Zloader (virus) - Free Guide
Zloader Removal Guide
What is Zloader?
Zloader is a threat that targets systems with the goal of obtaining banking information
Zloader, otherwise known as Zeus Sphinx or Tredot, is banking malware that first emerged in August 2015, and since then keeps coming back with new campaigns. Malware is based on a well-known Zeus Trojan – its source code was leaked in 2011, so malicious actor groups quickly found ways to utilize it.
This banking Zloader malware is being sold on underground forums for everybody willing to use it – for as low as $500. Since its release, the Trojan kept a relatively low profile but soon resurfaced again with COVID-19 malspam campaigns,[1] imitating the pandemic relief payment emails. Nonetheless, it can also be distributed in different ways, such as fake updates or scam messages placed on malicious websites, as well as exploit kits (Sundown).[2]
Once installed, Tredot will hijack built-in processes (Windows Explorer) and patch executables of Google Chrome, Mozilla Firefox, and Internet Explorer in order to capture user information, such as banking credentials, email, and social media logins, etc. While its main purpose on the host system is to steal data, it will also download and install another well-known malware Zbot.
| Name | Zloader |
|---|---|
| Type | Banking Trojan |
| Aliases | Zeus Sphinx, Tredot |
| Origins | The malware was introduced into cyberspace in 2015 and is based on the source code of Zeus banking malware |
| Distribution | The intruder was seen in many malicious campaigns and uses multiple attack vectors, including phishing spam, hacked websites, fake updates, exploits, drive-by downloads, etc. |
| Related files | Forwardhou.dll, cnfnot32.exe, ChiefCo.dll, vsmsoui.dll, myvtfile.exe, etc. |
| Infection symptoms | Trojans are typically very difficult to detect as they are programmed to not emit any symptoms to a regular user |
| Associated risks | Infected computers can be used to install more malware, such as Zbot Trojan, which can compromise user safety and computer security further. Ultimately, data-stealing malware infection can result in financial losses, further malware infection, Windows system damage, and even identity theft |
| Malware removal | To eliminate the malicious payload, along with secondary ones, you should employ powerful anti-malware software and perform a full system scan (access Safe Mode if required – we explain how below) |
| System fix | Malware can leave the operating system damaged after it is terminated. To fix this damage and issues that come with it, you can employ a PC repair tool FortectIntego |
When it comes to malware, there are several different sources that it can come from and end up on your machine. If the system is not adequately protected with security software and other tools, there is nothing that could stop malware, such as Zloader, from spreading throughout the PC, and even laterally if it is connected to a network.
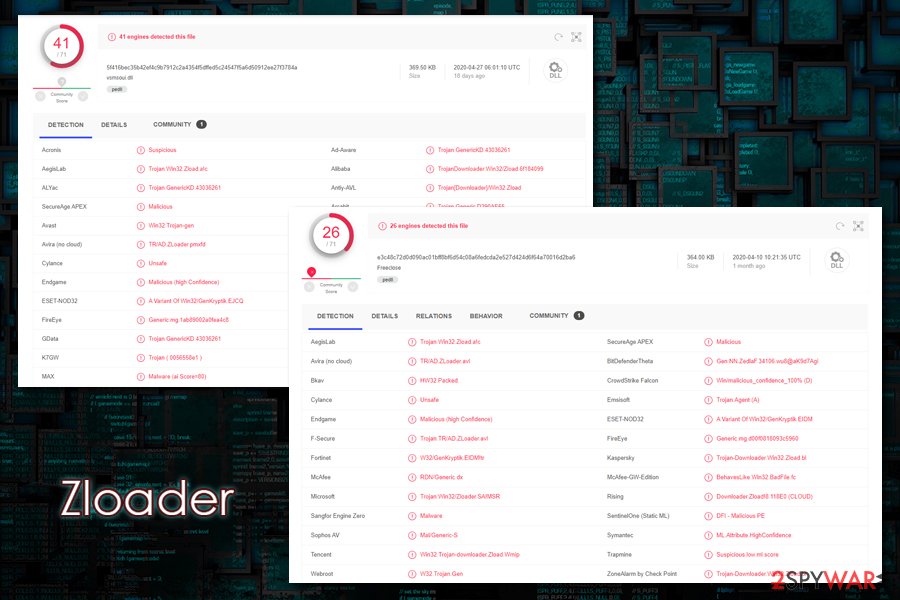
Therefore, it is really important to protect your machine adequately. In fact, you can altogether avoid the malware removal process and the compromise of your sensitive data if you employ a robust anti-malware application, which detects malware under the following names (note that there are thousands of malicious files that can initiate the download of Tredot malware, hence the executable, as well as detection names vary):[3]
- TR/AD.ZLoader.avl
- Trojan-Downloader.Win32.Zload.bl
- Trojan:Win32/Zloader.SA!MSR
- RDN/Generic.dx
- W32.Trojan.Gen
- Trojan.Agent (A)
- A Variant Of Win32/GenKryptik.EIDM, etc.
