Win32:BogEnt (Tutorial) - 2021 update
Win32:BogEnt Removal Guide
What is Win32:BogEnt?
Win32:BogEnt is a computer virus detection name that is based on behavioral analysis
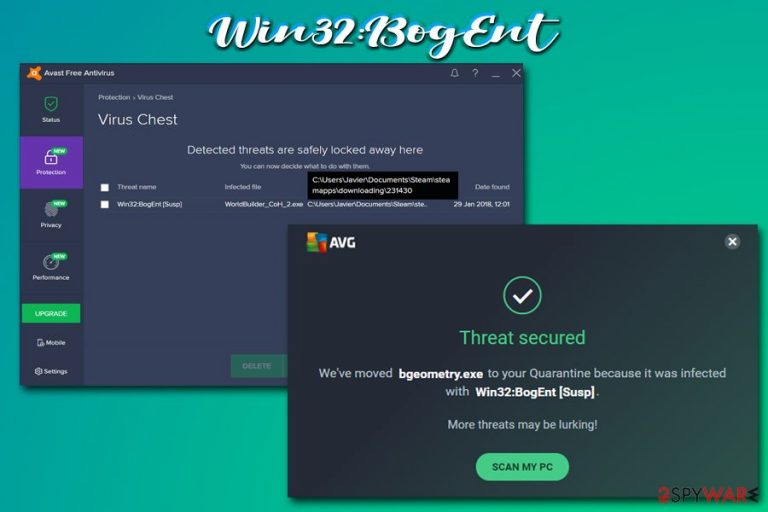
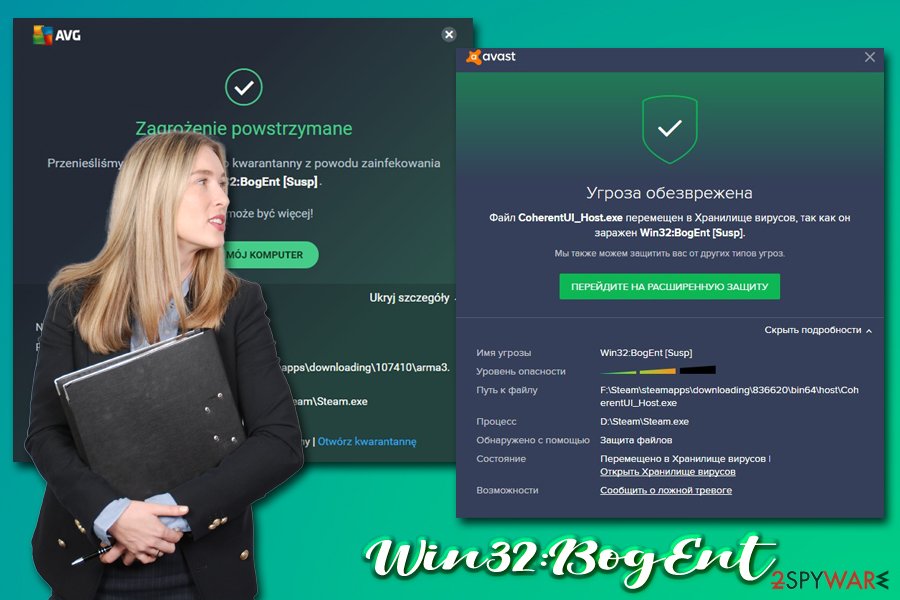
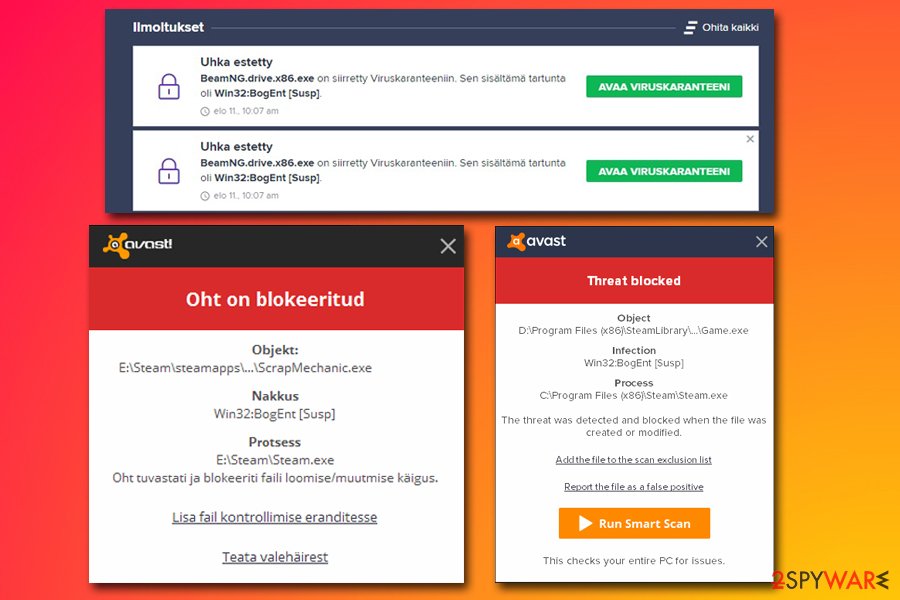
Win32:BogEnt is a heuristic detection that describes unusual behavior of particular files located on the host system. The definition is only used by Avast and AVG anti-malware software and seems to be related to video games from Steam, as well as pre-installed ones. Multiple users complained that they got the pop-up claiming that malicious files were found in relevant folders, which were removed or quarantined as a consequence. However, many others had doubts about it, and not in vain, as, in some cases, the detection might indeed be a false-positive.[1]
Nevertheless, users should never ignore WIN32 BogEnt [Susp] or any other detections that are flagged by their AVs. The behavioral analysis looks for particular signs and symptoms of certain files or programs that are dropped on the system. Therefore, dismissing the possibility that the detection can indicate malware infection is not adequate, either.
