Ad Avenger browser hijacker (Free Instructions)
Ad Avenger browser hijacker Removal Guide
What is Ad Avenger browser hijacker?
Ad Avenger is a fake ad-blocker that shouldn't be trusted
Ad Avenger is presented as an app that is capable of not only stopping all the ads but also improving browsing speed and stopping all the trackers, allegedly improving privacy. However, this app is very deceptive – instead of blocking the ads, it inserts its own everywhere users go. Hence, it is categorized as a potentially unwanted program[1] and a browser hijacker.
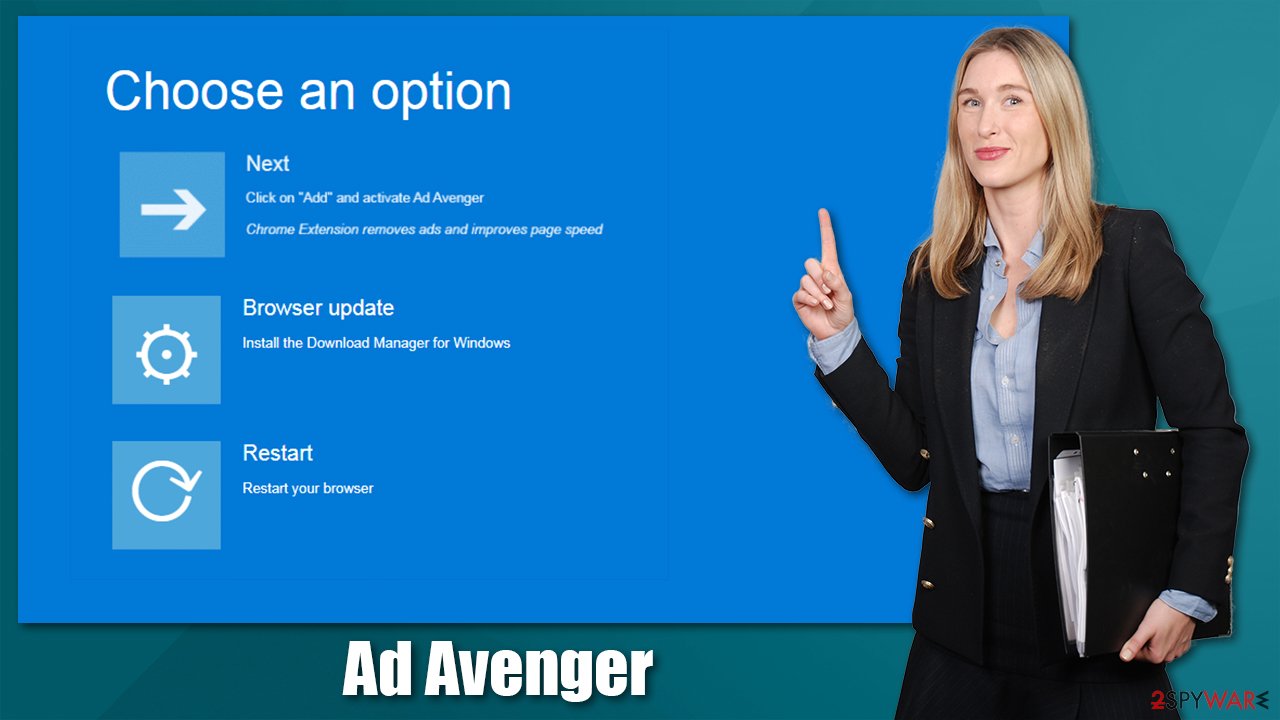
While the app can be downloaded from the official Chrome Store and the official website, it is now how most users acquire this extension. Instead, they either download it inadvertently via a software bundle from a third-party website or after being tricked by a misleading advertisement. In this case, the extension ad tries to imitate a Blue Screen of Death error interface.
This misleading technique is very common and is used by malware[2] authors to spread their creations around. Misleading information, attributes, and messages are commonly shown to users in various social engineering attacks. This is one of the red flags when dealing with unknown programs, browser extensions, or applications – never trust those that are spread using malicious methods, such as fake updates or misleading ads.
Once installed on the system, Ad Avenger does not make any visual browser changes, unlike many other browser hijackers (they typically change homepage/new tab URL and append an alternative search provider). However, the suspicious activity can be felt relatively soon after the application is installed – an increased number of ads is the main one.
However, with the help of the permissions that the app requires upon installation, it can read and change all the data on all websites. While it is not unusual for such extensions to require these permissions, it allows them to collect data about users for marketing purposes.
