Netwalker ransomware (Easy Removal Guide) - Recovery Instructions Included
Netwalker virus Removal Guide
What is Netwalker ransomware?
Netwalker ransomware – a type of malware that focuses on attacking cities and organisations
Netwalker ransomware, otherwise known as Mailto ransomware, is a file locking virus that was first spotted in August 2019, and since then keeps attacking high profile companies and even municipalities. The most recent victim of malware – Illinois Public Health District website, which was used to deliver information to people about the COVID-19 virus.[1] Luckily, the health organization managed to recover swiftly and did not pay the ransom.
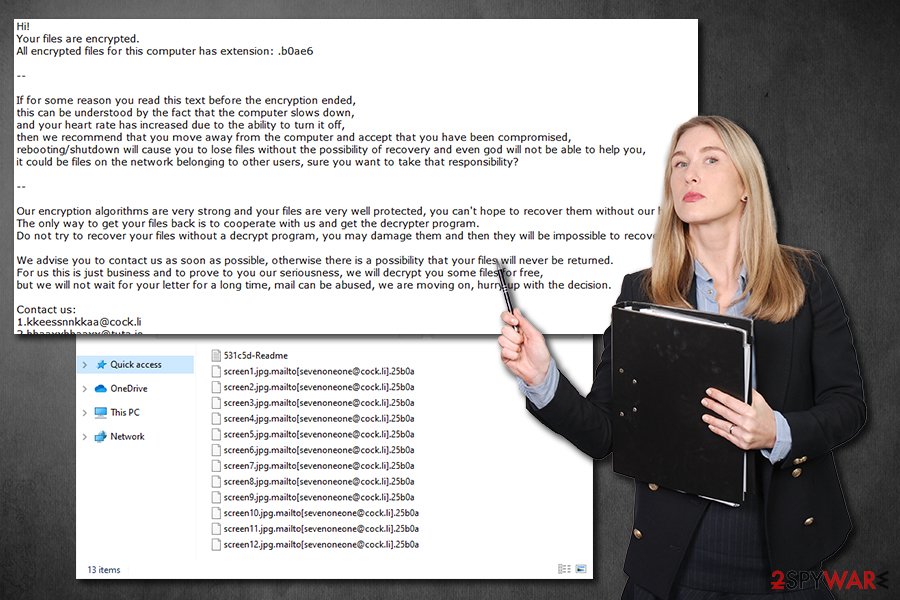
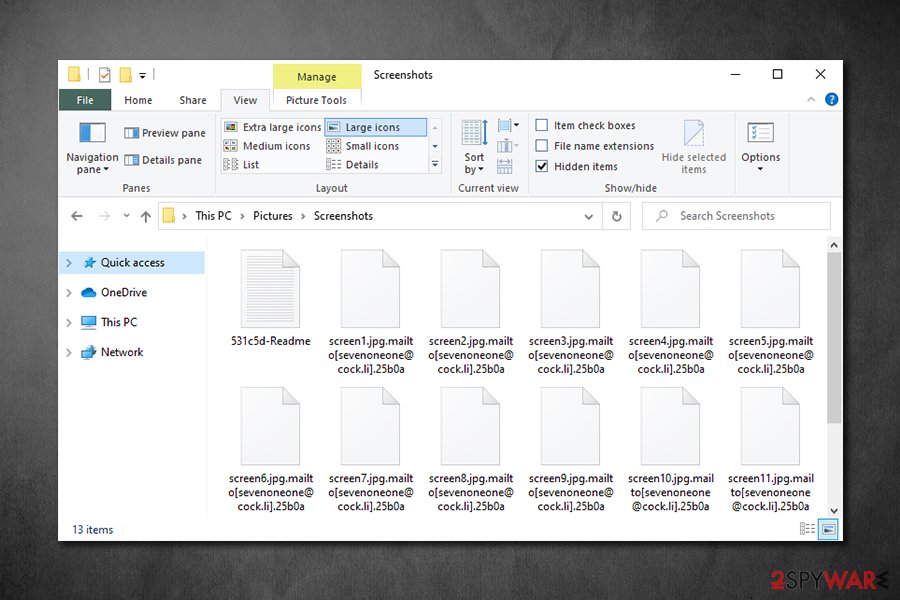
The main goal of Netwalker virus – encrypt pictures, documents, databases, and other data on the machines and networks with AES cipher and then demand a ransom payment for the decryption tool that can return files into their original state. Typically, suchlike data is marked with a unique code (ID), which usually consists of six or five alphanumeric characters, for example, .e85fb1, .c3f7e, or 531c5d. In earlier versions, Netwalker ransomware also used .mailto extension – hence the original name.
