Mybarpoint.xyz ads (fake) - Tutorial
Mybarpoint.xyz ads Removal Guide
What is Mybarpoint.xyz ads?
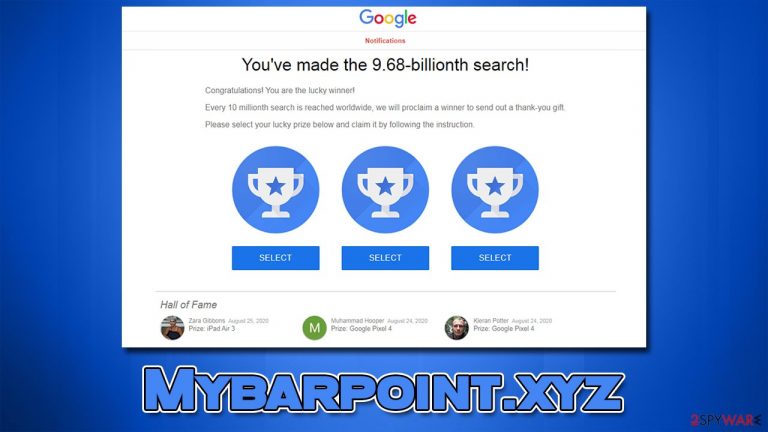
Mybarpoint.xyz scam wants you to click on one of the fake gifts: it's fake
Mybarpoint.xyz is a fake website that promotes survey and gift card scams.[1] You may have accessed it accidentally while browsing the web, although redirects from potentially dangerous websites are more likely to occur. In some rarer cases, adware could also be one of the main reasons you encounter phishing[2] messages.
Upon entry, users are told that they have been selected by a reputable company (Google, Amazon, etc.) to receive an expensive gift – all they have to do is answer a few questions or simply select one of the three gift boxes. What people don't know is that the main goal of the Mybarpoint.xyz scam is to make them provide their personal information or subscribe to useless services.
If you have encountered this scam, you should not interact with any of its components and not provide any of your personal details. Otherwise, you might face personal information disclosure or even identity theft.[3] Below we provide several tips on what to do in both scenarios and what to do to protect yourself in the future.
| Name | Mybarpoint.xyz |
| Type | Scam, phishing, adware |
| Goal | Make people provide personal information, subscribe to useless services, download malicious software or subscribe to push notifications |
| Distribution | Adware, malicious links, redirects from other websites |
| Dangers | Malicious software can cause redirects to malicious websites – financial losses, malware infections, and data disclosure can be more likely |
| Removal | You should check your system for adware – scan it with SpyHunter 5Combo Cleaner for a quick check |
| Other tips | After the removal of PUPs and malware, we recommend scanning the system with FortectIntego to clean browser caches and fix virus damage automatically |
Scam analysis
Mybarpoint.xyz is a misleading website that could promote various fake giveaways, gift cards, and other lottery-based material. There are many variations on how this can be portrayed, but these scams usually use a name of a reputable and well-known company to make the scheme more believable.
They also attempt to imitate the looks of websites those companies use, so, for example, if you see the “You've made the 9.68-billionth search!” scam, Google's typical colors, logos, font, and other attributes would be shown. In other cases, you could be told that you were selected by Amazon for a chance to receive a pricy item:
Congratulations!
Amazon.com User!
You've been selected as a lucky user for a chance to get the $1000 Amazon Gift Card, Apple iPhone X or Samsung Galaxy! Please click OK for a chance to GET your reward
It is important to note that if the message seems too good to be true, it likely is. High-profile companies don't randomly select people only to give them items worth hundreds or thousands of dollars – there's simply no point in them doing this.
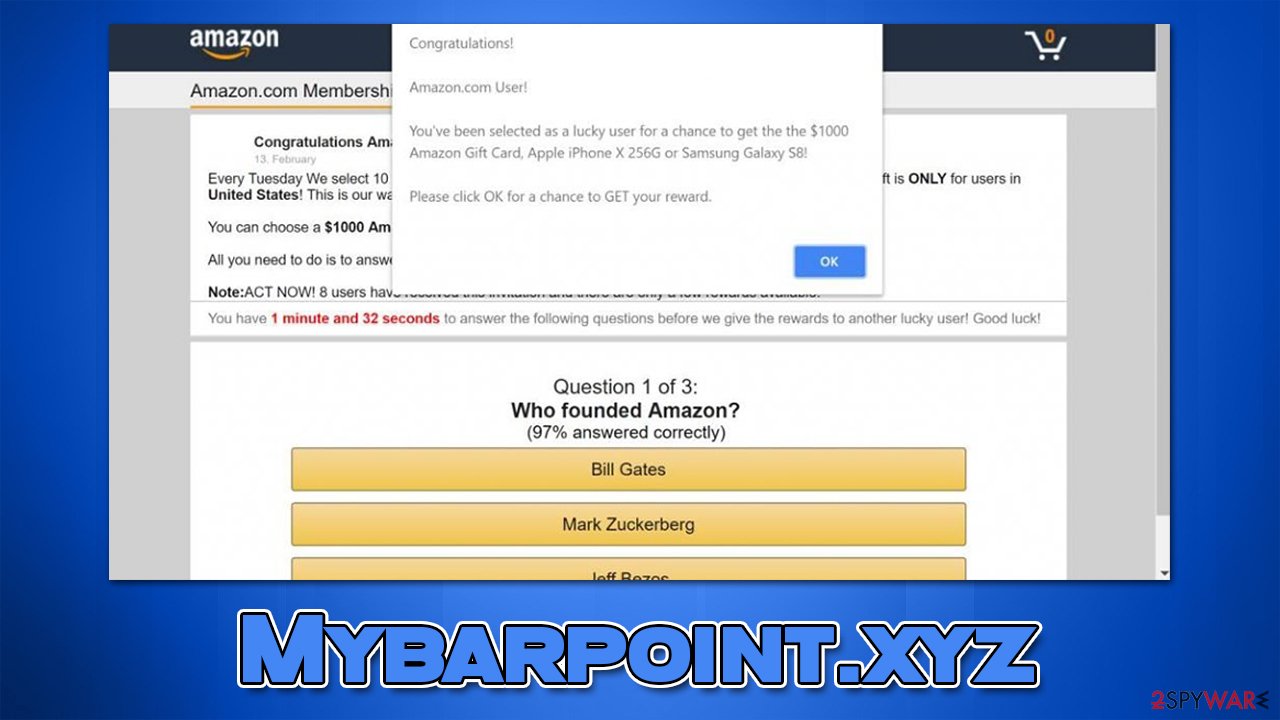
Therefore, we recommend you always be skeptical when it comes to giveaways, especially if the prizes are way too good. Also, always check the URL of the page showing the message – it is pretty obvious that Mybarpoint.xyz has nothing to do with Amazon or Google.
Adware and malware removal
If you constantly encounter misleading messages and phishing websites, you should make sure your system is not infected. The first thing you should do is scan your system with SpyHunter 5Combo Cleaner or Malwarebytes anti-malware. It can locate all adware and malware to remove them effectively.
Some potentially unwanted programs might not be detected automatically as they are not inherently malicious, but they can lead to a lot of privacy and security issues sometimes. Thus, check the installed applications section and get rid of everything you find suspicious:
Windows
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till the uninstallation process is complete and click OK.

