Catchlucksurvey.top ads (scam) - Free Instructions
Catchlucksurvey.top ads Removal Guide
What is Catchlucksurvey.top ads?
Catchlucksurvey.top is a survey scam site attempting to lure you with expensive gifts
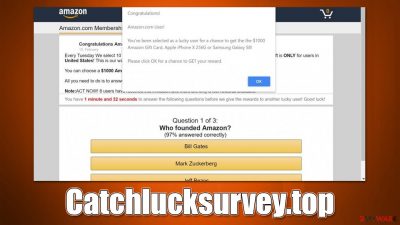
Catchlucksurvey.top is a malicious website that is used by cybercriminals to promote their fake online surveys – it uses various deceptive techniques to trick users into participating in them. Once users fill out the survey, they are promised an expensive item, and the only request to allegedly receive it is to provide personal information such as name, address, phone number, and credit card number, which is then used for various malicious purposes.
The other alarming thing about Catchlucksurvey.top is that it could be related to adware infection. Adware is a type of potentially unwanted software that spreads using bundling,[1] which often results in unintentional installation from users. Its main purpose is to show pop-ups, banners, deals, offers, in-text links, and other types of ads whenever they go, and, unfortunately, this often includes phishing content.
| Name | Catchlucksurvey.top |
| Type | Scam, phishing, adware, redirect |
| Operation | Make people provide personal information, subscribe to useless services, download malicious software or subscribe to push notifications |
| Distribution | Redirects from other malicious websites, adware |
| Dangers | Malware such as adware can cause redirects to malicious websites – financial losses, malware infections, and data disclosure can be expected |
| Removal | To remove unwanted apps manually, you can follow our removal guide below. If the unwanted ads and other disruptive behavior do not stop, you should scan your computer with SpyHunter 5Combo Cleaner security software and delete all threats automatically |
| Security tips | FortectIntego can help you when dealing with leftover adware files, for example, you can get rid of various browser trackers and fix system damage automatically |
Scam techniques used
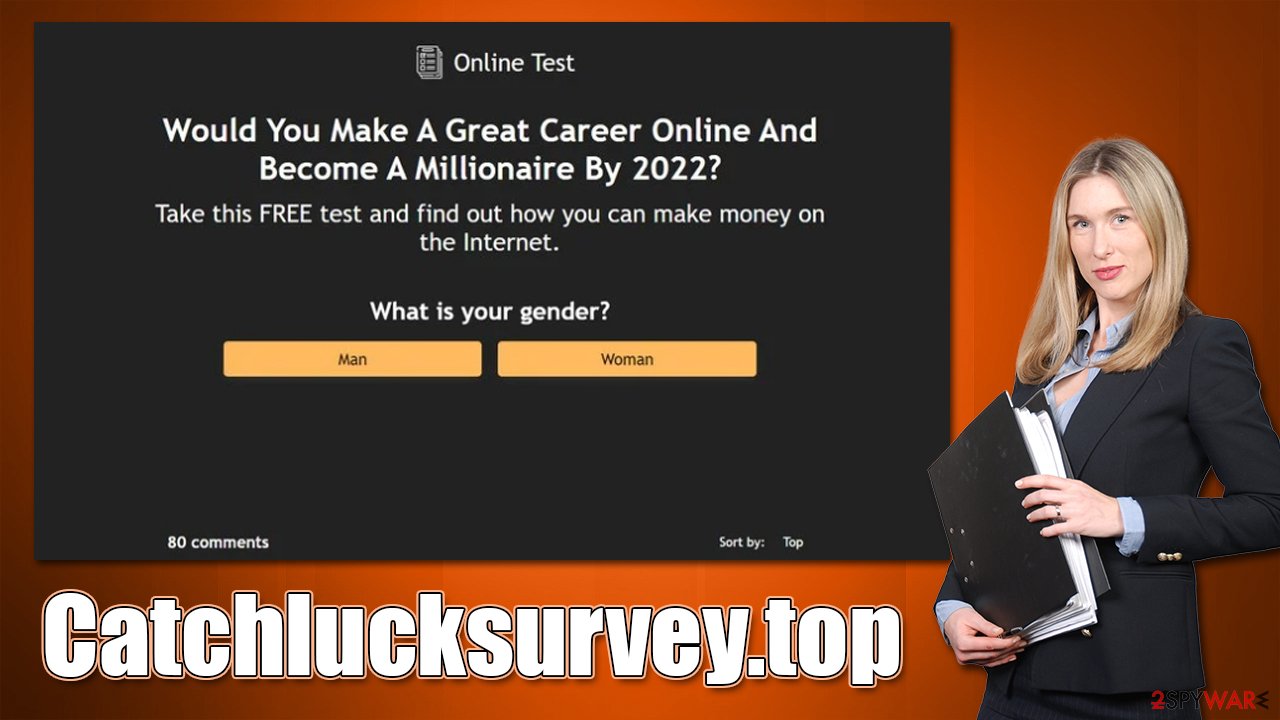
Survey and gift card scams are two types of online fraud that have become increasingly popular. Technical support scammers usually exploit people's fears by making them think their system is infected, but in this case, criminals rely on convincing users that they are extremely lucky.
