SearchProvided Mac virus (Free Guide)
SearchProvided Mac virus Removal Guide
What is SearchProvided Mac virus?
SearchProvided is a Mac virus that can seriously compromise your device

SearchProvided virus is malicious software that belongs to the broader family of Adload malware, specifically targeting Mac computers. It is designed to infiltrate a user's system and wreak havoc by performing a variety of harmful activities.
Once installed, the SearchProvided virus alters browser settings, including changing the homepage and other preferences. This allows the virus to redirect users to suspicious websites, which may further expose the victim to additional threats or scams. Moreover, the virus inundates users with unwanted ads, creating an unpleasant browsing experience and potentially leading to more dangerous content.
One of the most concerning aspects of the SearchProvided is its ability to install additional versions of itself, thus multiplying its presence on the infected system. This makes it increasingly difficult for users to detect and remove the malware manually.
Another alarming feature of the virus is its capability to steal sensitive data from the infected Mac. The virus can access personal information such as usernames, passwords, and financial data, which may be used for identity theft, financial fraud, or other malicious activities.
Due to its persistent nature, the SearchProvided virus is particularly challenging to remove manually. Users are advised to follow a comprehensive guide that outlines the necessary steps to remove this malicious software from their system.
| Name | SearchProvided |
| Type | Mac virus, adware, browser hijacker |
| Malware family | Adload |
| Distribution | Fake Flash Player installers or bundled software from malicious sources |
| Symptoms | A new extension and application are installed on the system; search and browser preferences are changed to use a different search engine; new user profiles and login items are created on the account; intrusive advertisements and redirects |
| Removal | The easiest way to remove Mac malware is to perform a full system scan with SpyHunter 5Combo Cleaner security software. We also provide a manual guide below |
| Other tips | Malware and adware can meddle with your system, reducing its performance. If you want to quickly fix various issues, we recommend you try using automated tools like FortectIntego |
How the virus spreads: common infection methods
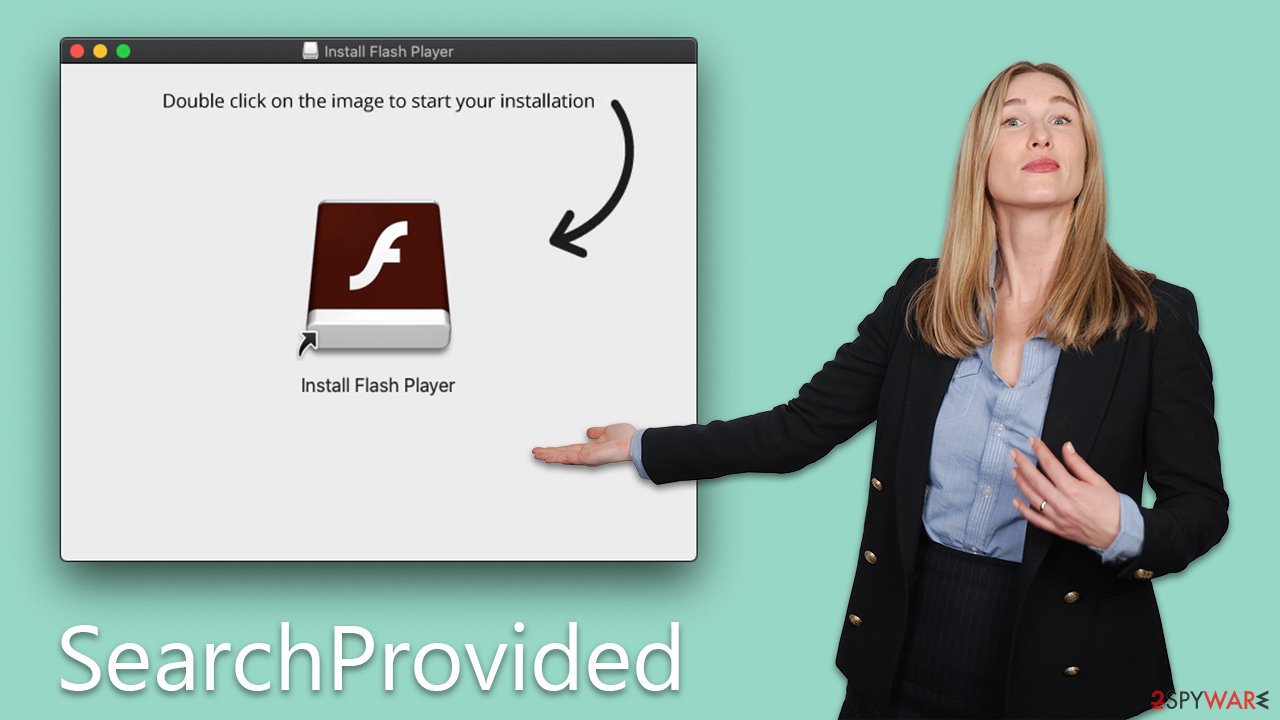
Understanding how the SearchProvided virus spreads is crucial in preventing its infiltration and the damage it can cause to Mac computers. Two primary methods are responsible for the widespread distribution of this malicious software: fake Flash Player installers and cracked software installers.
