CaptchaResolverHere.top ads (scam) - Chrome, Firefox, IE, Edge
CaptchaResolverHere.top ads Removal Guide
What is CaptchaResolverHere.top ads?
CaptchaResolverHere.top is a scam website that spams users with unending ads
Potentially unwanted programs, namely, adware, is one of the causes for unexpected browser redirects. These ad-supported applications alter web browser settings in order to expose users to all kinds of commercial content for monetary gain. Unfortunately, some of that content might not always be secure, and CaptchaResolverHere.top is one of the places that users end up on either due to adware or after being redirected from another malicious website.
It is not a secret that some people don't realize that they have landed on a scam site; otherwise, there would be no financial losses that so many people suffer from each year. It is true that this particular scheme is not as damaging as tech support or gift card scams, although it still belongs to this category and can cause not only frustration but also to make users exposed to even more dangerous content.
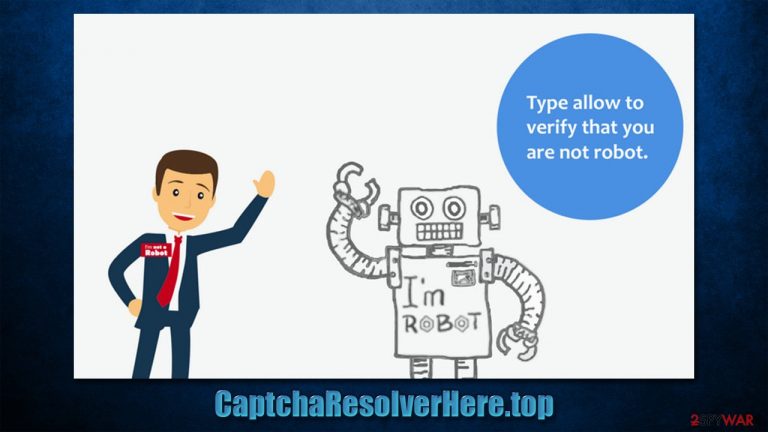
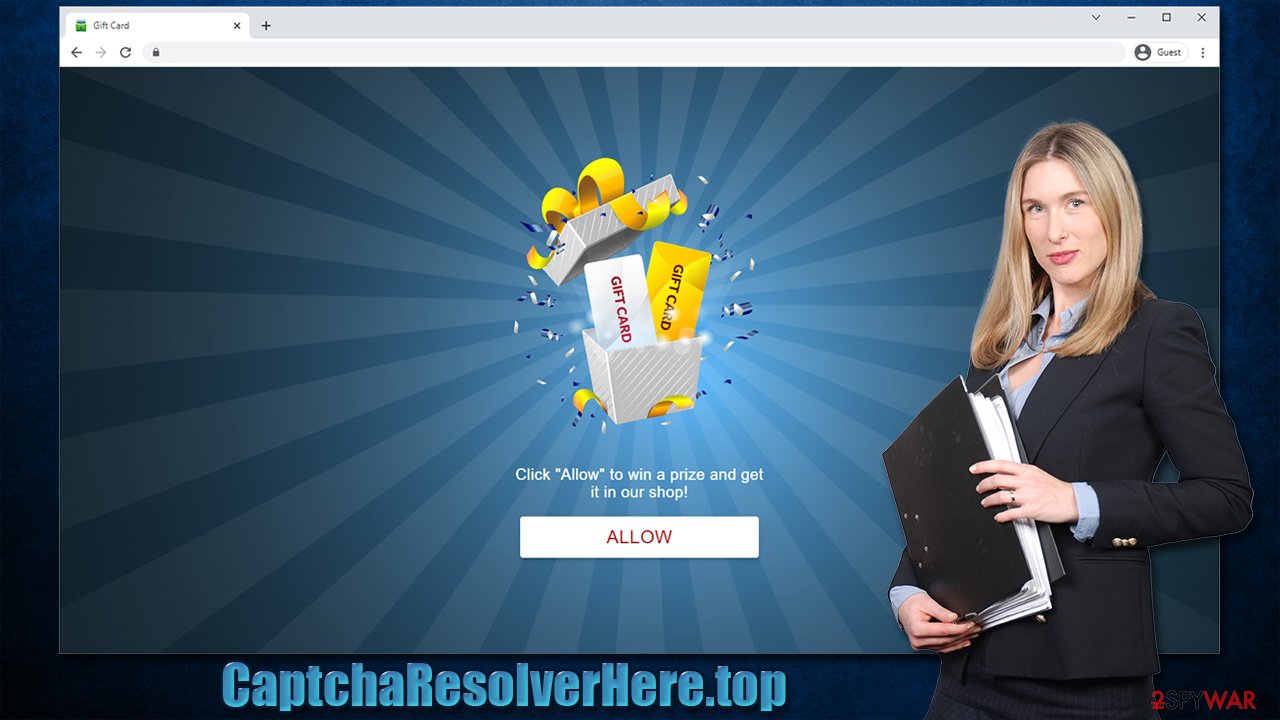
The scheme is relatively simple – the “Allow” button within the notification prompt is simply presented as something completely different and visitors believe that it is a way to watch a promised video or that it is a simple verification step similar to captcha. As soon as people oblige, they have already allowed the site to send them information at any time.