| Name | Netwalker ransomware |
| Type | File locking virus, cryptomalware |
| Cipher | Malware uses a symmetric algorithm AES to perform encryption process on all personal files located on local and networked drives |
| Previously known as | Mailto, Kazkavkovkiz, Kokoklock |
| File extension | Malware uses alphanumeric characters as an extension, which also indicates the user's ID, as well as a contact email (in most cases). Example of an affected file: document.xlsx.mailto[sevenoneone@cock.li].25b0a |
| Ransom note | [ID/extension]-Readme.txt, for example, 25b0a-Readme.txt |
| Contact | In newer versions, victims are asked to visit a predetermined Tor site; previous contact emails include kazkavkovkiz@cock.li, Hariliuios@tutanota.com, 2Hamlampampom@cock.li, Galgalgalgalk@tutanota.com, kkeessnnkkaa@cock.li, hhaaxxhhaaxx@tuta.io, sevenoneone@cock.li, kavariusing@tutanota.com |
| Data recovery |
Without backups, there is no 100% secure way of recovering compromised data. The remaining options include:
|
| Malware removal | To get rid of the infection, scan your machine with reputable anti-malware software, such as SpyHunter 5Combo Cleaner or Malwarebytes |
| System fix | In case your computer works slowly or is experiencing other stability issues after the infection is terminated, use FortectIntego to fix virus damage |
After the data locking process, the Netwalker virus delivers a ransom note which name compiles of victim's ID – “ID-Readme.txt,” which also matches the marker appended to each of the locked files. Inside the note, cybercriminals explain that their system was compromised, and that they need to pay a ransom in cryptocurrency in order to regain access to data. For communication purposes, criminals provide email addresses, such as Hamlampampom@cock.li, avariusing@tutanota.com, or sevenoneone@cock.li, although in the newest variants users are asked to connect to a Tor network instead.
There are several different ways of Netwalker ransomware delivery – malicious actors often employ several attack vectors to infect as many victims as possible. The most common distribution methods include:
- Spam email attachments or hyperlinks
- Software vulnerabilities and exploit kits[2]
- Malicious ads
- Fake updates
- Weakly protected RDP connections
- Software cracks, etc.
If you were unlucky enough to get infected with this virus, you should pay close attention to your computing practices in the future – you can find more tips in the second section of this article. Nevertheless, you should now focus on alternative methods for data recovery, as well as Netwalker ransomware removal.
Before the Netwalker file virus begins the encryption process, it first modifies Windows systems in order to operate as intended. For example, it uses a built-in API to inject malicious code into the explorer.exe process, which is protected – it helps the encryption to be performed successfully.
Additionally, Netwalker ransomware also performs other standard changes for a successful infection routine, including deletion of Shadow Volume Copies, insertion of new malicious files and processes, modification of Windows registry database, etc. To revert these changes later after malware termination, you can use repair tools like FortectIntego.
Once the preparations are complete, Netwalker ransomware will begin to scan the system for data to encrypt – it targets the most commonly used file types, including .pdf, .jpg, .dat, .xlsx, .mp4, .txt, .zip, and many others. This way, cybercriminals guarantee that they can cause maximum damage to users and encourage them to pay the ransom. Despite that, the main goal of Netwalker virus authors is not to corrupt the system, so it skips files located in Windows, Program Files, Microsoft, Internet Explorer, and other folders.
Depending on the version of the infection, Netwalker ransomware will append each of the files with a particular extension, which usually includes a contact email. For example, an encrypted file would look as follows: document.xlsx.mailto[sevenoneone@cock.li].25b0a. The shortcut of the file would no longer represent the app it usually can be opened with, and instead, victims will not be able to use data at all.
