IProtectYou (Improved Instructions) - updated Jul 2018
iProtectYou Removal Guide
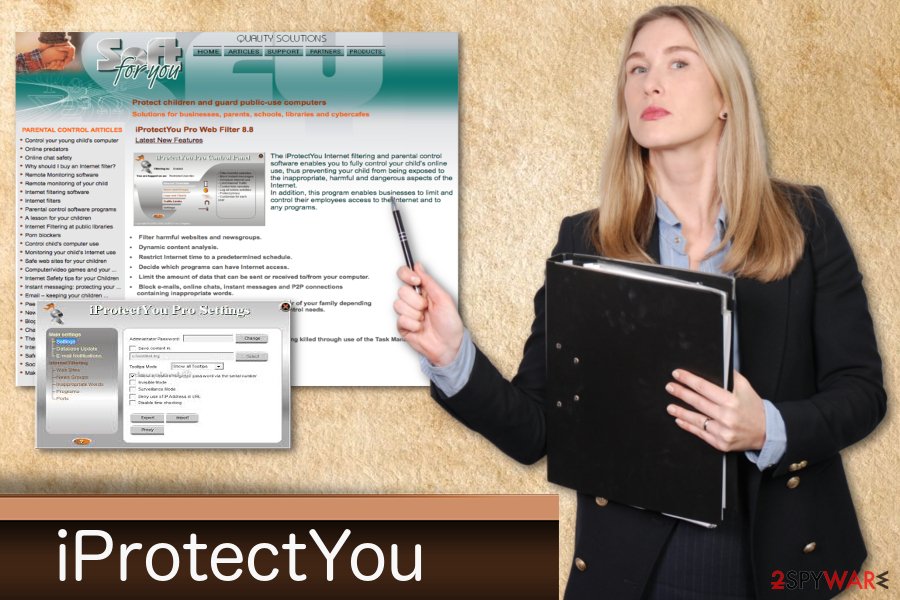
What is iProtectYou?
iProtectYou is a malicious program capable of spying on users
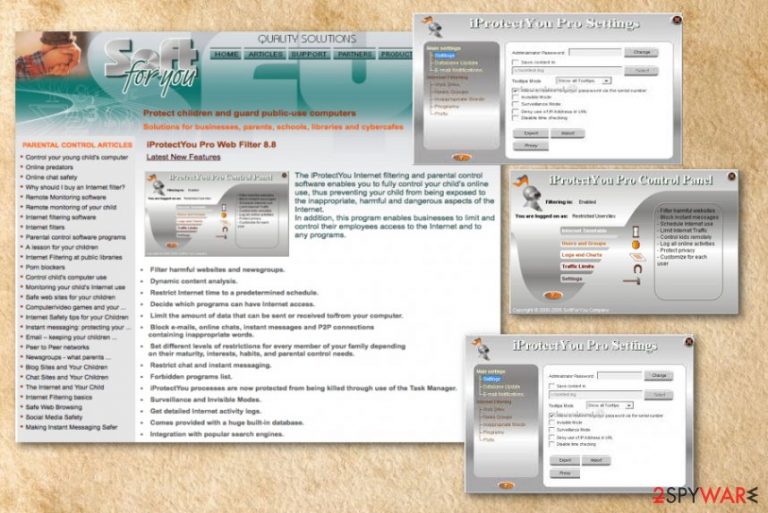
iProtectYou is a program that was initially created for the filtering and parental control service. Nevertheless, cybercrooks managed to utilize this application for spying on users by logging keystrokes, filtering web content and monitoring their internet and program use. The application tracks user activity monitors Internet using habits, filters web content and logs all user keystrokes. It sends gathered data to a predefined e-mail address. The threat automatically runs on every Windows startup.
| Name | iProtectYou |
|---|---|
| Type | System tools |
| Symptoms | Display fake system error messages, slows down the PC, displays intrusive ads |
| Danger | Can attract malware |
| Distribution | Insecure downloads, infected email attachments |
| Elimination | Use FortectIntego for iProtectYou removal |
The application was developed by SoftForYou for all versions of the Windows operating system. Authors of this software have an official website, where iProtectYou and other programs can be downloaded. However, the app typically spreads via software bundling and in other dubious ways. That is why security researchers call it a PUP – potentially unwanted program.[1]
iProtectYou virus creates fake messages of fake malware infections that look legitimate. Fake error messages about issues with the OS force users to restart the computer. iProtectYou can also install other unwanted programs which can slow down the PC.
You should remove iProtectYou from your PC if you want to get rid the intrusive advertisements and pop-up windows. Also, this program can collect information about the user, like IP addresses, location, browsing history, search queries, etc. This data is later shared with third-parties and used for marketing purposes.
iProtectYou removal is important because the app can be potentially dangerous, especially if it is controlled by cybercriminals. Also, the program can access Windows Registry and modify it. You should use the anti-malware tools like FortectIntego for iProtectYou virus elimination.
Downloads from questionable websites can lead to infections
The most common way of spreading PUPs is insecure websites and downloading freeware[2] or updates. That is why it is important to set all your software updates to automatic setting – you can then be sure that the update is legitimate.
Software bundling is a standard marketing technique that is used by many worldwide. Nevertheless, it is not entirely fair, as the crucial bits of information are often hidden in small text or Advanced/Custom settings. Note that developers of software will always prompt you to use Recommended/Quick mode. This is done on purpose so that that critical installation steps would be skipped.
