Brkdown.com (Removal Guide) - Free Instructions
Brkdown.com Removal Guide
What is Brkdown.com?
Brkdown.com is a scam site you should never download software from
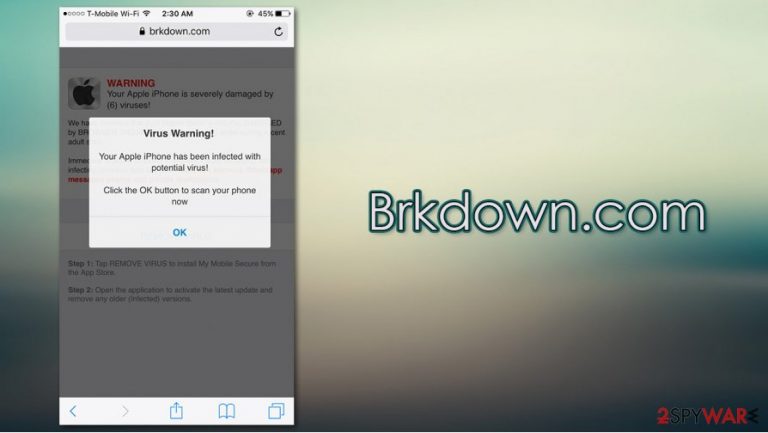
Brkdown.com is a malicious website that you could encounter at any time when browsing the web via Google Chrome, Mozilla Firefox, MS Edge, or another web browser. While the web page could be encountered on all platforms, iPhone or Mac users are the ones who are most commonly targeted. The website is known to promote all sorts of fake claims and scams with the intention to make users download potentially dangerous software on their devices.
The Brkdown.com popup claims that “they” (whoever they are) have detected a number of Trojans,[1] viruses, and other malware on the device due to browsing of “corrupted sites.” According to the message, the offered security application needs to be installed in order to prevent theft of sensitive data, such as Facebook/WhatsApp logins and private messages, as well as photos located on the device. It is important to note that no websites can detect malware on your system, hence Brkdown.com is a scam and should never be trusted.
| Name | Brkdown.com |
| Type | Phishing, scam, fake alert |
| Claim | The message says that malware was found on the device, and that the login credentials of Facebook and other social networks, personal photos, and other sensitive data will be stolen |
| Goal | The main goal is to make users download a suspicious application for the fake virus elimination |
| Distribution | The popups and redirects to the site can be encountered after clicking on a malicious link or after being redirected by adware or another potentially unwanted program |
| Related | Your Apple iPhone is infected, Your system is infected with 3 viruses |
| Elimination | If you did not download anything, you a are unlikely to be infected; however, we recommend checking the system with anti-malware or looking for adware programs manually |
| Further steps | You should perform a full system scan with anti-malware and then remediate the computer or phone with FortectIntego repair tool |
First of all, before understanding the goals and principles of the Brkdown.com scam operation, it is important to know how you can get there. Without a doubt, you did not type in the web address to land on the site. However, you are likely to be redirected to it after visiting a suspicious website (torrents, video-streaming, gambling, X-rated, and similar). These automatic redirects are typically executed thanks to JavaScript[2] or other background processes. You might also encounter the Brkdown.com virus alert after clicking on a link.
In some rare cases, you might be infected with adware – a variation of a potentially unwanted program category, which specializes in browser takeover, redirects to suspicious websites, intrusive ad campaigns, as well as background information tracking for marketing purposes. Thus, if Brkdown.com redirect is persistent, you should either check for PUPs manually or scan the device with powerful anti-malware, such as SpyHunter 5Combo Cleaner or Malwarebytes.
However, please keep in mind that all the claims you see on the message that is shown to you on the site it bogus – Trojans and other malicious programs are unlikely to reside on your device. Even if so, it would not be related to this “detection,” as websites generally can't detect and diagnose infections of the device.
