Rootkit.TDSS (Virus Removal Guide) - Free Instructions
Rootkit.TDSS Removal Guide
What is Rootkit.TDSS?
Rootkit.TDSS – malware that deeply infects Windows system files to operate
Rootkit.TDSS, TDL3, or Alureon [Microsoft] is a malicious program designed to hide the existence of any process on the infected machine in order to perform malicious and dangerous actions.
The main purpose of the rootkit is to intercept user web traffic and steal sensitive data such as credit card details, banking credentials, logins, social security numbers, and much more.
The virus may also replace essential system executable files, which may then be used to hide processes and files installed by the attackers. It can also cause several Blue Screen of death crashes when operational.
| Name | Rootkit.TDSS |
|---|---|
| Type | Rootkit, bootkit |
| First detection | 2007 |
| Function | Intercepts user traffic and collects a variety of personally-identifiable and sensitive information |
| Removal | The virus might be very difficult to remove due to its extensive persistence mechanisms. Use robust anti-malware tools to get rid of it in Safe Mode if required |
| System fix | If you noticed that Windows is crashing, works much slower, programs fail to launch, or you face other stability issues, use FortectIntego to fix malware-caused damage automatically |
Rootkit.TDSS is installed without the user's permission through the use of trojan viruses, whereas Trojan virus can download and install additional malware, adware, or even rogue anti-spyware applications. Therefore, it is important to protect your machine with security software that can repel such attacks – we recommend using SpyHunter 5Combo Cleaner or Malwarebytes.
This virus may also infect the MBR sector, which is executed prior to Windows boot. The removal of malware can be complicated, but it is essential.
When your computer is infected with a TDSS rootkit, you may encounter the following symptoms:
- Google (Bing, Yahoo) search result links will be redirected to various misleading sites that promote rogue products or display bogus advertisements.
- Security related websites will be blocked.
- Frequent BSOD errors
- You won't be able to launch legitimate anti-malware or anti-virus applications.
- You may find that web pages load slower.
It goes without saying that you should not tolerate the presence of this threat on your Windows machine. Keep in mind that it can record very private personal data, eventually providing access to your online banking or other personal accounts.
It would not be surprising that you would lose money at any time, become a victim of future phishing campaigns, or even suffer from identity theft. Therefore, follow the detailed instructions we provide below in order to remove all the malicious files and components of this rootkit.
Virus removal instructions
Please use TDSS virus remover and remove it as soon as possible after detection. First of all, download TDSSKiller.
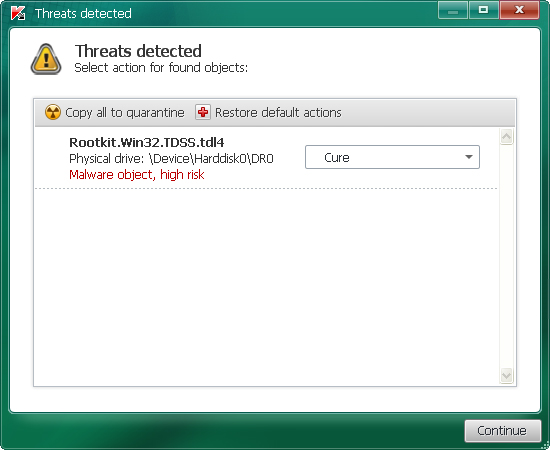
This tool was created to remove rootkits that belong to numerous hard-to-remove malware families. Run the program and press the Start scan button for the utility to start the scan process. The scan won't take long – only a few minutes.
After the scan, it will list malicious files. Suspicious objects should be skipped, and malicious, high-risk objects should be deleted. After clicking Next, the utility applies selected actions and outputs the result. Select the correct option and click Continue.
A reboot might require after disinfection, so just click Reboot. Now, your computer should be TDSS rootkit free. Note that additional malware could be hiding on your PC. If for some reason, you are unable to use the provided scanner, you should access Safe Mode with Networking and perform a full system scan.
Additionally, scanning the device with SpyHunter 5Combo Cleaner or another reputable security software can help ensure that no malicious components are left on your machine. Don't forget to clean your web browsers and fix registries – you can use FortectIntego for the job.
Getting rid of Rootkit.TDSS. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Rootkit.TDSS and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
