Shlayer Trojan virus (Virus Removal Guide) - updated Feb 2019
Shlayer Trojan virus Removal Guide
What is Shlayer Trojan virus?
Shlayer Trojan virus is the threat that disables Gatekeeper to run malicious payloads on macOS devices

Shlayer Trojan virus is malicious software that targets Mac users and is typically installed via BitTorrent file sharing sites or fake Adobe Flash updates. Also known as OSX/Shlayer or Crossrider, the threat is especially dangerous because it establishes configuration profiles which increase the persistence and users struggle when trying to get rid of it. The most recent variant of the virus that spreads via rogue Flash Player updates focuses on disabling the macOS Gatekeeper security agent.[1] The discovery was made by TAU researchers, and according to them, versions from 10.10.5 to 10/12/.3 can get affected by this updated version. The malicious installer uses DMG, .pkg, .iso, .or zip file formats.
| Name | Shlayer Trojan virus |
| Also known as | OSX/Shlayer, Crossrider |
| Type | Trojan horse, adware |
| Affected systems | macOS |
| First discovered | 2018 |
| Symptoms | Aggressive pop-ups lead to insecure sites, the computer is filled with programs the user never installed, altered search engine and homepage, etc. |
| Recently discovered features | Disabling macOS Gatekeeper security agent to distribute malicious payloads |
| Distribution | Fake Adobe Flash updates, cracks, BitTorrent sites |
| Elimination | Download and install reputable security software |
| Optimization | To revert the damage done by the virus, scan your Mac with FortectIntego |
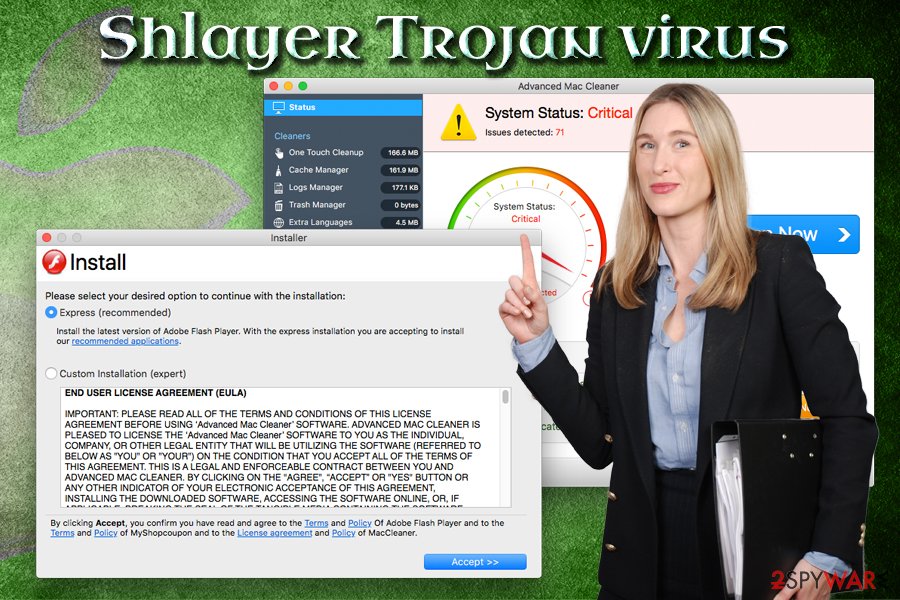
The primary purpose of Shlayer Trojan virus is to download and install various potentially unwanted programs, such as Advanced Mac Cleaner or Mac Cleanup Pro. Initially, Apple does not allow automatic installations of apps that do not come from Apple store, but Shlayer Trojan enables such functionality and macOS gets filled with bloatware that degrade the operation of the device. It is also known that the malware changes Google Chrome's or other browser's search engine to Chumsearch.com.[2]
Shlayer Trojan virus is one of the most well-known malware that is designed for Macs. Users typically wonder around BitTorrent sites and download a crack for legitimate software. It is not surprising that such illegal tools are often malicious, and most of the security applications will detect the file as malware, regardless of its functionality.
Alternatively, users might get infected when they get redirected to a malicious site that prompts them to update Adobe Flash. When Shlayer Trojan virus is launched, it will display two installation methods: Express (recommended) or Custom Installation (expert). If the latter is chosen, users can see what is actually being installed:
Custom installation (expert)
- Install Adobe Flash Player & MyShopcoupon.
- Install ChumSearch.
- Install maccleaner.