| Name | Win32:BogEnt |
| Type | Malware |
| Infection means | You can infect your machine with malware in various ways, including downloading pirated or cracked software, not having anti-malware software installed, failing to update your operating system and the installed programs on time, opening malicious file attachments, etc. |
| Affected systems | Windows 7, Windows 8/8.1, Windows 10 |
| Is it a false-positive? | Win32:BogEnt is a heuristic detection definition, meaning that certain behavior is analyzed in order to conclude whether the file is malicious. In some cases, a behavioral analysis might not detect files correctly and flag legitimate data as malicious. In this case, if you encountered this detection while playing Steam games, it is likely that the detection is false |
| Malware removal | If the file is malicious, you should eliminate it immediately. For that, you can scan your device with an alternative anti-malware tool, such as SpyHunter 5Combo Cleaner. You can also employ our manual guide below to find malicious files yourself |
| Further actions | If your computer was affected by any type of malware, it is highly recommended to scan the device with a repair tool such as FortectIntego. It can find and fix Windows registry, correct system settings and ensure that your device works just as well as before |
To make sure that your machine is clean, you should scan the detected file with another security software. Once you are sure that the detection is a false-positive, you can add it to your exception list and wait for relevant anti-virus engines to update their definitions. Finally, you should not hesitate to remove Win32:BogEnt if other anti-malware tools are flagging it as malicious
The virus detection can relate to various game titles, including Company of Heroes 2, H1Z1 King of the Kill, Chuzzle Deluxe, Path of Exile, and many others, as well as flagging such files as libcef.dll, libcef.exe, bgeometry.exe, galaxy.dll, LaunchPad.libs, etc.
Therefore, if you see the detection after updating or downloading a game, it is most likely a false positive, as Steam is a secure gaming platform that makes several checks that do not allow malware to be distributed via it (however, it does not avoid issues as a platform). Besides, a game developer confirmed[2] that Avast and AVG flag their game files as malicious due to the way the “hotloading” works – the feature is related to updating the game without needing to restart it.
Simply because Win32:BogEnt is heuristic does not mean that is can never be a real threat. Malware can be downloaded by users without them realizing it. Cybercriminals use the following methods for its distribution:
- Exploits[3]
- Fake updates
- Unprotected RDP connections
- Spam emails
- Drive-by downloads
- Software cracks, etc.
Therefore, if you engage in high-risk activities or disable your security software for some reason, there is a high probability that it is indeed malware. What it can do on your system, however, is very hard to tell, as this particular name can be attributed to various types of malware, including rootkits, Trojans, data stealers, ransomware, and others.
Before you proceed with Win32:BogEnt removal, you should use another anti-malware software and scan the detected file once again – we recommend using SpyHunter 5Combo Cleaner or Malwarebytes, although other reputable tools can be used as well.
After malware elimination, you should also take care of your computer's health. Keep in mind that infections can alter the way Windows works negatively. As a result, you might experience lag, slowdowns, crashes, BSODs, and other symptoms, even after virus elimination. If you want to avoid these disturbances, we highly recommend remediating your system with FortectIntego.
To avoid malware from intruding your computer, make sure you practice safe browsing habits
As mentioned before, malware developers use various distribution methods in order to infect as many users as possible. While some techniques might be more sophisticated than others, all of them work to a certain degree and, in most cases, the end-users are the vector that triggers the infection. Therefore, you should be aware that malware could infect your computer in places you least expect, although certain exposures to online threats are triggered purposely (such as downloading of software cracks despite knowing the risks).
Security experts from zondervirus.nl[4] claim that comprehensive security solutions, along with safe online browsing practices, can make an enormous difference when it comes to computer security and online safety. Thus, ensure you always install the latest security updates on time, equip your machine with anti-malware software, backup your files, never download software cracks/pirated programs, install ad-block and never click on suspicious email attachments or hyperlinks in spam emails. Also, you should make sure that all your accounts are protected by strong passwords that are never reused – best would be employing a password manager.
Ways to deal with Win32:BogEnt detection
If you saw this detection on your computer, you should never ignore it. Either you will not be able to play your favorite Steam games or malware will be performing malicious activities behind your back – and you definately do not want that. Therefore, take immediate action and do not ignore the issue. Before you remove it, however, you need to ensure that it is not a false positive.
For that, you should employ another security application and perform a full system scan – you could use SpyHunter 5Combo Cleaner, Malwarebytes, or another anti-malware software. If it gets flagged as well, proceed with Win32:BogEnt removal as soon as you can, as malware might cause tremendous damage to the PC and your online safety. If you noticed that your system is lagging, crashing, or throwing errors after malware elimination, we recommend using FortectIntego to fix the underlying issues caused by the infection.
If a secondary scan returns no detections, you should exclude the file from being scanned again and enlist it into the exception list. We include the instructions for both security applications:
Make an exclusion Avast:
- Go to Menu and select Settings
- Pick General tab on the left and click on Exceptions
- Click on Add Exception button
- You need to type in the file path of the file or select browse to specify the file in question
- Find the file and click OK
Make an exclusion on AVG:
- Click on the menu at the top-right and pick Settings
- Next, go to General > Exceptions
- Select Add exception
- Type in the file path or find it via the Browse option and click OK
Getting rid of Win32:BogEnt. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Win32:BogEnt and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Margaret Rouse. False Positive. WhatIs. IT website.
- ^ Avast! scanned my PC and then deleted the exe for this game?!. Steam. Official forums.
- ^ What is an Exploit Kit?. PaloAlto Networks. Cyberpedia.
- ^ Zondervirus. Zondervirus. Cybersecurity advice from industry experts.
