Recuperadados@protonmail.com ransomware / virus (Simple Removal Guide)
Recuperadados@protonmail.com virus Removal Guide
What is Recuperadados@protonmail.com ransomware virus?
Review of Recuperadados@protonmail.com ransomware virus
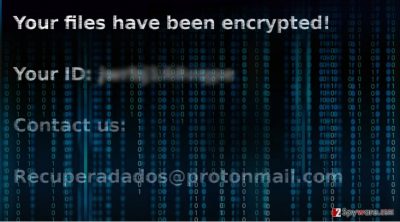
Recuperadados@protonmail.com virus operates as the cyber infection which is ready to encrypt users’ crucial files. According to the displayed email address, it sparks speculations whether it is related to Il tuo computer e stato infettato da Cryptolocker! malware. The ransom notes of the latter and former threats are written in Portuguese. Furthermore, both of them use @protomail.com domain as the public email address. According to the IT experts, this threat is based on the HiddenTear ransomware pattern, thus, it would be a mistake to underestimate the threat. Despite how ominous file-encrypting threats may look, there are prevention and confrontation ways [1]. In the last section of this article, you will find recommendations how to remove recuperadados@protonmail.com from the device. In addition, we add a few suggestions on the recovery of the files as well.
While “English” crypto-malware threats comprise the majority of the ransomware business, more “multinational” threats start to appear as well. It is not the first time when Spanish or Portuguese users are attacked with ransomware. Such countries as Malaysia also report of the virus activity [2]. It suggests that despite the quality of the Internet network and the area of residence, you might encounter recuperadados@protonmail.com ransomware or another infection.
When this particular malware settles on the device, it will take some time to encode your files. Afterward, all of them will possess .bloqueado file extensions. Attaching the attachments referring pop culture or mythology has been a prevalent tendency among cyber crooks [3]. As a result, all of the files become inaccessible. In relation to this, the crooks urge the victims of Recuperadados malware to contact them via specific recuperadados@protonmail.com email address. Naturally, you will have to pay in return for the key. According to the [AVISO-IMPORTANTE]-.txt message, victims should pay 1500 USD in return for the decryption tool. Even if FBI occasionally changes its mind concerning the need to pay the ransom [4], you should not trust hackers on their word [5]. Instead, we recommend you to focus on recuperadados@protonmail.com removal. FortectIntego ensures complete elimination of the threat.
When did the hijack happen?
If you follow the news in the IT field, you might be familiar with the most dominant ransomware distribution method. Specifically, felons prefer disguising crypto threats under update.exe, explorer.exe, or dllhost.exe fil, .doc or .zip folder. Users recklessly open the attached files only to find out later what menacing content they released from the Pandora box. After the infected file is activated, it might start executing the primary functions of the ransomware via Rundll32.exe or another system function. In addition, note that exploit kits are the secondary most popular channel for delivering ransomware. In comparison with the first method, they are more menacing as you cannot detect them simply with a naked eye. In this regard, we recommend installing a trusted security program which lowers the risk of recuperadados@protonmail.com hijack.
Eliminating the malware
Recuperadados@protonmail.com removal does not take long if you opt for the automatic method. Install a security tool, for instance, FortectIntego or Malwarebytes, and let it deal with the malware. In order for it to eradicate all components of the threat, update its virus database. Nonetheless, you should keep in mind that some versions of the file-encrypting malware tend to bother the elimination process by locking computer screen or disabling other crucial functions. If you cannot remove recuperadados@protonmail.com virus for this reason as well, do not panic but follow the guidelines. In the end, you will also find some suggestions how to recover your files if you do not have a backup at hand.
Getting rid of Recuperadados@protonmail.com virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Recuperadados@protonmail.com using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Recuperadados@protonmail.com. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Recuperadados@protonmail.com from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Recuperadados@protonmail.com, you can use several methods to restore them:
Choosing Data Recovery Pro
If recuperadados@protonmail.com malware assaults your PC and encodes your files, it is understandable that you may risk paying in the hope of retrieving the files. However, give this program a try and see. You might succeed in eliminating the files and avoid wasting money.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Recuperadados@protonmail.com ransomware;
- Restore them.
How effective is ShadowExplorer?
Latest Windows OS versions are automatically set to create shadow volume copies. This program uses these patterns to recreate the copies of your locked data. As it is unknown whether the virus deletes the copies, you should make a rush.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Recuperadados@protonmail.com and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Wayne Williams. How to beat ransomware. ITPRO. IT Analysis, Business Insight.
- ^ Hanna Sheikh Mokhtar . Alert for Malaysian Internet users of escalating ransomware attacks. New Straits Times Online. Malaysia General Sports and Lifestyle News.
- ^ Aesir and Osiris ransomware viruses join Locky family. Virus Activity Blog. IT News.
- ^ John Zorabedian. Did the FBI really say “pay up” for ransomware? Here’s what to do…. NakedSecurity. Award-winning computer security news .
- ^ Patrick O'Neill. FBI tells businesses to not pay ransomware hackers, 70 percent of US businesses do anyway. FedScoop. The leading government tech media company in DC and the community’s platform for education and collaboration through news, events, radio and TV.





















