Iforgot.apple.com (Virus Removal Guide) - Free Instructions
iforgot.apple.com Removal Guide
What is iforgot.apple.com?
iforgot.apple.com is a legitimate Apple domain, although it can also be used in spoofing attacks

iforgot.apple.com is a domain name used by Apple to provide account recovery options. However, its name is also often used within a spoofing site[1] by cybercriminals to scam macOS/Mac OS X users into providing their sensitive information. In most cases, users get the scam email directly into their Inboxes, and it doesn't matter which email provider is used – Gmail, Yahoo, Outlook, or other.
The scam consists of a carefully engineered plot: the email is seemingly sent by the tech giant Apple, and claims are made that somebody tried to enter the victim's account. Allegedly, the entry to the account has been disabled “for security reasons,” and the only way to regain the control of it is to enter the iforgot.apple.com link and provide the required AppleID information.
Those who provide the required details will risk the disclosure of their personal details to malicious parties, as crooks will be able to gain access to personal files, make purchases on the AppStore and steal details from personal messages, leading to further data compromise. If received, you should immediately remove iforgot.apple.com email from your inbox, change login details, and scan your machine for malware.
| Name | iforgot.apple.com |
| Also known as | Your Apple ID was used to sign in to a new web browser |
| Type | Scam, spoofing site |
| Distribution | Spam emails |
| Targets | Mac users |
| Risks | Money loss, sensitive data disclosure to cybercriminals, malware infections, etc. |
| Termination | If you entered your credentials to the spoofing site, hackers might have gained control of your machine and planted a keylogger or another nasty malware. Make sure you scan your computer with security software |
| System tweak | Use FortectIntego to delete junk and other useless files to increase computer performance |
The nature of the iforgot.apple.com fake email is extremely deceptive, as many companies engage in the practice of warning people about the attempts to log in from a different IP by email – it is a common practice, and security feature can alert users to change their passwords, secure the account by applying two-factor authentication, etc.
However, cybercriminals often abuse the feature in a scam scheme and claim that the account will be disabled if the credentials are not entered into a site link provided (it can come from various emails, one of the users said that the scam was sent from noreplyappidreport01@smtpuserid.com):
Dear Customer,
Your Apple ID has been temporarily disabled for security reason.
When you see this alerts, you can go to iforgot.apple.com to unlock your account with your existing password.
Your account will permanently disabled if you do not verify your account under 24 hours.Sincerely,
Support
Aapple ID | Support | Privacy Policy
Here are the signs and symptoms[2] or the iforgot.apple.com scam being fake:
- Pay attention to the way you are addressed – “Dear Customer.” Apple knows your name, and it would use it instead of a generic one
- Grammar and spelling errors
- A threat – claim that your account will be disabled. Apple you not threaten you with disabling your account for whatever reason.
Note that iforgot.apple.com is a real domain used by Apple to recover the lost AppleID. However, the text of the link is not the same domain you will be redirected to, as it works as a hyperlink so that anything can be highlighted as a link name.
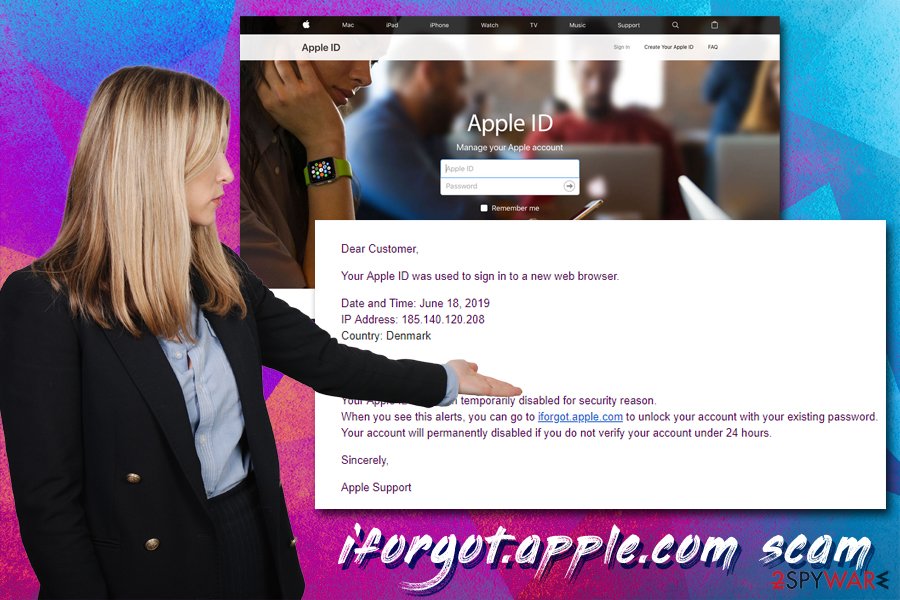
In most cases, users will be redirected to a fake website that has nothing to do with Apple (appleid.account-support.reacomescan.com) but looks strangely familiar due to its copied design. Thus, no matter what, never enter your credentials into this spoofed site, as ramifications might be disastrous – your AppleID could be hijacked, purchases made in your name, or even identity stolen.
