Findhealthinfonow.com browser hijacker (Tutorial) - Chrome, Firefox, IE, Edge
Findhealthinfonow.com browser hijacker Removal Guide
What is Findhealthinfonow.com browser hijacker?
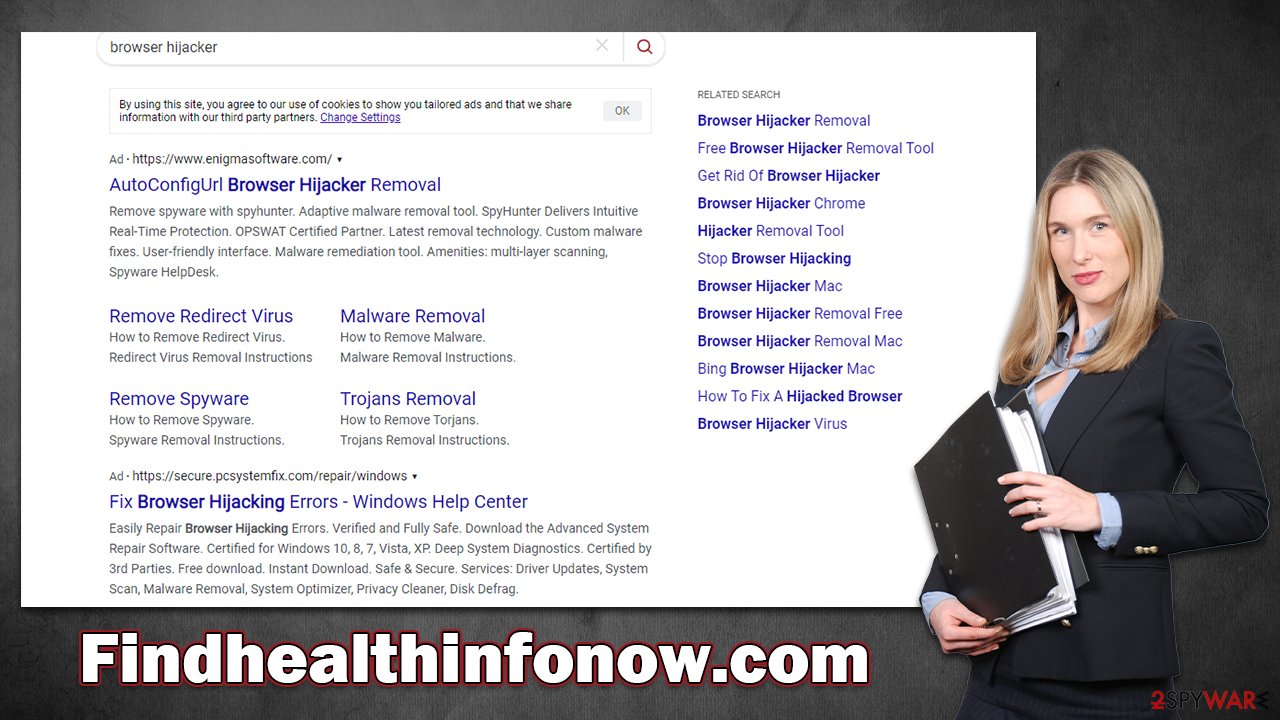
Findhealthinfonow.com can hijack your browsers and take over your search results

Findhealthinfonow.com is an URL you might notice taking over your Google Chrome, Mozilla Firefox, MS Edge, or another web browser. If that's the case, you have a potentially unwanted application installed on the system, which is likely to come in the form of an extension. These apps are not particularly dangerous, but it is incorrect to assume that they are beneficial. Furthermore, these programs have a lot of suspicious and deceptive characteristics, so they should be removed as soon as possible.
Findhealthinfonow.com would not only place itself on the front page but would also alter the search provider and the results it brings. Instead of showing genuine links that reflect the search query, users would be exposed to all types of ads and clicks that benefit the hijacker authors. This could hinder people from finding what they are looking for and may also lead them to websites that advertise questionable content.
| Name | Findhealthinfonow.com |
| Type | Browser hijacker, potentially unwanted program |
| Distribution | Bundled software, third-party websites, fake updates or ads |
| Symptoms | A browser extension or an application installed on the device; homepage and new tab address set to findhealthinfonow.com; ads and sponsored links in search results and elsewhere; promotion of other PUPs |
| Risks | Data tracking from various third parties, exposure to malicious ads, redirects to phishing sites |
| Removal | You can eliminate the unwanted program manually, although you should scan your system with security software to ensure it's not infected with other threats |
| Other tips | After removing all potentially unwanted applications, we recommend you employ the FortectIntego utility to clean your web browsers and repair any damaged system files |
The fake features
Browser hijackers fall into a category of potentially unwanted programs, and the naming is for a reason. First of all, most people install these apps inadvertently along with freeware[1] or other software from the internet. It is more likely to happen on less secure websites, so downloading software from trusted sites is advisable. Deceptive advertisements such as fake Flash Player updates or misleading statements can also be used by PUP authors for their distribution.
People may also install a hijacker without realizing it is one. For example, Findhealthinfonow.com uses a similarly-named homepage title if “Find Health Info Now,” which may imply that it could help users find information about anything health-related. However, this couldn't be further from the truth.
The hijacker is pretending to be useful only to stay on users' machines for as long as possible to generate ad revenue. Besides the basic search function, which brings inaccurate search results filled with ads, there is no link to anything related to health: it does not provide any links or special search settings, for that matter.
There are plenty of other browser hijackers that act in exact same manner, although the theme may vary. For example, CoolADSBlockSearch may imply that it can block ads or that UltraCouponSearch would direct users to the best deals on the internet – all of this is misleading, to say the least.
Removal of Findhealthinfonow.com hijack
It might sometimes be difficult to determine which application is causing your browser settings to change, especially if you have quite a few of them installed on your device. While most hijackers can be easily removed manually, sometimes these changes might indicate that a symptom has been affected by a much more serious threat.
Therefore, we recommend you scan your system with SpyHunter 5Combo Cleaner/Malwarebytes anti-malware software, which could easily check whether it is true or not. Some malicious programs can root[2] themselves into the system and may be impossible to remove manually for a regular computer user, hence anti-malware tools are perfect solutions here.
When speaking of Findhealthinfonow.com removal, it is likely to be installed on the browser as an extension, so you should start by accessing browser settings and getting rid of the app under the name of “Find Health Info Now.” Note that this may not always be the case and that the application causing browser changes could be named something entirely different.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.

MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

If you have not found the reason why your browser has been hijacked within the Extensions section, you should try checking the applications installed on the system level. Note that security software would most certainly find and remove malicious apps installed this way, so you can skip this step if you have already performed a full system scan.
Windows
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

Mac
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Finally, removing browser caches, cookies,[3] and other web data should be the final action in the removal of an undesirable program. These items are utilized to gather information about your surfing habits and can remain on the browser if not deleted, allowing for further data gathering.
Thus, you should remove these leftover files from your system after you are done with Findhealthinfonow.com and other unwanted application removals. To do this quickly, rely on FortectIntego or refer to the manual steps below:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

How to prevent from getting browser hijacker
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ What Is Freeware?. Lifewire. Tech News, Reviews, Help & How-Tos.
- ^ Rootkit. Wikipedia. The free encyclopedia.
- ^ Cookies and Web Beacons. NTT. NTT Communications.