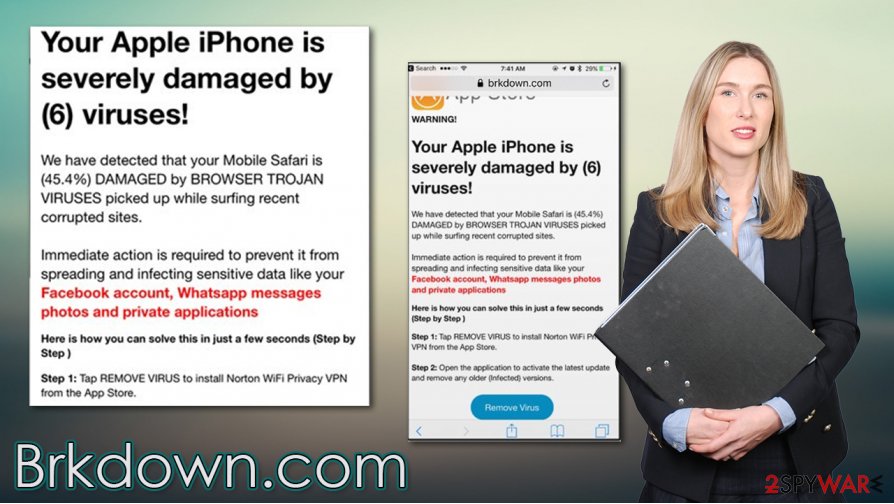
Upon Brkdown.com entry, you might encounter several different variations of the scam. Here is an example that promotes the “Your Apple iPhone is infected” scam:
Your Apple iPhone is severely damaged by 19 viruses!
We have detected that your Browser is (59%) DAMAGED by BROWSER TROJAN VIRUSES picked up while surfing recent corrupted sites.
Immediately install mobile security application or sensitive data like your Facebook account, WhatsApp messages, photos and private applications will be infected and stolen.
[Install] [Cancel]
The Brkdown.com popup looks very plain, although it does include the Apple devices' settings logo, which might make some people think that the message is legitimate. The first red flag is that the pop-up is not coming from an official source. It also attempts to intimidate users by applying a timer, creating a sense of urgency.
Do not worry, your social media accounts are safe. However, you should remove Brkdown.com popup by simply closing down the web page immediately. No matter what you do, do not download and install the promoted applications, as it could easily result in malware infections.
If you did install something, Brkdown.com removal might become a bit more difficult. First of all, you should check the installed program section of your device. However, the best way to eliminate all potentially malicious software is by scanning your Mac or another device with SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable software. To remediate the system, experts[3] also recommend using FortectIntego.
Ways to recognize online scams and avoid adware infections
As mentioned above, adware could be one of the main causes you see scams on your device. These PUPs might take over the web browser and inserts ads everywhere. Unfortunately, some of those ads or redirects might be deceptive and, in some cases, even dangerous. Therefore, it is best to ensure that your phone or desktop computer is adware-free. For that, consider practicing the following:
- If possible, only download apps from official sources (App Store, Google Play, etc.);
- Never visit torrent or similar sites that distribute software cracks or pirated application installers;
- During the installation of third-party software, always opt for Advanced/Custom settings instead of Recommended/Quick ones – it will let you stay in control of the process;
- Remove all the ticks from the pre-ticked boxes, read the fine print, and watch out for misplaced buttons.
Online scams might also be encountered randomly on thousands of malicious websites. Therefore, it is important to recognize them not to be tricked. As previously noted, phishing and scam sites are often used to make users download malicious software, provide sensitive information, or waste money on useless apps. Never downloads anything from sites that claim your device is infected with malware – they can not diagnose such intricacies. Always check the URL of the page you are visiting, as it will be an unknown address that has nothing to do with official sources such as Apple.
Eradicate Brkdown.com scam pop-ups for good
First of all, it is important to note that if you saw the Brkdown.com virus notification for the first time, you should not panic and simply close down the tab or the web browser. However, if you downloaded and installed software suggested to you after being intimidated by the message, Brkdown.com removal would work slightly differently.
First of all, if you are using an iPhone, go to Settings > Safari and then enable Block Pop-ups and Fraudulent Website Warning feature. This will prevent websites from showing you scam notifications in the future.
Now, you should ensure that your system is safe and not infected. For that, you can either visit the installed app section of your device and look for inconsistencies. If you are not quite sure what you are doing, you should instead rely on powerful security tools – they could remove Brkdown.com scam leftovers and all the associated malicious programs within just a few minutes.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Brkdown.com. Follow these steps
Uninstall from Windows
To uninstall potentially unwanted programs from Windows machines, access the Programs and Features section via the Control Panel:
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
If your Mac is showing adware infection signs, proceed with the following instructions:
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
You should eliminate all the extensions from Chrome, as they could be the reason why you are facing redirects and ads:
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
You can reset Safari to ensure that no suspicious settings are present on it:
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Brkdown.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting mac viruses
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Trojan horse (computing). Wikipedia. The free encyclopedia.
- ^ Andra Zaharia. JavaScript Malware – a Growing Trend Explained for Everyday Users. Heimdal Security. Security research.
- ^ Novirus. Novirus. Cybersecurity insights and advice.
