Rumba ransomware (Virus Removal Guide) - Free Instructions
Rumba virus Removal Guide
What is Rumba ransomware?
Rumba virus is a file locking malware that spreads using cracks and demands ransom payment of $980 in Bitcoin
Rumba virus is a ransomware that was discovered on January 19th, 2019. It is a variant of the infamous Djvu virus which belongs to STOP ransomware family and uses the AES encryption algorithm to encode personal documents, pictures, videos, databases and appends .rumba or .ramba file extension. Generally, Rumba virus does not differ from its predecessors (such as .Tfude), as it also drops ransom note _openme.txt and uses the same contact emails – pdfhelp@india.com and pdfhelp@firemail.cc. However, bad actors do state that they want $980 in Bitcoin, also offering a 50% discount within 72 hours of the initial computer compromise. Rumba ransomware has been spotted attacking people in Germany, Hungary, Poland, Turkey, Chile, Thailand, Egypt, and other countries. The main distribution methods used for this version is cracks from a variety of software that is bundled on third-party sites, as well as fake Windows updates. Good news is that malware, alternatively known as Ramba virus, is decryptable.
| Name | Rumba |
| Type | Ransomware |
| Family | STOP |
| Variant of | Djvu ransomware |
| First spotted | January 19th 2019 |
| Ransom note | _openme.txt |
| File extension | .rumba, .ramba |
| Ransom size | $980 or $490 |
| Distribution | Fake Windows updates, cracks for pirated software |
| Decryptable? | Yes, find more information here |
| Elimination | Use security software that can recognize the threat – we suggest FortectIntego, which is based on Avira engine |
While most ransomware virus authors rely on spam emails to distribute the malicious payload on victims' machines, all the Djvu versions, including Rumba, has been delivered with the help of fake updates and cracked software.[1] Due to the rampant increase in the number of infections, Rumba virus, and all the other variants have become one of the most prevalent crypto viruses in the past months.
Users often download cracks such as KMSPico or pirated versions of Photoshop and other legitimate programs, which includes the malicious Rumba ransomware payload. Therefore, it is vital to use protective tools that could block malware infection entirely. Those who did not have anti-malware installed and got infected, should download FortectIntego or other software that detects the virus, and remove Rumba virus entirely.
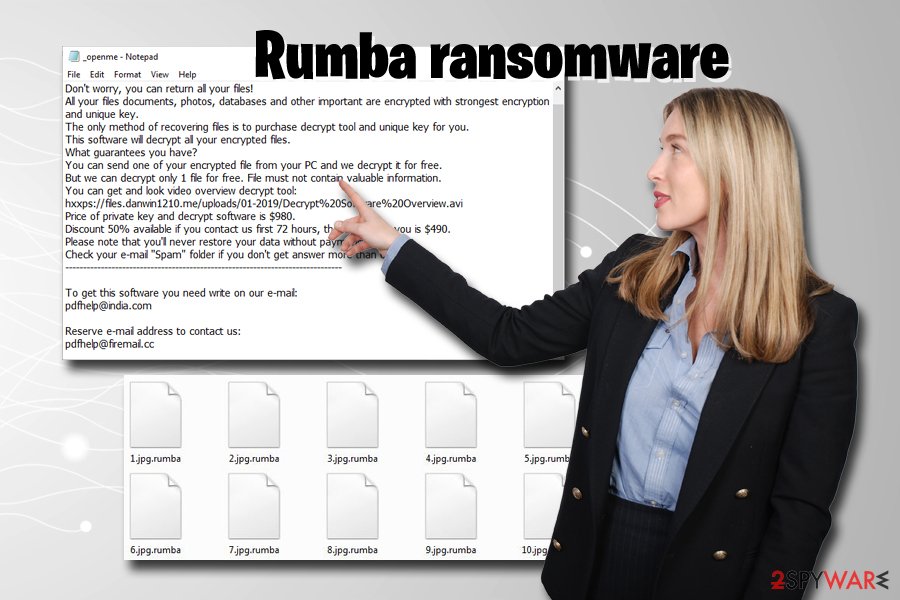
After infiltration, Rumba ransomware performs system changes, modifies personal files to make them inaccessible, and drops a ransom note into each of the affected folders, which reads:
———————— ALL YOUR FILES ARE ENCRYPTED ————————
Don't worry, you can return all your files!
