Domn ransomware (Free Guide) - Decryption Methods Included
Domn virus Removal Guide
What is Domn ransomware?
Domn cryptovirus is a newly discovered version of the Stop/Djvu notorious ransomware family
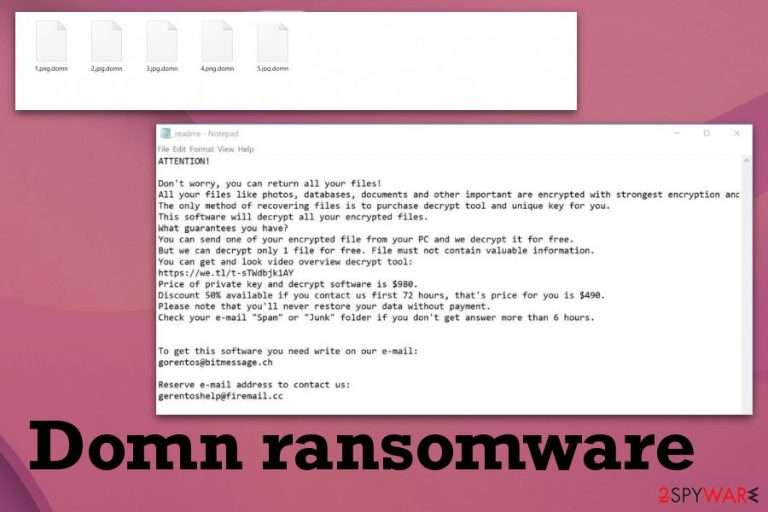
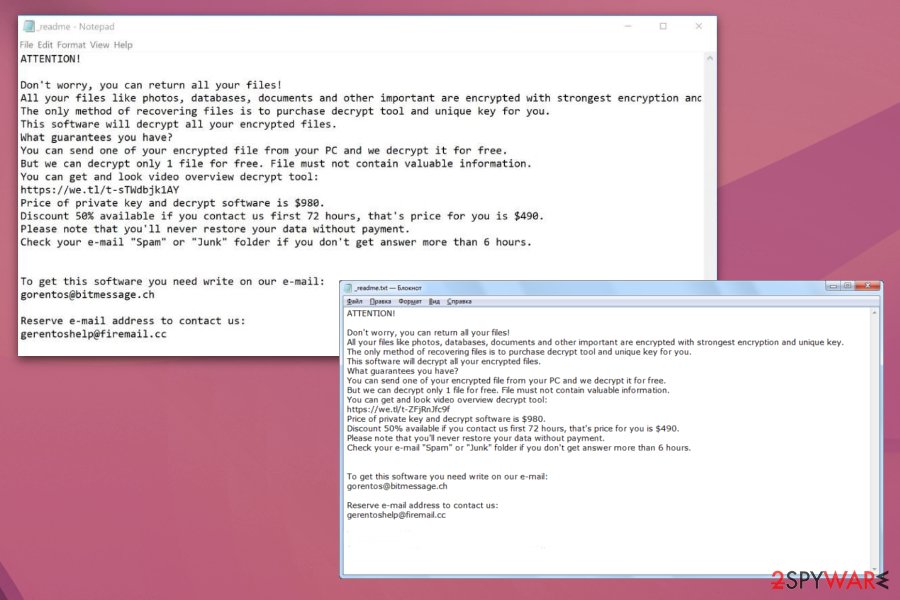
Although the ransom note is the same _readme.txt file that was used for previous versions, and contact emails remain to be gorentos@bitmessage.ch, gerentoshelp@firemail.cc, Domn ransomware virus is one of the more updated variants. Encryption process was recently altered, and the initial algorithm slightly changed, so the STOP decryption tool that was capable of decrypting encoded files is not helping victims at the moment.[1]
Domn ransomware virus has no particular symptoms besides the ransom note that gets delivered after file encryption, so the infiltration is the worst thing because it is silent and unnoticeable. The attack starts with a file-locking process and other activities that ransomware performs happen in the background. STOP ransomware family are known for leaving other threats directly on the machine or injecting the system with a particular personal data-stealing module. Such a script can obtain information stored on the machine or steal details from the browser and other programs.
