Yeabests.cc virus (Removal Instructions) - Aug 2017 update
yeabests.cc virus Removal Guide
What is yeabests.cc virus?
Yeabests.cc virus hijacks browser shortcuts to stay on the computer system

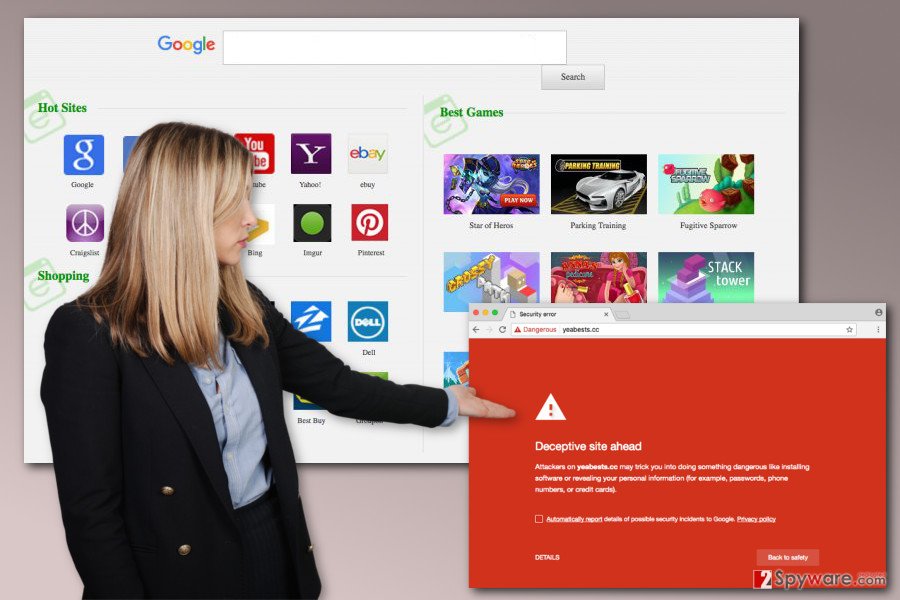
Yeabests.cc virus is categorized as a potentially unwanted (PUP) and a browser hijacker which is closely related to another shady search tool TopYea Search. This suspicious application might hijack the most popular web browser and alter their settings. As a result, users may find an unknown search engine set as their default homepage.
However, developers of the search engine would not agree with this classification. Yeabests.cc is presented as legitimate and useful search service. This tool is supposed to deliver improved search results from Google. Though, these improvements are nothing more than commercial content. The browser hijacker might not only deliver misleading ads but also include sponsored links into search results. It functions very similarly to other related browser-hijacking search tools such as:
Sadly, Yeabests.cc redirect tendencies are not safe and credible. One click on the search result or ad might lead to the potentially dangerous third-party website where you can be tricked into installing bogus software or suffer from phishing[1] or tech support scam.
Indeed, the biggest problems are related to this corrupted search engine that modifies results. It includes lots of commercial content and sponsored links in order to boost traffic to particular websites. If you found this search tool installed without your permission, you must remove Yeabests.cc immediately with a help of FortectIntego.
Yeabests redirect virus often travels in the software bundles and hijacks web browsers unnoticed. However, the signs of the infection are loud. It might replace default homepage, search engine, and new tab address. What is more, it might append arguments to various Windows shortcuts and install browser helper objects to protect its presence.
Thus, Yeabests.cc removal might be slightly complicated.[2] However, at the end of the article, you will find illustrated instructions that will help you to take back control over your browser. Furthermore, you have probably noticed that this search engine also provides a facility to access shopping and gaming websites right from the homepage.
However, such functionality might turn out to be quite damaging rather than beneficial. This is because the browser hijacker is despised for its TopYea redirect ability. If you get tempted into entering the websites from the app platform displayed on the homepage, you might reach the web page of your interest after several redirects to advertising, gaming or even adult-content sites.
Though the former web pages are quite harmless, the latter might cause damaging effects to your computer. Some of the redirect websites mislead to another web pages “enhanced” with destructive malware[3] and viruses.
Furthermore, Yeabests hijack might also be damaging in a sense that the PUP collects NPII (non-personally identifiable information).[4] It comprises of your search queries, visited websites, the data of the operating system, and geographical location. This data might slip into the hands of third-parties which display their ads to you.
Once they get a hold of it, they analyze the information. Furthermore, scammers generate new advertisements which are specifically designed for particular users matching their personal preferences and interests. Thus, depending on the number of clicks of these pay-per-view ads, authors collect quite a decent income. After all, if you dislike the idea of being constantly surveyed, then you should remove http://Yeabests.cc/ at once.
TopYea distribution techniques
If you did not visit its official web page, then, most likely, CC virus has infiltrated your computer via freely downloadable software packages. Browser hijacker might end up on your PC if you have recently installed a new audio player, photo editing software, updated Flash Player or Java. Probably, you have noticed that there was an add-on entitled as “yeabests.cc” pinned inside the software package.
