Trojan.Win64.Miner.gen (virus) - Tutorial
Trojan.Win64.Miner.gen Removal Guide
What is Trojan.Win64.Miner.gen?
Trojan.Win64.Miner.gen is the threat that affects the performance of the computer significantly because it uses resources to mine cryptocurrency
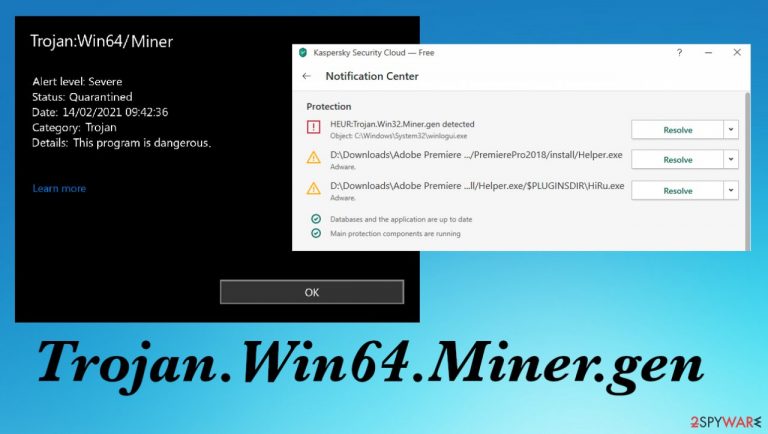
Trojan.Win64.Miner.gen is the type of cyber infection that damages the machine while running in the background. It is not showing any symptoms and mainly affecting data on the system or speed, so users cannot notice the intruder easily. The trojan is categorized as a miner because it invades the machine with the purpose of using resources to mine cryptocurrency. Every time you turn on your computer the malicious program launches and starts its malicious procedures. The infection can spread via pirated applications, cracked games, malicious file attachments from email notifications.[1]
There are various other features that such infection has. One of them can be acting as the vector and spreading different viruses on the already affected machine. You might have the trojan and then get the ransomware in fiction due to the compromised security of the system. It is extremely important to remove the threat as soon as possible because over time these intruders can lead to serious issues.
Even though Trojan.Win64.Miner.gen virus have a main goal and functions, it can be malicious and act differently too. Trojans and other more silent, symptom-less malware can trigger many damaging activities, so you should take care of this infection as soon as it is possible. That can be done with anti-malware tools only because trojan is not the program that you could see on the desktop or in any folder.
| Name | Trojan.Win64.Miner.gen |
|---|---|
| Type | Trojan, cryptocurrency miner |
| Issues | The infection causes suspicious sped issues, show up as files or processes running in the background |
| Danger | Trojan can lead to infiltrations of different malware, including ransomware[2] |
| Distribution | Malicious files with the payload can come during pirating of software while downloading game cracks, or from malspam email attachments |
| Elimination | The best solution for these types of infections – anti-malware tools and a thorough system cleaning process |
| Repair | Silent malware can easily alter files, settings, damage data on the machine, so you should run FortectIntego and fix these issues caused by the infection |
The infection can spread when people surf the web without paying enough attention to details and what content gets opened or visited. It is always advised to be cautious online by various experts.[3] Trojan.Win64.Miner.gen can be spread using email campaigns when some notifications pose as messages from a known company or service.
Clicking on those emails can already be risky, but if you get the email with an attachment and download that file, open any random link from the message, you can receive the malicious file without knowing. An infection like this happens quickly, so your machine becomes infected in a matter of minutes.
In most cases, trojans act unnoticed and delete themselves off of the machine, but some changes can become damaging and the performance offers, making the user aware of the problem. random files, programs running on the machine, causing high usage of resources can indicate the infection.
Malicious pieces silently cause serious damage
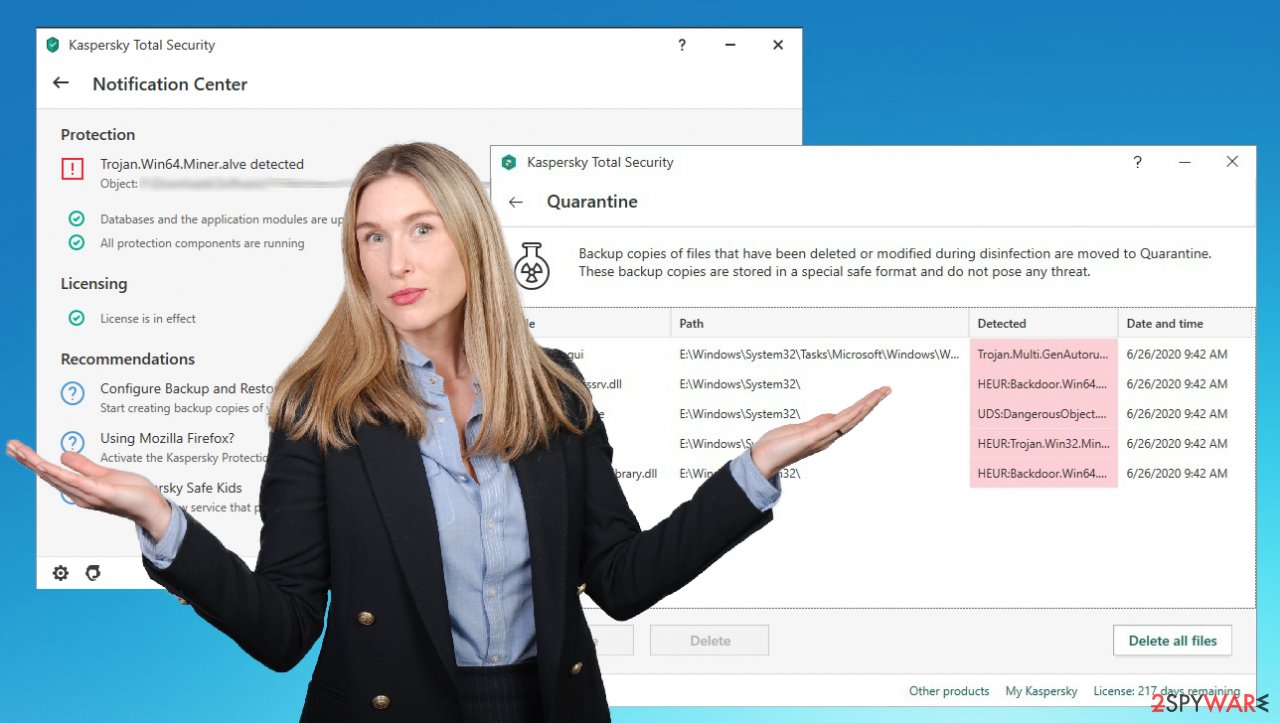
These pieces of malware cannot be noticed unless the anti-malware tool that you use indicates Trojan.Win64.Miner.gen detection and you see that the machine is possibly affected by the threat and can explain those speed or performance issues. Otherwise, without tools like SpyHunter 5Combo Cleaner, that can remove detected threats, the machine is affected, but users have no idea about it.
Once a computer is infected with malware, its system is changed to operate differently. For example, an infection can alter the Windows registry database, damage vital bootup, and other sections, delete or corrupt DLL files, etc. Once a system file is damaged by malware, antivirus software cannot do anything about it, leaving it just the way it is. Consequently, users might experience performance, stability, and usability issues, to the point where a full Windows reinstallation is required.
Therefore, we highly recommend using a one-of-a-kind, patented technology of FortectIntego repair. Not only can it fix virus damage after the infection, but it is also capable of removing malware that has already broken into the system thanks to several engines used by the program. Besides, the application is also capable of fixing various Windows-related issues that are not caused by malware infections, for example, Blue Screen errors, freezes, registry errors, damaged DLLs, etc.
- Download the application by clicking on the link above.
- Click on the ReimageRepair.exe.
- If User Account Control (UAC) shows up, select Yes.
- Press Install and wait till the program finishes the installation process.

