Usethemarketings.com ads (fake) - Free Guide
Usethemarketings.com ads Removal Guide
What is Usethemarketings.com ads?
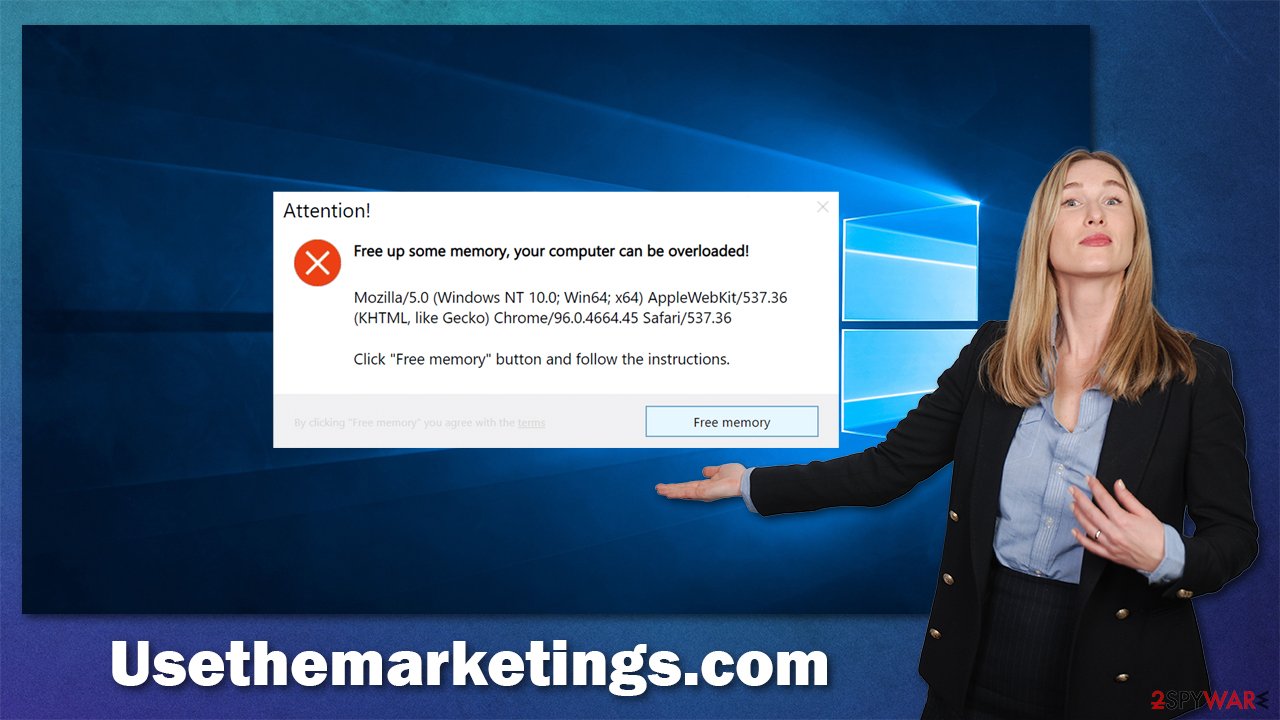
Usethemarketings.com urges users to free up some memory by offering to install potentially unwanted programs

