Ballacks ransomware (virus) - Free Guide
Ballacks virus Removal Guide
What is Ballacks ransomware?
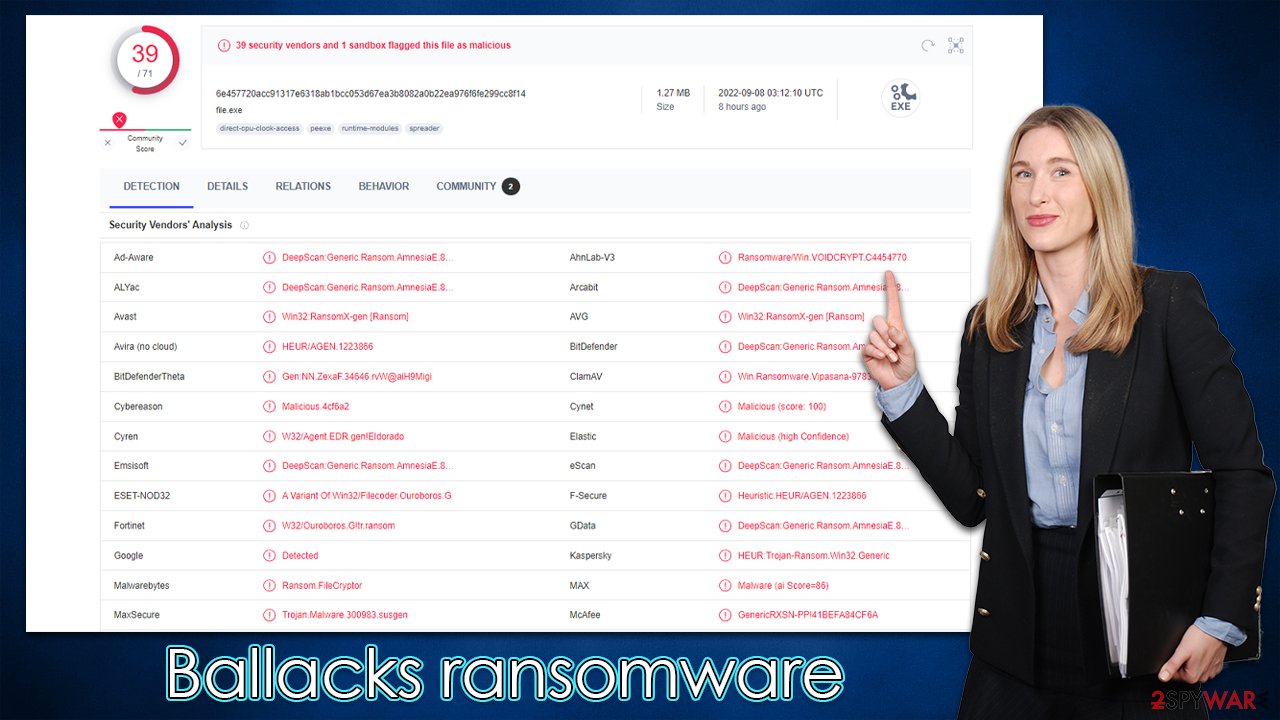
Ballacks ransomware is a VoidCrypt variant that locks personal files and asks for a payment