Shlayer Trojan virus installer will install the following onto the macOS:
- Advanced Mac Cleaner;
- Chumsearch.com browser hijacker;
- MyShopCoupon;
- MyMacUpdater;
- mediaDownloader
- Adobe Player
Once installed, Shlayer Trojan virus will perform the scan using Advanced Mac Cleaner and activate Siri's voice that says that the computer has multiple problems (which is obviously a lie). As typical to scareware, it will show numerous issues and, users who want to fix them need to pay a hefty $107 for it. As evident, users should ignore these warning and remove Shlayer Trojan virus together with the unwanted programs that it installed.
However, even after Shlayer Trojan virus removal, users will not be able to get rid of all the traces left by PUPs because it sets up a malicious configuration profile that lingers until the profile is deleted. We explain below how to accomplish that. Until then, users will still see Chumsearch.com as their main page on Safari and Chrome.

As researchers reported, samples discovered during their analysis affects most of the newest versions:
Samples discovered by TAU have been seen to affect versions of macOS from 10.10.5 to 10.14.3. To this point, all discovered samples of this malware have targeted only macOS. The malware employs multiple levels of obfuscation and is capable of privilege escalation.
Attackers use the legitimate code signing through Apple's developer program and that allows them to bypass MacOS's restrictions and warnings that are enforced using gatekeeper. However, Shlayer virus still uses shell scripts to deploy secondary payloads, run commands and execute scripts.
The final payload collects information from the system, creates a unique ID for the infected device and downloads other malware from the remote server. That secondary malware payload is an .app executable, as TAU report writes:
Once the malware has elevated to root privileges, it attempts to download additional software (observed to be adware in the analyzed samples) and disables Gatekeeper for the downloaded software using spctl. This allows the whitelisted software to run without user intervention even if the system is set to disallow unknown applications downloaded from the internet.
Shlayer Trojan virus can read and transmit the data you type while the malware is installed. It means that your name, passwords, and even banking details are at risk of the exposure. In addition, users will suffer from constant ads and redirects during their web browsing.
To detect the unwanted software on your device, check your applications folder. If you see any apps you never installed or the ones mentioned above – you should be concerned. The best way to protect your Mac is by employing reputable security software. We recommend using FortectIntego or SpyHunter 5Combo Cleaner, although you can use any other trusted AV engine that would detect malicious processes automatically.
Forget Adobe Flash or never install its updates from third-party sites
Adobe Flash is an outdated platform and is barely used anymore, as it will be shut down in 2020.[3] The player is known to have multiple security flaws,[4] and have been abused by cybercriminals for years (fake updates). Besides, most modern browsers have the feature already built-in, so there is no need to download Adobe Flash.
However, if you ever find the need for Adobe Flash, download it from the official website. Additionally, set it to click-to-run mode, so that it would not launch automatically on dangerous sites.
As it is typical of malware, it is widely spread on BitTorrent sites. Therefore, experts[5] recommend staying away from them. However, if you will be torrenting, keep in mind the following:
- Do not download cracks or keygens;
- Employ security software and keep it updated;
- Enable Firewall;
- Download ad-blocking software;
- Keep your system and software updated;
- Read comments before downloading;
- Scan each unknown file with anti-malware software.
Remove Shlayer Trojan virus with the help of these instructions
The first thing you have to do is to remove Shlayer Trojan virus and the applications that it installed. If you are savvy enough, you can proceed simply go Application folder and look for apps mentioned above. However, be aware that OSX/Shlayer is designed to download and install unknown programs automatically. Therefore, we recommend users using profession software that could take care of Shlayer Trojan virus removal automatically.
Once the unwanted applications are removed, you will have to delete the malicious profile that Shlayer Trojan created. Please follow these steps:
- Go to System Preferences;
- Click on Profiles;
- Locate a suspicious profile;
- Remove it by clicking on the “-” button.
Finally, we recommend resetting each of the installed browsers as described below.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Shlayer Trojan virus. Follow these steps
Delete from macOS
To remove Shlayer Trojan virus from your Mac, follow these steps:
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
To make sure all the settings are reset on MS Edge, follow these instructions:
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
You need to reset Safari by performing these steps:
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Shlayer Trojan registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Carbon Black Threat Analysis Unit. New MacOS malware variant of Shlayer discovered. Carbonblack. Big Data analytics.
- ^ Jay Vrijenhoek. New OSX/Shlayer Malware Variant Found Using a Dirty New Trick. Intego. Mac security researchers.
- ^ Matthew Wilson. Adobe Flash will be shut down in 2020. Kit Guru. Tech News | Hardware News | Hardware Reviews.
- ^ Adobe Security Bulletins and Advisories. Adobe. Computer Software company.
- ^ Viirused. Viirused. Security researchers.