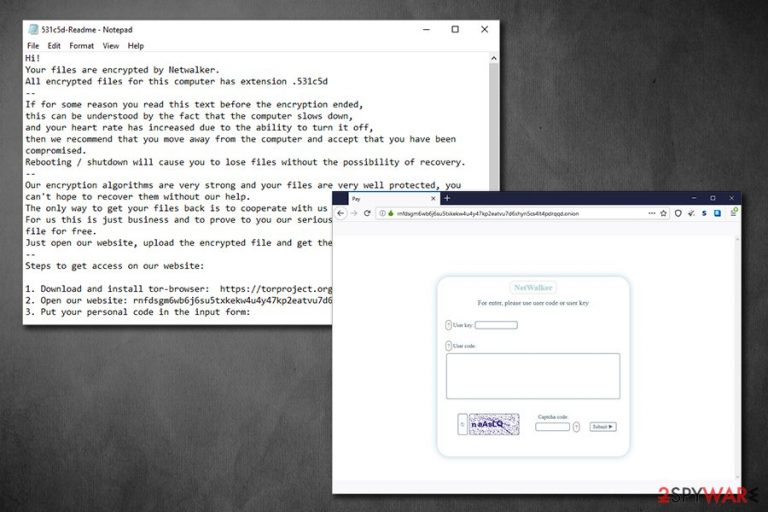
The ransom note that the virus drops also varies slightly, depending on the version. The most recent Netwalker ransomware note reads the following:
Hi!
Your files are encrypted by Netwalker.
All encrypted files for this computer has extension .531c5d
—
If for some reason you read this text before the encryption ended,
this can be understood by the fact that the computer slows down,
and your heart rate has increased due to the ability to turn it off,
then we recommend that you move away from the computer and accept that you have been compromised.
Rebooting / shutdown will cause you to lose files without the possibility of recovery.
—
Our encryption algorithms are very strong and your files are very well protected, you can't hope to recover them without our help.
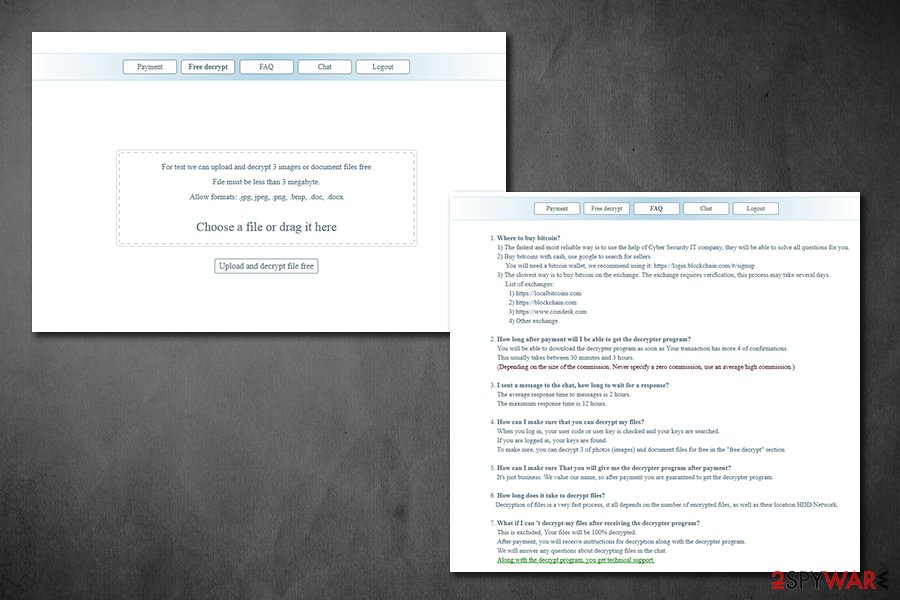
The only way to get your files back is to cooperate with us and get the decrypter program.
For us this is just business and to prove to you our seriousness, we will decrypt you one file for free.
Just open our website, upload the encrypted file and get the decrypted file for free.
