XINOF ransomware (virus) - Jan 2021 update
XINOF virus Removal Guide
What is XINOF ransomware?
XINOF is the name of a ransomware virus that is a sibling of Fonix gang

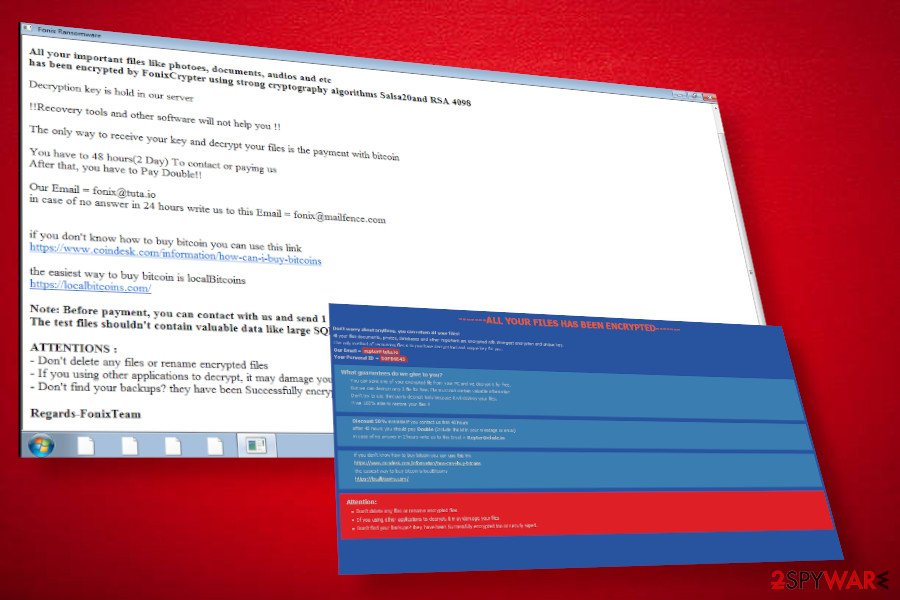
XINOF ransomware is a successor to a relatively new crypto-malware Fonix. The new variant, which is actually the first update of the initiate ransomware virus that resurfaced in the middle of July 2020. Detected by a well-known ransomware researcher dnwls0719[1], the malware is known for leveraging malicious MS Word and Excel attachments of spam emails and locks users' data using Salsa20and RSA4098 encryption models.
The XINOF virus uses a specific pattern to mark the locked files – the email address (thunder@fonix.email) + a unique ID number (8 characters) and .XINOF extension at the end. Besides, it generates several ransom notes under different locations and names them either How To Decrypt Files.hta or Help.txt, or both. Victims are expected to email criminals on thunder@fonix.email or alternative email provided on the note and transfer the payment within 48 hours. Although the ransom size is not known, a single dollar paying to the criminals is not worth the risk.
| XINOF | |
| Type | Ransomware / File-locking virus |
| Genealogy | Fonix or FonixCrypt ransomware family |
| Distribution | Alike predecessor, it can infiltrate PCs via unprotected RDPs or infected spam email attachments |
| Extension | [thunder@fonix.email].[unique 8 character ID].XINOF |
| Criminal contact | thunder@fonix.email |
| Ransom note | How To Decrypt Files.hta and Help.txt |
| Symptoms | All personal files encrypted Ransom notes dropped on various folders Slow PC's performance High CPU usage spotted on the Task Manager |
| AV detection | Malicious ransomware processes can be recognized by updated AV programs as: Trojan:Win32/Filecoder.d609ee7d Win64:Trojan-gen Trojan.TR/FileCoder.zcrtt W64/Filecoder.BY!tr Trojan.Win32.Diss.suvdl Trojan:Win32/Ymacco.AA4C Gen:Variant.Razy.603845 A Variant Of Win64/Filecoder.BY, etc.[2] |
| Termination | Only a full scan with AV security can help |
| Virus cause damage | Every virus leaves its marker on the Windows system performance. Overfilled registries, damaged system files, and other negative consequences eventually can lead to crashes and weaken the security. Therefore, we recommend using FortectIntego repair tool regularly |
XINOF ransomware virus does not have unusual traits that would allow it to stand out from the crowd. However, its abilities should not be underestimated. Based on the research, the virus shows a tendency to spread via highly obfuscated files that can hardly be detected by AV programs. This way, it gets a freeware to infect PCs exhibiting less and medium protection.
Right after the install, the malware runs the xinof.exe file, which runs the payload and drops multiple helper objects under locations like C:Program Files, C:Users/[current user]/AppDataRoamingMicrosoft C:\Windows\System32, and many others. Therefore, it is not possible to detect and remove XINOF file virus manually. It can only be detected by professional security software.
When the ransomware gains persistence, it enables the encryption tool, which uses a mathematical structure (the combination of Salsa20and RSA4098) to completely lock non-system files. Only after that, the victim is acquainted with the v virus and its capabilities. For finding out more, the victim has to open the Help.txt file (the excerpt given below) or click on the How To Decrypt Files.hta file, which redirects to the Tor site automatically.
ALL YOUR FILES HAS BEEN ENCRYPTED!!!
