Your computer has been locked (Sep 2017 update) - Simple Removal Guide
Your computer has been locked Removal Guide
What is Your computer has been locked?
“Your computer has been locked” continues its deceptive campaign
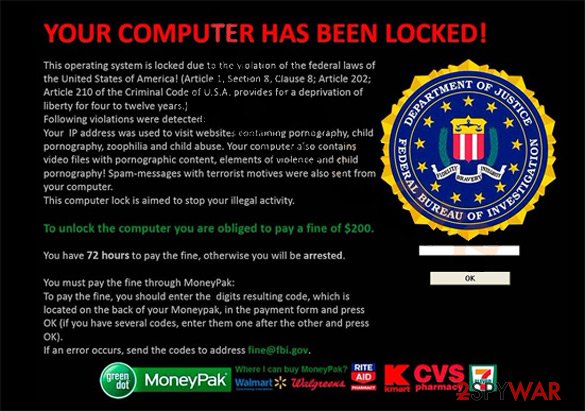
“Your computer has been locked” virus as a file-encrypting threat using the disguise of the FBI[1]. The British version of the ransomware disguises under the authority of West Yorkshire Police. It has features of a trojan and tech support scam[2]. The original version threatens you to transfer the ransom; otherwise, you will be arrested for the alleged crimes.
Alternatively, by showing fake Google Chrome warning alerts, the infection aims to convince users that their operating system has been highly infected with viruses and persuade them into calling a technical support specialist. In this regard, at least the virus is right about one thing – the device has been infected with the malware.
The latest version, “Your computer has been locked’” screenlocker, locks the screen and asks to contact the technician. Either such call is charged with an extremely expensive rate or you might download a completely futile application. In any case, remove “Your computer has been locked.” It is known that the virtual infection is related to the family of Ukash viruses[3], often detected in the form of ransomware.
As soon as the malware occupies the system and downloads the payload inside, the PC performance gets paralyzed. You will see only a huge and annoying alert saying that it's from Royal Canadian Mounted Police or from the Department of Justice. Proceed to Your computer has been locked removal. FortectIntego or Malwarebytes speeds up the process. Here is one of the scam examples:
Your computer has been locked. But dont worries, the files will never delete. Just your computer is locked because your computer has viruses. If you want the code, contact the nearest microsoft technician. The reason A unusal activity has been detected on your computer. Your computer might be at risk, and this is the reason the locked your computer. Click on the button to contact the nearest microsoft technician. Click on the button to contact it. Nearest Microsoft Technician found
Contact: +62 067885169823
|LINE ID: technician460
Once Your computer has been locked ransomware settles on the operating system, a series of unpleasant occurrences appear. The overall PC performance highly deteriorates, annoying alerts asking to restart the device pop up regularly, etc. It is not difficult to notice that it is a scam. Usually, the very text of “Your computer has been locked” ransomware or tech support scam is written with obvious grammar mistakes and typos.
The design alters as well. Even if the crooks devise a refined scam or malware and you get doubts about its legitimacy, look for a phone number. No legitimate system error asks you to call a specialist. In the case of “Your computer has been locked” scam you are expected to call +62 067885169823, 1800-235-661 or pay the ransom in exchange for the unblocking services.
Additionally, the malware may encrypt some of your important files. If you encounter the screen locker version of this malware, use the following code – 01548764GHEZG784. It will grant you access and you will be able to start the elimination process.
Your computer has been locked!
Warning!
Your computer has been locked due to violation of the law in Canada.
The following violations have been revealed:
– The act of the film shooting. Registration or transfer of documents with pornographic content involving minors, child pornography, sodomy and violence against children. The punishment provided by Article 163.1/164 of the Criminal Code of Canada entails imprisonment for a term of 5 to 7 years.
(other 'crimes')
To unlock your computer, you have to pay a fine in accordance with Canadian law in the amount of 100 euros. A penalty in the form of fine is possible only if it is your first violation. Repeated violation entails criminal liability. If you do not pay the fine, your computer will be confiscated and your case will be referred to the Court.You can pay the fine through our partner or by using Ukash voucher. You can get Ukash voucher for the amount of $250, then fill in the form, specifying a voucher code and then click on the “Pay the fine” button.