Usethemarketings.com is a malicious scam website that one might encounter while browsing the internet on Google Chrome, Mozilla Firefox, MS Edge, or any other browser. It is one of the millions of malicious websites that aims to trick users into doing something they otherwise wouldn't; in other words, it's a scam.
The main purpose of the fraudulent website is to make people think that they are running out of memory. Upon entry, they are told that their computer can be overloaded and other them the “solution” – downloading and installing software that allegedly can do that. Usethemarketings.com might also show other types of messages that should never be trusted.
It is dangerous to download software that is offered in such a deceptive and misleading manner. Cybercriminals use similar tactics to spread malware, which might cause severe damage to your computer and your personal safety.
You might encounter scam sites after clicking on a malicious link or being redirected automatically, which is caused by adware[1] infection. These potentially unwanted applications are known to be installed inadvertently due to software bundling and other deceptive techniques.
Thus, if you are being redirected to malicious sites randomly, there is a high chance there is a malicious program or browser extension installed on your system. Below we explain how to eliminate these components manually or automatically and then remove the leftovers.
| Name | Usethemarketings.com |
|---|---|
| Type | Scam, adware, redirect |
| Operation | Claims that the memory is full and suggests to free it by offering insecure software |
| Distribution | Software bundles, malicious redirects, ads |
| Symptoms | Redirects to suspicious websites that hold plenty of commercial or scam content; fake messages offer to download malicious software; ads plague every visited website; unknown extension or program installed on the system |
| risks | Those who have malicious software installed on their systems are more likely to encounter malicious websites, resulting in financial losses, malware infections, and more |
| removal | To get rid of unwanted apps manually, you can follow our removal guide below. If the unwanted ads and other disruptive behavior does not stop, you should scan your computer with SpyHunter 5Combo Cleaner security software and delete all threats automatically |
| Further steps | Malware or adware infections can diminish the performance of your computer or cause serious stability issues. Use FortectIntego to remediate your device and ensure that the virus damage is fixed |
Scam explained: how not to trust fake alerts online
Internet is very vast, with almost two billion websites circulating on the world wide web. Some stay online for decades while others get shut down very quickly for one reason or another. In fact, Google, service providers, and other regulatory bodies shut down malicious websites daily.
Unfortunately, due to such a large number of them, it is difficult to shut them down quickly enough. And this is precisely the reason why phishing websites thrive – there are plenty of users who get tricked by them. However, it becomes much easier to recognize deception after learning a few important pointers about scams.
Let's start from the fake message you might see after you enter Usethemarketings.com:
Attention!
Free up some memory urgently, your computer is overloaded!
Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko), Chrome/96.0.4664.45, Safari/537.36
Click “Free memory” button and follow the instructions.
First of all, visually, the whole page looks like something one would see on a Windows computer – Windows-themed wallpaper and a pop-up message that strongly resembles a legitimate one. This is a typical tactic used by cybercriminals, as they want to create a sense of legitimacy, and they do that by impersonating well-established and known companies.
Microsoft and its operating system are one of the names that come up in many scams, for example:
- Pornographic virus alert from Microsoft
- Your system is infected with (3) viruses
- Your computer has been blocked
- Your Windows PC has been infected, etc.
Similar to these scams, Usethemarketings.com tries to confuse users with various numbers and names that might seem gibberish for regular computer users. In fact, this message makes no sense, as what is listed there are versions of browsers, which has nothing to do with memory, or, at least, not in this situation.
Whenever you see familiar attributes, such as Microsoft,[2] Apple, or Google logo, please pay attention to the content that is being presented to you. Legitimate companies would never frighten you with messages that something is missing or that your computer is infected and additional software needs to be downloaded to fix the situation.
Ignore these messages, as they are all fake. The main goal is to make people install potentially dangerous software on their systems while profiting from this endeavor. Instead, leave the page immediately without interacting with it and then check your system for adware, as we explain in the next section of the article.
Perform adware removal
It is important to note that the Usethemarketings.com site's appearance is just a symptom of adware – you won't find a program or a browser extension under the same name. Thus, finding and removing potentially unwanted programs or malware manually might be difficult, especially for less experienced users.
Therefore, we strongly recommend using the automatic method and performing a full system scan with SpyHunter 5Combo Cleaner or Malwarebytes. Malware, in particular, is stealthy and does not have active windows, so identifying its presence without security tools is almost impossible for regular computer users.
If you are confident with your skills, you can follow the instructions for manual removal below.
1. Check for unwanted extensions
Extensions are by far the easiest to eliminate and usually do not cause any difficulties. If you have never had to deal with this process before, proceed with the following steps:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.

MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

MS Edge (legacy)
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

2. Uninstall suspicious programs
If you have not found any suspicious extensions, you should check the apps that are installed on the system level. Applications or programs might be installed with higher permissions, which might allow them to perform harmful activities behind users' backs. Keep in mind that this step might not be successful (you might be denied the removal), or the entry of the unwanted program might simply be missing.
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

Mac
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

3. Clean or reset your browsers
Adware and other potentially unwanted programs store various components within browsers and their folders. For example, cookies help third parties with tracking activities and can prevail for years if not deleted. Likewise, cookie sessions are vulnerable to hijacking,[3] which would allow cybercriminals to access your accounts and other personal information. Thus, make sure you delete cookies, caches, and other web data – you can do this quicker with FortectIntego, although the manual method is also explained below.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

MS Edge (legacy)
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Note: you can also reset your browsers to reach the same result, although this step is usually not necessary as long as browser caches are cleaned properly.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Will Kenton. Adware. Investopedia. Financial website.
- ^ Mary Jo Schrade. Tech support scams adapt and persist in 2021, per new Microsoft research. Microsoft. Official blog.
- ^ Session hijacking attack. OWASP. Foundation for software security.
