Protectwatcher.xyz ads (scam) - Free Instructions
Protectwatcher.xyz ads Removal Guide
What is Protectwatcher.xyz ads?
Protectwatcher.xyz is a fake website that tricks users into buying a subscription

Protectwatcher.xyz is a fraudulent website created by cybercriminals to display false information to visitors in order to get them to download potentially unwanted software. The primary objective here is monetization through various illicit means, including showing fake virus alerts so that users would purchase software licenses, making money from push notification spam, and redirecting users to other dangerous websites that could jeopardize their privacy and computer security.
While Protectwatcher.xyz ads are not directly linked to some type of a virus infection, this possibility should not be excluded – adware is one of the most common potentially unwanted applications that could have been installed on your system unintentionally, so it's important to check it thoroughly.
How scammers achieve their goals
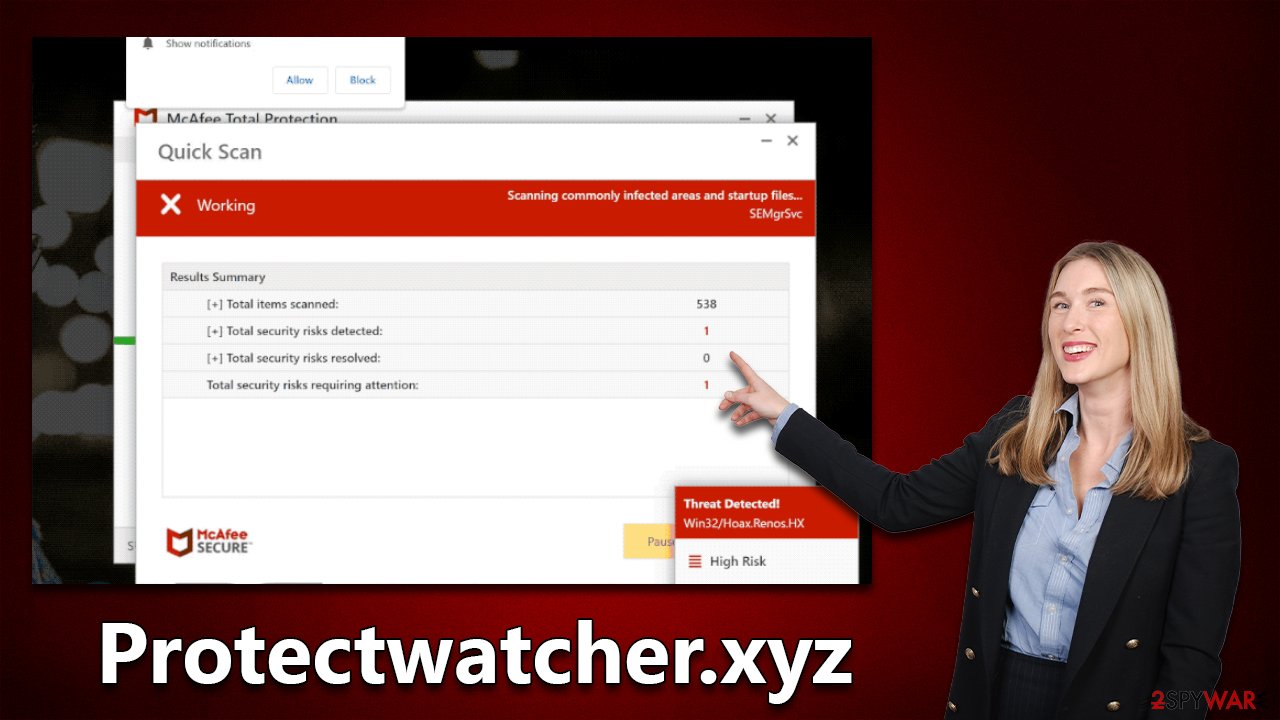
Many cybercriminals use the element of surprise to commit online fraud, as it is very effective in eliciting an emotional response from victims. The goal is to scare users into making hasty decisions before they realize they are being scammed. Protectwatch.xyz uses this tactic by impersonating a system scan with several pop-up messages and what seems to be a progress bar. A short while later, users are presented with the following alarming results:
Your PC is infected with 5 viruses!
ACTION REQUIRED
Your McAfee Subscription Has Expired!
Renew now to keep your PC protected.
If your PC is unprotected, it is at risk for viruses and other malware.
In reality, McAfee did not initiate any scans on your system – it is the work of scammers. In fact, it is virtually impossible for any website to diagnose your computer regarding its security, as only robust anti-malware software installed on the device can do so. Websites can, however, record general information about any user, including their operating system, IP address, web browser and its version, and similar details, which are also often abused in phishing[1] campaigns.
The fake results are shown to everybody who enters the scam page – they are simply a replica of the security vendor's anti-malware software. There are thousands of other websites that use reputable vendors' names in this scheme, and the fake scanning performed is identical to that of Protectwatcher.xyz (Alltimesecuritysystem.live, Haloweenpromob2.click, and Asxerk.click are just a few examples).
| Name | Protectwatcher.xyz |
| Type | Scam, fraud, phishing, redirect |
| Operation | The scam is based on scaring users into believing that their systems are infected and that they need to remove the allegedly found malware with promoted software |
| Distribution | Redirects from other malicious websites, adware |
| Risks | Loss of finances due to fake subscriptions; redirects to other malware-laden, scam websites; installation of potentially unwanted or malicious software |
| Removal | You should not interact with any links or ads shown on the scam page and shut it down immediately. Then, perform a full scan with SpyHunter 5Combo Cleaner security software as a precautionary measure |
| Other tips | Cleaning web browsers is one of the secondary things you should do after PUP/malware removal to secure your privacy. You can use FortectIntego to do it quicker |
What to do if you have enabled push notifications
First off, you should check whether you enabled push notifications from Protectwatcher.xyz, as it delivers the request as soon as one enters the website. If you have clicked the “Allow” button either intentionally or not, you might start receiving suspicious pop-ups with various dubious content in them – you might be exposed to more fake virus infection alerts, bogus lottery winnings, get-rich-quick[2] schemes, and similar.
Push notifications are not a direct result of virus infection and would show up as long as the website is permitted to do so. In other to stop the intrusive activity, you have to access browser settings and block the relevant URL as follows:
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