—
Steps to get access on our website:1. Download and install tor-browser: https://torproject.org/
2. Open our website: rnfdsgm6wb6j6su5txkekw4u4y47kp2eatvu7d6xhyn5cs4lt4pdrqqd.onion/
3. Put your personal code in the input form:{code_531c5d:
Netwalker ransomware uses symmetric encryption algorithm AES, which means that the same secret key is used to lock and unlock data on the infected machine. There is no point in trying to guess it or acquiring this key from another victim, as it is unique per person. Unfortunately, there are very few possibilities to recover data without backups. However, if you think that paying criminals for Netwalker ransomware decryptor is a good idea, you should think twice, as they might simply not deliver the tool, and you will end up using your money along with data.
Thus, remove Netwalker ransomware first with the help of anti-malware software that detects the threat,[3], and then attempt to recover data using alternative methods we provide below. Nevertheless, we also advise making a copy of encrypted data prior to any actions.
Protecting your files from ransomware
As mentioned above, there are several methods for how ransomware manages to penetrate user devices. Some of the techniques used might be primitive, while others – more sophisticated, although the result remains the same for victims – their files are locked and can no longer be accessed. It is also important to note that file encryption and computer encryption are two separate actions, and malware removal will not return files into their original state. Precisely due to this reason, ransomware is so devastating.
While data backups can help a lot when dealing with file locking virus, malicious actors most recently started a disastrous trend – they threaten to publish information stolen from the infected machines. For a company or a business, suchlike data disclosure can be devastating. Thus, the best way to battle ransomware is not to get infected in the first place – here are some tips that could help you repel malware in the future:
- Equip your computer and networks with sophisticated anti-malware software;
- Protect your Remote Desktop connections: never use a default TCP/UDP port, use a VPN, disconnect from the service as soon as it is not needed, use strong passwords to protect access;
- Do not download pirated application installers or software cracks/loaders/keygens;
- When dealing with new emails, watch out for attachments like .pdf, .doc, .exe, .zip, or similar, as they could contain malware. Additionally, hover your mouse on a hyperlink and check the real address before clicking on it;
- Use two-factor authentication where possible;
- Update your operating system along with all the installed applications as soon as security patches are shipped.
Finally, you should always ensure that you store backups of your most important files, and they should not be connected with your main system in any way.
Terminate the Netwalker virus infection
Most users who get infected with ransomware never dealt with the infection before, so they usually don't know how to proceed. Indeed, having all files get locked can be a devastating and frightening experience for many, especially those that have important data on the infected machine. That being said, you should not rush Netwalker ransomware removal, as the action could permanently damage the encrypted files. In such a case, even a working decryption tool might fail to retrieve the compromised data.
Therefore, you should backup encrypted files and only then remove Netwalker ransomware from your computer. For that, you should use reputable anti-malware software and perform a full system scan (if you need to access Safe Mode, please check the instructions below). As previously stated, this action would not recover your files, unfortunately, so you are left with a limited number of options:
- paying criminals
- trying third-party software
- waiting till security experts develop a free decryptor.
None of these are ideal and pose a risk – that is why having backups is so important when dealing with ransomware. Our advice would be trying recovery software first and then exploring other options, as required.
Getting rid of Netwalker virus. Follow these steps
Manual removal using Safe Mode
To get rid of Netwalker virus in a troubleshooting environment, perform the following actions:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Netwalker using System Restore
System Restore can also be used to get rid of malware:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Netwalker. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Netwalker from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Netwalker, you can use several methods to restore them:
Data Recovery Pro can be used when trying to recover encrypted files
While this tool was not designed to decipher ransomware-encrypted files, it can sometimes bring at least some data back from the hard drive.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Netwalker ransomware;
- Restore them.
When attempting file recover, Windows Previous Versions feature might be worth paying attention to
This method will only work if Netwalker ransomware failed to delete Shadow Volume Copies, and you had System Restore enabled.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer might be the answer
ShadowExplorer is another option that may be viable if malware failed to perform the Shadow Volume Copy removal process.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryption tool is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Netwalker and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Debra Pressey. C-U Public Health District's website held hostage by ransomware attack. The News Gazette. Daily newspaper.
- ^ What is an Exploit Kit?. PaloAlto Networks. Security blog.
- ^ 2001.exe. Virus Total. File and URL analysis.