- The analysis of your machine will begin immediately.

- Once complete, check the results – they will be listed in the Summary.
- You can now click on each of the issues and fix them manually.
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.

By employing FortectIntego, you would not have to worry about future computer issues, as most of them could be fixed quickly by performing a full system scan at any time. Most importantly, you could avoid the tedious process of Windows reinstallation in case things go very wrong due to one reason or another.
However, there are no other options for thorough malware removal other than anti-malware solutions – applications like Malwarebytes. You can get some detection names other than Trojan.Win64.Miner.gen, but the main purpose of such infection cleaning process is to eliminate any threats found on the machine. When you scan the system with an antivirus tool it shows all possible infections, so you can clear them all.
Unfortunately, Trojan.Win64.Miner.gen can block such tools and other programs that act as security solutions, so you need to get some help for the removal procedure. It becomes difficult to remove serious threats like this over time. We recommend getting a trustworthy tool and run that more often to avoid these issues.
Another helpful tip is to enter the Safe Mode with Networking and take care of the infection then. If the virus blocks or disables some programs, you can rely on this method and eliminate the threat fully without additional issues. However, this option is for Trojan.Win64.Miner.gen removal can be a bit difficult for less tech-savvy people.
If malware is not letting you use antivirus in normal mode, access Safe Mode and perform a full system scan from there.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.
- Scroll down to pick Update & Security.
- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.
- Go to Advanced options.
- Select Startup Settings.

- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.

Once you reach Safe Mode, launch SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable antivirus, update it with the latest definitions and perform a full system scan to eradicate malware and all its malicious components. Trojan.Win64.Miner.gen can cause serious damage if you leave it on the system.
Trojans can execute themselves automatically and install other threats on the machine without your permission or even knowledge. This is a sneaky infection that shouldn't be kept on the system. Even though the mining is not affecting you financially, this malware piece or additional infections can sometimes access your credentials, sensitive data and steal funds from accounts online.
Trojan.Win64.Miner.gen as any other malware can act as it is created to, so malicious processes are not limited to mining cryptocurrency. Often these pieces get indicated as the vector for ransomware like one of the most common and widespread viruses – Djvu ransomware. keep the machine safe with anti-malware tools.
How to prevent from getting trojans
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Malicious Email Attachments. Proofpoint. Education.
- ^ Ransomware. Wikipedia. The free encyclopedia.
- ^ Lesvirus. Lesvirus. Spyware related news.
