LegendDeploy Mac virus (Free Guide)
LegendDeploy Mac virus Removal Guide
What is LegendDeploy Mac virus?
LegendDeploy is a Mac virus that can seriously compromise your computer security
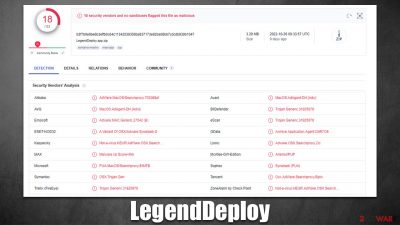
LegendDeploy is malicious software that attacks Mac systems. It belongs to a large family of Adload viruses, which have been known in the cybercrime landscape for at least five years. While the main goal of malware is to function as adware[1] and expose users to ads, there are plenty of other characteristics that are considered malicious.
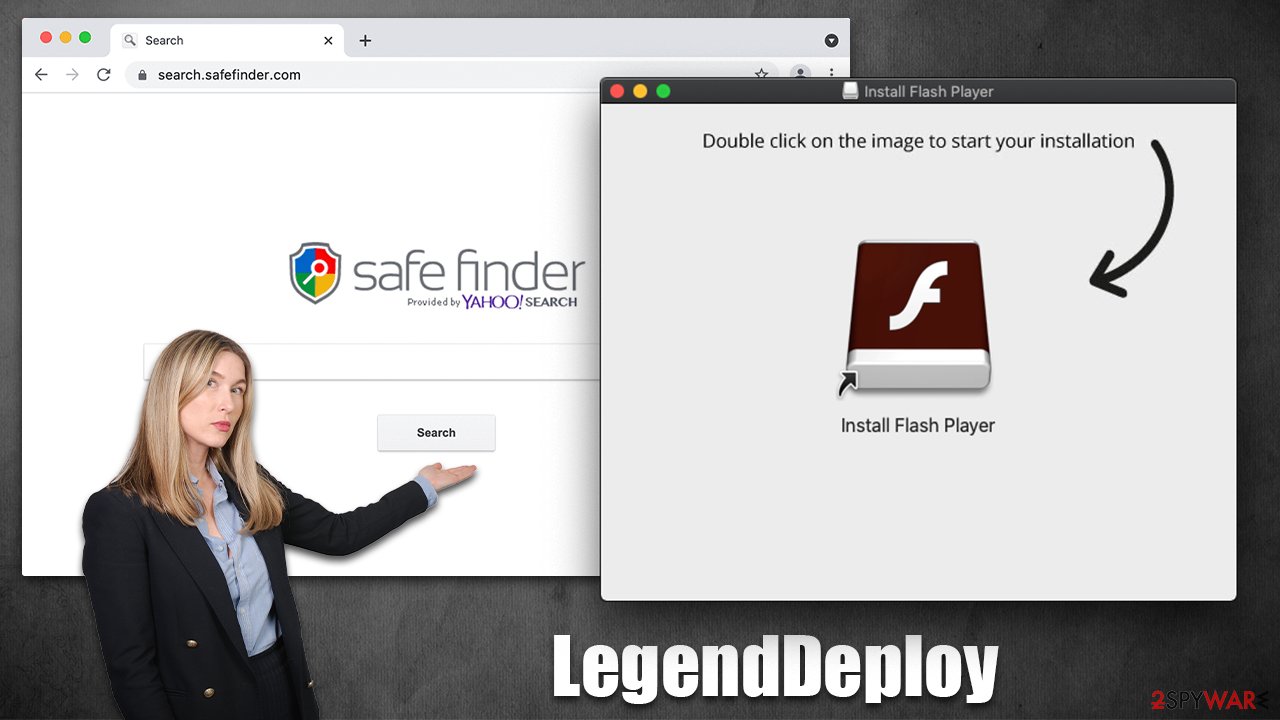
The LegendDeploy virus commonly attaches itself to Mac operating systems via fake Flash Player installers and illegal software bundles that are downloaded from malicious websites. Once installed, the virus will typically change your browser settings (for example, it may change your homepage and search provider to an alternative such as Safe Finder) without you knowing and expose you to sponsored links and intrusive ads.