-
Fake Flash Player Installers
One of the most prevalent tactics used by cybercriminals to spread Adload is through fake Flash Player installers. Unsuspecting users may come across pop-up ads or notifications on websites, urging them to update their Flash Player to the latest version. These deceptive prompts often mimic the appearance of legitimate software updates, making it difficult for users to differentiate between genuine and malicious installers.
Once the user clicks on the fake Flash Player installer, the SearchProvided virus is downloaded and installed onto their Mac computer. The malware then initiates its harmful activities, such as altering browser settings, displaying intrusive ads, and stealing sensitive information.
To protect against this method of infection, users should avoid downloading software updates from unverified sources. Instead, they should rely on official websites or in-app update notifications to ensure the legitimacy of the updates.
-
Cracked Software Installers
Another common method of spreading the SearchProvided virus is through cracked software installers. Cybercriminals often bundle the virus with pirated or cracked versions of popular applications, which are then distributed through peer-to-peer networks, torrent websites, or other untrustworthy sources.
When users download and install these cracked applications, they inadvertently introduce the virus to their system. The malware then proceeds to infect the computer, compromising its security and performance.
The allure of free or heavily discounted software can be tempting for many users. However, the risks associated with cracked software installers far outweigh the potential benefits. Users should always obtain software from legitimate sources, such as the official websites of developers or authorized retailers. By doing so, they can minimize the risk of encountering various malware.
In conclusion, understanding the primary methods through which the SearchProvided virus spreads is essential for prevention. Users should be cautious when encountering software updates, particularly those for Flash Player, and should avoid downloading cracked software from unverified sources. By remaining vigilant and adhering to safe browsing practices, users can significantly reduce the likelihood of falling victim to this virus and similar threats.
Malware removal explained
Due to the elevated system permissions granted to SearchProvided, removing it may not be as straightforward or efficient as uninstalling a regular application. Besides depositing numerous malicious files on the system, this malware creates new profiles and login items.
Utilizing built-in AppleScript, the virus can effectively evade detection by security features such as XProtect and Gatekeeper, allowing it to continue functioning even if the primary app and/or browser extension have been removed. Consequently, they may reappear later.
As a result, we advise using automatic removal methods with security software like Malwarebytes or SpyHunter 5Combo Cleaner to effectively eliminate the infection. Regardless of the chosen removal technique, it is important to clear web browser caches to minimize future complications.
The SearchProvided virus operates by initiating background processes upon installation. To effectively remove the primary application, it is essential first to terminate these processes using the Activity Monitor. Follow these steps:
- Open Applications folder
- Select Utilities
- Double-click Activity Monitor
- Here, look for suspicious processes and use the Force Quit command to shut them down
- Go back to the Applications folder
- Find the malicious entry and place it in Trash.
![Uninstall from Mac 1 Uninstall from Mac 1]()
Upon infiltration, the virus might establish new User profiles and Login items for persistence. This might be the reason why you can't get rid of the app or the extension.
- Go to Preferences and select Accounts
- Click Login items and delete everything suspicious
- Next, pick System Preferences > Users & Groups
- Find Profiles and remove unwanted profiles from the list.
You should get rid of Launch Daemons and other configuration data left by malware. Proceed with the following:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and delete all the related .plist files.
If you opt to clean the infection manually, the extension may still be active in your browser and continue to collect data and execute other malicious activities, so you need to make sure that this component is removed at once:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Once you uninstall the extension, be sure also to delete all its cached data from your local folders, or it may continue to track your activities. FortectIntego is a great tool for automating this process and can also remove other junk from your system to improve performance. If you prefer doing this manually, follow these steps:
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
If you were unable to remove the extension in a regular way, you should simply reset Safari. Follow these steps:
- Click Safari > Preferences…
- Go to the Advanced tab.
- Tick the Show Develop menu in the menu bar.
- From the menu bar, click Develop, and then select Empty Caches.
![Reset Safari Reset Safari]()
If you use Firefox or Chrome, check the below instructions.
Getting rid of SearchProvided Mac virus. Follow these steps
Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.