Therefore, do not get trick by this questionable distribution technique. Make sure you download software from reputable sites only. Even then, look out for optional components within the installation managers: select Advanced/Custom settings and eliminate all the tick marks by add-ons, toolbars, system optimizers, and other offered bloatware.
iProtectYou termination steps
To remove iProtectYou, you should rely on certified and reliable tools. Anti-malware programs can perform a full system scan on your computer and detect all possible threats. FortectIntego or Malwarebytes are professional tools that researchers[3] recommend. Install one of these programs and clean tour system immediately.
iProtectYou removal is important if you want to use your device normally again. Do not forget that there is a possibility that this app accessed Windows Registry. Cleaning your PC more often can be beneficial in general. So keep your anti-malware tool up to date and run it from time to time.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of iProtectYou. Follow these steps
Uninstall from Windows
Get rid of iProtect You by following these steps:
-
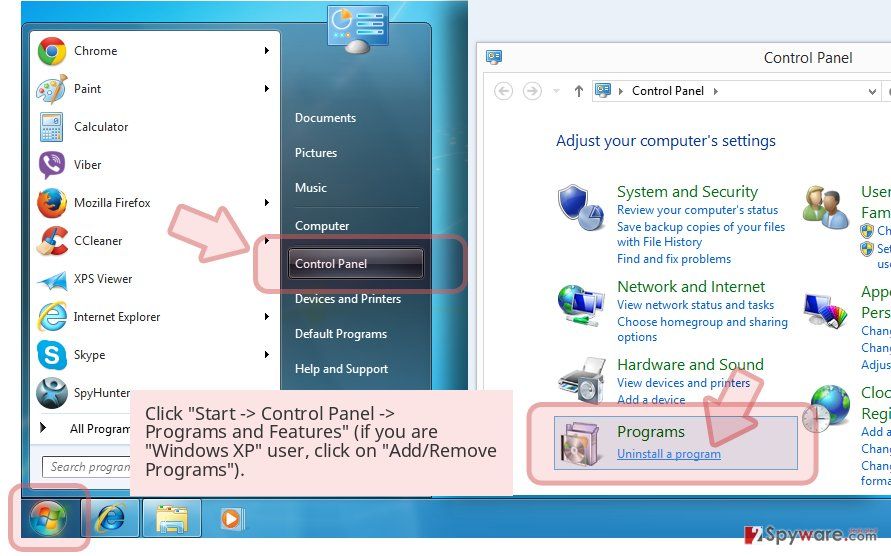
Click Start → Control Panel → Programs and Features (if you are Windows XP user, click on Add/Remove Programs).

-
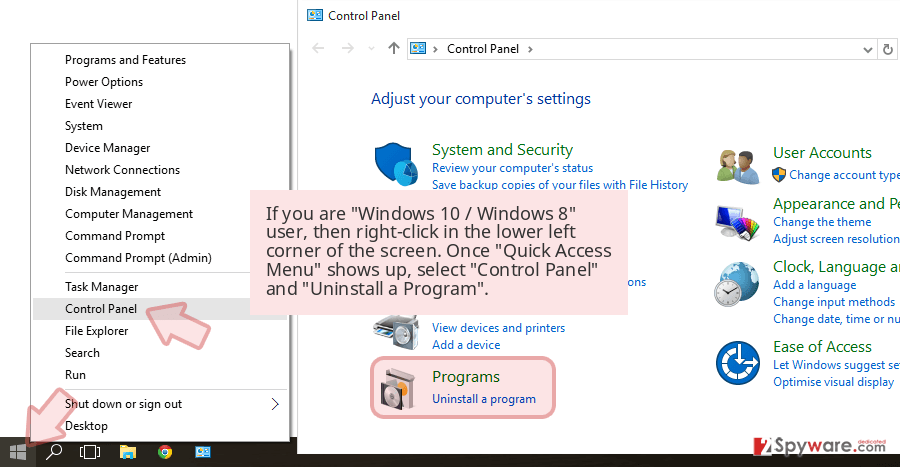
If you are Windows 10 / Windows 8 user, then right-click in the lower left corner of the screen. Once Quick Access Menu shows up, select Control Panel and Uninstall a Program.

-
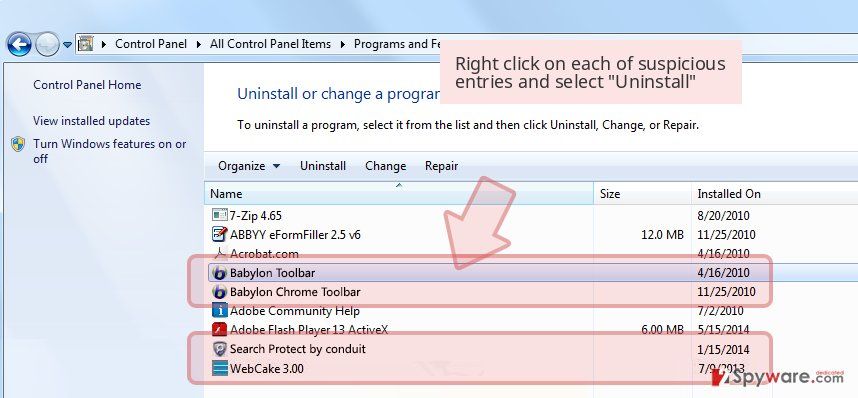
Uninstall iProtectYou and related programs
Here, look for iProtectYou or any other recently installed suspicious programs. -
Uninstall them and click OK to save these changes.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of iProtectYou registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting spyware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.