Many individuals have extensive collections of personal files on their laptops – photos, videos, home projects, and confidential documents – yet few believe they could ever lose access to them. Unfortunately, this happens when Ballacks ransomware – VoidCrypt variant – infiltrates a Windows computer and encrypts[1] all the personal files situated there.
Typically, ransomware enters users' machines using some form of phishing, for example, spam emails that include malware-laced macros[2] are one of the most common ways of being infected. Alternatively, some cybercriminals rely on more advanced methods, such as those exploiting software vulnerabilities on users' computers. In short, people don't install the virus on purpose.
Once on the system, the Ballacks virus would search for data to encrypt and would append the .ballacks extension to each of them immediately (user ID and email are also used – they are attached before the extension). Suchlike data would also lose the regular logos, making it immediately noticed that something's wrong.
Without being able to open files, users are often lost as to what to do next, and some answers are provided in the ReadthisforDecode.txt ransom note. We recommend not interacting with attackers and solving the problems in alternative ways, which we describe below.
| Name | Ballacks virus |
|---|---|
| Type | Ransomware, file-locking malware |
| File extension | .(ID)((email).ballacks |
| Malware family | VoidCrypt |
| Ransom note | ReadthisforDecode.txt |
| File Recovery | The most reliable method to retrieve lost data is by using backups. If this is not an option or the files were encrypted as well, chances for recovery are very limited – see all potential solutions below |
| Malware removal | Remove the computer from the network and the internet, then run a complete system check with SpyHunter 5Combo Cleaner security software |
| System fix | If malware is installed on your system, it can potentially damage or corrupt crucial system files, which often results in crashes, errors, and other stability issues. FortectIntego PC repair software can automatically fix any such damage by replacing corrupted files |
About the VoidCrypt strain
Ballacks ransomware is one of the numerous variants of VoidCrypt, which is generally an established malware family operational since at least early-mid 2020. In these few years of its operation, crooks behind it had released dozens of variants we have previously talked about – HIP1, Angry, and 1more are just a few examples of such.
While the likes of other prominent ransomware families, such as Djvu, which consistently releases variants almost identical to one another (the extension differs), VoidCrypt authors take a little different approach, even though similarities are visible.
For example, all versions employ a similar pattern when using file appendixes (ID, email, and extension), although ransom notes themselves seem to be written individually for each variant – they also name the notes differently almost every time. While malware initially used AES and RSA encryption algorithms to lock data, this may vary with the newer versions.
How to tackle Ballacks virus infection correctly
Unfortunately, most people who get infected with ransomware are first-timers, which often means that they know little about the infection or how to handle it. Indeed, it is important to perform the steps in the correct order to avoid further damage to the encrypted files of the OS.
1. Remove malware after disconnecting the internet
When dealing with ransomware, the first thing to do is get it off of your computer. Because malware might be exchanging information with attackers over the internet, you should turn off your WiFi or Ethernet connection right away. You may then try downloading Malwarebytes or SpyHunter 5Combo Cleaner antivirus software and cleaning your PC completely to remove the infection at once.
It is important to note that in some cases, malware may interfere with the operation of security software to prevent victims from removing it. Most commonly, this is done in order to continue encrypting files or running other malware in the background. If that is the case for you, you can access Safe Mode and remove Ballacks ransomware from there:
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on the Start button and select Settings.
- Scroll down to pick Update & Security.
- On the left side of the window, pick Recovery.
- Now scroll down to find the Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.

2. Attempt the file recovery
Encryption makes files unreadable without a key, which is often stored on a server operated by hackers. They can then use the user ID to figure out which key decrypts which victim's files. Each of the keys assigned to victims is different, hence it is not a password-for-all type of situation.
Data encryption and virus infection are two separate events, both of which should be addressed as distinct circumstances. This indicates that by scanning your computer with antivirus software, you will remove all dangerous files that would otherwise continue to operate and encrypt all incoming documents, for example. What this would not accomplish is restoring files, and they would remain locked. This is one of the most dangerous traits of ransomware.
While it is true that cybercriminals are likely to hold the key to Ballacks ransomware-encrypted files, it is never worth the risk of paying – you may lose your money along with files. Thus, we recommend going the alternative route, even though it may not be successful every time.
If you have data backups, you can restore your files as soon as you remove malware from your device. However, if you don't have them, you should first make copies of encrypted files first before proceeding with the following steps, or you may corrupt data beyond repair. Once done, you can start with data recovery software as such:
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
Because of the work of security researchers, decryption tools for certain ransomware strains may also be developed. In some circumstances, competent authorities obtain the servers of criminal organizations and release their keys to the public – which is generally performed by reliable security companies. Here are a few links to get you started:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

Malware might be able to do a lot of harm to Windows systems, requiring a complete reinstallation in some situations. An infection, for example, may modify the Windows registry database, damage bootup files and other sections, remove or corrupt DLL[3] files, and so on. Antivirus programs can't restore damaged files; instead, specialized software should be utilized – FortectIntego is one of the best options available.
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Encryption. Investopedia. Sharper insight, better investing.
- ^ Malicious Macro. Blumira. Detection & Response.
- ^ What is a DLL. Microsoft. Documentation.
