Easy Search Tool browser hijacker (Free Instructions)
Easy Search Tool browser hijacker Removal Guide
What is Easy Search Tool browser hijacker?
Easy Search Tool is a browser hijacker that changes your search preferences to insert ads into your searches
Easy Search Tool is a potentially unwanted application[1] that specializes in browser hijacking functions. It is typically installed inadvertently due to the deceptive distribution practices of the developers, namely software bundling[2] or misleading advertisements encountered on various insecure websites.
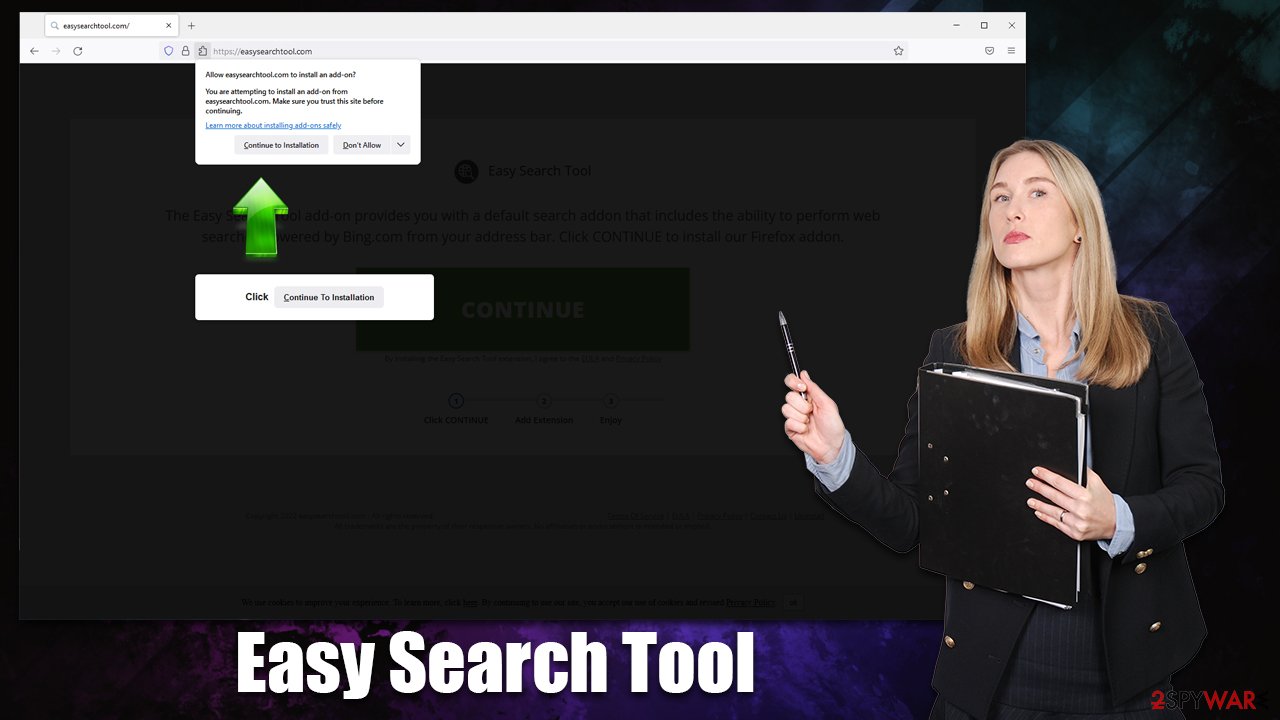
Once installed, the hijacker would immediately make changes to Googe Chrome, Mozilla Firefox, MS Edge, or another compatible web browser by swapping the default homepage/new tab to easysearchtool.com. This ensures that users are forced to use the fake search tool that produces inaccurate, ad-filled results powered by Bing, Yahoo, or another provider.