All your important files like photoes, documents, audios and etc has been encrypted by FonixCrypter using strong cryptography algorithms Salsa20and RSA 4098
Decryption key is hold in our server
!!Recovery tools and other software will not help you !!
The only way to receive your key and decrypt your files is the payment with bitcoin
You have to 48 hours(2 Day) To contact or paying usAfter that, you have to Pay Double!!
Our Email = thunder@fonix.email in case of no answer in 24 hours write us to this Email = fonix@mailfence.com if you don't know how to buy bitcoin you can use this link.
The easiest way to buy bitcoin is local Bitcoins.Note: Before payment, you can contact with us and send 1 free small file (size less 2Mb) as decryption test
The test files shouldn't contain valuable data like large SQL or Backup files.ATTENTIONS :Don't delete any files or rename encrypted files
– If you using other applications to decrypt, it may damage your files
– Don't find your backups? they have been Successfully encrypted too or securly wiped.
No matter how scary this virus may seem, do not fall for panic. No rush to pay the ransom. The only thing that should arouse your interest should be how to remove XINOF ransomware completely. Do not postpone the elimination of malicious programs as they often can run secondary payloads and severely damage the system.

The XINOF removal and .xinof file recovery are two different processes
Do not get deceived by claims that running a scan with a security tool will both remove the virus and decrypt .XINOF files. That is not true and you should not trust the websites that share such claims. File encryption algorithms cannot be cracked down by AV scanners as they do not have such a function or at least not yet.
Anyway, there are several methods that can help you recover .XINOF extension files. These are the following:
- You can pay the criminals and expect that they will send you the decryption key (NOT recommended);
- You can use backups of the locked files. Please note that Gmai account automatically creates backups, so you may check what files can be restored via the connected account;
- Alternatively, you can use third-party data recovery tools, for example, Data Recovery Pro or Shadow Explorer. Although they cannot guarantee a full data recovery, there's a chance to unlock some of the .XINOF ransomware files.
- Finally, you can contact reputable ransomware researchers, provide them with the ransomware samples, and wait for a free decryptor to be released.
Protect your machine using a strong AV engine and be careful with suspicious content online
Cybercriminals make use of various security gaps, be it unprotected RDP, security vulnerability, zero-day vulnerabilities, remote code execution possibilities, and whatnot. Therefore, it's very important to take any possible precautionary measures to protect the machine if you store single file copies and valuable information on it. For this purpose, it's not enough to install the AV program. It's also important to keep it updated, ensure that a full service is enabled (real-time protection, scan to email, and similar). Besides, regularly update the software and all possible patches to minimize security risks.
Despite the variety of virus distribution techniques, spam remains the main and the most successful way of disseminated malicious cyber infections. Spam emails may be spread via targeted attacks to specific emails or distributed by bots en masses using random email addresses that might have been leaked during a data breach[3]. Therefore, hundreds of less experienced users can get tricked into opening malicious spam email attachments. Thus, do not get tempted by the curiosity to check the “Order confirmation” if you haven't ordered anything or similar.
The ways to remove XINOF ransomware virus from Windows machines
XINOF ransomware removal is the main thing that you should think of as soon as your files get locked. However, make sure that this process may not be easy to accomplish. The ransomware may run tens of malicious files, some of which may work as helper tools that block AV scanners, prevent the system from rebooting, and similar.
Therefore, in order to remove XINOF virus from the Windows system completely, you have to restart the machine into Safe Mode with Networking. That's the only way to temporarily disable malicious processes and launch the AV scanner. Our recommendation – use SpyHunter 5Combo Cleaner or Malwarebytes security tools, though you a free to choose whichever security software you prefer using.
After XINOF virus removal, try alternative file recovery options. We'll provide a full list of our suggestions below. However, be aware that these methods do not grant file recovery, so, if possible, use backups or check for available decryptors on these websites:
- https://www.nomoreransom.org/en/index.html
- https://id-ransomware.malwarehunterteam.com/
- https://www.emsisoft.com/ransomware-decryption-tools/
- https://www.avast.com/ransomware-decryption-tools
Getting rid of XINOF virus. Follow these steps
Manual removal using Safe Mode
There are two ways to disable XINOF ransomware processes and remove it completely. For that, you can either restart the system into Safe Mode with networking or enable System Restore as explained below:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove XINOF using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of XINOF. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove XINOF from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts..XINOF files cannot currently be decrypted for free. However, there are several methods that can help to return at least some of the files.
If your files are encrypted by XINOF, you can use several methods to restore them:
Download Data Recovery Pro
Data Recovery Pro is a tool that best works when recovering the files that are not encrypted, but lost because of the system crash. Nonetheless, many people reported that the tool extracted some of the locked files successfully.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by XINOF ransomware;
- Restore them.
Windows Previous Versions feature might help you recover at least some .XINOF encrypted files
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Take advantage of the Shadow Explorer
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No XINOF decryption tool yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from XINOF and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ dnwls0719 profile. Twitter. The social media network.
- ^ XINOF.exe. VirusTotal. Free URL and file scanner.
- ^ Abi Tyas Tunggal. The 36 Biggest Data Breaches [Updated for 2020]. UpGuard. Australian cybersecurity startup company.