You can remove Zloader by employing reputable anti-malware software, such as SpyHunter 5Combo Cleaner or Malwarebytes. However, in some cases, you might have to access Safe Mode with Networking in order to suppress its activities, since it is known to use persistence techniques. Unfortunately, in many cases, you might not even be aware the Tredot is sneakily operating in the background, as Trojans are designed to be stealthy and not show symptoms of the infection.
Despite that, you might see some strange computer behavior due to various actions by the malware, such as random PC shutdowns/restarts, increased CPU usage, errors, BSODs, and similar. This behavior might also persist after you remove Tredot – you could employ tools like FortectIntego to fix the damage done to the operating system instead of reinstalling it completely.
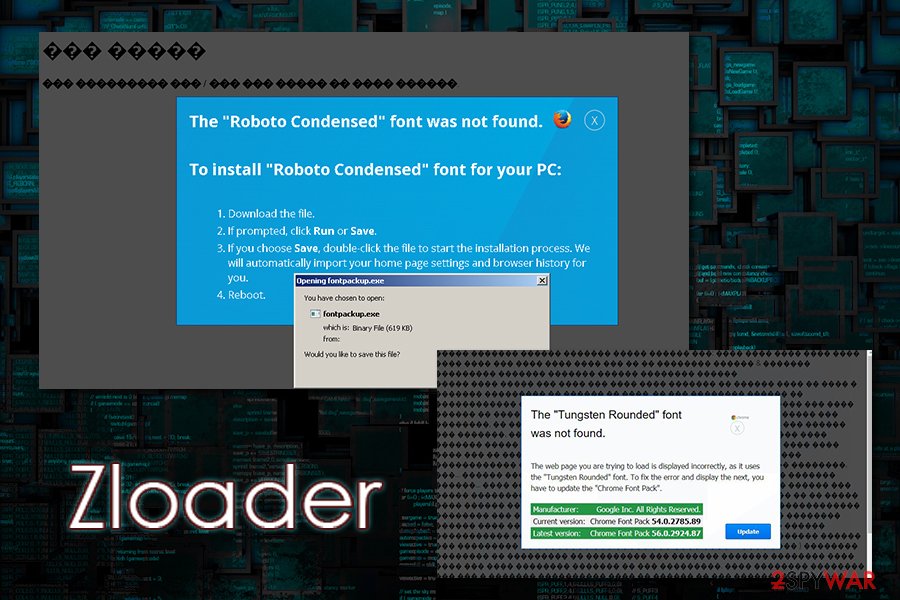
Malware spread using fake warnings and error messages
A very popular tactic used by threat actors to distribute the Zloader virus is by using fake messages that claim that the contents of the website are not recognized due to a missing font. This popular technique is not new and has been used by many different malware developers, such as Spora ransomware or Ursnif banking malware.
This tactic allows the attackers to exploit the human mind and make them believe that what they are doing is not harmful. To achieve that, Zloader malware operators first need to ensure that users visit fake message websites, and it is often done via malicious advertisements, JavaScript processes, and much more.
Once users land on the site, they are typically presented with the following text:
The “Roboto Condensed” font wasn't found.
The website you are trying to load is displayed incorrectly, as it uses the “Roboto Condensed” font. To fix the error and display the text, you have to update “Chrome Font Pack”.
Manufacturer: Google Inc. All Rights Reserved
Current Version: [version]
Latest version: [version]
This makes users believe that they need to download a font pack in order to view the contents of the page. Typically the downloaded file is named “Chrome_Font.js” or “Mozilla_Font.js” – the name differs depending on the web browser used. The JS extensions mean that the file is a JavaScript file, which would download and execute the malicious payload on the host computer.