In any case, if you have installed the app and it did not match your expectations (or you can't recall installing it in the first place), you can easily get rid of it. We explain everything you need to know below.
| Name | Ad Avenger |
|---|---|
| Type | Browser hijacker, potentially unwanted application |
| Distribution | Fake advertisements, software bundles, official sources |
| Symptoms | An extension or application is installed on the system; various websites display intrusive pop-ups, banners, and other types of ads |
| Risks | Installation of other potentially unwanted programs/malware, personal data disclosure to unknown parties, monetary loss |
| Removal | To remove browser extension, access the settings of your browser, although we strongly recommend running a scan with SpyHunter 5Combo Cleaner security software |
| Optional steps | After you eliminate all PUPs from your system, make sure you clean your web browsers and repair system files. You can do that automatically with FortectIntego or refer to our manual guide |
While some websites are relatively respectful to users and show discreet ads that do not negatively impact their experience, plenty of sites use full-page, intrusive ads that change the place of page components and make it difficult to access the contents. Unfortunately, this keeps happening even on the most prominent websites that specialize in news or entertainment.
While it is easy to avoid sites like that (people simply look for alternatives for a better experience), some ads simply can't be avoided. That is where ad-blockers shine – they can be useful in many ways. Millions of users download them to prevent intrusive advertisements from ruining their browsing experience.
Stopping annoying ads is just one part of the ad-blockers operation, as it can also prevent malicious JavaScript from being executed from malicious websites, essentially preventing automatic malware infections and computer compromise.
Unfortunately, there are downfalls as well. First of all, some websites might require users to disable them in order o access the site's contents. Likewise, some websites simply break due to their functionality, as they block components necessary for the site's operation. Finally, it prevents content creators from monetizing their content, so it would be thoughtful if users would turn it for creators they care about.
Overall, an ad-blocker is a great tool that improves browsing quality and prevents dangerous scripts from being executed. However, not all ad-blockers are useful or even safe. We have shown plenty of deceptive ad-blockers that insert their own ads, sell user data, or even redirect to malicious websites. Good examples are Adblocker for YouTube, Nano Adblocker & Nano Defender, Supreme Adblocker, and many others. Ad Avenger joins this extensive list.
Browser hijacker authors commonly use deceptive distribution methods
While many potentially unwanted programs can be downloaded from their own websites or even official stores (for example, Ad Avenger can be downloaded from the Chrome store), it is not the main distribution method used by the authors. In most cases, people get tricked into installing Ad Avenger n their systems by the following:
- Fake advertisements
- Software bundles
Fake ads can be encountered everywhere on the internet, but places like torrents on illegal video streaming sites are common ground for malicious content. In this case, it was spotted that the app was distributed via a fake Blue Screen of Death[3] advertisements.
Software bundling is also a very common PUP delivery method – it remains one of the most popular ones due to its success rate. Users typically rush the installation of free programs they download from third-party websites, and this aspect is used to trick people into installing additional components.
For example, if they pick Recommended settings, it gives permission for the installer to implement components that were otherwise hidden. To uncover them, users need to select the Advanced installation method, which would allow declining all the optional installs. You should also pay attention to things like fine print, pre-ticked boxes, and similar tricks.
If you never installed the app yourself and you spotted that your browser is redirecting you to ad-filled, scam, and similar unwanted websites, and shows you ads everywhere you go, you should uninstall Ad Avenger from your system, as it might be the cause of this unwanted activity. In order to be successful at this, follow the detailed instructions in the section below.
Removal of browser hijacker
Unusually, browser hijackers are not difficult to eliminate, especially those that come as browser extensions (with a few exceptions). Their main operation surface is the browser, as the hijacker uses it to deliver advertisements. Therefore, if you want to remove the unwanted ads, you should start with eliminating the extension first.
Step 1. Get rid of the extension
Browser extensions are easy to remove. If you have never done this before, we provide the guide below.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.

MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Step 2. Scan your system with security software
Security software should be installed on all devices, be it a desktop computer or a phone. Malware is just way too profitable for cybercriminals and they constantly come up with new ideas on how to make it more prevalent. The unfortunate thing is that malware is usually very sneaky and very hard to notice for regular users.
Thus, to protect yourself from dangers and remove malicious software from a machine, you should perform a full system scan with SpyHunter 5Combo Cleaner or Malwarebytes anti-malware. This would ensure that not only other potentially unwanted programs but also malware is terminated appropriately at once.
Step 3. Clean your browsers
Browser hijackers and other potentially unwanted programs are known to gather various information about the web browsing practices of those who have them installed. Typically, the collected data includes the IP address, device ID, approximate location, technical machine information, browser type and language, search queries, visited websites, and much more. The information is used for various purposes and is often shared with third parties.
For the data collection to be successful, tracking technologies like cookies are used, and they remain on the device for a very long time. Thus, it is recommended to clean the browsers from time to time, especially after the removal of potentially unwanted applications. You can either use the instructions below or employ FortectIntego maintenance and repair utility.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

How to prevent from getting browser hijacker
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ PUPs Explained: What is a “Potentially Unwanted Program”?. How-to Geek. Site that explains technology.
- ^ What is Malware?. Forcepoint. Cyber Edu.
- ^ Tim Fisher. Blue Screen of Death (BSOD). Lifewire. Tech News, Reviews, Help & How-Tos.