After this, the activity does not start for a while. This is one of the main reasons why people don't know how to remove CaptchaResolverHere.top ads from their computers. They would show up randomly without being triggered by anything, as long as Google Chrome, Mozilla Firefox, MS Edge, or another browser is running or idling in the background.
Without a doubt, it makes the web browsing experience a true nightmare, as the pop-ups are shown on top of everything else running at the time. Likewise, people are at risk of clicking on links accidentally, as well as being tricked into clicking them intentionally. Thus, please do not interact with the content that is presented to you and follow the instructions below to eliminate the unwanted activity once and for all.
| Name | CaptchaResolverHere.top |
| Type | Push notifications, ads, scam, pop-ups |
| Distribution | The entry point is via the notification prompt – users need to press the “Allow” button |
| Symptoms | You may start seeing intrusive pop-ups on your desktop – clicking these may lead to insecure or even malicious websites |
| Risks | Ads and links to sites displayed by the website might be dangerous: users might suffer from monetary losses, install malware or potentially unwanted programs on their systems, or disclose their sensitive data to cybercrooks |
| Removal | To stop the intrusive pop-ups, you need to access the settings section of your browser. You should also check your system with SpyHunter 5Combo Cleaner, Malwarebytes security software to eliminate adware and malware |
| Recovery | Potentially unwanted programs often leave traces within web browsers – cookies, for example, are used for tracking. You should get rid of these leftovers with FortectIntego or employ our manual guide |
How scammers gain revenue from tricking users
Online scams are very prevalent and, while tech companies and regulatory bodies made the internet an overall relatively secure place, users simply can't be protected fully due to the vastness of the internet itself. Thousands of websites are created daily, and thousands or closed due to one reason or another. In many cases, some of these sites are malicious.
There are many different types of scams and phishing sites around, and the content depends on the creators' preferences. Typically, crooks rely on human emotions and/or lack of knowledge in the cybersecurity field. For example, people might be shown a fake prompt that tells them that their computer is overloaded and they need to free some memory, with the solution immediately provided – download this software to do so. We have recently discussed how this phony tactic manifests on the Usethemarketings.com website.
To add to the confusion, scam authors rely on already established company names (e.g., Google or Microsoft) and attributes in order to make the scheme more believable. These are typical social engineering tricks, and, unfortunately, many people still get fooled by them.
Push notification scams that CaptchaResolverHere.top belongs to have been around for at least half a decade when push notification API[1] was implemented on desktop-based web browsers. Initially, it was meant to be a useful feature that allows users receive information from websites they find interesting or useful. It also increases engagement with those particular websites, which brings more traffic to them.
While on the surface this might be like a great option, cybercriminals were soon to realize that it can be easily abused, and ads shown instead of useful links. This is why thousands of websites are being produced for no other reason but tricking people into pressing that “Allow” button within the notification prompt.
Crooks usually employ a simple but effective method to succeed at this scheme – they claim that it is an essential step to allegedly view the underlying content. In reality, there is no content to explore; in the best-case scenario, users are simply redirected to similar places – Itchytidying.com, Live-updates-center.com, or Fondoftravel.club – where they can get scammed again.
The best thing to do is not interact with anything such sites produce and instead work on CaptchaResolverHere.top removal. The good news is that if no links or ads from this or a similar site were clicked, you are likely to be safe. At the same time, you should not exclude the possibility of the adware infection, as we already mentioned.
Check your device for adware
Adware is usually spread via various deceptive methods, which makes people install it unintentionally. Hence, many might not even be aware that they have potentially unwanted programs running in the background. To avoid this, employ a powerful ad-blocker and never rush the installation of freeware[2] apps from third-party sources.
In order to check for adware, you should check all the installed browser extensions and remove everything you don't recognize. Keep in mind that some extensions might become malicious suddenly – this usually happens when owners of the application change.
Likewise, adware could also be installed on the system level, which expands its operational capabilities. These apps are also more dangerous and sometimes more difficult to remove. You can try accessing Control Panel or Applications on Mac to get rid of unwanted apps manually.
However, if you are having difficulties finding the PUP or can't remove it due to one reason or another, you should instead rely on a powerful security tool, e.g., SpyHunter 5Combo Cleaner or Malwarebytes. They can also check for malicious background processes and files and remove them at once for you.
After that, we strongly recommend cleaning web browsers from cookies,[3] caches, and other web data. FortectIntego can be useful for this job, and it could also fix any damage left by adware or malware, ensuring proper PC operation in the future.
Removal instructions for push notifications
In order to remove CaptchaResolverHere.top ads, you will have to enter the settings section of your web browser. Push notifications themselves are not malicious; they just might carry malicious links, depending on the website they are coming from. Thus, anti-malware software would not find and remove them for you, so you have to do it yourself.
Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

Keep in mind that you can use this guide to either allow or deny permission to show notifications for any other website.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Application Programming Interface (API). IBM. Cloud Education.
- ^ Tim Fisher. What Is Freeware?. Lifewire. Tech News, Reviews, Help & How-Tos.
- ^ HTTP cookie. Wikipedia. The free encyclopedia.