However, this is not the only way Tredot malware is propagated since it is distributed by various groups of cyber criminals thanks to its malware-as-a-service scheme. It means that everybody wanting can use the malicious code, as long as they pay a particular sum of money. The services of malware strains are typically advertised on the dark web's hacking forums, and those willing to use malware to their advantage do not even need to be proficient hackers.
Thus, pro protect yourself from malware, consider using these precautionary measures:
- Install comprehensive anti-malware software with real-time web protection feature;
- Update Windows along with all the installed applications as soon as security patches are released;
- Use strong passwords for all your accounts;
- Enable two-factor authentication (2FA) where possible;
- When dealing with emails, never allow the clipped attachments to run macros (“Allow content”) on your machine;
- Do not download software cracks and pirated software installers;
- If used, protect your Remote Desktop adequately: never use a default TCP/UDP port, employ VPN, limit usage to only people who actually need it, etc.
The functionality of the Zloader malware
As mentioned above, the virus uses a variety of techniques to proliferate the system. Since there are multiple different variants of the malware, it might also evolve with different features that might not be present in other versions. However, as explained by researchers, the malware does not change much since its initial release back in 2015 and simply resurfaces in different campaigns.
Once the infection is triggered in one way or another, Tredot Trojan hijacks WScript.exe process to contact its Command & Control server in order to retrieve the malicious DLL file (it is often self-signed – a technique used to evade detection by anti-malware tools) and placing it into %SYSTEMDRIVE% folder, and later launched with the help of a legitimate Regsvr32.exe. Malware then places thousands of files into %AppData% folders and modifies the Windows registry for persistence.
Zloader malware then proceeds to apply a patch to various processes on Windows, such as Windows Explorer (explorer.exe), Google Chrome (chrome.exe), Mozilla Firefox (forefox.exe), and Internet Explorer (iexplorer.exe). These changes to the processes allow the malware to inject code into web browsers and capture users' credentials and other sensitive data, later sending it off to a remote server controlled by the attackers via the “Tables” function:[4]
Once a connection to the Tables panel has been established, Sphinx will fetch additional JavaScript files for its web injects to fit with the targeted bank the user is browsing. Injections are all set up on the same domain with specific JS scripts for each bank/target
The trojan will also download and install Zbot from a Command & Control server after configuring proxies. Also, malware is capable of injecting malicious payloads into memory, making it so much more difficult to detect and remove.
All in all, Tredot, along with its secondary payloads such as Zbot, serves as a deadly combo that is capable of comprehensively stealing data from the compromised computer, performing man-in-the-middle attacks,[5] and compromising the host machine/network even further.
You need to eliminate Zloader/Tredot as soon as possible
Malware can target regular consumers, as well as corporations/businesses. Thus, you should immediately segregate the infected machine from the network before performing the malware removal, as it can spread laterally and reinfect the system once deleted.
Note that malware also can inject payload into memory, so security software might not recognize it prior to infection – until all the malicious files are populated. Thus, to remove Zloader properly, you should access Safe Mode with Networking and perform a full system scan from there. Ensure that anti-malware is up-to-date before performing a scan, however, as new variants of the Tredot virus are emerging regularly. Try SpyHunter 5Combo Cleaner or Malwarebytes for the job.
Once you eliminate the Zloader virus, remember to deal with the aftermath of the infection. First of all, if your machine is lagging and returning errors, use tools like FortectIntego to fix the damage done to the system files. Also, do not forget that info-stealing malware can cause tremendous damage, even if it is removed.
Thus, you should monitor your online banking to ensure that no unsolicited transactions were performed. It is also recommended to change all the passwords that were used within the browsers of the infected computer.
Getting rid of Zloader. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Zloader and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Scott Ferguson, Apurva Venkat. Phishing Campaigns Leverage Latest COVID-19 Themes. BankInfoSecurity. Bank information security news.
- ^ Threat Spotlight: Terdot.A/Zloader Malicious Downloader. Threat Vector. Cylance threat research blog.
- ^ e3c48c72d0d090ac01bff8bf6d54c08a6fedcda2e527d424d6f64a70016d2ba6. Virus Total. File and URL analysis tool.
- ^ Amir Gandler, Limor Kessem. Zeus Sphinx Trojan Awakens Amidst Coronavirus Spam Frenzy. SecurityIntelligence. IBM security blog.
- ^ Man-in-the-middle attack. Wikipedia. The free encyclopedia.














