Muslat ransomware (Removal Guide) - Free Instructions
Muslat virus Removal Guide
What is Muslat ransomware?
Muslat ransomware is the crypto-extortion based threat that focuses on locking users' files and requiring money for the alleged decryptor
Muslat ransomware is a cryptovirus that shows the ransom message in _readme.txt file and demands to pay for the decryption tool that may not even exist or work for your encrypted files. This is a version of Djvu ransomware that already has more than a hundred different variants released in the wild. Since this is a popular ransomware family, Michael Gillespie, a researcher that reports about these versions maintain a tool capable of decrypting files affected by this notorious malware, so follow his posts and wait for updates STOP virus decrypter. At the time of writing, the needed update was not released yet.
Since Muslat ransomware virus is a cryptocurrency-based malware, it is dangerous to contact criminals behind the threat. Cybercriminals don't care for the state of your files, so you should remove the threat, clean the machine, and ignore any suggestions to write these people. Ransomware becomes a threat that targets corporates, and even those victims restrain from paying the ransom.[1] Since there is a possibility to get your files back with STOP virus decrypter, remove Muslat ransomware from the PC and store encrypted data for later use once the tool gets upgraded. This way you can avoid additional virus damage.
| Name | Muslat ransomware |
|---|---|
| File marker | .muslat |
| Family | STOP virus |
| Contact information | Telegram: datastore. Emails: gorentos@bitmessage.ch, gorentos@firemail.cc |
| Ransom note | _readme.txt |
| Distribution | Email campaigns delivering notifications with file attachments including malicious documents or infected links |
| Decryption possibility | Follow STOP decrypter updates by Michael Gillespie |
| Elimination | Use FortectIntego for Muslat ransomware removal |
Ransomware attack starts with a system check during which threat actors can see if the computer was already infected or not, the location of a victim, other details about the device in particular. Muslat ransomware developers then start the encryption process it all the information is satisfying.[2]
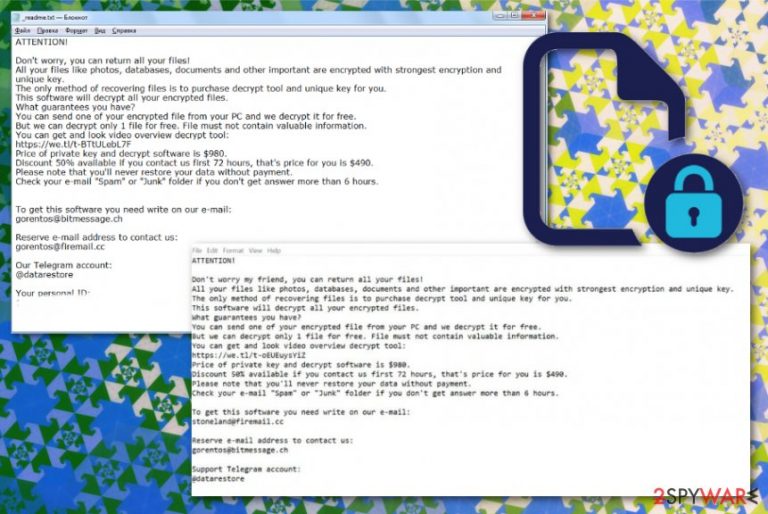
When your files get encrypted, virus places a ransom note on the desktop and in every folder with encoded data. _readme.txt reads the following:
ATTENTION!
Don't worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-7AKxZTQTdy
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
stoneland@firemail.ccReserve e-mail address to contact us:
gorentos@bitmessage.chOur Telegram account:
@datarestoreYour personal ID:
Muslat ransomware gets the name from the file appendix .muslat that appears on every photo, document, audio, or video file once the encryption is done. This is the primary function that cryptovirus has, but file-locking is not the only process that malware runs on the machine.
