IdentityStack mac virus (Free Guide)
IdentityStack mac virus Removal Guide
What is IdentityStack mac virus?
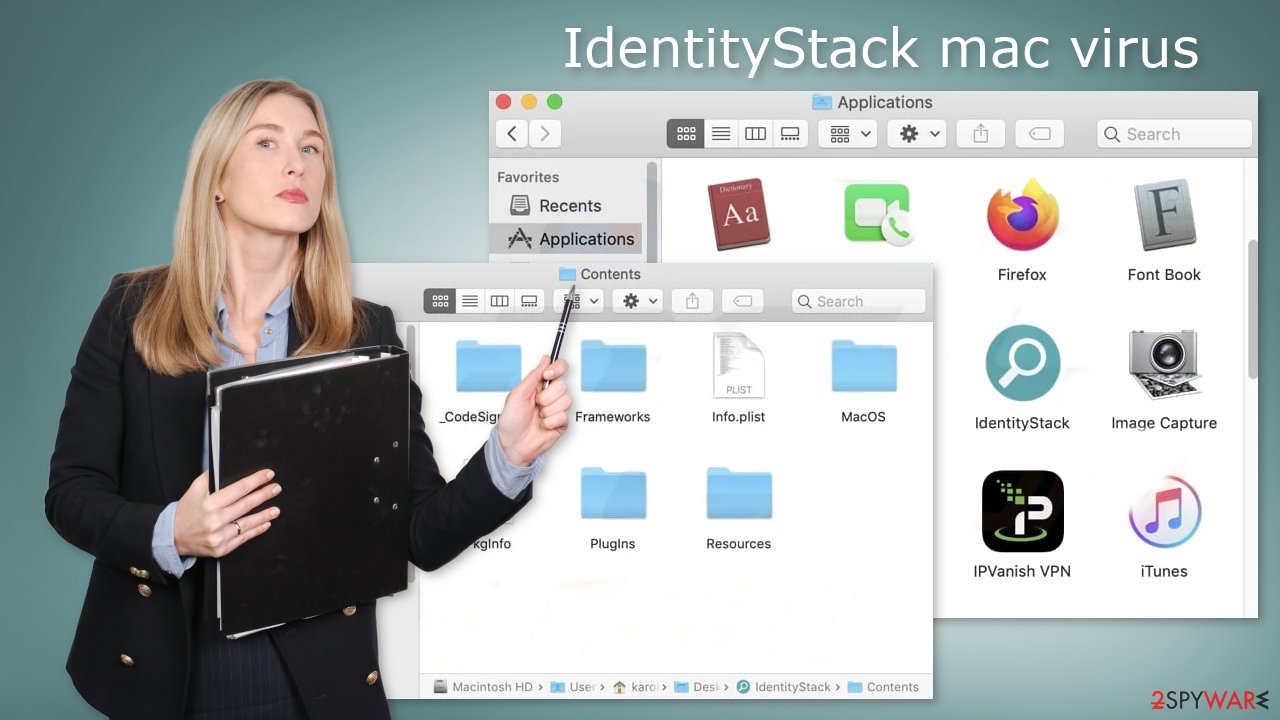
IdentityStack is an aggressive form of adware that specifically targets Mac computers

IdentityStack is a virus that specifically attacks Apple computers. It belongs to the Adload malware family and is capable of causing increased commercial content, like pop-ups, banners, and redirects. It may also change your main browser settings without you realizing it, such as your homepage, new tab address, etc.
If people are only allowed to use selected channels for browsing, it raises a lot of user privacy and security concerns. For example, crooks might place ads from rogue advertising networks[1] that lead to dangerous websites. Also, people could end up on scam pages that try to get personal information or trick them into installing PUPs (potentially unwanted programs)[2] and malware.
| NAME | IdentityStack |
| TYPE | Adware, browser hijacker, mac virus |
| MALWARE FAMILY | Adload |
| SYMPTOMS | Different homepage and new tab addresses; redirects to some other search engine and shady websites; machine performs worse than before; unknown apps appear on the machine |
| DISTRIBUTION | Fake software updates, deceptive ads, installing programs from peer-to-peer file-sharing platforms |
| DANGERS | Altered search results can lead to dangerous websites; pop-up ads might be promoting scams; the virus can install other PUPs or even malware in the background |
| ELIMINATION | Eliminating this Mac virus manually can be quite complicated. The easiest and most effective way would be to open a professional security tool and scan your system to delete every related file |
| FURTHER STEPS | FortectIntego should be used to completely wipe out any data left and fix the remaining damage |
IdentityStack in detail
Adware[3] specifically targeting macOS devices is more aggressive than its Windows counterpart, often running scripts or installing other PUPs and malware in the background without users' knowledge. Changes caused by adware may go unnoticed until it's too late – the software can bypass Apple's XProtect security system designed to protect against such threats.
