National-speed-device-clean.rest ads (scam) - Free Instructions
National-speed-device-clean.rest ads Removal Guide
What is National-speed-device-clean.rest ads?
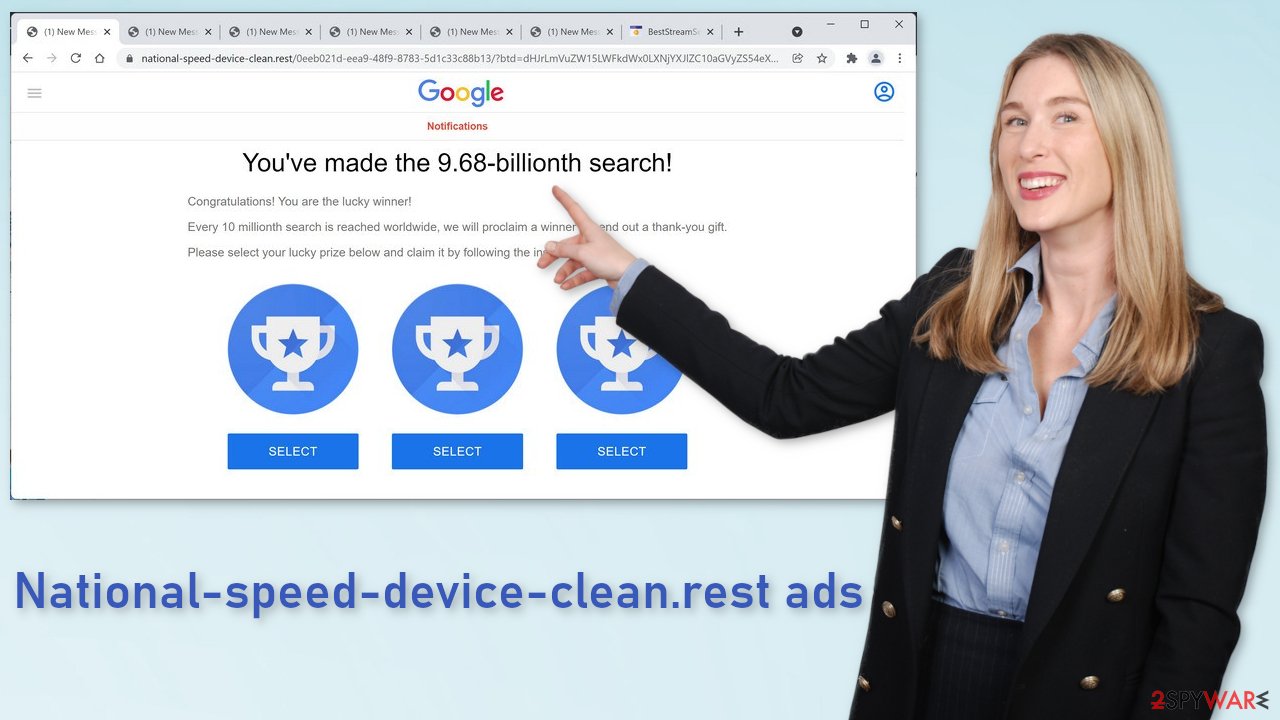
National-speed-device-clean.rest tries to lure out users' personal information in the hopes of receiving a gift
National-speed-device-clean.rest is a phishing site that displays a fake message trying to pretend that it's a tech company, for example, Google or Apple. Seems like the “You've made the 9.68-billionth search” scam is still floating around the Internet luring less IT-savvy users in.
Once people stumble on this website, from appearance, it looks like a legitimate Google site because of the similar formatting. They are met with an exciting message, and of course, many want to believe it. But as the saying goes – if something seems too good to be true, it probably is. The text on the site says:
Congratulations! You are the lucky winner!
Every 10 millionth search is reached worldwide, we will proclaim a winner to send out a thank-you gift.
Please select your lucky prize below and claim it by following the instruction.
