Your Apple iPhone is infected (Removal Guide) - 2020 update
Your Apple iPhone is infected Removal Guide
What is Your Apple iPhone is infected?
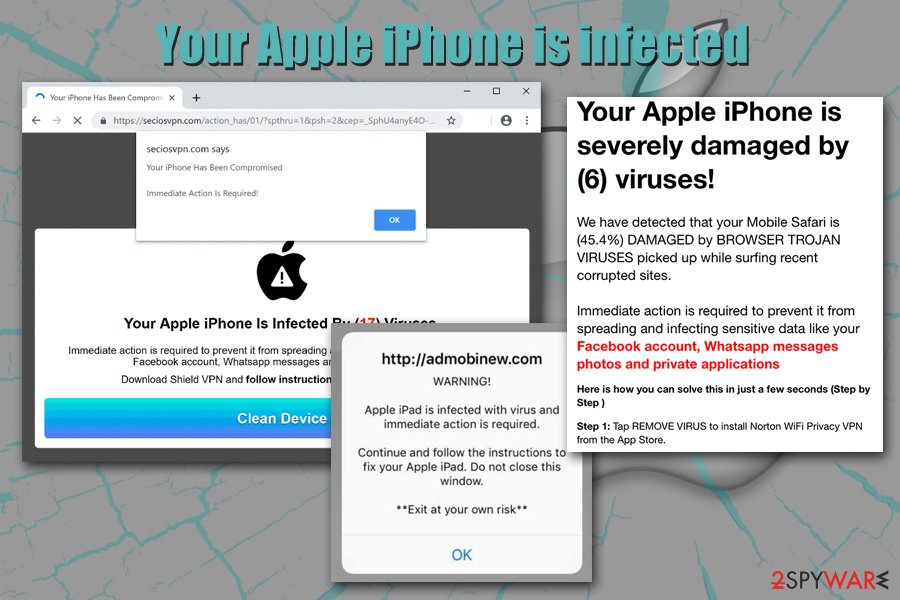
Your Apple iPhone Is Infected By (17) Viruses – fake notification that mainly pops up for iPhone users, but sometimes could also be seen on other devices
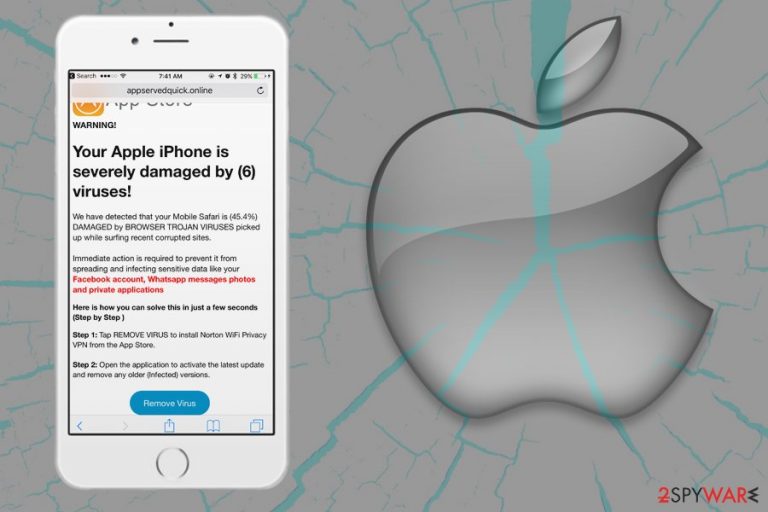
Your Apple iPhone is infected (also known as Your Apple iPhone Is Infected By (17) Viruses) is a fake iPhone virus pop up that users might encounter on various devices, although the scam originally targets iOS users. Nevertheless, this notification can appear seemingly out of nowhere on Safari, Google Chrome, Mozilla Firefox, or any other used browser. The main goal of Your Apple iPhone is infected scam is to make users download suspicious or even malicious applications, as well as disclose their sensitive information, such as credit card details.
Regardless of which device users encounter the Your Apple iPhone Is Infected By (17) Viruses pop-up, it can happen due to two main reasons: either the iPhone/Macintosh/Macbook is infected with adware[1] or they stumbled upon a malicious website on the internet. The best thing to do after seeing Your Apple iPhone is infected notification is to completely ignore it – simply leave the page or even close down the browser. It is also important to find out whether the notification is not a sign of adware infection – we will explain how to deal with it later.
| Name | Your Apple iPhone is infected |
| Alternative names | Your Apple iPhone is infected by (17) viruses, Your Apple iPhone Is Infected By (6) Viruses |
| Type | Online scam |
| Category | Mac virus, Mac malware |
| Similar scams | Immediate Action Required, Your system is infected with 3 viruses, Your Mac Might Be Infected |
| Goal | The main goal of the scam is to make users download potentially unwanted programs or disclose sensitive information |
| Cause of appearance | While in most cases users can encounter specially compiled scam messages online accidentally, some such devices might be affected by adware, which is typically spread with the help of dubious software distribution technique called bundling |
| Associated risks | Users might install malware that is programmed to perform various malicious activities on the device, e.g., steal sensitive information, send spam, install other malware, etc. |
| Solution | The best way to terminate the unwanted activity related to “Your Apple iPhone is infected” is a scam the device with anti-malware software |
| Further actions | For best results, we recommend resetting all the installed browsers and performing system scan with FortectIntego |
Online fraud[2] has been prevalent for many years now – it is aimed to convince inexperienced users to do something they otherwise would not do with the help of social engineering.[3] While some campaigns are made relatively easily-recognizable, crooks do no rush to check their grammar and spelling mistakes even now, as they know that there are plenty of internet users who do not speak English that well and would not know the difference. Your Apple iPhone Is Infected By (17) Viruses scam has several versions, some of them are written better, some – worse.