The browser extension is designed to acquire various personal information, including login passwords or credit card information, creating serious privacy and security risks. Malware is especially challenging to remove since it employs numerous persistence strategies to stay on the system for as long as possible. How to effectively eliminate the infection and prevent its recurrence is explained below.
| Name | LegendDeploy |
| Type | Mac virus, adware, browser hijacker |
| Malware family | Adload |
| Distribution | Users typically get infected after being tricked by a fake Flash Player update, although repacked installers from torrent sites can also be the cause of infection |
| Symptoms | A new extension is downloaded to the browser, along with a matching app; search and browsing preferences are changed to use a different search engine; new user profiles and login items are created on the account; intrusive advertising and redirects |
| Risks | Installation of other malware, personal data disclosure to cybercriminals, financial losses |
| Removal | The easiest way to eliminate unwarned and malicious software on Macs is by performing a full system scan with SpyHunter 5Combo Cleaner security software. Alternatively, you can attempt to terminate the infection manually |
| System optimization | Third parties can use cookies to continue tracking your online activities, so we recommended clearing browser caches and other leftover files with FortectIntego |
Adload versions
LegendDeploy is descended from Adload, one of the most well-known malware families out there. After being discovered in the wild for the first time in 2017, it has subsequently released hundreds more variations, including MainFrameSelect, ActiveLink, PowerAnalytics, and many others.
The operation and distribution of the strain are largely unchanged despite some slight alterations between versions. One of the simplest ways to spot the infection is that it constantly utilizes the magnifying glass icon for both the core application and the browser extension.
Although LegendDeploy is classified as adware, its effects on the system go much beyond just displaying advertising; in fact, many of its characteristics are regarded as harmful.
Capabilities of the virus
Adload infects a large number of Apple devices because it employs relatively straightforward distribution and operating methods that are highly effective for Mac machines. You should never download software from websites that distribute pirated software, and you should be alert of fraudulent Flash Player upgrades to prevent infection.
The virus's primary objectives – showing adverts and making pay-per-click[2] revenue – are supported by a wide range of other features. For instance, the virus can fully evade being detected by built-in Mac protections like XProtext and Gatekeeper by using AppleScript.[3]
The browser extension component of the virus also aids in carrying out its operations; in addition to reading users' passwords and credit card information, it also has the ability to insert advertising while they browse the web. Of course, this functionality is quite risky and could lead to identity theft and other massive problems.
Quick and easy LegendDeploy removal
Unlike normal apps, you likely won't be able to remove the browser extension or application easily. Thanks to its elevated permissions on your system, the app drops several malicious files and creates new profiles and login items. Therefore, we recommend getting rid of the LegendDeploy virus automatically with Malwarebytes or SpyHunter 5Combo Cleaner security software so you don't have to bother with the steps below. Regardless of which method of elimination you choose, we still recommend cleaning your web browser caches[2] thoroughly to prevent issues in the future.
Once installed, the malware runs background processes to fulfill its tasks. To remove the main application, you should first shit down these processes via the Activity Monitor:
- Open Applications folder.
- Select Utilities.
- Double-click Activity Monitor.
- Here, look for suspicious processes and use the Force Quit command to shut them down.
- Go back to the Applications folder.
- Find the malicious entry and place it in Trash.
![Uninstall from Mac 1 Uninstall from Mac 1]()
Login items are responsible for booting the malicious app as soon as the computer starts up, while Profiles tackle different account settings. These malware-related components should be deleted as follows:
- Go to Preferences and pick Accounts.
- Click Login items and delete everything suspicious.
- Next, pick System Preferences > Users & Groups.
- Find Profiles and remove unwanted profiles from the list.
Finally, you should get rid of Launch Daemons and other configuration data left by malware. Proceed with the following:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and delete all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
If you choose to eliminate the infection manually, the extension may still remain on your browser and continue gathering data and performing other malicious tasks. Thus, start by removing it:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
If you successfully deleted the extension through the conventional methods, you should additionally clear the browser caches to prevent the tracking of any additional data. Running a FortectIntego maintenance utility is the easiest way to accomplish this and get rid of all junk. Another choice is to adhere to these guidelines:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
If you were unable to uninstall the extension after trying all of the suggested methods, you could always reset the browser:
- Click Safari > Preferences…
- Go to the Advanced tab.
- Tick the Show Develop menu in the menu bar.
- From the menu bar, click Develop, and then select Empty Caches.
![Reset Safari Reset Safari]()
If you are using Google Chrome or Mozilla Firefox, find the malware removal details below.
Getting rid of LegendDeploy Mac virus. Follow these steps
Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Adware. Investopedia. Source of financial content on the web.
- ^ Pay-per-click. Wikipedia. The free encyclopedia.
- ^ Phil Stokes. Massive New AdLoad Campaign Goes Entirely Undetected By Apple’s XProtect. SentinelLabs. Security research blog.