1. Your computer will be unlocked right after authenticity control of Ukash voucher. Usually it takes about 1-4 hours. Find your nearest store terminal
2. As for a Ukash voucher for $250
3. Give the retailer your cash including your fee
4. The shopkeeper will print your voucher with a 19-digit Ukash PIN
5. Take the voucher and pay the fine
Such messages are fake and you don't have to pay the ransom through Ukash, Paysafecard, Moneypak or other payment systems. “Your computer has been locked” malware is just a tool helping scammers to wheedle out money from users. 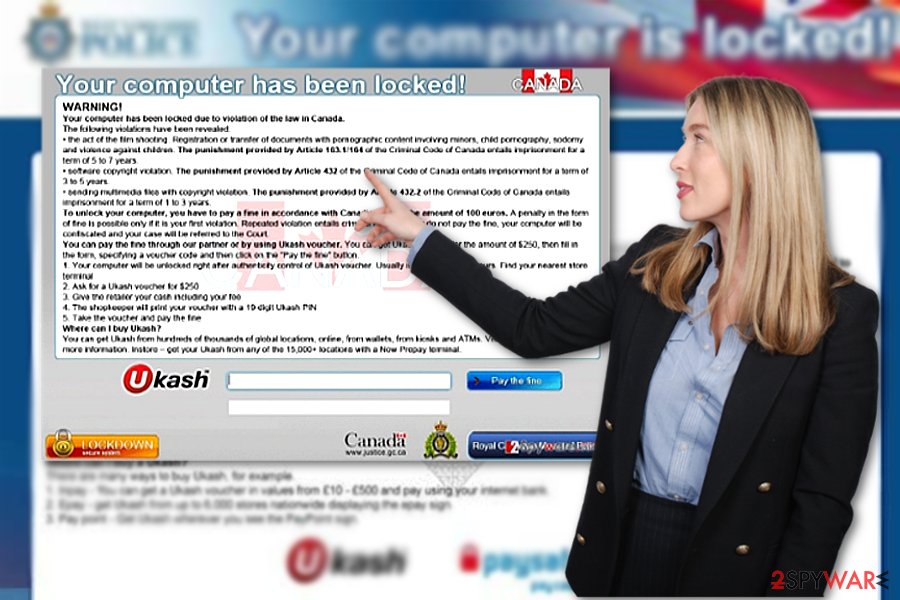
Distribution peculiarities
Like other samples of the same category, the virus might lurk in infected illegal file-sharing domains. There is also a risk to get redirected to the site which contains exploit kits[4] – the harbingers of ransomware – by clicking on fake Google Chrome warning alerts. The latter might function as browser-based tech scams.
Note that such counterfeited messaged urge you to call “Google Chrome.” Note that the latter is a browser, not a company. In addition, in case of a genuine notification, it does not display any phone numbers. Additionally, beware of links to videos with unexpectedly high ratings. What is more, the hijack might occur via a spam attachment.
Such method has proven to be highly profitable as users still fall for fake police warning emails, customs declarations forms, and tax refund reports. Explore the email carefully to look for hints:
- grammar mistakes
- typos
- absence of credentials
- altered logo of the company
In case of doubt, verify the sender before extracting the menacing malware from the attachment. Clicking on it accelerates “Your computer has been locked” hijack.
“Your computer has been locked” elimination options
“Your computer has been locked” removal does not take long if you entrust the process to a security tool, such as FortectIntego or Malwarebytes. These applications will get rid of all ransomware components shortly. If they are updated daily, they will guard the operating system from minor and more complex viruses.
If you cannot remove “Your computer has been locked” virus due to some system errors or problems with the downloading process, follow the guide to regaining the access. After that, take a look at data recovery options. Note that this malware targets non-native English users, such as Czech[5], as well.
Getting rid of Your computer has been locked. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Your computer has been locked using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Your computer has been locked. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Your computer has been locked from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Your computer has been locked, you can use several methods to restore them:
How effective is Data Recovery Pro?
If you do not have any backup copies, install the utility and run it. It should be able to help you recover some of your files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Your computer has been locked ransomware;
- Restore them.
The benefits of ShadowExplorer
This program comes in handy restoring the data after the attak of serious ranosmware. By using the automatically stored shadow volume copies, the app recreates the lost or encoded files.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Your computer has been locked and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Jennifer Kraus. FBI Warns Of Scam Posing As Microsoft Workers. NewsChannelNetwork. TN News, Weather, Sports.
- ^ John Broodkin . Tech support scam victims lost $120 million—and will get $10 million back. ArsTechnica. IT news and commentary.
- ^ Rick Maybury. How do I block the Ukash virus?. The Telegraph. .
- ^ Catalin Companu. New Disdain Exploit Kit Sold on Underground Hacking Forums. BleepingCo0mputer. News,reviews and tech support.
- ^ Eliminate computer threats. Odstranitvirus. IT News and Malware Removal Guides.