This is exactly how the browser hijacker settled on your computer. Such mistakes are common to the countless number of users worldwide. Most of them might argue that they do not have time for reading installation instructions. As you can see, it takes considerably more time to get rid of similar malware afterward.
All in all, if you want to prevent a browser hijacker from rummaging through your computer,[5] take note and choose “Custom” installation” mode rather than “Recommended” settings when installing new software on your PC. Then, make sure you uncheck the unnecessary pre-marked applications. Also, do not forget that you have to choose only reliable and safe sources for software downloads. File sharing websites or Torrents are not one of them. Always choose official developers' website.
Remove Yeabests.cc redirect virus manually or using anti-malware software
If you are interested in all of the Yeabests.cc removal options, you can first check the manual elimination guidelines just below the article. Make sure you do not miss any of the indicated steps. Otherwise, some affiliate files with the virus might be left. Thus, the probability of getting hijacked by this PUP significantly increases.
If you have already tried the manual removal but Yeabests.cc keeps coming back, and you can install an anti-spyware application and scan your PC with it. It will guarantee that the hijacker is completely eliminated. This software comes in handy not only in dealing with this particular unwanted application but with other various types of malware as well.
Lastly, we would like to advise you to stick to the legitimate and trustworthy Google or Bing search engines rather than opting for new but highly insecure alternatives. If you are experiencing difficulties and can’t remove Yeabests.cc or any other browser hijacker from your computer, do not hesitate to contact us and we will try to help.
We have also noticed that this browser redirect virus is extremely prevalent in Poland. In case you are a Polish-speaking computer user, consider visiting usunwirusa.pl site for CC virus removal guidelines[6].
IMPORTANT. If you encounter “1.0.0.1 YeaDesktop verification code” error when trying to delete the hijacker's components from the system, you should follow this tutorial to fix the problem.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of yeabests.cc virus. Follow these steps
Uninstall from Windows
What can be frustrating for the less experienced users while removing Yeabests.cc is that it is Windows Management Instrumentation (or WMI) based infection, which means it is fileless. It does not drop files on the infected computer's hard drive, so the antivirus software may not be able to detect it. Below, we provide a tutorial on how to uninstall CC virus from the system:
- To remove it from your computer, you will have to manually run the WBEMTest which can be found in this directory C:\Windows\System32\wbemtest.exe. Right-click on this executive file and run it as Administrator.
- Click Connect and type root\subscription in the Namespace field. Click Connect again.
- Check the Enable All Privileges checkbox and then click Enum Instances button.
- You will see a pop-up that asks to enter Superclass name. Type ActiveScriptEventConsumer and click OK.
- Carefully look through the list of findings and if you can see an instance with “ASEC,” select it and then click Delete.
- Now, clean each of your browser shortcuts. Use the tutorial provided below to clean them. You must delete the http://yeabests.cc/ link from the Target field and Apply changes to get rid of the hijacker. If you have some shortcuts pinned to your task bar, remove them and re-pin them here after cleaning browser shortcuts.
Nevertheless, we strongly recommend obtaining a professional antivirus utility which would be able to locate the virus in the Windows Management Instrumentation records as well.
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Though this virus rarely infects Mac operating systems, Safari is still among the target browsers. So, if your computer has been infected, please follow the instructions provided below or scan your computer with reputable antivirus tool, such as SpyHunter 5Combo Cleaner.
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
To remove this browser hijacker from your browser completely, look for extensions or add-ons that may be related to this virus and remove them. Keep in mind that they may hide under various titles, so be very attentive.
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Although Yeabests.cc works based on WMI and does not create files on the computer, that you could delete, it may still appear on your browser as an add-on or extension, so go through the list of the installed components and evaluate their reliability by consulting reputable online sources.
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
To make sure this browser hijacker is eliminated from your browser entirely, please take care of the additional extensions it may have left on your browser. Delete the suspicious browser add-ons which may have been recently installed on your computer.
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
In the list of browser extensions, look for Yeabests.cc, TopYea Search and related extensions and remove them. This is the only way you can ensure the virus will not bounce back to your browser.
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of yeabests.cc registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting stealing programs
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Emma Williams, Debi Ashenden. Phishing scams are becoming ever more sophisticated – and firms are struggling to keep up. The Conversation. In-depth analysis, research, news and ideas from leading academics and researchers.
- ^ Windows PUPs: how do I remove potentially unwanted programs?. The Guardian. News, sport and opinion from the Guardian's US edition.
- ^ What is Malware and How to Defend Against It?. Kaspersky Lab. The official website of the security software developer.
- ^ Chris Hoffman. The Many Ways Websites Track You Online. How-to Geek. Includes help, tutorials, tips and how-to guides for Windows and Linux.
- ^ Lincoln Spector. Five precautions for avoiding malware when you download and install software. PC World. Laptops, Tablets, iPads, Desktop PCs, Printers & More.
- ^ UsunWirusa. UsunWirusa. Malware Removal Tutorials.























