LIZARD (Phobos) ransomware (virus) - Free Guide
LIZARD (Phobos) virus Removal Guide
What is LIZARD (Phobos) ransomware?
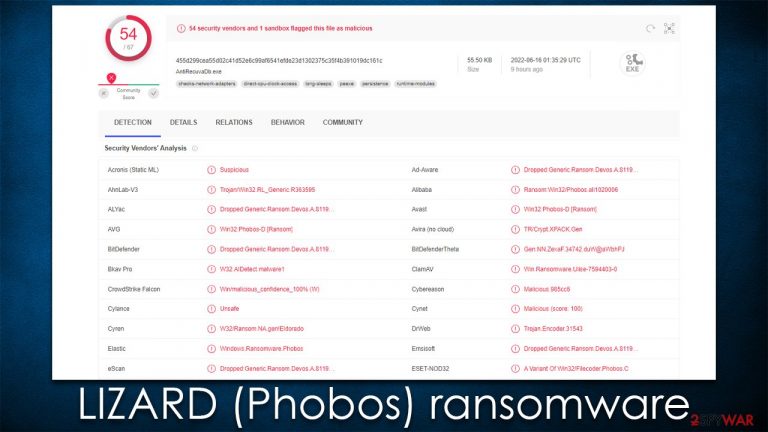
LIZARD (Phobos) is a ransomware-type virus that encrypts all files and then tries to extort money from victims
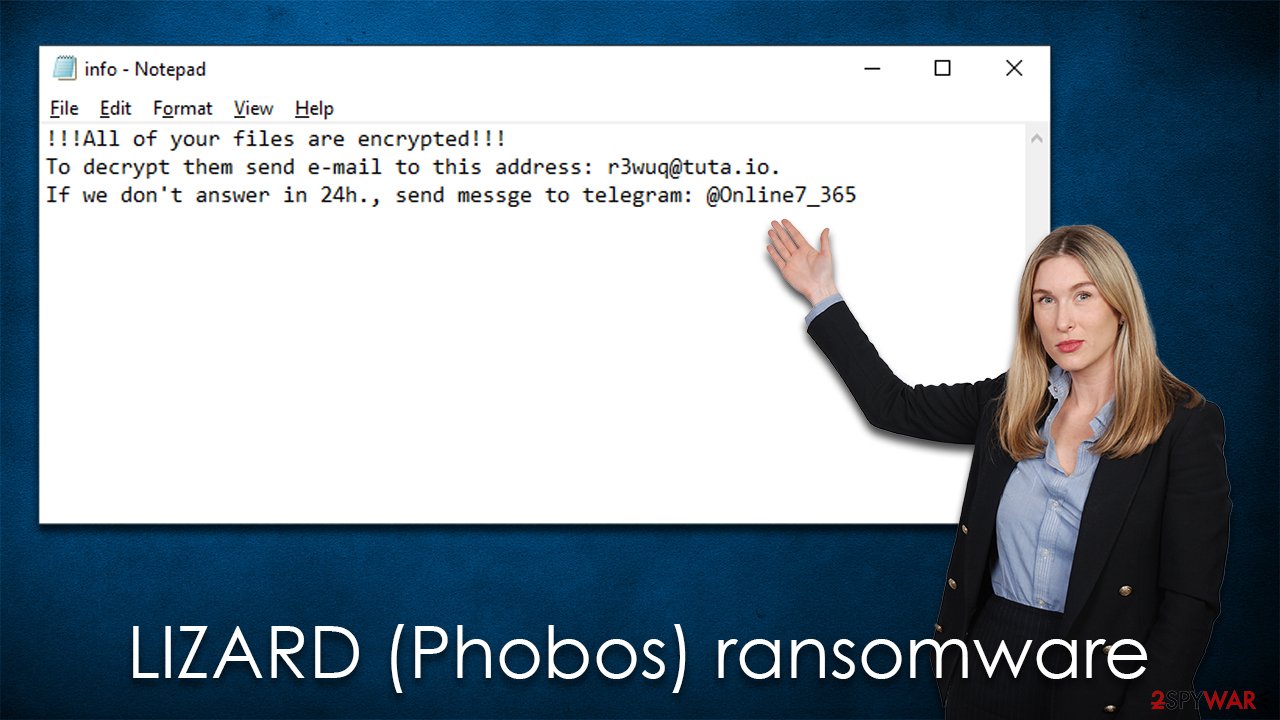
The main goal of LIZARD (Phobos) virus is to extort money from users after encrypting all files. As soon as the encryption of pictures, videos, documents, databases, and other personal data is finished (files acquire [ID].[r3wuq@tuta.io].LIZARD extension), malware delivers two ransom notes info.hta and info.txt, which explains to victims that they need to contact cybercriminals to via Telegram (@Online7_365) or r3wuq@tuta.io email in order to make the files usable again.
LIZARD ransomware was first spotted in the wild in the middle of June 2022. As the title suggests, it's a variant of an extended malware known as Phobos, which has been around for at least half a decade by now. Previous variants of the strain we already covered are Elbie, GUCCI, XHAMSTER, and many others. While they don't differ much, the contact information and a few other details vary.
| Name | LIZARD (Phobos) virus |
|---|---|
| Type | Ransomware, file-locking malware |
| File extension | .LIZARD |
| Ransom note | info.hta and info.txt |
| Contact | r3wuq@tuta.io or @Online7_365 on Telegram |
| File Recovery | The only secure way to restore files is by using data backups. If such is not available or were encrypted as well, options for recovery are very limited – we provide all possible solutions below |
| Malware removal | Disconnect the computer from the network and internet and then perform a full system scan with SpyHunter 5Combo Cleaner security software |
| System fix | Once installed on the system, malware might seriously damage some system files, resulting in crashes, errors, and other stability issues. You can employ FortectIntego PC repair to fix any of such damage automatically by replacing system corruption |
The ransom note
The ransom note is the first communication between the attacks and victims, which is why crooks always ensure that it is delivered as soon as the encryption process is finished. The main goal of cybercriminals is to increase the number of users who would pay a ransom, and the only way to do so is to ensure that they have contact information.
The LIZARD virus belongs to the Phobos family – ransomware that has been around for many years now, and it always delivers a couple of ransom messages – a brief one enclosed in a TXT file and an extended message that provides much more details about the whole thing. It reads the following:
All your files have been encrypted!
All your files have been encrypted due to a security problem with your PC. If you want to restore them, write us to the e-mail r3wuq@tuta.io
Write this ID in the title of your message
If you do not receive a response within 24 hours, please contact us by Telegram.org account: @Online7_365
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us. After payment we will send you the tool that will decrypt all your files.
Free decryption as guarantee
Before paying you can send us up to 5 files for free decryption. The total size of files must be less than 4Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
How to obtain Bitcoins
The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click 'Buy bitcoins', and select the seller by payment method and price.
https://localbitcoins.com/buy_bitcoins
Also you can find other places to buy Bitcoins and beginners guide here:
http://www.coindesk.com/information/how-can-i-buy-bitcoins/
Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
We do not recommend paying or even contacting cybercriminals, as they may never fulfill their promises and not send you the decryptor even after the payment is made. You are better off making copies of your encrypted files and then attempting to restore them using data recovery software, or waiting for a decryption tool for this Phobos variant.
Malware removal
Ransomware victims are often confused about what they should do next after being infected. Indeed, most infected users are first-time victims, and some don't even know what ransomware is. Indeed, it is important to perform malware removal and data recovery in the correct way; otherwise, the whole remediation might fail and result in even more damage.
As soon as malware gains access to the system, it may establish a connection with a remote Command & Control server. This allows cybercriminals to send additional commands to malware to perform, update it, or even deliver additional payloads. Thus, it is extremely important to disconnect your computer from the internet (as well as the network, if applicable) before proceeding with LIZARD (Phobos) virus removal.
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
Once your system is disconnected from the device, you can then perform a full system scan with SpyHunter 5Combo Cleaner, Malwarebytes, or another powerful security software to eliminate the infection. While it is true that ransomware can often self-destruct after performing its job of data encryption, it might not always be the case. Ransomware is often propagated along with other computer infections (mostly data-stealing Trojans), which can cause additional damage to privacy and computer security.
Fix damaged system files
After malware infection, Windows is no longer the same, as some system files might get damaged or even destroyed. This can result in system instability – crashes, failure to launch programs, BSODs,[1] and many other issues. If you are suffering from these problems after eliminating the infection, use data recovery software as explained below.
- Download FortectIntego
- Click on the ReimageRepair.exe

- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process

- The analysis of your machine will begin immediately

- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.

Alternative file recovery methods explained
The final step is to recover the locked files without paying cybercriminals. Users often misunderstand how data encryption works or know nothing about it. Some people believe that they can restore them as soon as they scan their computer with anti-virus or that their files are permanently corrupted as soon as they get encrypted – none of these are true.
The truth is that encryption algorithm such as AES or RSA,[2] or a combination of those if applied correctly, is extremely secure and can't be broken even by the most sophisticated supercomputers. At the same time, it does not mean that the data affected is corrupted – it simply needs a unique key, which is held on the attacker's servers.
Preparing the backups of your personal files is the best way to mitigate ransomware attacks. If you have not prepared backups, restoring LIZARD ransomware-encrypted data may be very difficult. Without backups, you can either use data recovery software or wait for a decryptor to be ready. Note that if you don't have working backups, you should make copies of encrypted files not to corrupt them during the recovery process.
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders which you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
Decryption tools might also be created for certain ransomware strains thanks to the efforts of security researchers. In some cases, law authorities seize the servers of malicious actors,[3] which allows the keys to be released by the public – reputable security vendors usually do this. Here are a few links you might find helpful:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Chris Hoffman. Everything You Need To Know About the Blue Screen of Death. How-To Geek. Site that explains technology.
- ^ Ron Franklin. AES vs. RSA Encryption: What Are the Differences?. Precisely. Software company.
- ^ DarkSide Ransomware Gang Quits After Servers, Bitcoin Stash Seized. KrebsonSecurity. Security news and investigation.
