Amazon order confirmation scam (Free Guide) - Removal Instructions
Amazon order confirmation scam Removal Guide
What is Amazon order confirmation scam?
Amazon order confirmation scam is a malware campaign that is distributing banking trojans
Amazon order confirmation scam is a malspam campaign that focuses on online shoppers. Its main principle is to act as an order confirmation email which is trying to reach people who have purchased goods on Amazon. Once the target is found, the scam campaign delivers malware disguised as a link to an order and shipping information. At the moment, Amazon order confirmation virus is an infamous Emotet banking trojan. However, it can be changed to any other virus. The particular campaign is using “Your Amazon.com order,” “Amazon order details,” or “Your order 162-2672000-0034071 has shipped” subject lines. Trojan payload gets dropped on the system as an executable file and then it runs in the background without user's knowledge.[1]
| Name | Amazon order confirmation scam |
|---|---|
| Type | Spam email campaign |
| Purpose | Distributes banking trojan and other malware |
| Spreads | Emotet |
| Disguised as | Order confirmation emails from Amazon |
| Executable files |
|
| Removal | Scan the system using FortectIntego and clean the device after Amazon order confirmation scam removal |
Amazon order confirmation scam virus attacks the system as a well-disguised email campaign which reports about the order confirmation details. Having in mind how active are people during the Christmas time, these emails look very convincing and can easily lure them into opening the message without thinking that it could be unsafe.[2]
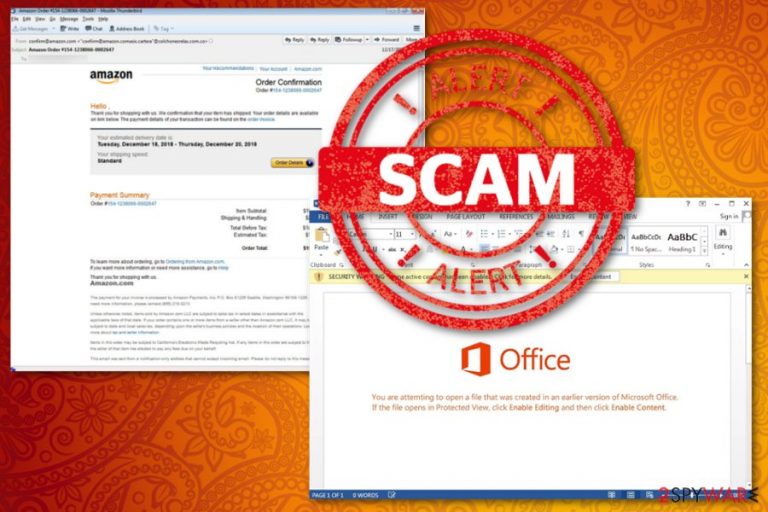
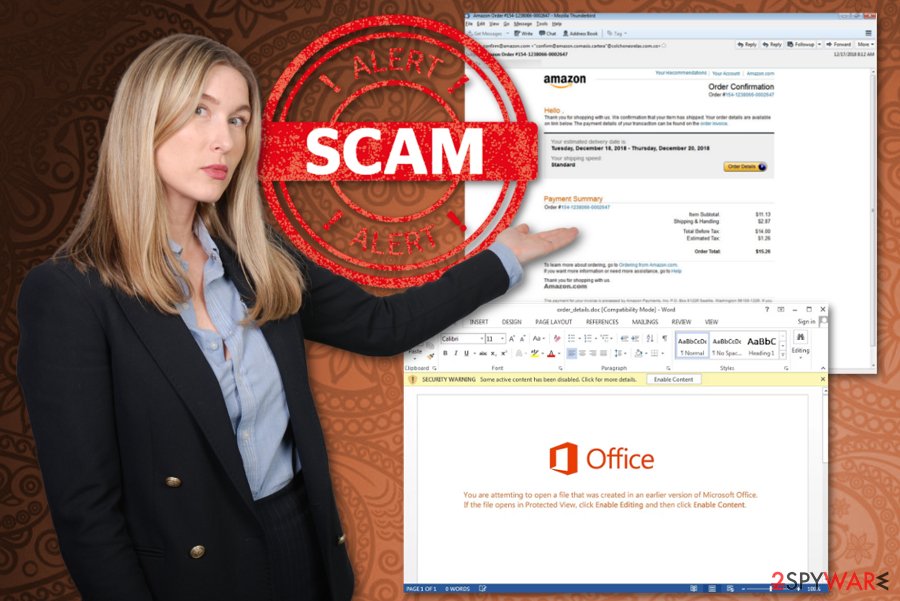
However, when you open the email with the fake Amazon order confirmation, you get no details about the package tracking that is allegedly shipped or any other information about the order you purchased. It seems that the only way to get details about the order is to open the attachment or the active button named Order Details.