These social engineering attacks are conducted by unfair people who join an affiliate marketing scheme to sell their products online and use the allocated online space for their promotions. However, instead, they plant a malicious Your Apple iPhone Is Infected By (17) Viruses or similar message on it. Thus, as soon as users are redirected to the page, they receive the following message:
Your Apple iPhone is infected by (17) viruses.
If not resolved immediately, the virus will crash your cell phone, damage the SIM card and delete all your contacts.
Follow the instructions below to remove the virus.
A similar version of the Your Apple iPhone is infected scam prompts users to download a Shield VPN application (note: never download it, as it might be fake):
Your iPhone Has Been Compromised
Immediate Action is Required!
Your Apple iPhone is infected by (17) viruses.
Immediate action is required to prevent it from spreading and infecting sensitive data like your Facebook account, Whatsapp messages and private applications
Download Shield VPN and follow instructions to clean your device.
Because typical Apple logos and the design of the Your Apple iPhone is infected by (17) viruses pop-up are used, some might believe that the message is coming from the tech giant itself. However, reputable companies would never prompt users to download anything in such ways – they have legitimate means of notifying users about any type of issue. Additionally, the biggest paradox is that users might encounter the Your Apple iPhone is infected notification on any type of device, which would not make any sense.

Besides, a “virus” is a type of malware that does not apply to macOS devices, as each application of these computers is segregated in its own sandboxed environment. Nevertheless, it does not mean that Macs cannot be affected by malware.
Thus, you should not interact with the scam and remove Your Apple iPhone Is Infected By (17) Viruses message from your browser immediately by closing the tab it is shown in. If, however, you noticed that your browsers are directing you to sites that display such scam messages often, you also need to ensure that your device is not infected with adware.
If adware is involved, Your Apple iPhone is infected removal from your browser is not going to be enough, as the potentially unwanted application will keep bringing you scam sites and exposing you to pop-ups, deals, offers, coupons, and other commercial content that is not only disturbing web browsing sessions but might also be dangerous.
The easiest way to get rid of unwanted applications as well as pop-ups like “Your Apple iPhone is infected by (6) viruses” is to scan the device with anti-malware software, although the termination process can also be performed manually – check the instructions below.
Ways crooks can expose you to online scams
As mentioned above, the fake iPhone virus pop up notifications and increased amount of advertising is often a sign of adware infiltration. Adware is one of the main cyber threats that plague Apple devices and, although not initially malicious, can cause major web browsing disturbances and bring users to scam and phishing sites. As a result, while adware on itself will mostly not steal your personal information or install malicious software automatically, it can link you to sites that could result in such an outcome. On the other hand, many users don't mind apps that show ads discreetly – this the precise requirement that major app stores demand from application developers.
Speaking of which, the main way to get infected with adware is to download software from unapproved sources, as these are known to bundle multiple apps into single installation packages and deliberately hide the optional components from users' sights during the installation process. Thus, if you still desire to install apps from external (non-official) sources, we suggest you do the following:
- Check if the application you want is not present on Apple Store or other official sources;
- Make sure you click on the correct “Download” button, as shady sites often provide fake buttons in order to make users install sponsored software;
- Once the application is launched, check for permissions it asks from the device – never let an app to have elevated (administrator's) permissions;
- During the installation process, make sure not to get tricked by pre-selected boxes, misleading offers, misplaced buttons, fine print text, and other ploys;
- If prompted, always opt for Advanced/Custom settings instead of Basic/Quick ones – this will let you control the installation better and decline the unwanted apps before finalizing the process;
- Employ anti-malware software that could recognize potentially unwanted applications and stop them prior to their installation.
Get rid of adware that shows you Your Apple iPhone is infected virus alerts
Your Apple iPhone is infected removal depends on many factors – the device you are using, whether it is infected with adware, and if you downloaded any of the applications suggested via the scam. Nevertheless, we suggest you from checking the installed apps on your device and terminating everything that you do not recognize. Additionally, depending on what type of adware app is affecting your device, you might be able to remove Your Apple iPhone is infected automatically with the help of anti-malware software.
If you are struggling with eliminating “Your Apple iPhone Is Infected By (17) Viruses” virus on your iPhone, you should disable the pop-ups and reset Safari as follows:
- Tap on Settings and ten pick Safari
- Select Clear History and Website Data and then confirm
- Now go to Advanced and enable Block Pop-ups and Fraudulent Website Warning features
If you are struggling with continuous pop-ups on your macOS machine, proceed with the manual removal guide below.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Your Apple iPhone is infected. Follow these steps
Delete from macOS
To terminate all the unwanted apps from macOS, please follow these instructions:
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Reset Safari to ensure that adware does not return with the unwanted activity:
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Your Apple iPhone is infected registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting mac viruses
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Lucian Constantin. What is adware? How it works and how to protect against it. CSO Online. Security news, features and analysis about prevention.
- ^ Why does online fraud occur?. Signifyd. Fraud Protection and Chargeback Recovery.
- ^ Social engineering (security). Wikipedia. The free encyclopedia.