| Name | Domn ransomware |
|---|---|
| Family | DJVU virus/ STOP virus |
| File marker | .domn gets added to every file stored on the machine. File encryption doesn't affect system files and data stored in those folders |
| Ransom note | The text file named _readme.txt appears on the screen automatically, and the document itself gets placed on the desktop, in various other folders containing encoded files |
| Contact emails | gorentos@bitmessage.ch, gerentoshelp@firemail.cc |
| Secondary payload | DJVU ransomware family has been known for delivering AZORult malware during the process of infiltration. This virus can affect the machine in the background and interfere with the general system cleaning |
| Distribution | Spam email attachments with infected files – a common way of ransomware distribution. STOP virus family variants are known to be included in software cracks, so when you get video games, applications, OS pay attention to DLL or EXE files loaded during the same installation process |
| Elimination | Remove Domn ransomware with anti-malware tool. There is no better way than automatic malware elimination. For virus damage elimination, perform a scan with FortectIntego |
| Possible ways for recovering data | File backups, thrid-party data restoring software, particular software offered by Dr.Web – Rescue Pack |
Domn ransomware modifies the particular host file, so the web browser cannot open antivirus provider pages, forums, or sites like ours, where you can find virus removal guides and download anti-malware tools needed for elimination of the cryptovirus. You need to reset or delete such files, so all legitimate and useful sites can be available. The path where you can find the file is C:\Windows\System32\drivers\etc\.
Things that Domn ransomware can alter include Windows registry, files, programs, even system folders. This threat can also install other programs and keep the existing ones from running properly. It affects your antivirus tools or security features significantly, so you may need help for the virus elimination because of this.
Domn ransomware may even reinstall itself and encrypt your files twice to make sure that there is no way to restore them. In most cases, the virus deletes itself after file encryption but leaves particular scripts that can run on the machine in the meantime.
Domn ransomware is the virus that causes your device to run slower and can even result is some unusual RAM or CPU usage. However, no other symptoms can indicate the infiltration of the cryptovirus. This is the unfortunate fact about the ransomware, but you should keep the anti-malware program and run an occasional scan to block such threats before the infiltration.
As for Domn ransomware removal, anti-malware tools are the best solution. Additionally, programs like FortectIntego can scan the machine fully and indicate possible threats, malicious programs, or files that affect the speed and performance of your device. Cryptovirus may get detected by a handful of different names, depending on the particular distribution vector. 
Decryption tool no longer supported: alternate methods
Criminals behind this Djvu virus changed recent malware versions and made decryption impossible. Proper asymmetrical encryption algorithms are used from now on, and offline keys are no longer used. Previously these helped victims to get their files back using STOP virus decryption tool that is no longer updated and supported. Researchers released final keys that have been extracted and starting the version with .coharos extension there is no service that Michael Gillespie can provide for victims.
Methods for Domn ransomware decryption with offline keys and online keys remain little. Experts are working on ways to get to use those offline keys. For now, all you can do is save your encoded data and wait for a newly developed decryption tool. Check the availability here. Researchers constantly update such tools and develop new ones to help victims, so you can store your affected files and clean the machine in the meantime.
As alternative virus removal and decryption method, Dr.Web researchers offer their services for victims for 150 euro. The service is called a Rescue Pack and provides personal decryption and 2-year service of security tool. This works for documents, PDF files, but cannot recover images or audio, video data. You can try to recover the test file and get back your money if the service is failing to help.
Remember that you need to remove Domn ransomware before you recovery data or attempt any other processes for system restoring. Active ransomware can affect your files or even damage them permanently of your try to add backed up files on the infected system.
