Eztv.io ads (Virus Removal Guide) - Free Instructions
Eztv.io ads Removal Guide
What is Eztv.io ads?
Eztv.io is a torrent website that might result in malware infection
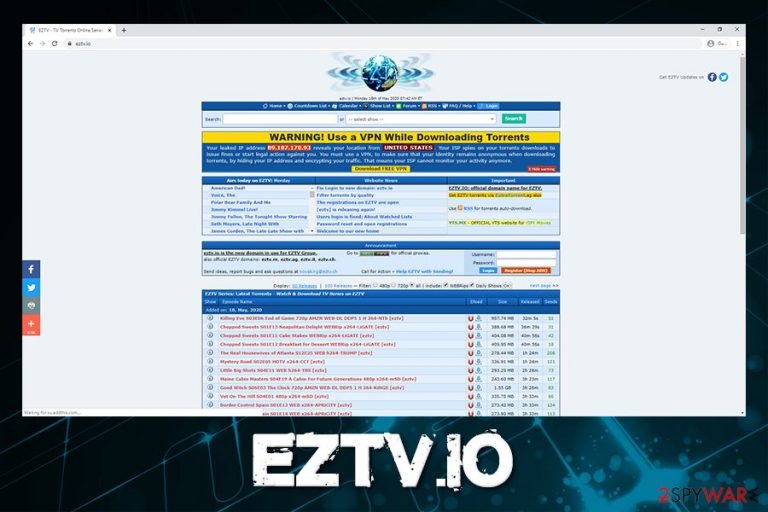
Eztv.io is a website that offers users to download TV shows, music, applications, and other files for free via the peer-to-peer network. While some users might access the site on purpose when looking for free download service, some might get redirected from another place on the internet, making the visit unexpected. Even though torrenting itself is not illegal, much of the content hosted on such sites typically are, so users should instead head to official websites to view the newest TV shows they like so much.
Besides hosting illegal content, Eztv.io ads are something that users will become accustomed to as soon as they access the site. As it is typical to torrent sites, advertising networks that are used are not secure at all. While some might direct users to legitimate sites, some ads might be boobytrapped with malware, which can be triggered by a background script once clicked on (in some cases, even a click is not necessary).
Finally, files downloaded from the Eztv.io might be malicious and include such infections like ransomware, Trojans, cryptoviruses, and much more. Find out how to protect your computer from dangers that lie within the shady peer-to-peer scheme.
| Name | Eztv.io ads |
| Type | Torrent site, peer-to-peer service |
| Infiltration | Ads might be embedded directly on the site, although desktop ads are caused by notification prompt that can be encountered on the website. Also, potentially unwanted programs and malicious apps might be downloaded directly via the peer-to-peer client |
| Risks |
|
| Elimination | To eliminate notifications on the desktop, you should access web browser settings and eliminate the site from the “Allowed” list. To delete malicious applications, you should scan the machine with reputable anti-malware software. We advise not to engage with any Eztv.io ads due to the risk of malware infection |
| System fix | If you found malware on your system, it might not work the same way as prior to the infection, even after it is terminated. If you see lag, crashes, and your machine suffers from other stability issues, scan it with repair program FortectIntego |
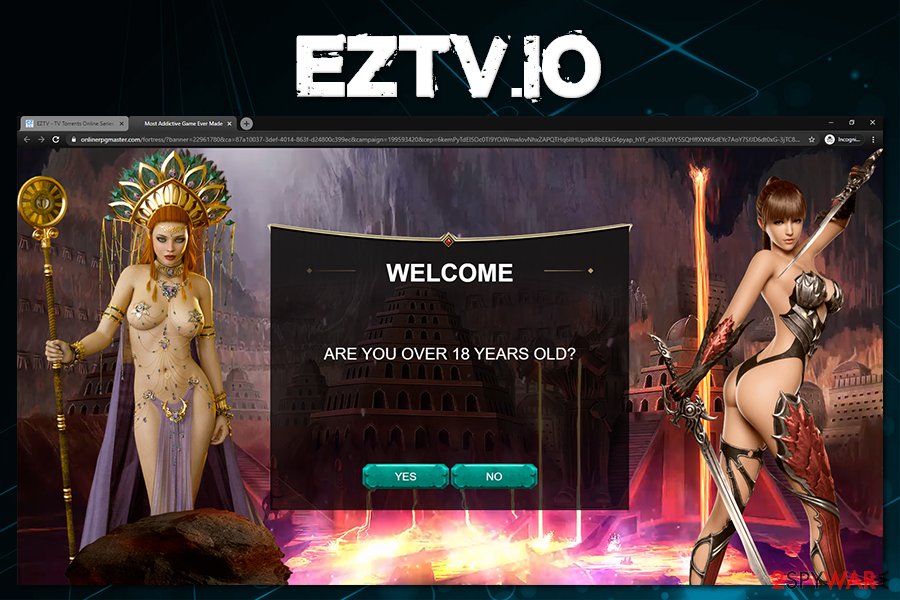
While most of the Eztv.io ads come from the website itself, some users might see a notification prompt that asks them to allow notifications to be shown. This is a very commonly used tactic that allows threat actors to display advertisements directly on users' desktops instead of the browsers. Since, in many cases, users allow notifications by accident, they do not know how to remove Eztv.io ads.