Although the ransom discount and test decryption build a trust, cybercriminals shouldn't be trusted at all. You need to remove Muslat ransomware as soon as you notice the ransom message or locked files and added programs. The sooner, the better because such malware alters many system files and functions:
- deletes Shadow Volume Copies;
- disables anti-malware tools and security functions;
- installs programs and data;
- changes registry entries.
Muslat ransomware can find various files stored on the machine, including credentials or account information that victims save on their device. If so, such details may be used to steal money or even identity. Users' account credentials, banking details, and similar personal information can be especially valuable for malicious actors who want to scam people.
Since Muslat ransomware developers can easily obtain this information, make sure to eliminate the threat as soon as possible. You can notice system slowdowns or any other symptoms, but once your data gets encrypted and marked with the extension, you can be sure that ransomware is the one that runs on your machine.
Muslat ransomware removal may seem especially difficult, but various AV engines can help with the issue.[3] Get a reliable anti-malware program and run the full system scan on the computer that got affected by this virus. Then, the tool itself can detect and indicate malicious programs, corrupted or useless files that need to be removed from your device.
Employ FortectIntego for the process and make sure to terminate Muslat ransomware altogether, so all the associated files get deleted alongside the main ransomware. Then, you can double-check it the system is virus-free and recover data using file backups or data restoring software.
Email phishing campaigns hide more than scams and advertisements
Spam email box fills up quickly, and often we just ignore the contents that automatically go there. However, malicious actors managed to update such campaigns and send dangerous emails to your primary mailbox. This becomes especially dangerous when people are not paying close attention to emails they receive and, most importantly, open on the computer.
Such emails pose as messages from services or companies with financial information or order details, so people are more willing to open a commonly received mail. Unfortunately, emails include file attachments and hyperlinks that lead to a direct download of malicious virus or payload of the malware.
You should at least avoid downloading and opening the attached file, so malicious macros are not triggered, and the ransomware payload is not dropped on the system. Experts[4] note to pay close attention to the sender and avoid opening emails that you were not expected to get, especially with attached files.
Eliminate Muslat ransomware alongside other files and applications from the system
You need to react to the Muslat ransomware virus infection as soon as you notice the ransom file or any suspicious activities possibly related to such type of malware. The sooner you delete this virus, the better because cryptovirus has no time to affect essential parts of the computer.
Muslat ransomware removal process requires anti-malware tools because all ransomware-type intruders can install applications and files on the affected machine without any permission and even disable more crucial programs. During a full system scan, reliable antivirus tool finds and indicates issues find on the PC.
Get FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes and remove Muslat ransomware while cleaning the system entirely. To be sure that all programs and files get deleted, reboot your PC in Safe Mode. We have a few tips for you below the article, as well as a few data recovery options.
Getting rid of Muslat virus. Follow these steps
Manual removal using Safe Mode
Reboot your machine in the Safe Mode with Networking to ensure that antivirus tool works for Muslat ransomware removal
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Muslat using System Restore
System Restore can help with ransomware because this feature allows recovering the machine in a previous state before the cyber infection
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Muslat. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Muslat from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Muslat, you can use several methods to restore them:
Do you need a file backup alternative? Try Data Recovery Pro
Data Recovery Pro can restore encrypted or accidentally deleted files
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Muslat ransomware;
- Restore them.
Windows Previous Versions feature – a method to restore Muslat ransomware affected data
When you enable System Restore, Windows Previous Versions can be used for file recovery
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer is capable of recovering encrypted data
Muslat ransomware can delete Shadow Volume Copies. However, when those are left untouched by the cryptovirus, ShadowExplorer can restore lost data
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
STOP decrypter can work for Muslat ransomware encrypted files. But there is a need for an update. Follow the researchers' reports
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Muslat and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Danny Palmer. Two-thirds of companies pay ransomware demands: But not everyone gets their data back. ZDNet. Technology news and advice.
- ^ Encryption. Wikipedia. The free encyclopedia.
- ^ Ransomware detection rate. Virustotal. Online malware scanner.
- ^ Senzavirus. Senzavirus. Spyware related news.







