Arachidenews.com ads (fake) - Free Instructions
Arachidenews.com ads Removal Guide
What is Arachidenews.com ads?
Arachidenews.com ads can redirect users to malicious websites
Arachidenews.com may begin appearing on your devices without warning. This activity can be seen on various operating systems, such as Windows and macOS, or mobile devices, like Android phones or tablets. However, its primary way of operation is through web browsers like Google Chrome, Mozilla Firefox, MS Edge, etc., so in order to get rid of these intrusive pop-ups, users would have to change settings within their browser of choice.
Contrary to popular belief, Arachidenews.com ads are not caused by computer viruses. Adware might be the main reason for browser redirects and increased ad activity, but this issue is more related to allowing a malicious website to show push notifications without restrictions. As such, the removal of push notifications can only be done manually – as explained below. We will also provide instructions for ensuring adware[1] and other unwanted software are removed effectively.
| Name | Arachidenews.com |
| Type | Push notifications, ads, pop-ups, scam |
| Distribution | The website gains access to deliver any information as soon as the “Allow” button is pressed within the push notification prompt |
| Symptoms | Push notifications from the site show up on the desktop. These pop-ups show fake notices and push scams. Links can also lead to websites filled with malware |
| Risks | Shown pop-ups incorporate fake notices and push scams. Links can also lead to websites filled with malware |
| Removal | Access browser settings to stop unwanted push notifications. After that, make sure that your system is not infected with adware or malware – scan it with SpyHunter 5Combo Cleaner |
| Other tips | It is important to clean your browsers after removing potentially unwanted programs from your system – use FortectIntego for quick and reliable results |
Scammers use social engineering to trick users
The initial and most vital step to the success of Arachidenews.com's scam is the element of surprise that the majority of users experience after running into the site by chance. This typically happens when people are visiting insecure websites, like torrent sites or other places where illegal software is distributed.
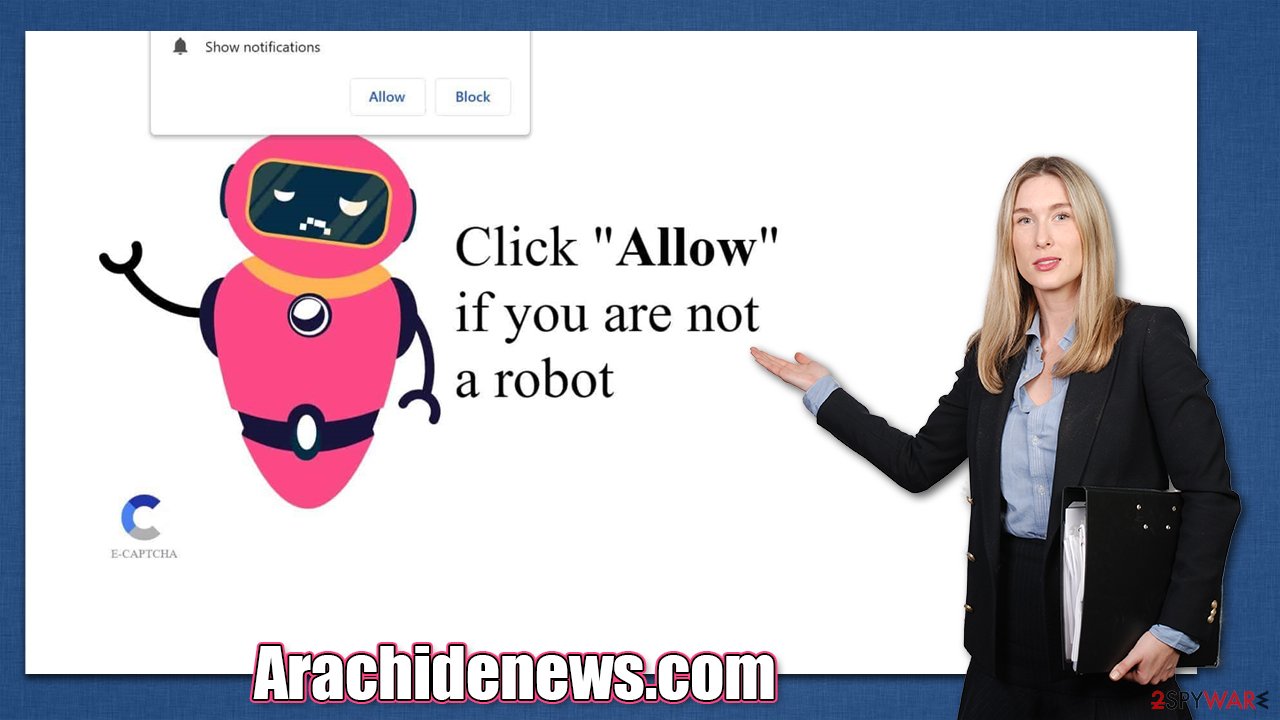
When users are unexpectedly redirected to a page, they don't see what they were expecting, which can catch them off guard. What they see is usually a request that makes sense at the moment but can be easily confused with legitimate elements they've encountered before. Here are a few examples:
- Click “Allow” if you are not a robot
- If you are 18+, tap Allow
- Your file is ready to download – press Allow to continue
- Can't play this video! Browser may block video autoplay… Click “Allow” to play the video
- Just one more step! “Allow” to continue.
These requests are specially crafted in a way to resemble legitimate ones: users previously have encountered websites that ask to confirm their age or that they are indeed human, not bots. In other cases, users are given reasons to press the Allow button that could also make sense, for example, that a browser is stopping a video from being played.
In reality, all of this is social engineering[2] which is cleverly used by scammers behind Arachidenews.com and similar push notification scam sites. The push notification feature is not malicious in any way – it was intended for legitimate purposes until cybercriminals realized that it could be used to deliver intrusive and malicious ads directly to users' desktops, as long as they come up with an excuse to make them click the Allow button within a fake website.
How to deal with adware and other malicious programs
Adware is a type of potentially unwanted software that can be encountered from various sources, such as software bundle packages downloaded from third-party websites or misleading or fake advertisements. Some people may install adware intentionally without fully understanding its capabilities and potential impact on their device.
Adware can display ads on a user's device, often in the form of pop-ups or banners, and can collect data about the user's online activities in order to target ads more effectively. It is important for users to be cautious when downloading software from unknown sources and to pay attention to any warning messages that may indicate the presence of adware.
If you have been encountering dubious websites like Arachidenews.com, Timelyoffersd2.click, Sulseerg.com, and others and seeing more ads than usual, you should definitely check your system for adware – the easiest way to do so is by scanning the system with SpyHunter 5Combo Cleaner or Malwarebytes anti-malware software.
Keep in mind that security software will not clear cookies[3] and some other leftover files, so we recommend using FortectIntego for that purpose. The maintenance and repair tool can also fix various damage caused by malware, which would resolve system crashes, errors, slowdowns, etc.
Removal of Arachidenews.com ads
As mentioned before, many users assume that the annoying push notifications are related to some kind of malware infection because the activity comes seemingly out of nowhere, is disruptive, and also might be showing suspicious content. Even after scanning the system with security software, users would not be able to get rid of these pop-ups because their access to doing so needs to be blocked via browser settings as follows:
Google Chrome (desktop):
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and choose Block. This should remove unwanted notifications from Google Chrome.

Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

Internet Explorer:
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
- Locate web address in question under Allowed sites and pick Remove.

How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Adware. Investopedia. Source of financial content on the web.
- ^ What is Social Engineering?. Knowbe4. Security awareness and training solutions.
- ^ What are cookies? | Cookies definition. Cloudflare. The Web Performance & Security Company.