We have written about several other Adload variants, such as EssentialModule, ConnectedField, and InitialConnection. You may have noticed that they share a similar appearance – a magnifier placed on top of a green, teal, or grey background. The main file for this virus can be found in the “Applications” folder.
Adload employs multiple strategies to make detection and removal difficult. For example, it creates numerous other files that appear as regular system files but are actually hidden in different folders throughout the machine. Therefore, avoid getting infected with Adload if possible.
Distribution techniques
Most of the time, fraudsters succeed in infecting people's devices by having them download “cracked” software from Torrent websites or peer-to-peer file-sharing platforms. Unfortunately, it is very difficult to know if these packages are safe and do not contain any malicious content.
It might be spendy, but utilizing official web stores is worth the cost. The apps that appear on these types of sites have undergone an intense review process. Also, since there are tons of free app options available, you're bound to find something that suits your needs perfectly.
Although Adobe Flash Player was discontinued in 2020 and replaced by HTML5, cybercriminals are still creating fake websites to trick people into downloading malware. Many individuals are unaware that Flash Player is no longer supported, so when they see a website telling them they need it to update their player, they comply without question.
It's critical that you regularly update your software and operating system. By doing so, you can prevent hackers from exploiting vulnerabilities to deliver malicious programs. In addition, software developers often release security patches that will help further protect your system.
Adload removal instructions
You should not do this yourself unless you know what you are doing and what kind of files you need to delete. Some of the files can have a .plist extension which is a normal settings file, also known as a “properties file,” used by macOS applications. It contains properties and configuration settings for various programs. The app also uses various persistence techniques and drops many files across the system, making browser extension and application removal difficult.
To keep your mind at peace, we recommend using professional anti-malware tools SpyHunter 5Combo Cleaner or Malwarebytes, which can detect unwanted programs and eradicate them. You also do not know if the virus installed any additional malicious programs, so this is the safest way to ensure the system is clean.
If you still want to try and delete it manually, proceed with these steps:
- Open Applications folder
- Select Utilities
- Double-click Activity Monitor
- Here, look for suspicious processes related to adware and use Force Quit command to shut them down
- Go back to the Applications folder
- Find IdentityStack in the list and move it to Trash.
If you are unable to shut down the related processes or can't move the app to Trash, you should look for malicious profiles and login items:
- Go to Preferences and select Accounts
- Click Login items and delete everything suspicious
- Next, pick System Preferences > Users & Groups
- Find Profiles and remove unwanted profiles from the list.
There are likely to be more .plist files hiding in the following locations – delete them all:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
The manual elimination process might not always result in full virus removal. Therefore, we still strongly suggest you perform a scan with security software.
Remove the malicious extension
An extension to your browser is also added by IdentityStack adware which starts performing all sorts of unwanted tasks. It possibly collects sensitive data and sends it to tracking servers. Some of the data that could be exposed is – IP address, user name, macOS version, browser versions, computer ID, items in the “Applications” folder, a list of agents, daemons, and system configuration profiles.
You should eliminate the add-on as soon as possible after the dangerous files are eliminated from your system. You can delete cookies and cache automatically with the help of FortectIntego. It will also fix any damaged files and system errors, so you should notice an improvement in the machine's performance.
If you prefer doing this yourself without additional help, here are the instructions. You will find guides for Google Chrome and Mozilla Firefox at the bottom of this article:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Cookies and website data:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
The simplest and quickest solution to this is completely resetting Safari:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.
![Reset Safari Reset Safari]()
Getting rid of IdentityStack mac virus. Follow these steps
Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Zeljka Zorz. How does a rogue ad network function?. Helpnetsecurity. IT Insights.
- ^ Chris Hoffman. PUPs Explained: What is a “Potentially Unwanted Program”?. Howtogeek. Technology Magazine.
- ^ Adware. Malwarebytes. Cybersecurity Basics.











