Trojan:BAT/Poweliks.A (Easy Removal Guide) - Virus Removal Instructions
Trojan:BAT/Poweliks.A Removal Guide
What is Trojan:BAT/Poweliks.A?
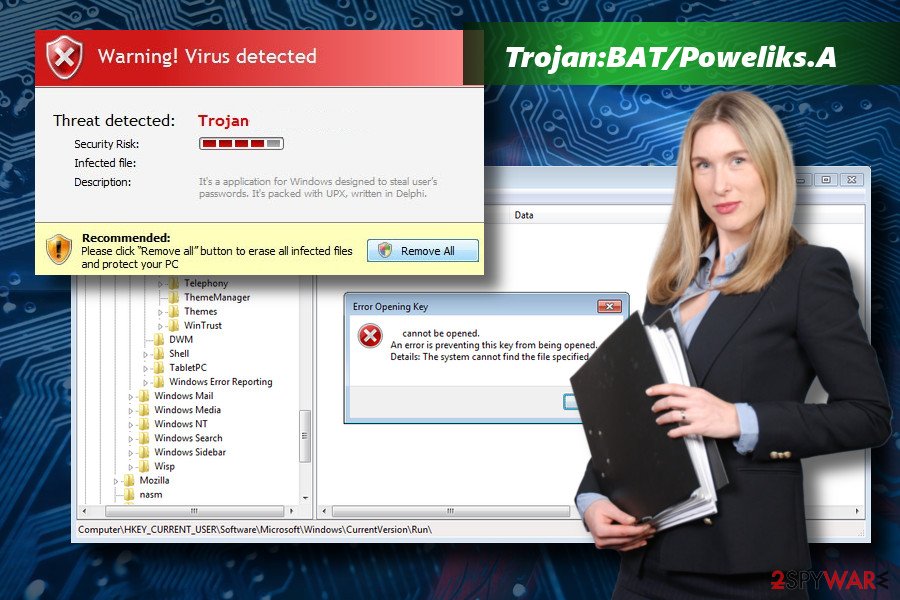
Trojan:BAT/Poweliks.A is a detection of a malicious Poweliks Trojan

Trojan:BAT/Poweliks.A is a name of a Trojan[1] horse returned to PC users by an AV-engine. This name can be used interchangeably with the following: Poweliks Trojan, Trojan.Poweliks, Trojan.Poweliks!gm, SONAR.Poweliks!gen1 and similar. The virus stands out from the others since it's is not detectable in the form of a file.[2] It resides in Windows Registry and relies on Watchdog maintenance.
| Name | Trojan:BAT/Poweliks.A |
|---|---|
| Type | Trojan |
| Related to | Poweliks Trojan |
| Also recognized as | TROJ_POWELIKS.A, Trojan.Poweliks.A, Trojan.Win32.Powerliks.a, Trojan:Win32/Powessere, ATrojan.Win32.Powerliks.a |
| Danger level | Medium. Initiates multiple system's changes, but does not harm the system directly. The risk – can infect the system with malware via dangerous ads |
| Download FortectIntego and run a scan in Safe Mode with Networking environment to get rid of Trojan:BAT/Poweliks.A | |
First detected in 2014, the malware mutated in many ways, but most of AV engines are still struggling to detect and immunize it successfully. Trojan:BAT/Poweliks.A malware does not have related files. That's why it's known as Fileless Trojan. Once executed, the malware uses various registry tricks, to name but a few:
- Creates the following entries:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\”(default)” = “[ENCRYPTED JAVASCRIPT]”
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\”[NON-ASCII STRING]” = “rundll32.exe javascript:\”\..\mshtml,RunHTMLApplication \”;document.write(\”\74script language=jscript.encode>\”+(new%20ActiveXObject(\”WScript.Shell\”)).RegRead(\”HKCU\\software\\microsoft\\windows\\currentversion\\run\\\”)+\”\74/script>\”)”
- Uses a special naming method.