Nevertheless, if you did enter your credentials, you need to take action immediately: change your login details on your AppleID (if unable, contact customer support), scan your device for malware with SpyHunter 5Combo Cleaner, Malwarebytes, or another security software, and contact your bank if any money was illegally taken from your account. Additionally, before iforgot.apple.com removal from your inbox, you should forward it to your local authorities that deal with scam cases.
In case your Mac is suffering from slow speeds, crashes, overheating, or other issues, it might not necessarily be related to malware infection. If you are experiencing performance issues, use FortectIntego to delete useless files from your system, increasing its stability and speed in the process.
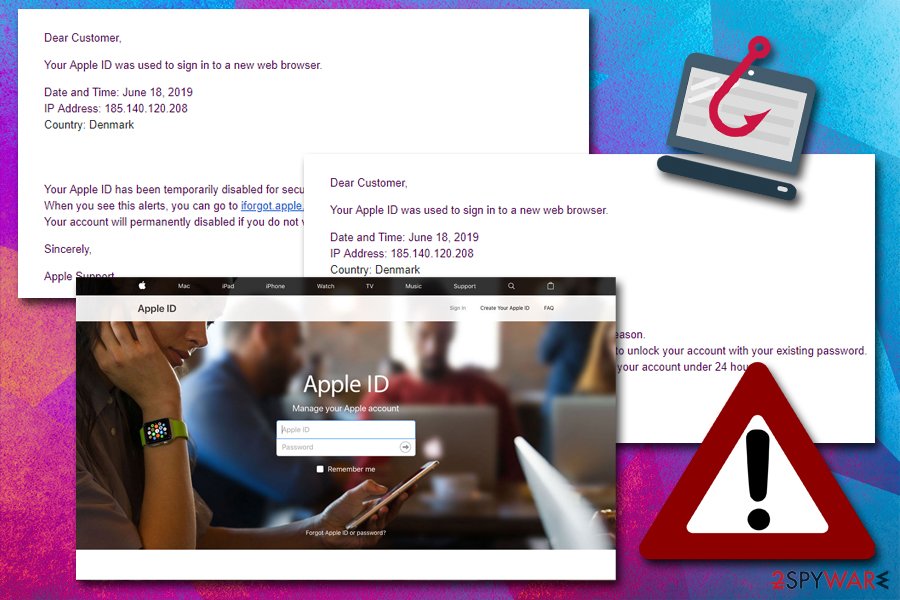
Scammers use phishing emails to steal your information or infect your device with malware
Spam email is among the most favorite malware and scam distribution methods around. For example, multiple ransomware and Trojan families employ obfuscated spam email attachments to initiate the infection.[3] Additionally, emails that lead to fake Amazon, Netflix, and other spoofed sites the harvest the login credentials thrive.
First of all, you should always check if the email is marked as spam – if it is the case, treat it with high caution, as it is most likely fake. Nevertheless, cybercriminals sometimes manage to bypass the built-in scanner, and some of these malicious emails manage to enter your Inbox. Therefore, always look for signs of deception, such as grammar mistakes, the “From” address, the content of the message (ask yourself whether the situation applies to you), etc.
Nevertheless, while many hyperlinks can lead you to a spoofed site, be aware that email addresses can be spoofed as well, and look identical to that of the original source, despite being something completely different. This technique is also widely used by hackers, as it makes the phishing attempt much more believable.
If you entered the fake iforgot.apple.com site and enter your credentials, immediately check your Mac for malware
Essentially, it does not matter if you remove iforgot.apple.com from your Inbox or not, as long as you do not interact with the provided hyperlink and/or enter your AppleID credentials. Nevertheless, if you received such a scam email, you should report it to your local authorities and change your passwords for both, the email and AppleID as a precautionary measure.
Nevertheless, if you did interact with the fake email and entered your credentials, malicious actors could access various services under your name, such as App Store, iCloud, iTunes, FaceTime, Apple Online Store, Find My iPhone and much more. Therefore, you should also scan your computer for malware as soon as possible to take care of iforgot.apple.com virus removal.
How to prevent from getting spam tools
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Website spoofing. Wikipedia. The free encyclopedia.
- ^ Luke Irwin. 5 ways to detect a phishing email – with examples. ITgovernance. Governance, Risk Management and Compliance.
- ^ Danny Palmer. Hackers use phoney invoice email to trick you into downloading malware. ZDNet. Technology News, Analysis, Comments and Product Reviews.