Unfortunately, when you click the button, the Amazon order confirmation scam starts automatic download which loads order_details.doc on the computer. When this file gets opened on the system, the window with confirmation appears.
The window states about the requirement to enable editing or content to properly view the order details and other information regarding your package. But malicious macros get triggered the minute you click on the suggested link or button. Then Amazon order confirmation scam executes PowerShell commands and downloads Emotet banking trojan or other malicious malware.
When the main campaign starts running according to the plan, your computer starts running slow due to the additional activity in the background. You need to remove Amazon order confirmation scam as soon as possible, as many researchers note[3] malware that gets automatically installed can:
- log keystrokes;
- steal account information;
- collect various data stored on the device;
- steal and later use logins and passwords;
- run additional crypto mining or similar processes;
- use resources of your device.
Employ reputable anti-malware tools for the proper Amazon order confirmation scam removal and scan the device thoroughly because there is a great danger that you are infected with Emotet banking trojan. Leaving it on the system can lead you to financial losses and identity theft. During the full system scan, antivirus programs will indicate all viruses hiding on the system. Additionally, use FortectIntego to fix the virus damage. Don't underestimate viruses as they can easily change different system's settings to enable needed commands.
Paying more attention to emails before opening documents may be crucial
During this time of the year, it is easy to fall for various scams and other malicious campaigns so paying attention to who is sending the emails before attempting to open the attached documents may affect the security of your machine. Especially, during the busy time like Holidays when it is common o get such order information emails or notifications from such big companies.
When receiving emails, make sure to confirm that the email is useful and legitimate. If you are not using the service or company be aware of such scams and legitimate-looking malicious email campaigns. You can delete the suspicious email or scan the document before downloading and opening on the computer.
Terminate Amazon order confirmation scam associated processes and programs
Amazon order confirmation scam removal is a must as you can be infected with Emotet virus which can cause serious problems. Do not attempt manual virus termination procedure, as Emotet is a banking trojan which can't be removed manually due to its maliciousness. Besides, this scam can be used for distributing other malware that tends to run in the background without the user's knowledge, and you cannot be found easily.
A better option for users seeking to remove Amazon order confirmation scam and related viruses is using anti-malware programs like FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes. These tools start with a full system scan and indicate what possible intruders are found on the machine. This way, you can delete all possible threats, fix virus damage and clean the system.
You may also need a few additional tips because Amazon order confirmation scam virus is a persistent threat. Follow your guides and tips below to clean the device from malware thoroughly.
Getting rid of Amazon order confirmation scam. Follow these steps
Manual removal using Safe Mode
You may need to reboot the machine in Safe Mode before system scan to make sure every malicious Amazon order confirmation scam file is deleted:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Amazon order confirmation scam using System Restore
Trey System Restore feature as a method for virus elimination:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Amazon order confirmation scam. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Amazon order confirmation scam and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting viruses
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Vangie Beal. The difference between a computer virus, worm and trojan horse. Webopedia. Online Tech dictionary for IT professionals.
- ^ kate Gibson. Holiday scams - and how to avoid them. CBSnews. Broadcasting service.
- ^ Avirus. Avirus. Spyware related news.