Without a doubt, such Eztv.io notifications should not be clicked, as the site may serve links to malware-laden, scam, and similar websites. Once there, users might be tricked into providing personal information, exposing credit card numbers or social security numbers. In other cases, users might be tricked into subscribing to a service that is useless, and then they will be charged every month until the service is canceled manually.
The problem is that many users do not check their online banking accounts, and it typically takes some time before they realize that the funds are leaving their accounts on a regular basis. Besides, Eztv.io ads are not the only place where users can encounter scam sites, so regularly checking online banking and not registering for any shady services is advisable.
The embedded Eztv.io ads might not be secure not because of the owners, but rather suspicious advertising networks that they employ. Poor quality ads are often shown on torrent sites, and cybercriminals are also often happy to buy the ad space. As a result, those who visit the site might get infected with malware automatically if no ad-block is used. Nonetheless, automatic malware installation is only possible if you have vulnerable software[1] on your device. This is why patching is so important.

Eztv.io ads are not the only issue that users can encounter, as the biggest danger lies within the site downloads. In many cases, malicious files can be disguised as useful ones, and users will be unaware that they are allowing malicious payloads into their machines. Here are a few examples:
- software cracks are often used to proliferate malware,[2] and these tools can often be found on sites like Eztv.io;
- the fake codecs, language packs and other files included with a video torrent might be malicious;
- downloaded files might be disguised as legitimate ones. For example, a file named “TV show S5E2.mkv.exe” is most certainly malicious, as it is an executable – something that a video should never be.
All in all, the installed Eztv.io malware in one way or another might be anything – from annoying ad-spamming bots to full-blown ransomware. The later is extremely dangerous as it can steal sensitive files found from the system, encrypt the rest, and then the attackers might publish the data on the dark web for everybody to see/take.
If you were unlucky and managed to get infected, you should perform Eztv.io virus removal as soon as possible. To do that, we recommend employing a powerful anti-malware tool, such as SpyHunter 5Combo Cleaner or Malwarebytes. In case malware is interfering with security software, you should access Safe Mode with Networking and performing the scan from there – we provide the instructions below. Also, if your computer struggles to work as before after the infection, we recommend employing a PC repair tool FortectIntego.
Avoid peer-to-peer sites
The overall security rating of torrent sites is relatively low, despite its visitor count. Since the service is not considered to be legal mostly, (multiple popular torrent sites were shut down previously due to copyright infringement), the website authors do not want to miss an opportunity to monetize as much as possible. Shady ad networks pay much money, hence the ads displayed on the site are not always of best of quality, and often even malicious. Besides, downloading files from torrent sites can directly result in malware infection.
Therefore, the best way to go around this is not to use torrent sites altogether – there are so many ways to get infected, and the service is often considered to be illegal. Nonetheless, if you still insist of using peer-to-peer network, take these precautionary steps in order to avoid malware infection and personal data compromise:
- Install comprehensive security software and keep it up to date;
- Backup your files regularly on an external drive or a virtual storage;
- Employ ad-block to prevent malicious scripts from being executed;
- Disable Adobe Flash and Java function and turn them to “click-to-run” setting;
- Never download software cracks/keygens/loaders – these executables are often embedded with malicious code (Djvu ransomware uses cracks as its primary distribution method, and infects hundreds of users daily);
- Watch out for copycat sites that look identical to the original site – these are often malicious or ask money for usage;
- before downloading a torrent file, read the comment section (users often hint that it is malware and that others should avoid it at all times);
- Before opening executable, scan it with anti-malware or tools like Virus Total.
Get rid of Eztv.io virus to protect your personal data
Malware that can be associated with the Eztv.io virus varies, meaning that users might get infected with ransomware, remote access trojans,[3] info-stealers, backdoors, rootkits, and other parasites. Each of these types is designed to perform different functions; for example, backdoors are often used to inclusion of the machine into a botnet and proliferating other malware. In the meantime, keyloggers are there to capture keyboard and mouse inputs and sending it off directly to the attackers.
Therefore, Eztv.io removal will depend on which type of malware your machine got infected with. Nonetheless, even if you did download and used a crack or other high-risk file, it does not mean that you are infected with malware, either. The best way to find out is to perform a full system scan with a powerful security application – we recommend using SpyHunter 5Combo Cleaner or Malwarebytes, although other reputable tools can also be used.
Then, in case Eztv.io was related to data-stealing, you should change passwords of your accounts and monitor your online banking closely.
Finally, if you want to remove Eztv.io ads from your desktop, follow these steps:
Google Chrome
- Select Menu > Settings
- Go to Advanced
- Under Privacy and security, pick Site Settings > Notifications
- Under Allow section, find Eztv.io
- Click More Actions and then choose Block
Mozilla Firefox
- Go to Menu > Options
- Click on Privacy & Security > Notifications
- Choose Settings – you should see Eztv.io entry
- Click on the the drop-down menu and select Block
- Save Changes
MS Edge
- Click on thee horizontal dots and select Settings
- Go to Site permissions > Notifications
- Click on More actions next to Notifications and select Block
Getting rid of Eztv.io ads. Follow these steps
Manual removal using Safe Mode
In case malware is tampering with your security program, access Sade Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Eztv.io and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting viruses
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Thomas Holt. What Are Software Vulnerabilities, and Why Are There So Many of Them?. Scientific American. Science News, Articles, and Information.
- ^ Software Cracks: A Great Way to Infect Your PC. KrebsonSecurity. Computer security and cybercrime news.
- ^ Malware spotlight: What is a Remote Access Trojan (RAT)?. Infosec. Security website.