- Hijacks CLSID entries (Class ID, which is a 16-byte value that identifies an individual object). Targets the {FBEB8A05-BEEE-4442-804E-409D6C4515E9}, {73E709EA-5D93-4B2E-BBB0-99B7938DA9E4}, and {AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} entries in particular. This way, it can run any time the system starts running or when the user of the infected PC opens specific folders;
- Misuses a legitimate rundll32.exe file to execute JavaScipt code, which is further used to compromise data on Windows Registry;
- Installs and runs Watchdog process, which maintains the Trojan and protectsts it from removal. It is capable of recovering the deleted virus instantly.
- Watchdog process also changes access rights to keep Poweliks Trojan undetected under Windows Registry. For this purpose, it uses unprintable characters;
- Builds a wall not to be detected within Registry. Most AV engines fail to remove Trojan:BAT/Poweliks.A virus since they cannot access the LocalServer32 subkey where the payload of the malware roots. For this purpose, it uses 0x06 byte and the 0x08 byte mechanism, which is not recognized as a Unicode printable character. Consequently, the LocalServer32 subkey becomes unreadable.
In short, specialists find it difficult to remove Trojan:BAT/Poweliks.A Trojan due to the intricate performance mechanism it uses. Once the Powerliks gets inside, its payload decrypts targeted values, runs PowerShell scripts to take control over Watchdog process and misuses rundll32.exe file to infect Windows Registry.
Trojan is a malicious cyber infection that can cause serious problems. They are often used for the distribution of ransomware, spyware, and other malware. Thus, NoVirus.uk[3] team urge people to remove Trojan:BAT/Poweliks.A without a delay using FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
Nevertheless, this trojan is not the most dangerous infection in the wilds. It's a tool employed by hackers who seek to generate pay-per-fraud activities to increase income from advertising. It is developed in a way to display keyword-based ads. It initiates a fake search by typing in default keywords and the browses for the required URLs. The minimum ads the
Trojan:BAT/Poweliks.A Trojan is requested to load is 3,000 by default, though not a single one will be revealed to the user of the infected PC. However, their content is not being investigated, so there's a high risk of getting infected with ransomware, spyware, keylogger or another severe cyber infection via trojanized invisible ads.
Spam email allows Trojan to circulate on the web since 2014
According to cyber security experts, the file-less Trojan is most frequently distributed via malicious spam email attachments. Typically, they are disclosed in the form of Doc file from a shipping company USPS. It claims to contain package-related information.[4]
In this case, the only way to secure your system from infection is to report such an email as spam and remove it asap. Keep in mind that legitimate companies are not distributing suspicious-looking emails with attachments unless the client is informed about that in advance.
Besides, the virus can use rogue software updates or infected ads to get installed on a target system. Watch out for prompts to update FLV Player, Google Chrome, Flash Player, Java, and similar software.
Remove Trojan:BAT/Poweliks.A from the system and restore Windows Registry easily
Tech-savvy people may find it easy to remove Trojan:BAT/Poweliks.A virus manually at first, but the process is more complicated than it initially might seem. The process requires a careful termination of multiple processes, the removal of the virus, and a restoration of Windows Registry entries.
To initiate Trojan:BAT/Poweliks.A removal successfully, designate this task to a professional anti-virus program, such as FortectIntego or SpyHunter 5Combo Cleaner. The first program recommended performs as a robust optimization tool. It contains a full database of Windows system's files and is capable of fixing Windows Registry. Thus, we would strongly recommend relying on Reimage.
Getting rid of Trojan:BAT/Poweliks.A. Follow these steps
Manual removal using Safe Mode
WatchDog process can block your antivirus program completely. If you cannot run the program that is currently installed on your PC, you should follow this tutorial to boot the system into secure environment.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Trojan:BAT/Poweliks.A using System Restore
If the previous method did not work, try to delete Poweliks this way:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Trojan:BAT/Poweliks.A. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Trojan:BAT/Poweliks.A and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Trojan horses are the most dangerous online threats of 2017. CTV News. Breaking news site.
- ^ Charlie Osborne. Poweliks Trojan goes fileless to evade detection and removal. ZDNet. 24/7 news coverage and insights.
- ^ NoVirus. NoVirus. Brithish cyber security news.
- ^ Poweliks Update. The Virus Doctor. Software developer's blog.