It would be nice if it was true. You should know that big tech companies do not select random visitors and shower them with gifts. Fraudsters behind the site want you to act based on emotions and follow the instructions in the hopes that this is real. In reality, all they want from you is your personal information or to infect you with PUPs (potentially unwanted programs) and malware.
| NAME | National-speed-device-clean.rest |
| TYPE | Phishing page, survey scam |
| SYMPTOMS | Questionable websites, advertisements pop-up unexpectedly while searching the web |
| DISTRIBUTION | Shady websites, deceptive ads, freeware installations |
| DANGERS | Installation of PUPs or malware, sensitive information disclosure, monetary losses |
| ELIMINATION | In order to avoid malicious ads, you should install a reliable ad-blocking app; check your system for adware |
| FURTHER STEPS | If you want to clean your web browsers quickly, we recommend using FortectIntego repair tool |
Crooks often choose to disguise themselves as a well-known brand that is trusted in order to increase their chances. People are more likely to believe anything if the message looks like from a trusted source that would never raise any suspicion. It is clear that Google has nothing to do with this page.
In the past, these kinds of pages were all over the place, so Google has done its part in trying to contain them but they cannot get rid of every single one and users have to be aware of the social engineering techniques[1] used online. The best thing you can do if you see a similar site is to look for more information on it.
If Google is actually giving away prizes for random visitors, surely there should be press about it or at least information in their official channels. Unfortunately, most of the time you will realize that you cannot find anything. That alone should raise a red flag and make you not want to interact with the website.
What causes phishing pages to appear?
If you have encountered national-speed-device-clean.rest, there is a big chance that you have been visiting shady websites. Many times the appearance of scam pages is caused by illegal streaming platforms[2] because they are full of deceptive ads and sneaky redirects. Even though Google promised to get rid of fake “Download” and “Play” buttons[3] that take users to random sites that can be malicious, they still exist.
Another possible reason you ended up on this site is adware. It is a PUP that hides in your system and performs various tasks in the background, like injecting ads in the search results, and other places, causing redirects to promotional websites that advertise gambling, x-rated videos, antivirus software, etc. You should never install anything in your system from a site that just opened randomly. Always look for official web stores.
This sneaky application could have ended up in your system when you were installing software from a freeware site. They need to monetize their activities somehow, so they use a method known as software bundling. It is what it sounds like – you choose a program you want to get, and you download not only the desired program but a package of them.
That is why it is especially important to avoid torrent sites, peer-to-peer file-sharing platforms because they are often filled not only with spyware, hijackers, but with trojans and ransomware too. What you can also do is choose the “Custom” or “Advanced” installation method and untick the boxes next to files that you do not need.
Check the system for adware
If you are not sure which programs or apps could be causing the erratic browser behavior, you should instead rely on a trustworthy anti-malware so it can do the job for you. SpyHunter 5Combo Cleaner and Malwarebytes are our top choices when dealing with potentially unwanted programs, although any other security solution with a PUP detection feature should suffice.
Keep in mind that this method will also ensure that there is no dangerous malware installed on your system, as such malicious software as Trojans or backdoors are known to lay doormat for a while before they show any signs of infection.
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Adware is a well-known and, by now, prominent problem on macOS computers as well. If you are using a Mac, proceed with the following steps:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
Clear browsers
You should make sure that you clean your web browsers accordingly. One of the easiest ways of doing so is by employing a PC repair and maintenance utility FortectIntego, it can easily take care of your privacy by cleaning your browsers quickly. Also, malware-related damage, some computer infections, and even computer errors can be removed thanks to this application.
If you want to clean your browsers manually, you can do that as well, although keep in mind that it is a much more tedious process than using an automatic tool.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.
![Remove extensions from Edge Remove extensions from Edge]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Internet Explorer:
- Open Internet Explorer, click on the Gear icon (IE menu) on the top-right corner of the browser
- Pick Manage Add-ons.
- You will see a Manage Add-ons window. Here, look for suspicious plugins. Click on these entries and select Disable.
![Remove add-ons from Internet Explorer Remove add-ons from Internet Explorer]()
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Social engineering (security). Wikipedia. The free encyclopedia.
- ^ https://crimestoppers-uk.org/keeping-safe/online-safety/streaming-online-know-the-risks. Crimestoppers. Online Safety Tips.
- ^ Andy Maxwell. Google Targets Fake ‘Download’ and ‘Play’ Buttons. Torrentfreak. Privacy and filesharing news.