In the background, Easy Search Tool would also collect various user data and use it to target[3] users with more attractive advertisements. The information might also be shared with certain parties, which makes the practice less secure due to data transfer leak risks. If you want to take your browser back into your hands, you should remove the hijacker, as we explain in the below sections of this article.
| Name | Easy Search Tool |
|---|---|
| Type | Browser hijacker, potentially unwanted application |
| Distribution | Software bundles, third-party websites |
| Symptoms | A new extension is installed on the browser; the homepage and new tab address are set to easysearchtool.com; a customized search engine is appended to the homepage; search results may include sponsored links and ads |
| Risks | Installation of other potentially unwanted programs or even malware, privacy risks due to information gathering practices, monetary losses |
| Removal | You can get rid of browser hijackers by following the manual guide below or by scanning the computer with powerful SpyHunter 5Combo Cleaner, Malwarebytes anti-malware software |
| Other tips | After you eliminate all unwanted and malicious programs from your system, make sure you clean your web browsers and repair system files. You can do that automatically with FortectIntego or refer to our manual guide |
How common are browser hijackers?
Browser hijacking applications used to be considered a form of malware a few decades ago, as they were almost impossible to remove in regular ways and used to extensively track user data in the background without permission. Nowadays, these apps fall into the potentially unwanted software category.
That being said, browser hijackers are extremely common and have many similarities – they all change browser settings (usually swapping homepage and new tab function) and display alternative search results filled with ads. Despite the developers' promises of better or faster search, such functionality simply does not exist, and the features that are presented as benefits are actually advertisements.
Just recently we have covered MySpace Tab, QuickCouponSearch, and Moon Darker extensions, which all have similar features that are practically useless to users themselves.
How does Easy Search Tool impact your browsing
Browser redirects through or to web addresses you are not familiar with (in some cases, even to familiar ones as well) should never be ignored. If you have noticed abrupt changes when browsing or using your search box, it means that there is a potentially unwanted application installed on your system or browser.
In this case, the redirects to easysearchtool.com and through other URLs are an indication of the Easy Search Tool browser hijacker, which is likely to be installed as an extension on Google Chrome or another web browser. If this is true, you will likely see changes in your search provider as well, as they would no longer be provided by Google if it was previously set to it.
While alternative providers might be absolutely legitimate and trustworthy when used by hijackers, these search engines do not perform the same. Instead, the hijacker alters the way these tools operate and inserts its own ads at the top of the results. They might not always be accurate or even safe, which might result in various unwanted consequences for those affected.
For example, one might be at a greater risk of installing other potentially unwanted applications or subscribing to useless services, as the top results might insert insecure links. Since most users don't pay close attention to the ad markings – they tend to just click the top result – it may fully alter which websites they visit and which items they purchase. In other words, the hijacker regulates results artificially, which can greatly impact the way users browse the web.
Removal instructions
First of all, we recommend performing a full system scan with SpyHunter 5Combo Cleaner, Malwarebytes, or another powerful anti-malware software. Because PUPs are commonly spread via deceptive methods, there might be additional dangerous apps installed on your system without your knowledge. Also, this step is very important if you visit high-risk websites such as torrents or illegal video streaming sites, regularly.
Your next step is to remove Easy Search Tool – a browser extension responsible for the unwanted changes to the homepage and other settings. This can easily be done by clicking the “Extensions” button next to the Settings menu of the browser, although it might not always be possible. Alternatively, proceed with the following steps:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
In order to stop the unwanted data tracking, you should also remove cookies and other web data after PUP elimination. To make it easier, you can employ the FortectIntego PC repair tool, capable of finding leftover files and eliminating them automatically. Alternatively, you can proceed with the following:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
How to prevent from getting browser hijacker
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Chris Hoffman. PUPs Explained: What is a “Potentially Unwanted Program”?. How-to Geek. Site that explains technology.
- ^ Bundled software. Computer Hope. Free computer help.
- ^ Targeted advertising. Wikipedia. The free encyclopedia.