Mac
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To thoroughly remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

PUPs can also be installed as browser extensions. In fact, it is the most common form used by their distributors, as they are easy to produce and replicate under different names if needed. The easiest way to remove unwanted add-ons is by clicking the “Extensions” button next to the settings menu.
After that, we recommend cleaning web browsers from cookies, caches, and other web data, as trackers could remain locally. The easiest way of doing this is by employing the FortectIntego repair and maintenance tool, although, if you prefer it, the manual method is also available:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

MS Edge (legacy)
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

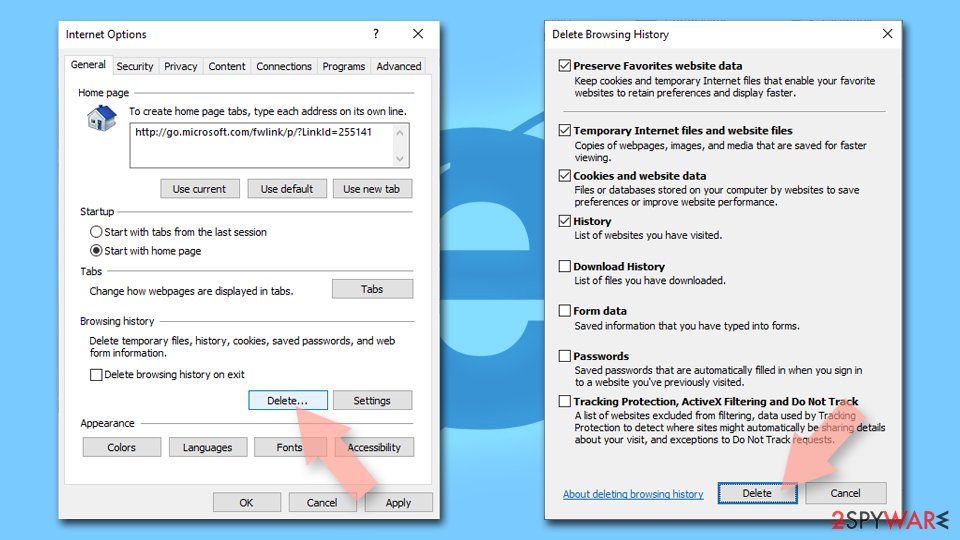
Internet Explorer
- Press on the Gear icon and select Internet Options.
- Under Browsing history, click Delete…
- Select relevant fields and press Delete.
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Lisa Rowan. Gift Card Scams Spiked In 2021. Here’s How To Avoid Getting Duped. Forbes. American business magazine.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ Julia Kagan. Identity Theft. Investopedia. Source of financial content on the web.