All your files documents, photos, databases and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://files.danwin1210.me/uploads/01-2019/Decrypt%20Software%20Overview.avi
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” folder if you don't get answer more than 6 hours.
——————————————————————————To get this software you need write on our e-mail:
pdfhelp@india.comReserve e-mail address to contact us:
pdfhelp@firemail.ccYour personal ID:
While most of the researchers advise not to contact cybercriminals, now there are even more reasons to do so, as .ramba ransomware is decryptable with the help of independent security researcher Michael Gillespie.[2] Please contact him if you got infected with this variant.
However, make sure that you perform Rumba virus removal before you apply the decryptor or use backups, as all the data will be encoded as well. In case you have no backups and decryption did not work for you, you still have a chance of recovering at least some of the files with the help of professional third-party software.
Pirated software, cracks, and fake updates might lead to ransomware infection – learn to protect yourself
As we already mentioned, security researches are receiving hundreds of submissions from victims in the recent months, so this variant of Djvu is extremely prevalent around the world. The success is fueled by the effective infection method – cracks and fake updates.
There are millions of users who download and install software from torrent and similar file sharing sites. While pirating is highly illegal and might result in fines or even jail time, users proceed to download and install illegal software. Also, it is a well-known fact that torrent sites are highly unsafe and host malware.[3] Nevertheless, it is crucial to minimize the risk if you decide to use such sites:
- Use anti-virus software and Firewall at all times;
- Patch the software and operating system on time;
- Stay away from cracks or keygens, these often host malicious payload inside;
- When downloading new software, make sure to pick Advanced/Custom installation settings in order to decline all the optional programs;
- Scan all the downloaded files with tools like Virus Total;
- Disable Adobe Flash and Java plugins or set them to click-to-run setting;
- Set all updates to automatic setting;
- Use strong passwords and a VPN;
Rumba virus fix and decryption solution
Rumba virus recovery should not be a complicated task, as long as you use reputable security software, such as FortectIntego. However, some malware might interfere with the normal operation of the computer and anti-malware tools. In such as case we recommend you enter Safe Mode with Networking as explained below and perform full Rumba virus removal from there.
Once you get remove Rumba ransomware, you can try one of three options to recover your data: use a decryptor created by experts, use backups, or make use of third-party recovery software. We are convinced that one of the methods should work for you, so check the guide below.
Getting rid of Rumba virus. Follow these steps
Manual removal using Safe Mode
To remove Rumba virus safely, enter Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Rumba using System Restore
System Restore can help you with virus elimination as well:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Rumba. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Rumba from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.There is no need to pay cybercriminals, as there is an official decryptor created. Pleases find the instructions below.
If your files are encrypted by Rumba, you can use several methods to restore them:
Use Data Recovery Pro to recover data affected by .rumba
Data Recovery Pro is a professional tool that is known to help some ransomware victims.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Rumba ransomware;
- Restore them.
Try to recover your data with the help of Windows Previous Versions feature
This method is only available if you had System Restore function enabled before the malware struck.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer might be the solution
If Rumba file virus failed to remove Shadow Volume Copies, ShadowExplorer would be able to recover all of your files.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Use STOPDecrypter to recover files encrypted by Rumba
The famous virus researcher Michael Gillespie has recently updated his STOPDecrypter 2.0.0.0 to fight against this Djvu virus version. You can download it by clicking this link. All the instructions and the tool can be found here.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Rumba and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ How safe is cracked software?. Quora. Question-answer site.
- ^ Michael Gillespie. If you are infected by STOP Djvu #Ransomware with extension ".rumba" . Twitter. Social network.
- ^ Pierluigi Paganini. Torrent websites infected 12 million Internet users per month. Security Affairs. Security website.





















