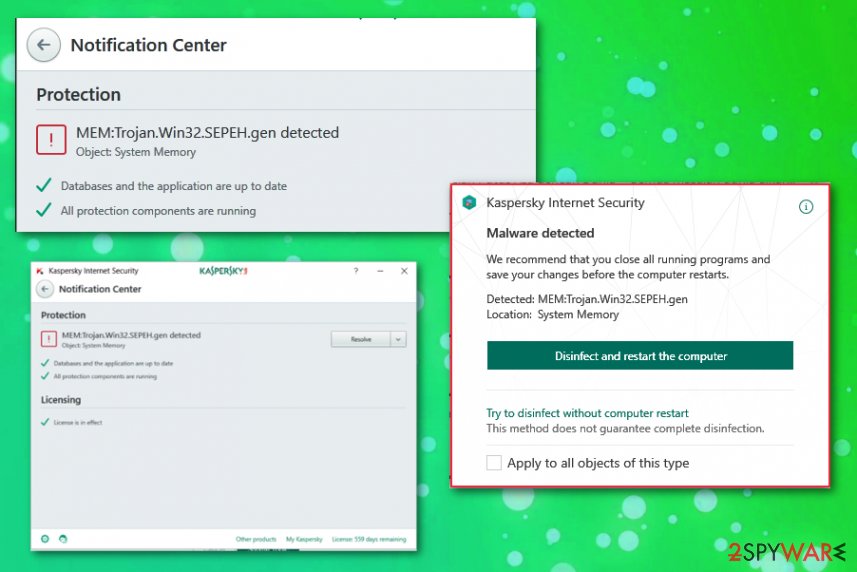
The particular malware name Trojan.Win32.SEPEH.gen is shown on the antivirus program windows like Kaspersky or Avira when the tool detects a malware of a specific type, due to a common activity, but cannot identify the threat by name or the infection is new and doesn't belong to any databases. However, there is no need for a certain malware name, you can remove this Trojan either way.
| Name | Trojan.Win32.SEPEH.gen |
|---|---|
| Type | Trojan horse[2] |
| Distribution | Spam email campaigns, other malware, infected files |
| Symptoms | Runs in the background causing slowness of the machine, installs other files and programs |
| Main danger | Can access data stored on the device and steal other credentials, files, infect the computer with malware |
| Elimination | Get reliable anti-malware to remove Trojan.Win32.SEPEH.gen from the system |
Trojan.Win32.SEPEH.gen is the malware detection result that may cause frustration for users, and a few online forum members claim that Kaspersky and other AV tools deliver this result, but it is challenging to solve the particular issue.[3] The problem may arise due to a malware detection database issue when the threat is not included in the database yet.
However, in most cases, Trojan.Win32.SEPEH.gen virus shows up as a detection result because of the real infection on the machine. Trojans can be identified by common symptoms and activities, malicious behavior, and based on these features, antivirus tools deliver warnings about particular virus detection.
Typical behavior of malware that causes Trojan.Win32.SEPEH.gen detection means that trojan can be set to:
- install other malware or malicious files;
- use your device to run processes like mining;
- use the affected device for click fraud;
- record keystrokes and steal information;
- send collected data to the hacker;
- give the remote access to attackers;
- show malicious commercial content;
- trick the person into clicking on questionable pages and redirects;
- suggest fake updates, rogue tool installations or purchases.
Trojan.Win32.SEPEH.gen malware should be eliminated no matter if these symptoms occur or not. The less damage this virus has caused, the better because that means trojan hasn't got much time to alter the setting on the machine. You should clean the system thoroughly to terminate the associated process and delete the malware itself completely.
The insidious Trojan.Win32.SEPEH.gen can be created with malicious purposes, and the shady infiltration is harmless in comparison with the primary goal of the hackers behind this threat. When the system starts crashing, showing warnings or Blue Screen of Death appears, you can be sure that your PC is affected by malware. This detection explains all the suspicious symptoms.
When you encounter system performance changes, unauthorized data, or network settings alterations, and this result of the AV tool scan, you need to remove Trojan.Win32.SEPEH.gen as soon as possible. The more time you give for such a virus, the more damage can be done.
For the through system scan and virus damage, Trojan.Win32.SEPEH.gen removal, we recommend getting an anti-malware program. You should be able to rely on the tool that showed you the heuristic name in the first place but feel free to double-check with an alternate tool.
Make sure to terminate Trojan.Win32.SEPEH.gen virus damage and clean the device thoroughly and scan the PC a few times. Also, Trojans are one of the more persistent threats, so reboot the machine in Safe Mode and then run a system check with FortectIntego.
Phishing campaigns create the risk for data and the security of a device
In most cases, various spam email campaigns target users' information or system files and data stored on the machine itself. However, such emails often contain infected files and even direct malware payload. Trojans are one of many cyber threats that come to the targeted computer during such phishing campaigns.
This is a common method because people are not paying enough attention to particular files they download and open on the computer or even processes happening on the machine. Such emails contain files filled with macros, and once those get triggered, direct malicious script is launched on the computer automatically. Unfortunately, you cannot notice the initial infiltration, only later symptoms.
Nevertheless, if you keep antivirus tools running on the machine and pay more attention to various processes, you can avoid cyber infections and evade malware termination in the first place. Also, keep the email box at the check and delete suspicious emails once received. This is what many experts[4] always advise.
Eliminate Trojan.Win32.SEPEH.gen virus and make sure to remove malicious files from the machine
When threats like potentially unwanted programs or rogue applications come to the system, you can find them and uninstall manually. However, malware like Trojan.Win32.SEPEH.gen virus is not that easy to delete because the trojan may hide in various places of the system, program folders, and so on. This is a threat that runs background processes and affects the performance of an infected device this way.
Trojan also can install other malware and generally work as a payload dropper, so this detection can only be a small threat in comparison with ransomware or cryptocurrency miners this virus can download. You should remove Trojan.Win32.SEPEH.gen as soon as your AV indicates the threat or you notice any symptoms.
For the best Trojan.Win32.SEPEH.gen removal results, rely on automatic anti-malware tools and scan the machine entirely. Tools like FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes can also help you to eliminate virus damage and additionally installed files and programs. Thorough system check improves the performance and even fixes system errors on Windows devices.
[GI=method-2Try System Restore feature on Windows to reverse the virus damage[/GI]
Getting rid of Trojan.Win32.SEPEH.gen. Follow these steps
Manual removal using Safe Mode
Remove Trojan.Win32.SEPEH.gen malware from the machine via Safe Mode with Networking
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Trojan.Win32.SEPEH.gen and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Phishing. Wikipedia. The free encyclopedia.
- ^ Josh Fruhlinger. What is a Trojan horse? How this tricky malware works. CSOonline. technology news and analysis.
- ^ Mem:Trojan.Win32.Sepeh.gen. Kaspersky. Community forum.
- ^ Ioys. Ioys. Spyware related news.