Removal of all unwanted and malicious software
Most people who land on a scam website have caused it themselves by clicking on a malicious link from another site. It's recommended to stay away from places like gambling, X-rated, torrent, and similar sites that often host these links and scripts. Not only can these places redirect you to phishing websites, but you may also be tricked into executing a malicious EXE file on your system, resulting in ransomware[3] or other malware infections, which can be devastating.
Browser redirects and an increased number of ads can also be caused by adware. So, if you're constantly being redirected to Protectwatcher.xyz or other strange websites, there's a decent chance that your device has some sort of unwanted software installed. A good place to start would be checking for programs on the system level:
Windows
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till the uninstallation process is complete and click OK.

Mac
Besides moving the unwanted app into Trash, removing adware might require a few more steps. Adware is known for inserting additional files that might cause the infection to resurface, so we recommend removing them too.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- Look for any dubious entries in the Application Support folder and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Browser extensions are also known to cause unwanted redirects and ads, so make sure you check whether all your extensions are trustworthy – remove everything you don't recognize or find suspicious.
If you're unsure when apps should or shouldn't be present, you can rely on SpyHunter 5Combo Cleaner or Malwarebytes to handle the adware removal process. This way, you won't have to worry about some of the components being left behind. We also recommend clearing browser caches to prevent data tracking with FortectIntego.
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ Get rich quick scams. SRA. Solicitors Regulation Authority.
- ^ Ransomware. Wikipedia. The free encyclopedia.