Ransom note analysis
After the file-locking, this virus is designed to provide the victim with further instructions and deliver a ransom note. _readme.txt file shows up on the desktop, in various folders that contain encoded files. This message is not changed for a while and DJVU virus developers try to create the trust between them and the victim with the soft tone of the note.
The message that Domn ransomware displays remains the same as previous versions and reads the following:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:https://we.tl/t-514KtsAKtH
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
To get this software you need write on our e- mail:
gorentos@bitmessage.chReserve e-mail address to contact us:
gorentos2@firemail.cc
Our Telegram account:
@datarestoreYour personal ID:
All those guarantees are not true, and often criminals can fake the decryption be sending you a copy of a file instead of recovering the one on the machine. Even the discount is offered to make people more willing to pay up, bet when you pay the ransom they get your particular data and can even demand a bigger sum.
Cybercriminals also claim that the decryption tool they have is the only solution for your encoded files, but researches have encountered a few examples when ransomware creators don't even have software capable of recovering those files. There is no reason to trust any of those claims, especially when it comes to Domn ransomware. This DJVU family released more than 160 versions over the course of 2019, and there is no sign that developers are going to stop anytime soon.
Content from sketchy sites, craked downloads, and spam emails deliver malicious ransomware scripts
Update requests, pirated content, and cracks or software and even malicious sites deliver content filled with malware. Your machine can get easily infected if you don't pay attention to such content. Other infections like Trojans, worms, and malware can also load a secondary script of cryptovirus or even set to infiltrate the machine with ransomware.
This virus family, in particular, is known for distribution way including software cracks, malicious files loaded in packs with cheat codes, serial numbers of video games, and so on. If you choose this fraudulent way, you need to know about the risk of getting malicious program planted on the machine. Especially, when you are not sure about the source the software, serial numbers or games come from.
However, the more common ransomware spreading method includes spam email attachments and malicious macros.[2] Emails that supposedly contain financial information, order details or shipping updates have documents attached to the notification that deliver ransomware directly on the machine. Experts[3] recommend deleting suspicious emails, especially when attachments claim about some questionable order or service.
Terminate Domn ransomware virus with anti-malware tools and improve the performance of your machine
To get rid of all the damage that Domn ransomware virus caused, you need a full scan on the machine. There is no other way than the automatic elimination of the cryptovirus because this is the best way to tackle all the parts of the machine and fix parts that got affected by the threat.
The process of Domn ransomware removal includes getting a full malware check on the machine with professional anti-malware program. Such tools can find and eliminate malware, PUPs, malicious files, and fic system errors or virus damage completely.
Unfortunately, there is no official tool capable of decrypting these files, but you can save encrypted files and check the availability here from time to time, or pay for Dr.Web researchers' service. Don't forget to terminate the Domn virus first.
Getting rid of Domn virus. Follow these steps
Manual removal using Safe Mode
Remove Domn ransomware by eliminating all threats. Safe Mode with Networking may help to achieve that
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Domn using System Restore
Try System Restore feature and recover the system to a previous state when Domn ransomware was not on the machine
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Domn. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Domn from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Domn, you can use several methods to restore them:
Data Recovery Pro for your encrypted files
When you need an option for data restoring, Data recovery Pro can work and restore Domn ransomware encrypted files
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Domn ransomware;
- Restore them.
Windows Previous Versions help with files affected by Domn ransomware
If you enabled System Restore before, Windows Previous Versions can help to get them back to normal state
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer for your encrypted files
When Domn ransomware encrypts files it sometimes deletes Shadow Volume Copies too. If not, you can employ ShadowExplorer and restore data
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Decryption is not possible for Domn ransomware
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Domn and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Francesco Bussoletti. A new ransomware is on the wild: Djvu. It spreads through fake cracks. Difesaesicurezza. Defense and security news.
- ^ Macro virus. Techtarget. Search security.
- ^ Virusai. Virusai. Spyware related news.