Catchlucksurvey.top could promote a variety of different scams, although most of them rely on fake surveys. For example, “You've made the 9.68-billionth search” is one of the misleading messages that has been used by numerous other fake websites, including Takeluckersurvey.top, Adshome.xyz, and many others.
Scammers often employ names of reputable companies such as Google – they also use their logos, formatting, and other attributes. It is important to note that all of these elements can be easily faked, and there are other ways to figure out the authenticity of the website. The biggest giveaway is the URL itself, as it becomes clear very quickly that Catchlucksurvey.top has nothing to do with Google or another reputable company.
The survey questions that are used which is very easy to complete – it takes just a few minutes, as it is not designed to be difficult. Usually, questions like “what is your gender?” or “how often do you use Google Chrome” are asked – something casual as that. For this superficial effort, users are promised an expensive item (iPhone, PlayStation) or a gift card from a prominent company such as Amazon.
Dangers of online scams
If you are ever asked to participate in an online survey, be very careful. Make sure that you only provide personal information to websites that you trust. If you are unsure about a website, do some research to make sure it is legitimate before participating in any surveys.
If you were tricked by misleading statements and filled in the information requested, keep in mind that contact details, such as emails or phone numbers, can later be used to push other scams or sold to malicious actors on the dark web.
Thus, we recommend you be aware of the incoming phishing attempts aimed at you – you could, for example, receive a fake email that would include a malicious attachment that, once opened, would infect your computer with ransomware[2] or other dangerous malware.
The best thing to do after encountering phishing websites is to close down the tab showing them immediately, not to click any buttons, fill in any personal details and never download any software, as it could be malicious.
Removal of Catchlucksurvey.top redirects and other tips
If you have noticed that your browser is commonly redirecting you to suspicious websites, you should immediately take action and check your device for infections. Below you will find all the necessary details for that.
Uninstall unwanted programs
We recommend starting by checking your system for the installed programs. These can be found either in Control Panel on Windows or Applications section on Macs.
Windows
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till the uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
On a Mac, removing adware might require a few more steps besides moving the unwanted app into Trash. Adware is known for inserting additional files that might cause the infection to resurface, so we recommend removing them too.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Scan with anti-malware
To save time, you can perform a full system scan with SpyHunter 5Combo Cleaner or Malwarebytes, which are powerful security software. Anti-malware will detect and remove all apps that act maliciously or engage in suspicious activities. Most aggressive adware is always found as long as the potentially unwanted program detection feature is enabled within the settings menu.
Remove extensions and clean your browsers
Adware could come in the form of a browser extension, so this aspect should also be checked. After that, you should clean your browsers as well. Cookies and other web data are kept on the local computer and may be used to monitor user information, including visited websites, IP addresses, search terms, and more. Furthermore, cleaning web data might help to prevent session hijackings[3] – dangerous cyberattacks. Thus, use FortectIntego and clean your device or follow the specified instructions below.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Clean web data on Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
Clean web data on Firefox:
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Clean web data on MS Edge:
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Clean Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Bundled software. Computer Hope. Free computer help.
- ^ Ransomware. Imperva. Application and data protection.
- ^ Allie Johnson. Session hijacking: What is a session hijacking and how does it work?. Norton. Security research blog.









